A phishing campaign impersonating Meta uses a Gmail sender display name and Google Forms to harvest login credentials and capture 2FA tokens in real time. The campaign then uses a vercel.app-hosted phishing page to collect credentials and immediately access compromised accounts. #Meta #GoogleForms
Category: Threat Research
.png)
Chinese state-sponsored cyber activity has shifted to industrialized, shared covert networks of compromised SOHO routers, IoT devices, and end-of-life edge appliances that route reconnaissance, C2, and exfiltration through geographically local exit nodes to frustrate detection and attribution. The ecosystem leverages an industrial contractor model, a shared malware/tooling economy (e.g., ShadowPad, PlugX), and advanced tradecraft such as DLL sideloading and hypervisor/UEFI implants to enable scale and persistence. #ShadowPad #KV-Botnet
.png)
Sysdig TRT observed a rapid, pre-auth SQL injection (CVE-2026-42208 / GHSA-r75f-5x8p-qvmc) against LiteLLM that used UNION-based payloads to enumerate tables holding virtual API keys, provider credentials, and environment variables. The operator executed schema-aware column-count discovery from rotating egress IPs but Sysdig saw no confirmed authenticated follow-on; patch to v1.83.7 and rotate exposed keys immediately. #LiteLLM #CVE-2026-42208

ESET Research uncovered a China-aligned APT group named GopherWhisper that targeted a Mongolian governmental entity and deployed a diverse Go-centric toolset including LaxGopher, RatGopher, BoxOfFriends, JabGopher, CompactGopher, FriendDelivery, and SSLORDoor. The group abused legitimate services (Discord, Slack, Microsoft 365 Outlook, file.io) for C2 and exfiltration, and ESET extracted thousands of Slack and Discord messages and draft Outlook emails to analyze the group’s operations. #GopherWhisper #Mongolia
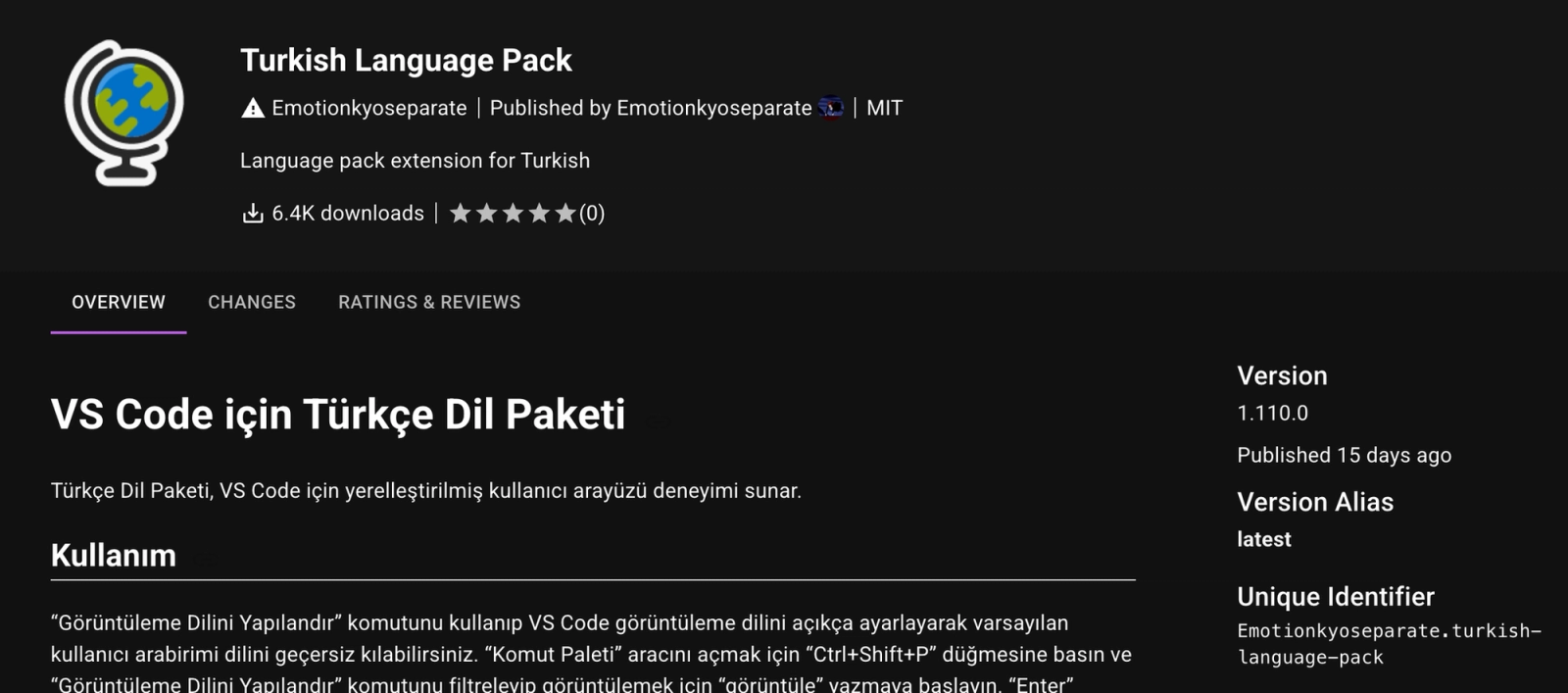
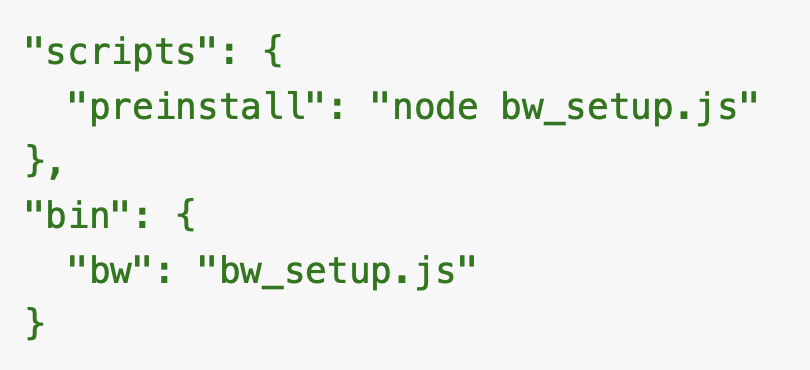
The GlassWorm campaign has expanded on Open VSX with a new cluster of 73 impersonation extensions that were initially published as benign “sleeper” packages and later updated to deliver malware through normal extension update and dependency mechanisms. Socket is tracking confirmed malicious activations and many high-confidence sleeper extensions that use cloned listings, transitive delivery, GitHub-hosted VSIX payloads, native binaries, and obfuscated JavaScript to evade detection. #GlassWorm #OpenVSX
The npm ecosystem shifted to a high-consequence threat landscape after the September 2025 Shai-Hulud worm enabled automated compromise and redistribution of malicious packages, accelerating token theft and CI/CD persistence. Unit 42 describes a multi-stage, heavily obfuscated payload attributed to TeamPCP that steals npm/GitHub/cloud credentials, exfiltrates via an HTTPS C2 and public…

Harvester has developed a new Linux variant of its GoGra backdoor that abuses the Microsoft Graph API and Outlook mailboxes as a covert C2 channel, using hardcoded Azure AD application credentials to poll mailboxes and execute AES-encrypted tasks. Symantec and Carbon Black link the Linux implant to a prior Windows GoGra campaign, showing cross-platform code reuse, identical typos, and tailored decoy documents targeting South Asia. #GoGra #Harvester

Cyble Research and Intelligence Labs (CRIL) uncovered a coordinated campaign of over 16,800 spoofed domains using subdomain trust injection, hyphen manipulation, and combined obfuscation to impersonate government portals for credential and payment card harvesting. Infrastructure clusters concentrate in Tencent Cloud and Alibaba Cloud APAC nodes with registrar dominance by Gname.com, and a distinct subset of domains shows TTPs consistent with APT36. #OperationTrustTrap #APT36

Elastic’s InfoSec team implemented an OpenTelemetry-based monitoring pipeline to ingest Claude Code and Claude Cowork telemetry into Elasticsearch for real-time observability, detection, and incident response. The pipeline includes self-managed EDOT collector and Elastic Cloud Managed OTLP options, custom mappings and ingest pipelines to parse tool parameters, and enables use cases like tool-invocation auditing, session reconstruction, permission analysis, and EDR correlation. #ClaudeCode #ClaudeCowork

Acronis telemetry of ~960 million backup job executions in H2 2025 reveals high failure concentrations during off-hours—especially Friday 01:00 and 02:00—with full backups at 02:00 failing at 21.61%. The report quantifies scheduling peaks (23:00 avg 185,693 jobs/day), identifies optimal hours by backup type (full best at 06:00, custom best at 14:00), and prescribes scheduling and monitoring changes to cut failure risk and business impact. #Acronis #SpaceQuotaReachedHard

Replace this text with exactly 2 sentences summarizing the content. At the end, add hashtags for specific keywords mentioned in the article—such as names of malware, threat actors, or affected organizations/systems. Avoid general terms like #malware, #ransomware, or #cybersecurity. Use this format: #Keyword1 #Keyword2

Cyble Research & Intelligence Labs tracked 1,675 vulnerabilities last week, including 111 critical CVSS v3.1 findings and more than 205 with public proof-of-concept exploits, while CISA added 10 vulnerabilities to its Known Exploited Vulnerabilities catalog. Active exploitation and rising attacks targeted collaboration, endpoint management, AI agent frameworks, and industrial control systems—most notably Microsoft SharePoint and Fortinet FortiClient. #MicrosoftSharePoint #FortinetFortiClient
Researchers documented a long-running international revenue share fraud (IRSF) campaign that uses fake CAPTCHA pages and TDS redirects to coerce victims into sending multiple international SMS messages that generate termination-fee revenue for the operators. The operation leverages affiliate tracking, back-button hijacking, and multi-stage redirection to maximize SMS volume and evade detection, and victims are advised: do not send a text to confirm you are human. #IRSF #Click2SMS
SentinelLABS discovered a previously undocumented 2005 cyber‑sabotage framework named fast16 that used an embedded Lua VM in a reusable service carrier (svcmgmt.exe) and a boot-start kernel driver (fast16.sys) to patch executables in memory and introduce subtle floating‑point errors into high‑precision calculation software. The framework included worm‑style propagation to deploy the driver across a facility, targeted engineering and simulation suites such as LS‑DYNA and PKPM, and later appeared in the ShadowBrokers “Territorial Dispute” signatures. #fast16 #LS-DYNA

China’s dominance of rare earth element (REE) processing and refining gives it significant geopolitical leverage, driving accelerated competition for critical minerals across the deep sea, the Arctic, Greenland, Antarctica, and space. State-sponsored and criminal cyber threat actors are increasingly targeting mining organizations and regulators to gain strategic advantage, with groups like BianLian and APT15 linked to compromises and extortion. #BianLian #APT15