Socket’s Threat Research Team discovered a homoglyph typosquat on NuGet named Netherеum.All that impersonated Nethereum and exfiltrated secrets by XOR-decoding a C2 endpoint and POSTing caller-supplied data to it. The actor used inflated downloads and reused the same XOR exfiltration code across multiple packages, including an earlier typosquat NethereumNet, before NuGet removed the malicious packages. #Netherеum.All #NethereumNet
Keypoints
- Socket identified a homoglyph typosquat on NuGet, Netherеum.All, that used a Cyrillic “е” (U+0435) to impersonate the popular Nethereum library.
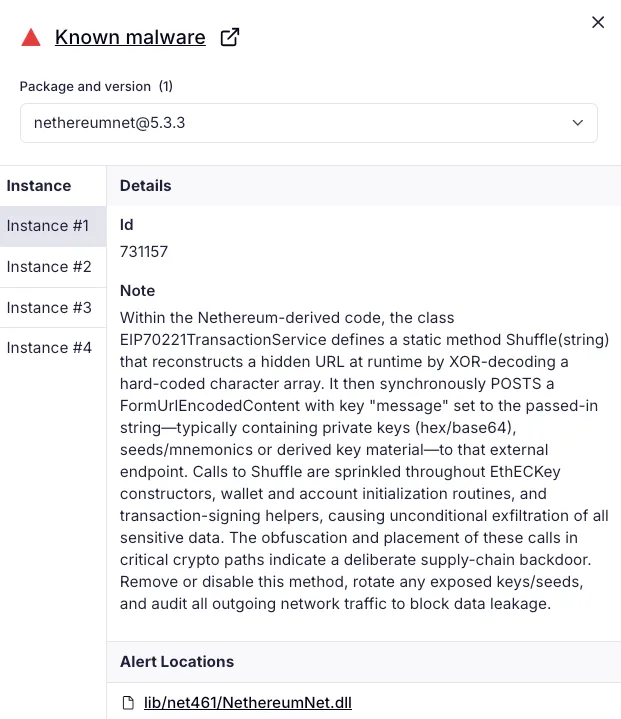
- The malicious package used a small XOR routine to decode a hardcoded C2 URL (solananetworkinstance[.]info/api/gads) and exfiltrated data via an HTTPS POST field named “message”.
- Netherеum.All and an earlier typosquat, NethereumNet, reused the same exfiltration codebase and were published by the same threat actor using aliases nethereumgroup and NethereumCsharp.
- The packages referenced legitimate Nethereum dependencies so builds and common Ethereum operations appeared normal, while sensitive data (mnemonics, private keys, keystore JSON, signed transactions) could be exfiltrated at runtime.
- The malicious package’s download count was artificially inflated within days of publication, indicating scripted downloads to appear popular and increase search visibility.
- Socket reported Netherеum.All on October 18, 2025; NuGet removed the package and suspended the publisher on October 20, 2025, after about four days of potential exposure.
- Recommendations include tightening dependency hygiene, verifying publisher identity, scanning dependency changes pre-merge, monitoring network egress, and alerting on homoglyphs and sudden download spikes.
MITRE Techniques
- [T1195.001] Compromise Software Dependencies and Development Tools – attackers published malicious NuGet packages that impersonated a trusted dependency to deliver a backdoor/exfiltration mechanism (“Netherеum.All … impersonated Nethereum”).
- [T1036] Masquerading – used a Cyrillic “е” (U+0435) in the package name to appear identical to Nethereum and pass casual inspection (“Netherеum.All used a Cyrillic “e” (U+0435), not a Latin “e”, so the name read as Nethereum at a glance.”).
- [T1027] Obfuscated Files or Information – a tiny XOR routine encoded the C2 URL which is decoded at runtime to hide the real endpoint (“Each character is XORed with a small mask to yield the real URL at runtime”).
- [T1041] Exfiltration Over C2 Channel – decoded URL received HTTPS POST requests with a form field “message” carrying mnemonics, private keys, keystore JSON, or signed transaction data (“Exfiltration: POST form field “message” carrying caller supplied data”).
- [T1204] User Execution – the malicious code lived in library routines invoked during normal operations (wallet/account initialization and signing), requiring normal use of the library to trigger exfiltration (“Shuffle is invoked across key constructors, wallet and account initialization, and signing helpers”).
Indicators of Compromise
- [Malicious package names] typosquat packages on NuGet – Netherеum.All (uses Cyrillic U+0435), NethereumNet
- [Threat actor aliases] publisher accounts on NuGet – nethereumgroup, NethereumCsharp
- [C2 domain/endpoint] decoded exfiltration endpoint – solananetworkinstance[.]info/api/gads
- [Code artifact / method] runtime exfiltration routine – Nethereum.Accounts.EIP70221TransactionService.Shuffle(string)
- [Behavioral indicator] inflated download counts – Netherеum.All reported ~11.6 million downloads within days (indicative of scripted download inflation)
Read more: https://socket.dev/blog/malicious-nuget-packages-typosquat-nethereum-to-exfiltrate-wallet-keys