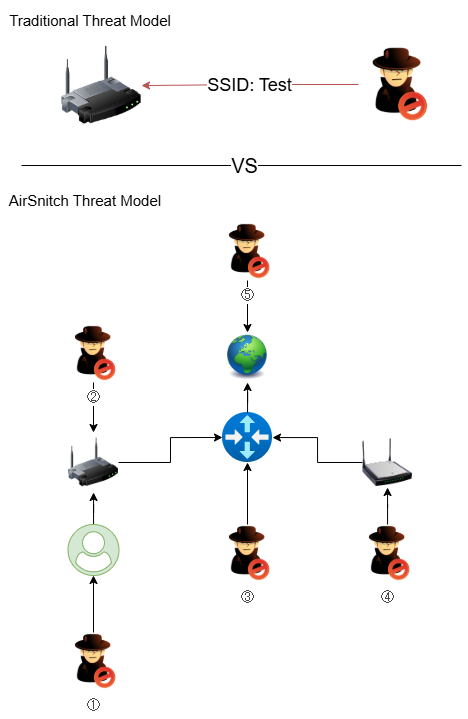
AirSnitch is a set of novel Wi‑Fi attack techniques presented at NDSS 2026 that exploit interactions between encryption, switching and routing layers to bypass protections in WPA2 and WPA3-Enterprise. These techniques (e.g., Gateway Bouncing, Port Stealing, Broadcast Reflection) enable attackers to intercept or inject traffic by manipulating MAC-to-port mappings and shared…
Category: Threat Research
ESET Research discovered a new NGate variant that trojanizes the legitimate Android HandyPay app to relay NFC payment-card data and capture PINs for contactless ATM cash-outs and unauthorized payments. The campaign, active since November 2025 and targeting Android users in Brazil, spread trojanized samples via a fake Rio de Prêmios lottery site and a fake Google Play page, and evidence in the malware logs suggests the malicious code may have been generated with GenAI #NGate #HandyPay
Red Menshen is a China-linked APT that uses a kernel-level, BPF-based backdoor called BPFDoor to establish highly stealthy persistence and packet-triggered command activation inside telecommunications and network edge devices. The group focuses on long-term infrastructure-level espionage by exploiting internet-facing devices, using multi-stage post-exploitation toolchains and covert activation mechanisms to collect communications and metadata at scale. #RedMenshen #BPFDoor

A new LOTUSLITE v1.1 backdoor variant was deployed in targeted campaigns against India’s banking sector and South Korean/U.S. policy circles, using DLL sideloading via Microsoft-signed binaries and CHM/JavaScript-based loaders. Attribution points to Mustang Panda with moderate confidence based on shared code lineage, residual exports (e.g., KugouMain), and reused Dynu-managed C2 infrastructure. #LOTUSLITE #MustangPanda
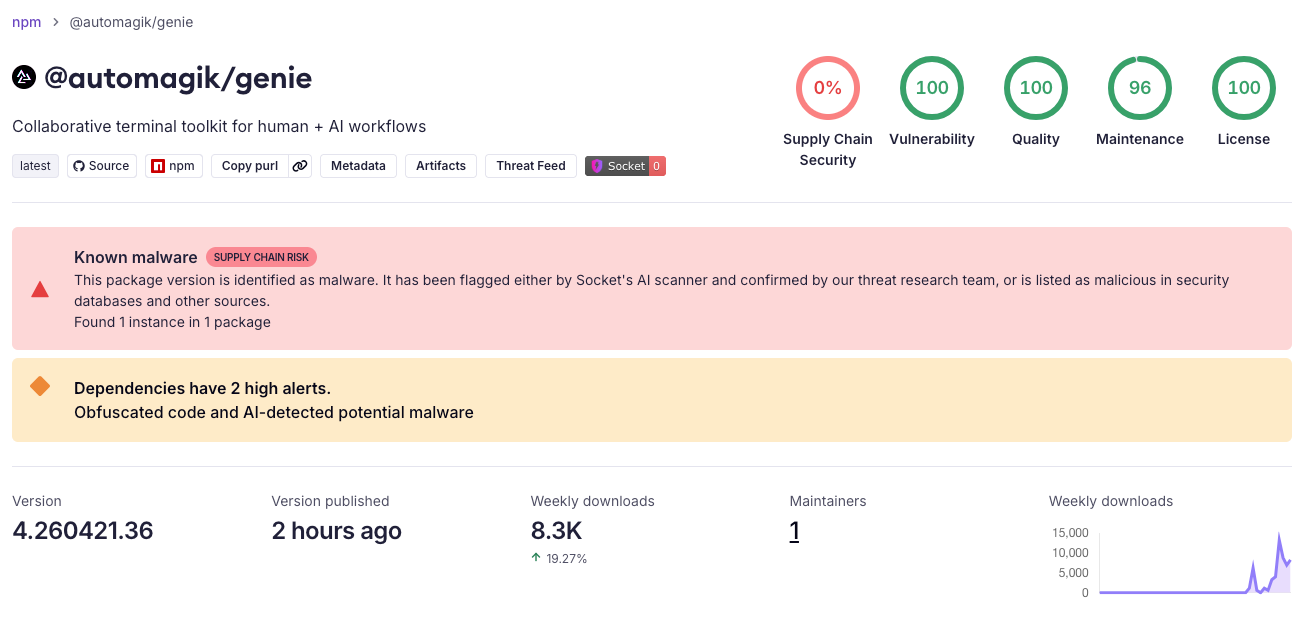
This report describes a worm-enabled npm supply-chain campaign that implanted install-time malware in multiple packages, harvested developer secrets and browser/wallet artifacts, exfiltrated data via an HTTPS webhook and an Internet Computer canister (cjn37-uyaaa-aaaac-qgnva-cai), and attempted self-propagation by republishing compromised packages and targeting PyPI. The activity shows strong tradecraft and code overlap with prior CanisterWorm incidents and is linked to TeamPCP–style supply chain attacks affecting packages tied to Namastex Labs’ Automagik ecosystem. #TeamPCP #NamastexLabs
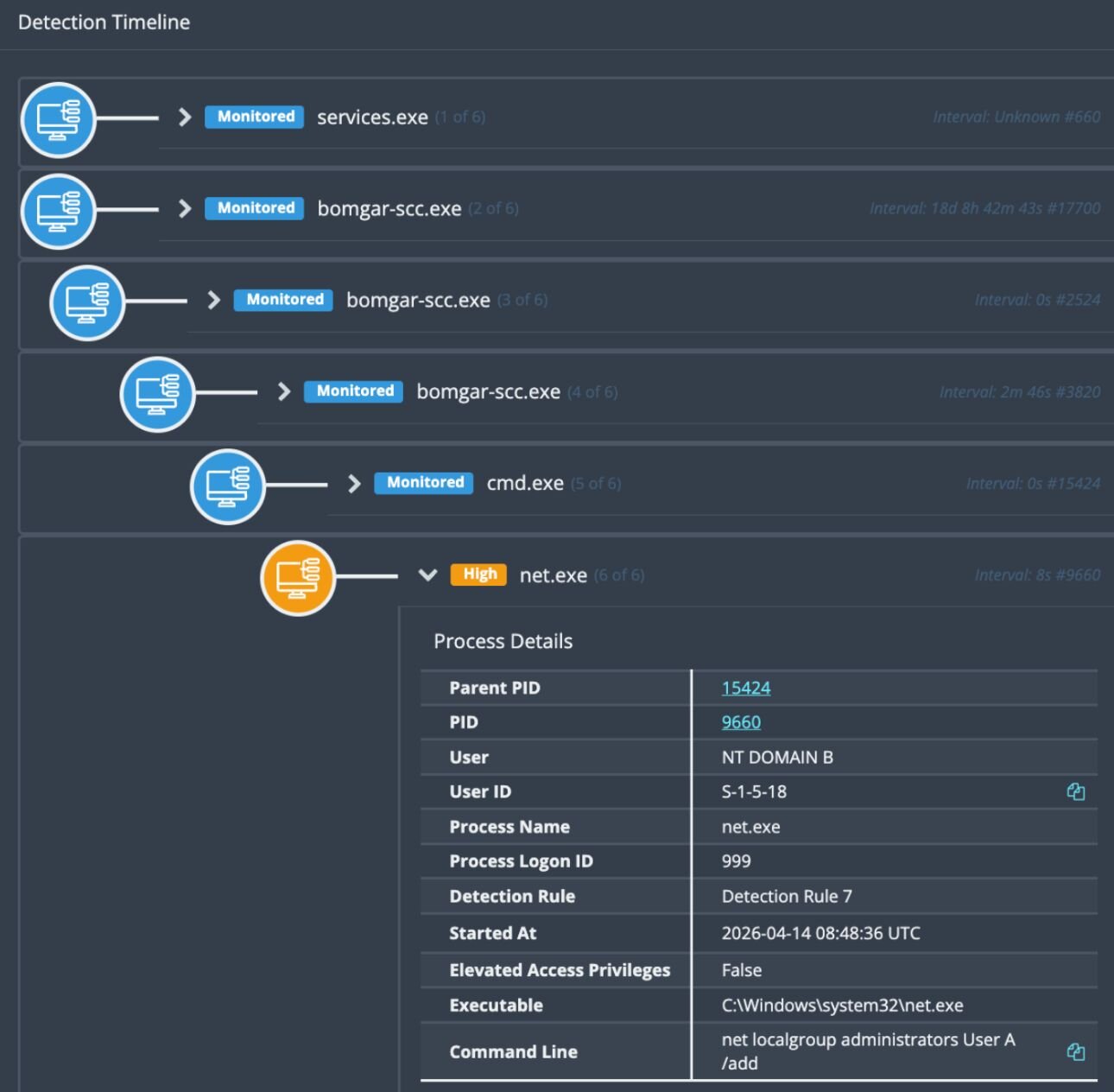
Huntress observed multiple exploitation waves of vulnerable Bomgar (BeyondTrust Remote Support) instances beginning in February and escalating in April 2026, with at least 10 impacted organizations initially and several incidents leading to LockBit ransomware deployments and mass downstream compromises. The attacks leveraged outdated Bomgar versions vulnerable to CVE-2026-1731, with malicious activity traced to processes like bomgar-scc.exe and artifacts including LB3.exe and PoisonX.sys. #Bomgar #LockBit

New AI models such as Anthropic’s Claude Mythos have rapidly accelerated autonomous discovery and exploitation of zero-day vulnerabilities, producing hundreds of working exploits and collapsing time-to-exploitation to hours or less. Security leaders are urged to act immediately by integrating AI-driven defensive tooling, adopting continuous patching and automated response, and following operational guidance like the CSA’s “AI Vulnerability Storm” briefing to become “Mythos-ready” #AnthropicMythos #ProjectGlasswing
A trojanized Antigravity installer downloaded from a typosquat domain (google-antigravity[.]com) ran a single malicious MSI custom-action that dropped PowerShell downloader scripts which checked in to opus-dsn[.]com and could fetch follow-on payloads. When activated, the follow-on payloads disabled Defender/AMSI, staged an encrypted .NET stealer via a fake MicrosoftEdgeUpdate.png delivered from captr.b-cdn[.]net, persisted…
A malicious PDF containing a “CHM оснастка” (CHM snap-in) button triggered the download of sankcionnui-MO-RF.rar from a compromised legitimate site, and numerous similarly named PDFs were identified. Analysis attributes the campaign to the financially motivated CapFix group and confirms the malware is CapDoor, with attackers using spoofed Windows-update domains including windowsextupdates.com as a CapDoor C2. #CapDoor #CapFix
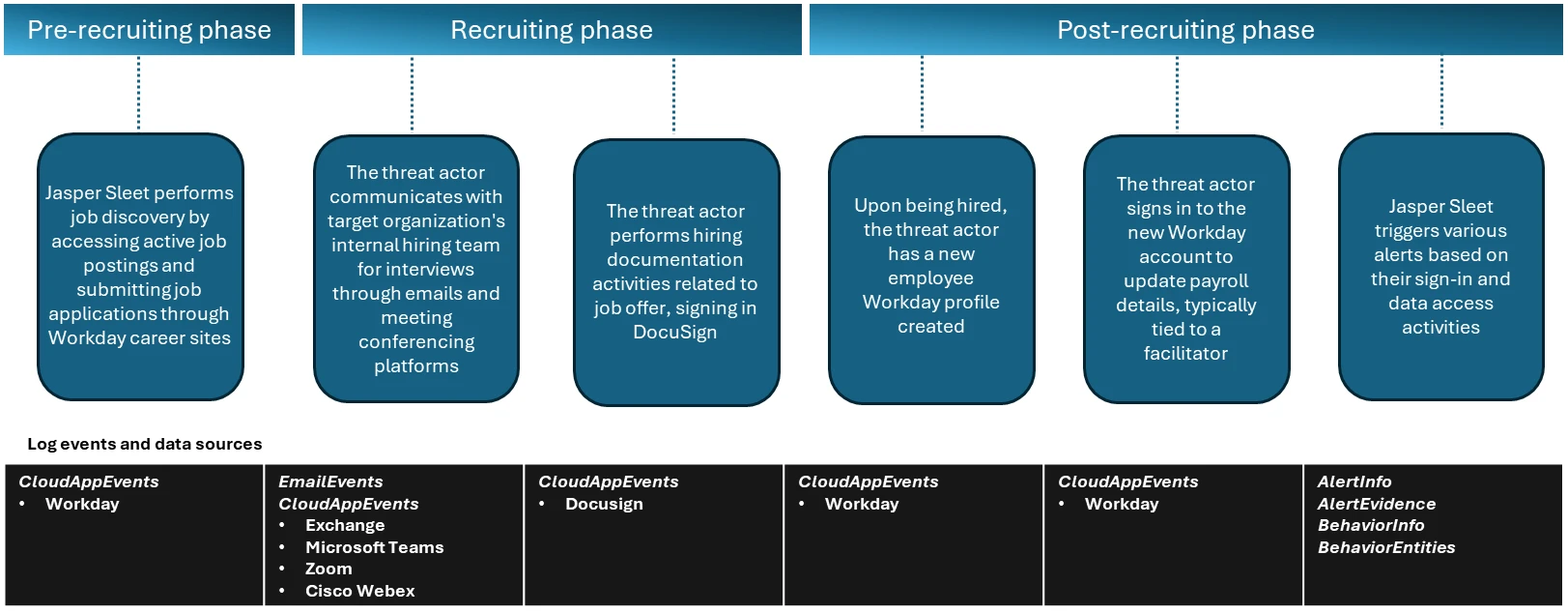
Microsoft observed the North Korea-aligned threat actor Jasper Sleet using stolen or fabricated identities and generative AI to pose as legitimate remote IT hires, abusing Workday and external career-site APIs to infiltrate organizations. The actor leverages external infrastructure and legitimate onboarding workflows to gain valid accounts, set up payroll, and access internal SaaS like Teams, SharePoint, OneDrive, and Exchange Online. #JasperSleet #Workday

Huntress investigated a real-world intrusion that deployed Nightmare-Eclipse tooling (BlueHammer, RedSun, UnDefend) alongside a Go-based reverse tunnel agent dubbed BeigeBurrow and linked activity to likely compromised FortiGate SSL VPN credentials. Artifacts were staged in user-writable folders (Pictures, short Downloads subfolders), operators performed hands-on-keyboard reconnaissance but privilege-escalation attempts largely failed; defenders are urged to urgently review VPN logs, endpoint telemetry, and the specific filenames and indicators observed. #BlueHammer #BeigeBurrow
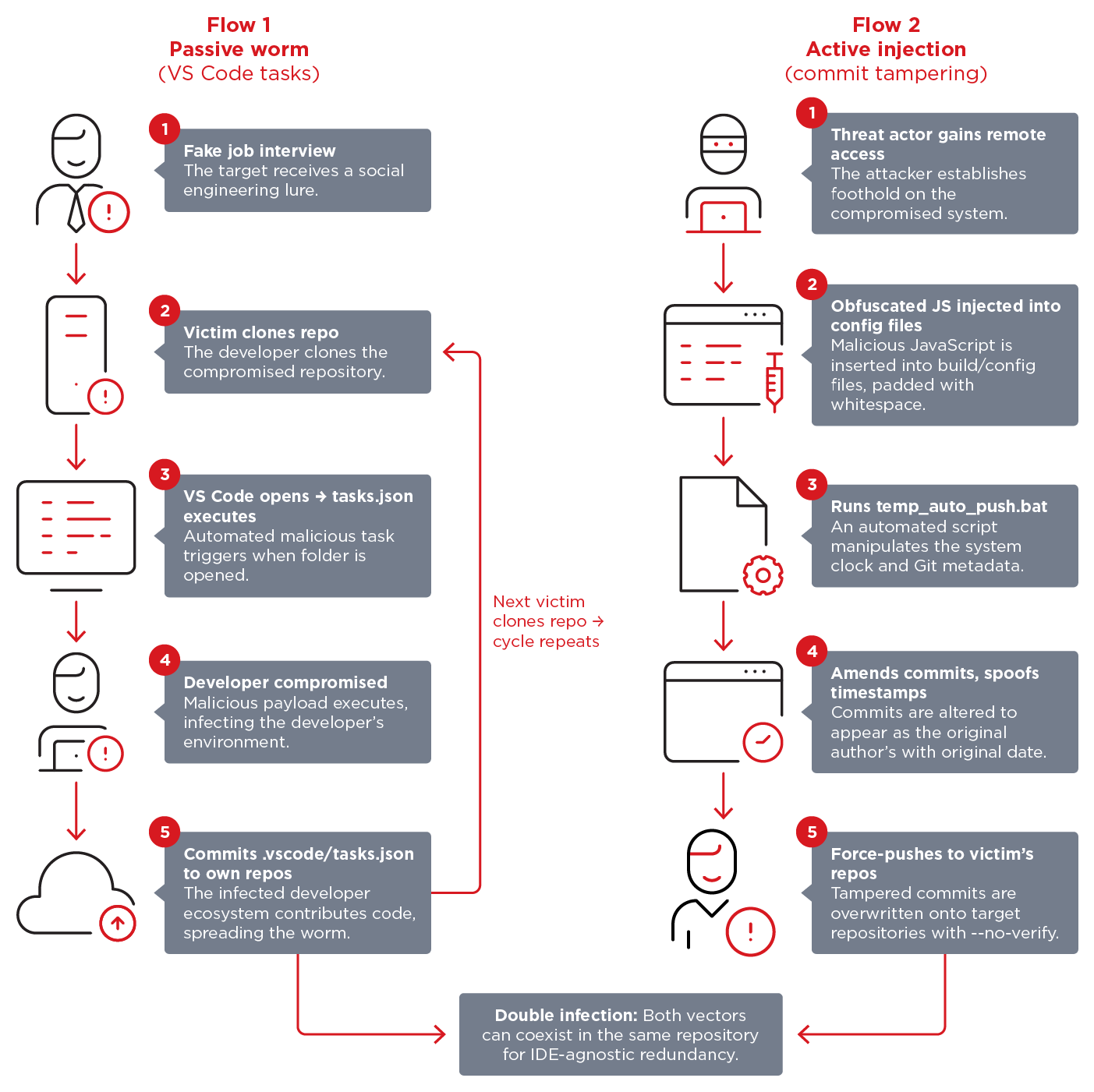
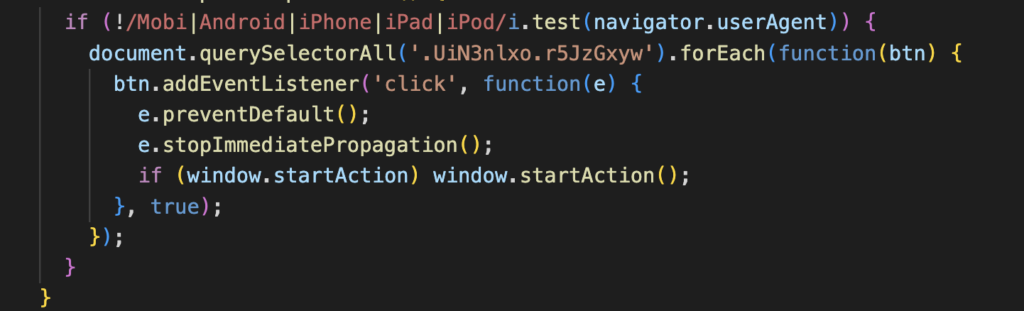
Void Dokkaebi has turned infected developer repositories into self-propagating malware delivery channels by abusing VS Code workspace tasks and injecting obfuscated JavaScript that rewrites git history. The campaign uses blockchain-staged loaders to fetch payloads and has delivered variants such as DEV#POPPER, enabling compromise of individual developers and amplification into organizations like…

LevelBlue’s Global Threat Operations identified a phishing campaign that abuses Microsoft’s OAuth 2.0 Device Authorization Grant (Device Code Flow) using a fake Adobe-themed site and compromised redirection infrastructure to obtain access and refresh tokens. The report documents the attack chain, key indicators such as hxxps://adobe.safest.org/ and Mandrill-based redirects, detection KQL queries, and recommendations including blocking Device Code Flow in Conditional Access Policies #Microsoft #DeviceCodeFlow

On 26 Mar 2026 a researcher released BlueHammer, a local privilege-escalation PoC abusing a TOCTOU race in Microsoft Defender’s update handling (linked to CVE-2026-33825), and subsequent PoCs RedSun and UnDefend demonstrated additional escalation and Defender-update disruption techniques. Huntress Labs warned actors are attempting to operationalize these tools, and Microsoft patched the core BlueHammer flaw in the April 14, 2026 Patch Tuesday updates. #BlueHammer #RedSun
Netskope Threat Labs details a ClickFix campaign delivering an AppleScript-based macOS infostealer that forces victims to enter their system password via a non-closable dialog and harvests keychain data, browser cookies, saved credentials, extension data, and desktop cryptocurrency wallets. The campaign uses user-agent filtering and paste-into-terminal social engineering to deliver platform-specific payloads and exfiltrates collected data to a hardcoded command-and-control server. #ClickFix #macOS