Netskope Threat Labs details a ClickFix campaign delivering an AppleScript-based macOS infostealer that forces victims to enter their system password via a non-closable dialog and harvests keychain data, browser cookies, saved credentials, extension data, and desktop cryptocurrency wallets. The campaign uses user-agent filtering and paste-into-terminal social engineering to deliver platform-specific payloads and exfiltrates collected data to a hardcoded command-and-control server. #ClickFix #macOS
Keypoints
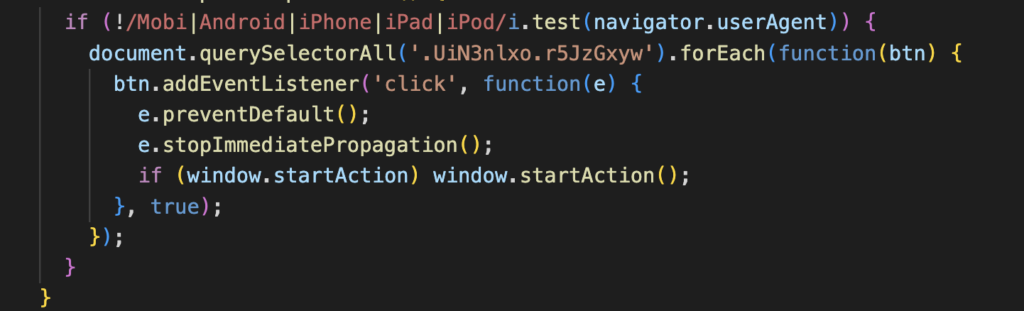
- ClickFix campaign uses client-side user-agent filtering to funnel desktop victims into OS-specific payloads, serving an AppleScript loader to macOS users and a NodeJS-based RAT to Windows users.
- The macOS payload deploys a persistent, non-closable AppleScript dialog that mimics a legitimate system prompt and validates the entered password via macOS Directory Services until the correct password is provided.
- The stealer prioritizes harvesting live session cookies from 12 Chromium-based browsers and collects saved passwords, autofill data, extension storage, and IndexedDB contents from 200+ browser extensions.
- The malware extracts the macOS Keychain (login.keychain-db) by capturing the plaintext login password via the deceptive dialog, removing the need to brute-force or crack encrypted keychain files.
- Attackers copy entire directories for 16 desktop cryptocurrency wallets and extension storages—potentially exposing private keys, seed phrases, and unencrypted wallet files.
- Collected data is staged in /tmp/xdivcmp/, compressed with ditto, exfiltrated via HTTP POST to a hardcoded C2 (e.g., http://172.94.9.250), and staging artifacts are deleted after successful upload; macOS updates (Tahoe 26.4 / Sequoia) introduce Terminal paste warnings to mitigate this tactic.
MITRE Techniques
- [T1059.006 ] AppleScript – Used as the platform-specific loader and to present the persistent credential prompt via AppleScript. (‘AppleScript-based loader’ / ‘deceptive AppleScript dialog box’)
- [T1204 ] User Execution – The campaign relies on social engineering that “lures victims into manually copying and pasting a malicious command” into a terminal or Run dialog to start execution. (‘lures victims into manually copying and pasting a malicious command’)
- [T1539 ] Steal Web Session Cookie – The stealer collects live session cookies from multiple browsers to enable session hijacking and MFA bypass. (‘harvest a wide range of sensitive data, including … live session cookies from 12 different browsers’)
- [T1555 ] Credentials from Password Stores – The malware extracts the macOS Keychain (login.keychain-db) and saved browser credentials by capturing the user’s plaintext password. (‘One of the script’s primary objectives is the extraction of the macOS Keychain’ / ‘login.keychain-db is a database file encrypted with AES-256’)
- [T1074 ] Data Staged – Collected artifacts are organized into a temporary staging directory (/tmp/xdivcmp/) prior to compression and exfiltration. (‘creates a temporary staging directory at /tmp/xdivcmp/’)
- [T1041 ] Exfiltration Over C2 Channel – Staged data is compressed and exfiltrated to the attacker’s server via an HTTP POST to a hardcoded C2 address. (‘exfiltrated via HTTP POST to the attacker’s command and control server’)
Indicators of Compromise
- [IP Address ] Command-and-control server – http://172.94.9.250
- [Directory / File path ] Staging and keychain artifacts – /tmp/xdivcmp/, Keychains/login.keychain-db
- [File / Database names ] Browser and credential artifacts – cookies.sqlite, login.keychain-db, logins.json
- [Campaign identifier ] Hardcoded build/campaign ID – e12285f507c847b986233991b86b22e3
- [Detection signatures ] Vendor detections reported by Netskope – Trojan.Generic.39744155, Script.Trojan.Heuristic
Read more: https://www.netskope.com/blog/macos-clickfix-campaign-applescript-stealers-new-terminal-protections