Warlock emerged in June–July 2025 after being deployed via exploitation of the ToolShell Microsoft SharePoint zero-day (CVE-2025-53770) by a China-linked actor tracked as Storm-2603, which also used LockBit and DLL sideloading (7z.exe/7z.dll). Investigations tie Warlock to earlier tooling and a reused stolen certificate (coolschool) linked to long-running Chinese-affiliated groups (CamoFei/ChamelGang) and show overlaps with Anylock, LockBit 3.0, and possibly Black Basta; indicators include multiple file hashes and a vulnerable Baidu driver. #ToolShell #Storm-2603
Category: Threat Research
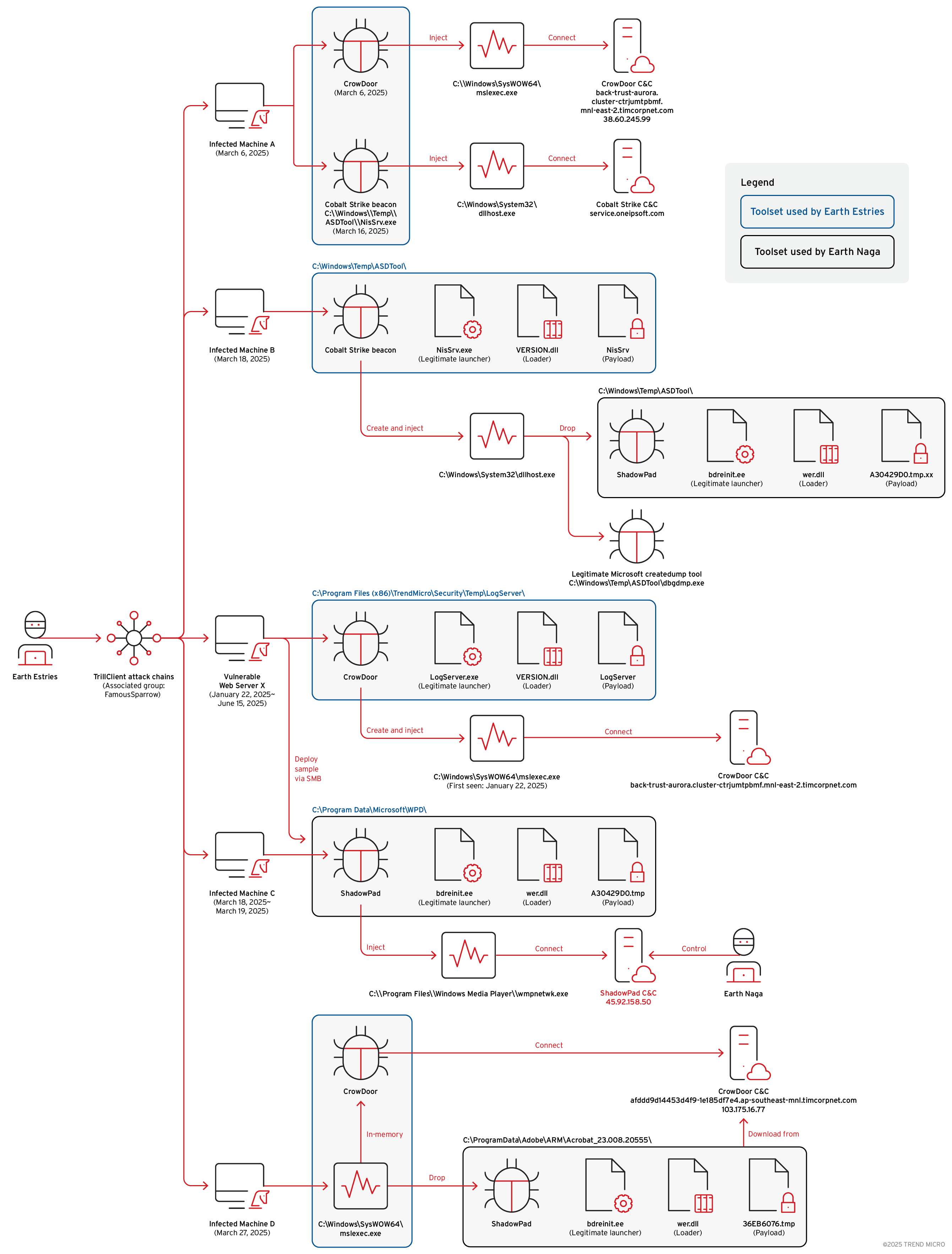
Trend Research documents a new “Premier Pass-as-a-Service” model in which Earth Estries functions as an access broker that provides persistent access to Earth Naga, enabling coordinated deployments of backdoors like CrowDoor and ShadowPad. The report outlines a four-tier framework for collaborative APT attacks and highlights targeted campaigns against government, telecommunications, and…
Cofense Intelligence discovered a sophisticated phishing script that selects a random .org domain, generates dual UUIDs, and performs server-driven dynamic page replacement to steal credentials while evading detection. This technique leverages HTML-based attachments and cloud-collaboration spoofing to deliver the malicious payload and targets enterprise users with tailored fake login pages. #Cofense #uuidv4

We applied survival analysis (Kaplan-Meier) to Qualys VMDR data ingested into the Elastic Stack to more accurately measure time-to-patch and account for censored (still-open) vulnerabilities, revealing that common mean/median metrics can hide long tails and open-case dynamics. The approach enables stratified comparisons across teams, environments, and severities and supports operational metrics like SLO adherence, arrival rate, burndown rate, and escape rate. #QualysVMDR #KaplanMeier

Operation Endgame (May 2024–May 2025) triggered multinational takedowns targeting loaders, botnets, and cash-out services, prompting selective Russian domestic enforcement that dismantled monetization nodes (e.g., Cryptex, UAPS) while higher-value ransomware operators with alleged intelligence ties (e.g., Conti, Trickbot) largely remained insulated. The resulting trust erosion in the underground drove tighter OPSEC, closed affiliate recruitment, rebrands, and decentralization as attackers adapted to sustained Western pressure and a conditional Russian “politics of protection.” #OperationEndgame #Cryptex #Conti #Trickbot
Netskope discovered a new Python-based remote access trojan that impersonates a Minecraft client named “Nursultan Client” and uses the Telegram Bot API as its command-and-control channel to steal Discord tokens, capture screenshots and webcam images, and perform system reconnaissance. The sample includes a hardcoded Telegram bot token and allowed user ID, demonstrates cross-platform C2 capabilities despite flawed Windows persistence, and appears to be a Malware-as-a-Service offering signed “by fifetka”. #NursultanClient #TelegramBotAPI
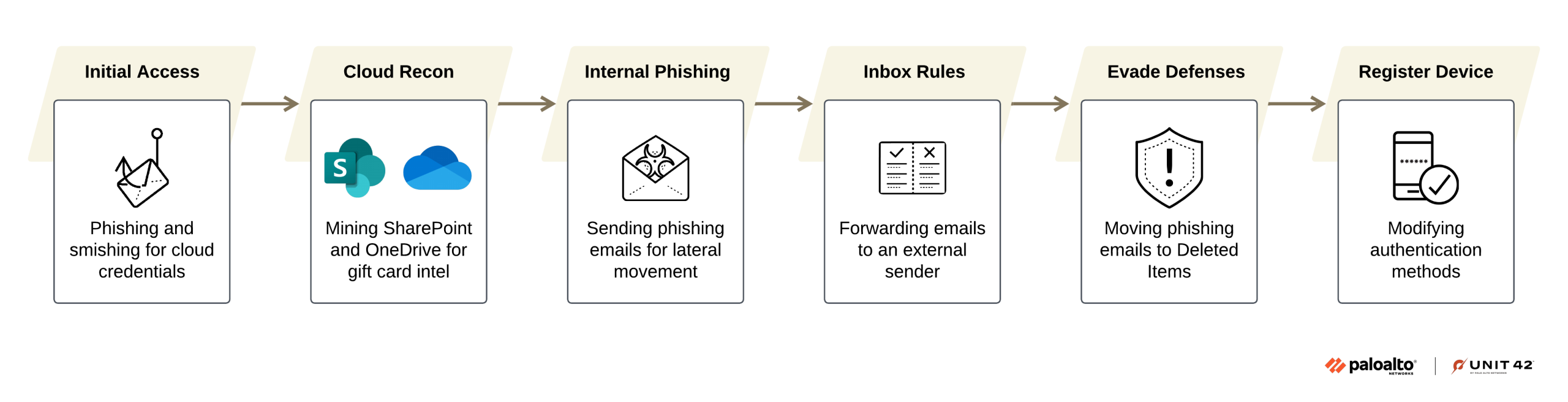
A Morocco-based financially motivated group tracked as CL-CRI-1032 (overlapping with Atlas Lion/STORM-0539) runs the Jingle Thief campaign, using phishing and smishing to steal Microsoft 365 credentials and carry out large-scale gift card fraud by abusing cloud services. Their tactics include tailored phishing, inbox rules for silent exfiltration, device/Authenticator registration in Entra…
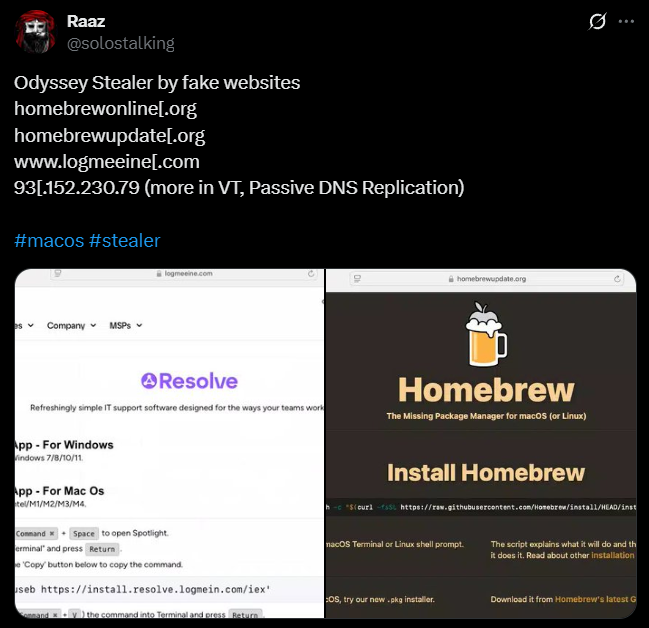
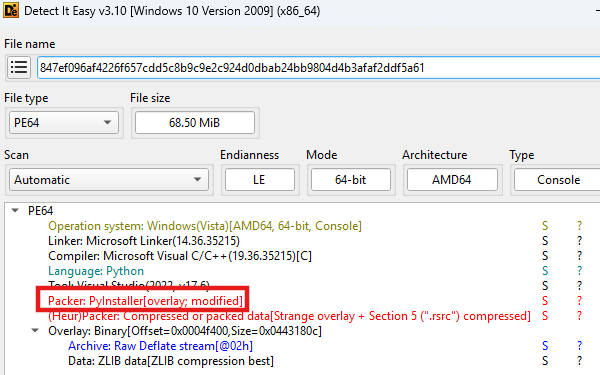
A coordinated campaign is impersonating developer tools and trusted services to trick macOS users into pasting base64-encoded curl commands that fetch and execute installer scripts delivering Odyssey Stealer and AMOS. Operators reuse infrastructure, SSL certificates, and domains (e.g., 93.152.230[.]79, 195.82.147[.]38, bonoud.com) to maintain persistence and scale across at least 85 phishing sites. #OdysseyStealer #AMOS #93.152.230.79 #195.82.147.38
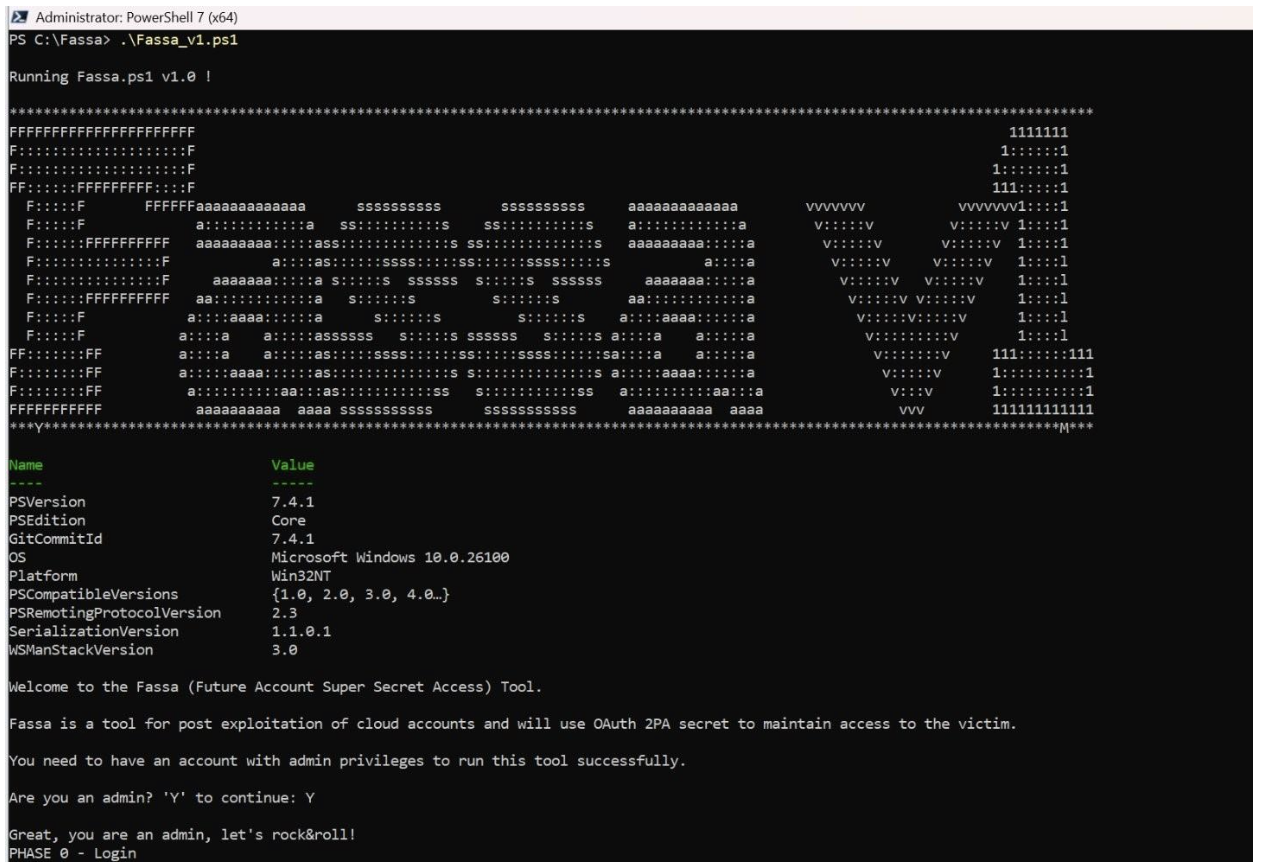
Proofpoint researchers demonstrated how attackers automate creation of malicious internal (second-party) OAuth applications to gain persistent access to Microsoft Entra ID tenants, allowing continued mailbox and file access even after credential resets or MFA enforcement. The researchers observed an active ATO using this technique linked to AiTM Tycoon phishing activity and…
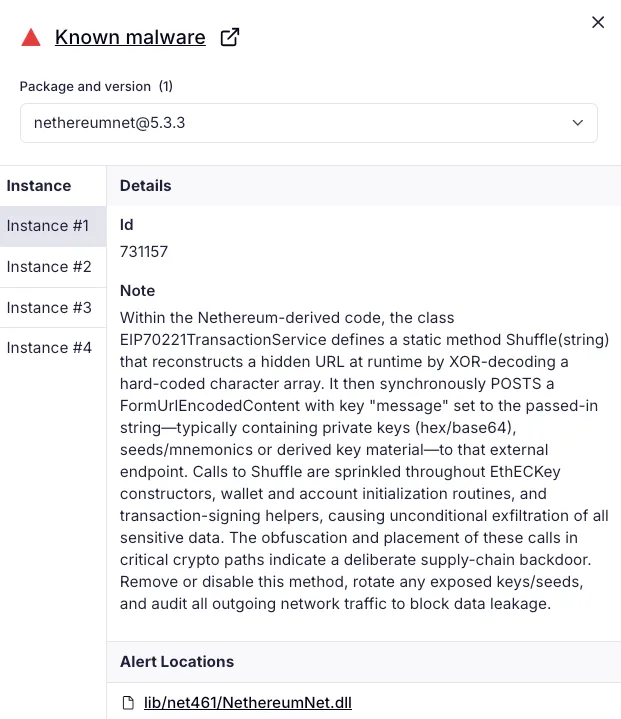
Socket’s Threat Research Team discovered a homoglyph typosquat on NuGet named Netherеum.All that impersonated Nethereum and exfiltrated secrets by XOR-decoding a C2 endpoint and POSTing caller-supplied data to it. The actor used inflated downloads and reused the same XOR exfiltration code across multiple packages, including an earlier typosquat NethereumNet, before NuGet removed the malicious packages. #Netherеum.All #NethereumNet

GTIG observed multiple pro‑Russia information operations rapidly promoting narratives to deflect blame for the Sept. 9–10, 2025 Russian drone incursion into Polish airspace and to undermine Polish and NATO responses. These campaigns—including Portal Kombat, Doppelganger, and Niezależny Dziennik Polityczny (NDP)—amplified messaging that questioned Russian culpability, blamed NATO/Poland, and aimed to erode domestic and international support for Ukraine. #PortalKombat #NiezależnyDziennikPolityczny
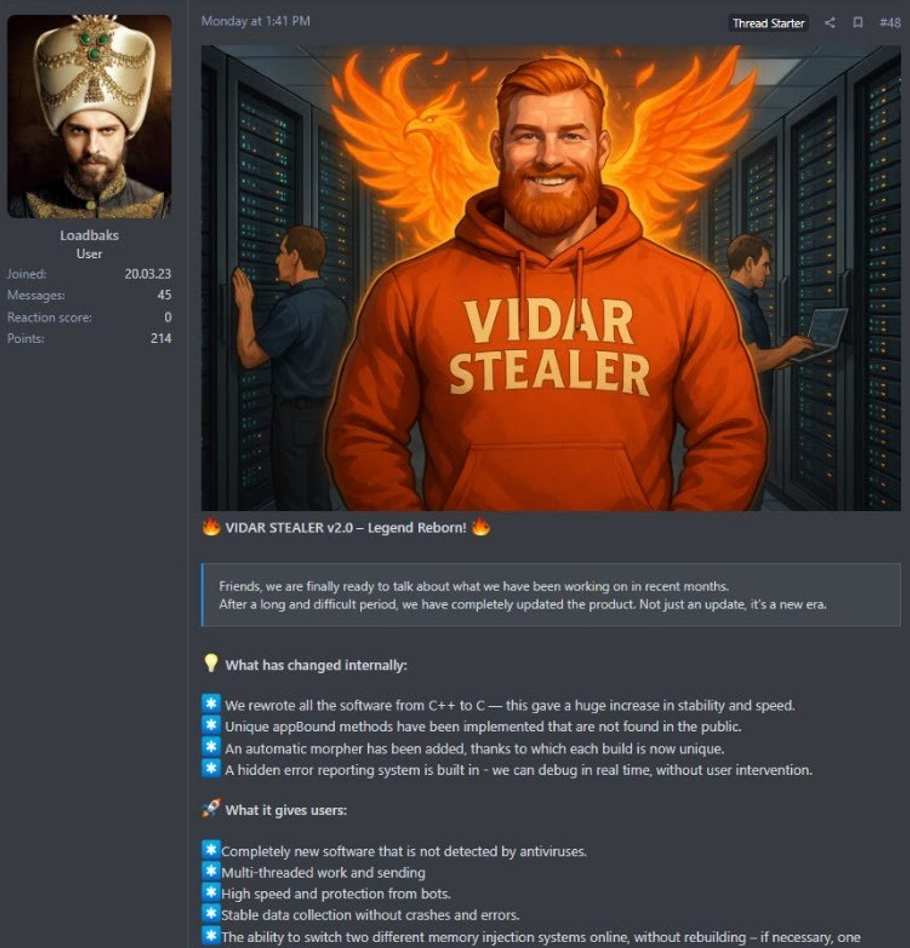
Trend Research analyzes Vidar Stealer v2.0, a full rewrite in C that adds multithreaded data theft, advanced anti-analysis and AppBound bypass techniques, and an automatic polymorphic builder, enabling faster and more evasive credential and wallet exfiltration. The release aligns with declining Lumma Stealer activity and a spike in Vidar adoption, suggesting…

A Chinese-speaking threat actor (REF3927) exploited publicly exposed ASP.NET machine keys on IIS servers to deploy a Godzilla-forked webshell, the GotoHTTP RMM, a kernel rootkit derived from the open-source “Hidden” project, and a malicious IIS module named TOLLBOOTH that provides SEO cloaking, webshell access, and management endpoints. The campaign affected hundreds of global IIS servers, leveraged reused machine keys for initial access, and used DKOM-based hiding, RMM-based remote control, and configuration fetched from c[.]cseo99[.]com to operate. #TOLLBOOTH #Z-Godzilla_ekp
Between late August and early September 2025, many IIS servers were compromised via ASP.NET viewstate exploitation using publicly exposed machine keys and a ready-made toolkit that installed a malicious IIS module named “HijackServer”, supplemented by a customized Hidden rootkit to conceal artifacts. The operation deployed C++, .NET and PHP variants of…
Sekoia.io decoded the opaque numeric UserAuthenticationMethod field in Microsoft 365 audit logs as a bitfield where each bit maps to a specific primary-capable authentication method by correlating Microsoft 365 audit logs with Microsoft Entra sign-in logs. The findings help investigators translate numeric values (e.g., 272, 33554704) into human-readable methods like Password Hash Sync, Staged Rollout, and Passkey, and highlight unmapped bits for community validation. #UserAuthenticationMethod #Sekoia.io
