Void Dokkaebi has turned infected developer repositories into self-propagating malware delivery channels by abusing VS Code workspace tasks and injecting obfuscated JavaScript that rewrites git history. The campaign uses blockchain-staged loaders to fetch payloads and has delivered variants such as DEV#POPPER, enabling compromise of individual developers and amplification into organizations like DataStax and Neutralinojs #VoidDokkaebi #DEVPOPPER
Keypoints
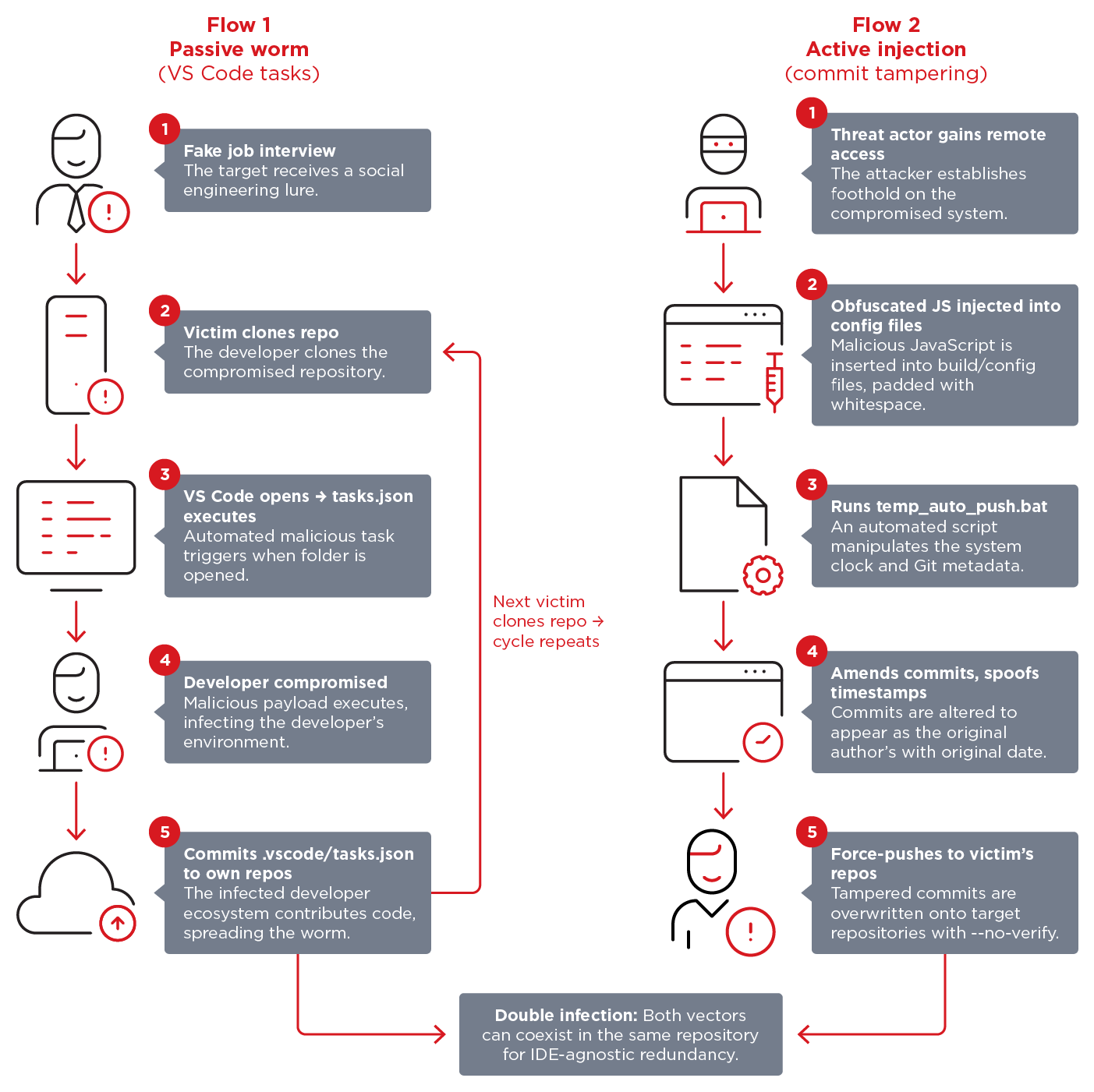
- Void Dokkaebi (aka Famous Chollima) uses fake interview lures to get developers to clone and open repositories that execute malicious VS Code workspace tasks or embedded payload files.
- Two complementary propagation mechanisms are used: passive spread via .vscode/tasks.json (runOn: folderOpen) and active injection of obfuscated JavaScript combined with git commit tampering.
- The injected JavaScript is a multistage blockchain-staged loader that pulls encrypted payloads from Tron, Aptos, and Binance Smart Chain transactions and decrypts them at runtime.
- One delivered payload is a DEV#POPPER RAT variant that uses WebSocket and HTTP-based C2, multi-operator session queues, and avoids CI/CD environments to target real developer workstations.
- TrendAI identified over 750 infected repositories, 392 downloader tasks.json files, 131 font/image launcher tasks, and 101 instances of the commit-tampering tool (temp_auto_push.bat) in March 2026.
- When infections reach organizational or popular open-source repositories (e.g., DataStax, Neutralinojs), the campaign amplifies to contributors, forks, and downstream projects, creating a cascading supply chain risk.
MITRE Techniques
- [T1195 ] Supply Chain Compromise – The threat converts developer repositories into delivery channels that infect downstream projects and contributors (‘A compromised developer’s repository becomes an infection vector for the next wave of victims’)
- [T1204 ] User Execution – Victims are tricked into cloning and opening repositories during fake interviews, triggering workspace tasks when trust is granted (‘clone and execute code repositories as part of fabricated job interviews’)
- [T1059.007 ] Command and Scripting Interpreter: JavaScript – Obfuscated JavaScript is appended to source/config files and executed by Node.js tooling as a multistage loader (‘obfuscated JavaScript… is added to the end of the file’ and ‘evaluated as JavaScript by Node.js tooling’)
- [T1027 ] Obfuscated Files or Information – The loader uses string shuffling, hex obfuscation, and character swaps to hinder analysis (‘layers of string shuffling, hexadecimal obfuscation, and character swap algorithms to hinder analysis’)
- [T1070.006 ] Timestomp (Indicator Removal on Host) – The commit-tampering script temporarily alters the system clock and amends commits to preserve original timestamps and authorship (‘temporarily alter the system clock to match the original commit’s timestamp’)
- [T1071.001 ] Application Layer Protocol: Web Protocols – DEV#POPPER uses WebSocket (socket.io-client) and HTTP endpoints for C2, heartbeats, and exfiltration (‘communicates with its command-and-control (C&C) server via WebSocket (using socket.io-client)’ and ‘/verify-human/[VERSION]’ and ‘/u/f’)
- [T1574 ] Hijack Execution Flow – Persistence achieved by creating a hidden .node_modules folder to hijack Node.js module search order and injecting versioned code into developer tooling (‘creates a hidden .node_modules folder for Node.js module search order hijacking’ and ‘injects versioned code… into developer applications’)
Indicators of Compromise
- [File names ] repository and tooling artifacts used as delivery/persistence – .vscode/tasks.json, temp_auto_push.bat
- [Configuration files ] targeted config/entry files where JS is appended – postcss.config.mjs, tailwind.config.js (also eslint.config.mjs, next.config.mjs)
- [String markers ] code and loader signatures found in infected files – global[‘!’], global[‘_V’], and version markers C250617A through C250620A
- [Domains / APIs ] blockchain and fallback endpoints used for staging – api.trongrid.io, fullnode.mainnet.aptoslabs.com (and Binance Smart Chain RPC endpoints)
- [Network paths / URLs ] RAT communication and exfiltration patterns – /verify-human/[VERSION], /u/f
- [IP addresses ] C2 / infrastructure observed in hunting queries – 198.105.127.210, 23.27.202.27, and other 7 addresses
- [Repositories / organizations ] affected code sources identified during analysis – DataStax repositories, Neutralinojs repositories