Huntress observed multiple exploitation waves of vulnerable Bomgar (BeyondTrust Remote Support) instances beginning in February and escalating in April 2026, with at least 10 impacted organizations initially and several incidents leading to LockBit ransomware deployments and mass downstream compromises. The attacks leveraged outdated Bomgar versions vulnerable to CVE-2026-1731, with malicious activity traced to processes like bomgar-scc.exe and artifacts including LB3.exe and PoisonX.sys. #Bomgar #LockBit
Keypoints
- Multiple exploitation waves of Bomgar RMM were observed beginning Feb 12 and rising again around April 3, 2026, impacting managed service providers and customer downstream networks.
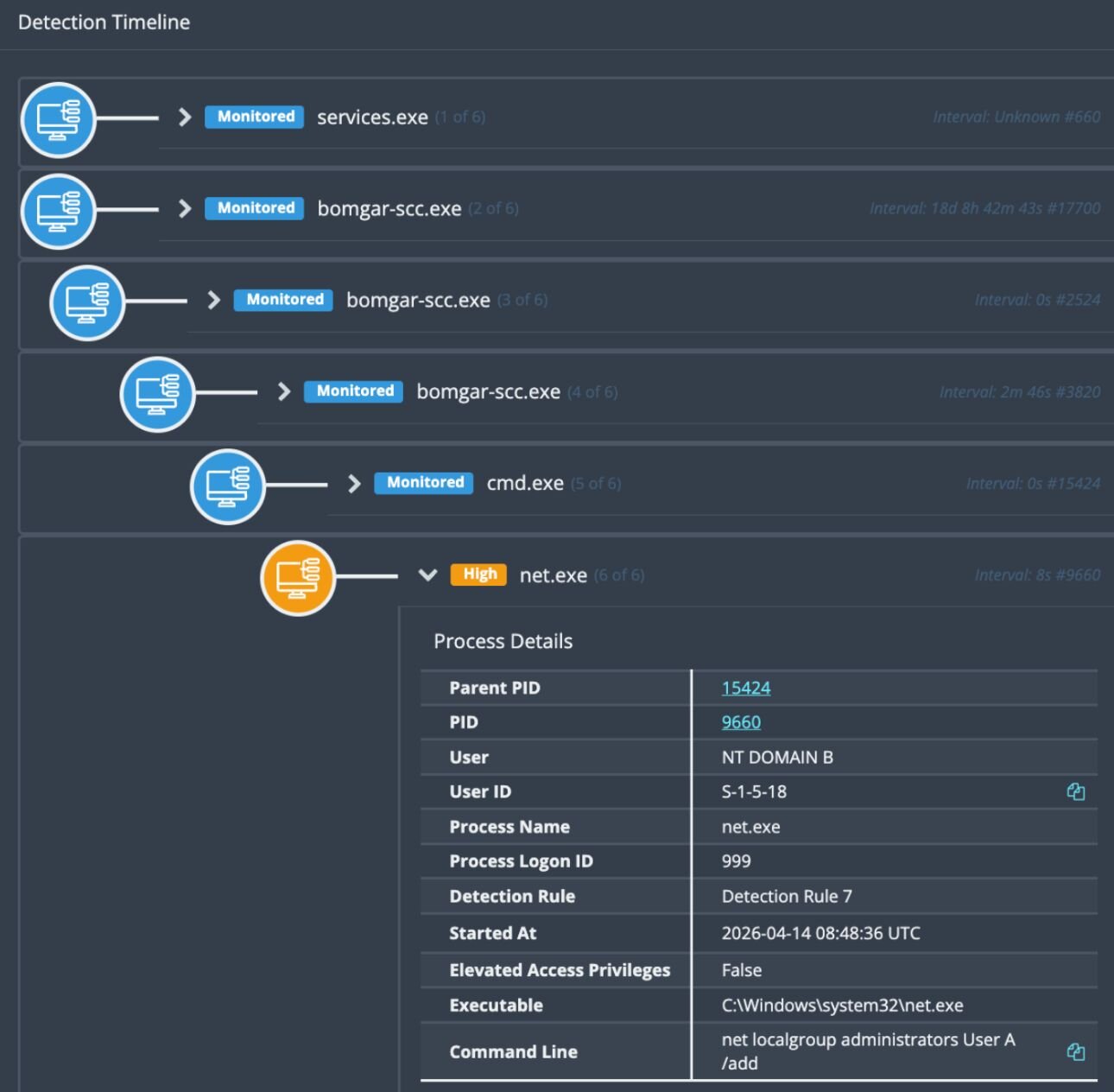
- Attackers exploited vulnerable/outdated Bomgar versions (CVE-2026-1731) to gain remote code execution and SYSTEM-level access via Bomgar remote shell sessions.
- Compromised Bomgar instances were used to create local and domain administrator accounts for persistence and lateral movement, often adding accounts to Local Administrators and Domain Admins groups.
- Threat actors deployed Remote Access Tools (AnyDesk, ScreenConnect, Atera), performed network/domain reconnaissance (nltest, NetScan), and installed ransomware (LB3.exe / LockBit) in multiple incidents.
- Defense-evasion techniques included deploying suspicious drivers (PoisonX.sys, hrwfpdrv.sys) and abusing legitimate binaries (HRSword.exe) to disable security tooling.
- Notable incidents: April 14 dental software compromise spreading ransomware to downstream orgs, and April 15 MSP compromise leading to mass isolation of 78 businesses and downstream exploitation.
MITRE Techniques
- [T1219 ] Remote Access Tools – Deployed and executed third-party remote access/management tools for persistence and remote control (‘deployed additional remote access tools including AnyDesk (C:UserssupportDocumentsAnyDesk.exe)’ and ‘installer for the Atera remote management tool’).
- [T1136 ] Create Account – Actors created new local accounts and added them to administrative groups to establish persistence (‘create a new local account, and elevate it first into the Local Administrators Group and then into Domain Admins’).
- [T1046 ] Network Service Scanning – Network enumeration was performed using NetScan to map and target network assets (‘execute NetScan, a network enumeration tool’).
- [T1087 ] Account Discovery – Domain reconnaissance and account discovery were performed using nltest and similar tools (‘performed domain reconnaissance (via nltest.exe)’).
- [T1053 ] Scheduled Task/Job – Persistence via scheduled task creation was observed (AteraAgentServiceWatchdog was created) (‘a scheduled task was created (AteraAgentServiceWatchdog)’).
- [T1486 ] Data Encrypted for Impact – Ransomware (LockBit / LB3.exe) was executed to encrypt endpoints and impact organizations (‘executed the ransomware binary… resulting in the successful encryption of the endpoint via LB3.exe’).
- [T1218 ] Signed Binary Proxy Execution – Legitimate binaries were abused to bypass defenses (HRSword.exe was used by actors to evade security) (‘the SOC also observed the actor using HRSword.exe, which is legitimate software abused by cybercriminals to bypass security defenses’).
Indicators of Compromise
- [File Hashes ] Ransomware and dropped tools – LB3.exe SHA256: 538b3b36dd8a30e721cc8dc579098e984cf8ed30b71d55303db45c7344f7a4cf, LB3.exe SHA256: 3529b1422da886b7d04555340dfb1efd44a625c2921af6df39819397176956d6, and other hashes (InputUpdate.exe, HRSword.exe, PoisonX.sys).
- [File Names / Executables ] Malicious and abused binaries observed – bomgar-scc.exe (malicious Bomgar process), LB3.exe (ransomware executable), and other artifacts like InputUpdate.exe and AnyDesk.exe.
- [Drivers ] Kernel/driver artifacts used to disable defenses – PoisonX.sys (SHA256: a5035cbd6c31616288aa66d98e5a25441ee38651fb5f330676319f921bb816a4), hrwfpdrv.sys (used by threat actor).
- [IP Addresses ] C2 / configured RMM endpoint – 146.70.41[.]131 (IP configured to renamed SimpleHelp RMM observed March 11).
- [Credentials / Passwords ] Attacker-set credentials observed – Adminpwd123.1 (password added by attacker), 123123qwEqwE (WDAGUtilityAccount password observed when added to Administrator group).
- [Email Addresses ] Ransom note contact – lokbt9@onionmail[.]org (email included in ransom notes from April incidents).
Read more: https://www.huntress.com/blog/uptick-bomgar-exploitation