LevelBlue’s Global Threat Operations identified a phishing campaign that abuses Microsoft’s OAuth 2.0 Device Authorization Grant (Device Code Flow) using a fake Adobe-themed site and compromised redirection infrastructure to obtain access and refresh tokens. The report documents the attack chain, key indicators such as hxxps://adobe.safest.org/ and Mandrill-based redirects, detection KQL queries, and recommendations including blocking Device Code Flow in Conditional Access Policies #Microsoft #DeviceCodeFlow
Category: Threat Research

On 26 Mar 2026 a researcher released BlueHammer, a local privilege-escalation PoC abusing a TOCTOU race in Microsoft Defender’s update handling (linked to CVE-2026-33825), and subsequent PoCs RedSun and UnDefend demonstrated additional escalation and Defender-update disruption techniques. Huntress Labs warned actors are attempting to operationalize these tools, and Microsoft patched the core BlueHammer flaw in the April 14, 2026 Patch Tuesday updates. #BlueHammer #RedSun
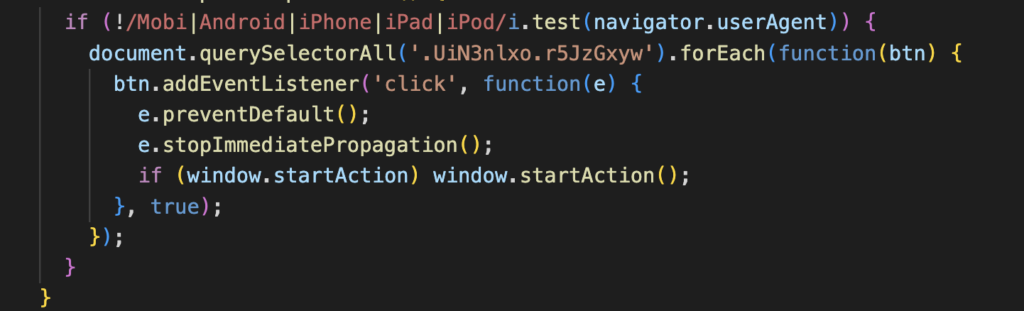
Netskope Threat Labs details a ClickFix campaign delivering an AppleScript-based macOS infostealer that forces victims to enter their system password via a non-closable dialog and harvests keychain data, browser cookies, saved credentials, extension data, and desktop cryptocurrency wallets. The campaign uses user-agent filtering and paste-into-terminal social engineering to deliver platform-specific payloads and exfiltrates collected data to a hardcoded command-and-control server. #ClickFix #macOS
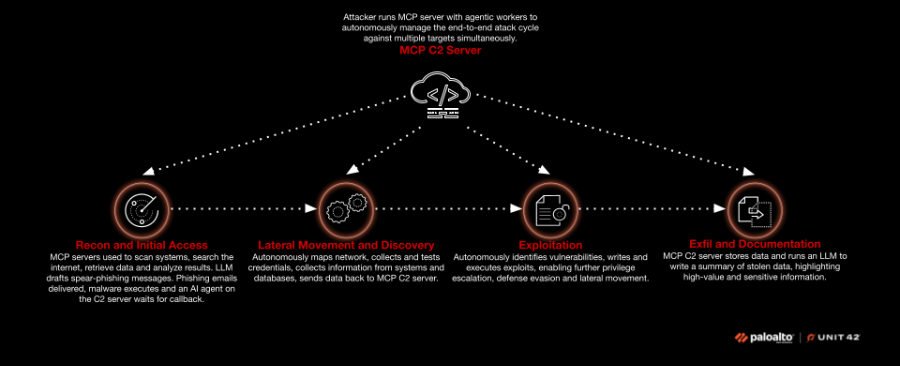
Unit 42 warns frontier AI models can autonomously discover vulnerabilities, collapse the patching window from days to hours, and enable AI-driven exploit chains that accelerate and scale attacks across the entire attack lifecycle. The report highlights elevated risks to open-source software and supply chains and urges immediate measures such as assumed-breach…
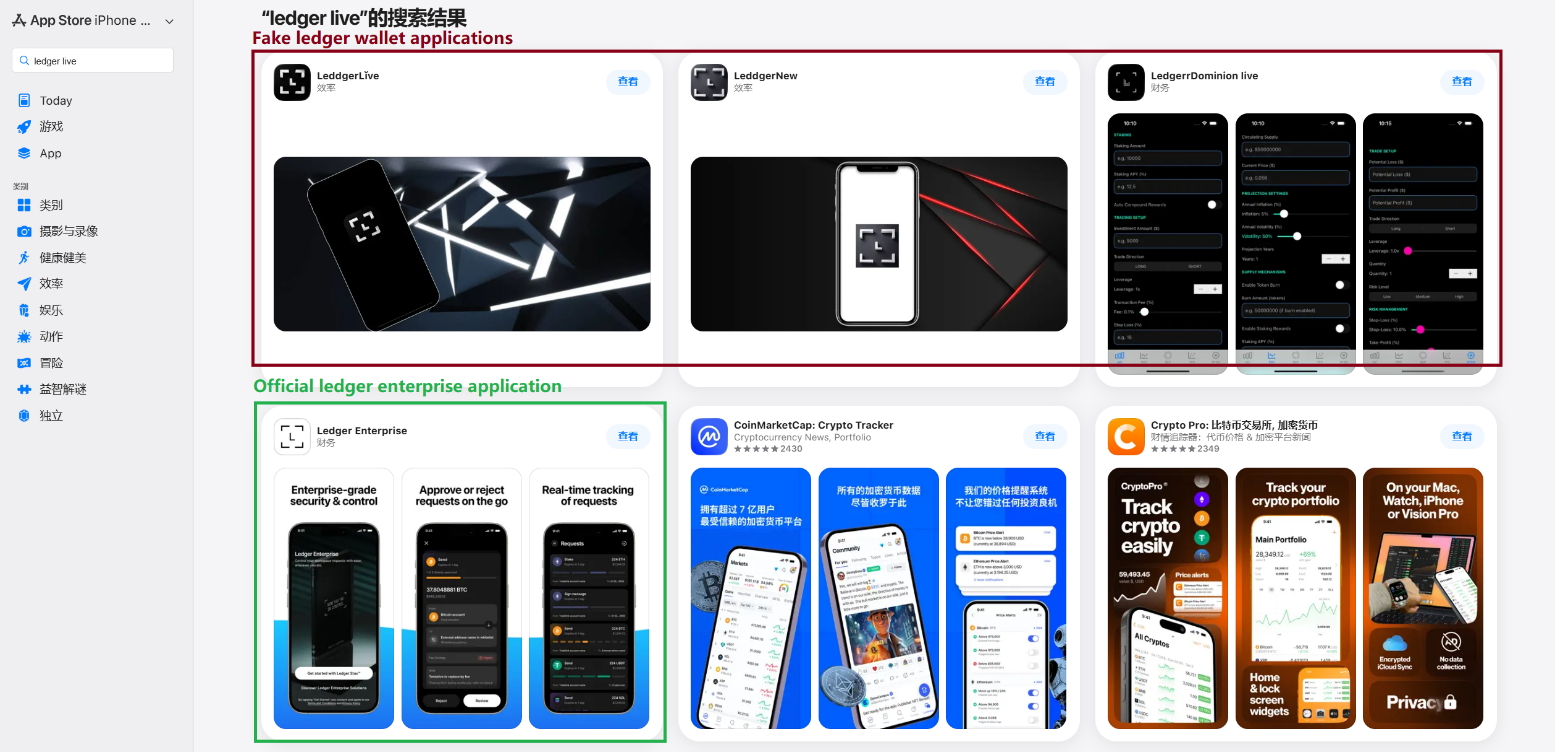
In March 2026 researchers uncovered over twenty App Store phishing apps that redirect victims to browser pages and provisioning-profile installers that deploy trojanized versions of popular crypto wallets to steal recovery phrases and private keys. The campaign, active since at least fall 2025, uses library injection and source-code tampering to scrape mnemonics and exfiltrate them to hardcoded C2 servers. #FakeWallet #SparkKitty
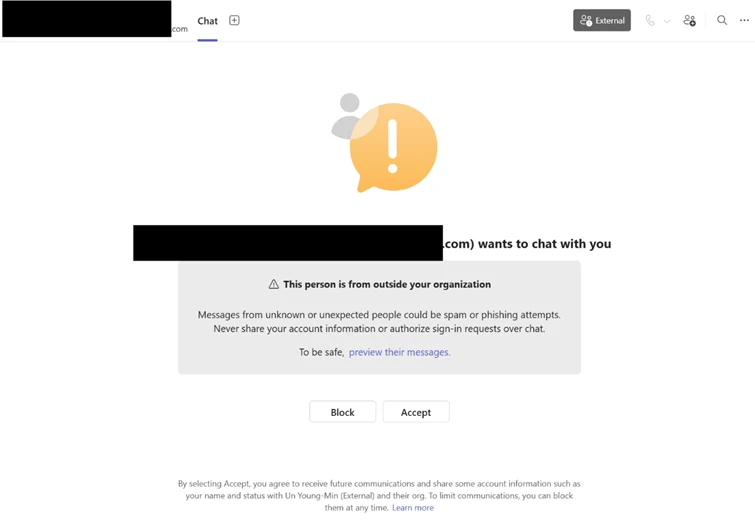
Attackers impersonate IT/help‑desk via cross‑tenant Microsoft Teams chats and calls (often with vishing) to socially engineer users into launching remote support tools like Quick Assist, granting interactive control, and approving elevation prompts; they then perform rapid reconnaissance, stage payloads via DLL side‑loading, and establish HTTPS command‑and‑control before pivoting via WinRM and deploying auxiliary management tooling. Defenders should prioritize user education, enforce Conditional Access and MFA, restrict remote management tools and WinRM, enable Safe Links and ZAP for Teams, and apply ASR/WDAC to prevent sideloading and detect Rclone exfiltration. #QuickAssist #Rclone
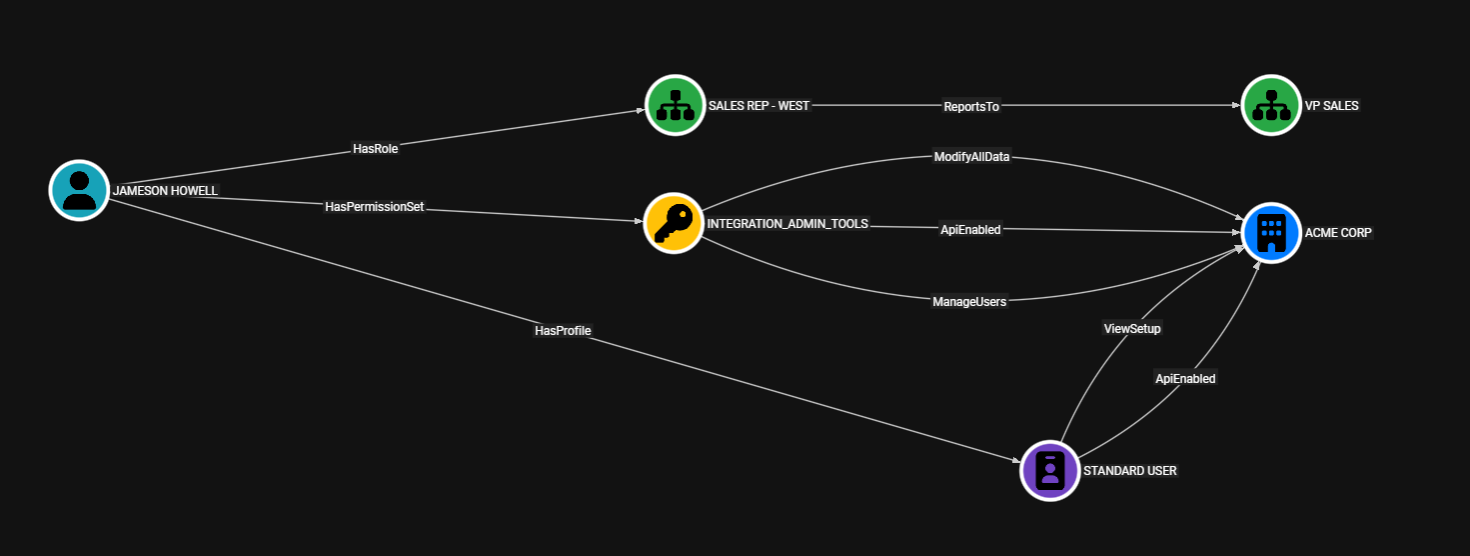
ForceHound is an open-source Python collector that builds a BloodHound CE identity graph to help audit Salesforce orgs by visualizing profiles, permission sets, roles, connected apps, field- and record-level sharing, and system capabilities. The post details collection modes (API, Aura, both), empirical CRUD probing, BloodHound CE integration, audit logging, scope-control flags, and frames urgency after the UNC6040 campaign that abused malicious Connected Apps. #ForceHound #UNC6040
CYFIRMA analyzed a sophisticated multi-stage post-exploitation framework that hijacks the .NET AppDomainManager to execute malicious code inside a legitimately signed Intel utility (IAStorHelp.exe), combining JIT-based shellcode, reflective loading, direct syscalls, and CDN-based domain fronting to evade detection. The campaign targets Middle East and EMEA financial organizations with strong sandbox-evasion, encrypted payloads, heap-based resilience, and anti-forensic memory teardown enabling stealthy C2 via Amazon CloudFront. #IAStorHelp #AppDomainManager
ForceHound extracts Salesforce identity and entitlement data and uploads it into BloodHound so defenders and attackers can query graph paths that reveal transitive privilege escalation and connected‑app exposures. Using targeted Cypher queries, the tool exposes paths from standard users to high‑value capabilities (e.g., ModifyAllData, AuthorApex, ApiEnabled) and highlights legacy Connected App authorizations that remain dangerous despite Salesforce’s 2025 restrictions. #ForceHound #Salesforce
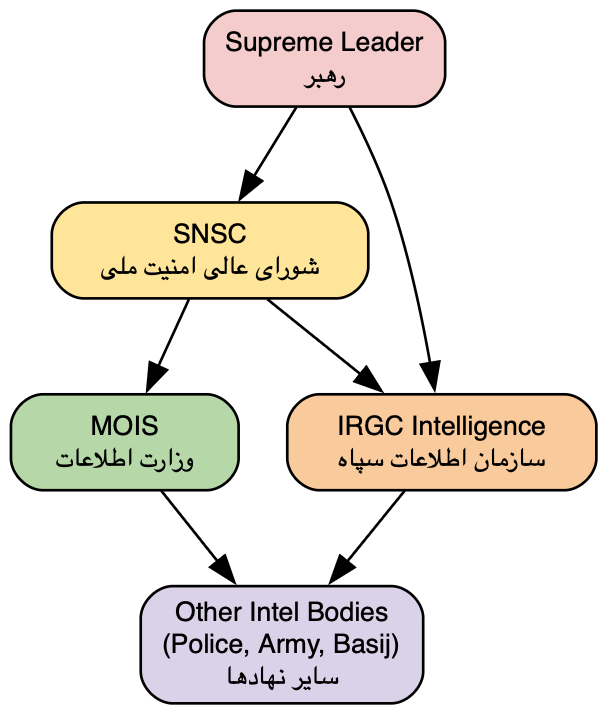
The report assesses that the Homeland Justice, Karma, and Handala personas are coordinated layers of a single MOIS-aligned cyber influence ecosystem that integrates intrusion, destructive tooling, surveillance, and narrative operations rather than representing independent hacktivist groups. The campaign evolved from 2022 Albania destructive intrusions into a modular hack-and-leak and Telegram-driven surveillance apparatus implicated in events including the Stryker Intune-based mass wipe and multiple targeted leak and doxxing operations. #Handala #MOIS
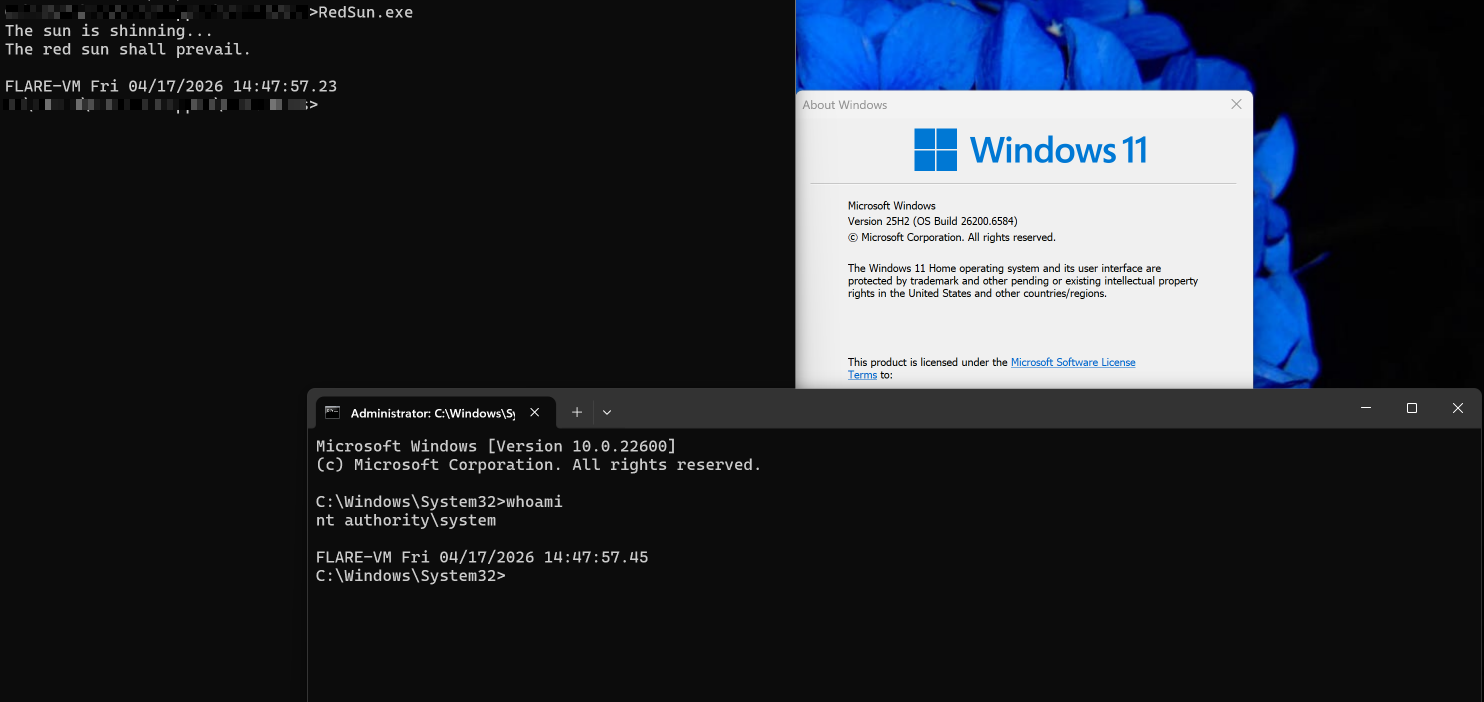
A logic flaw in Windows Defender’s remediation path (MpSvc.dll) allows a local unprivileged user to race a restore operation and redirect Defender to write an attacker-controlled binary into C:WindowsSystem32, enabling SYSTEM code execution. The public PoC exploit “RedSun” chains Cloud Files placeholders, a batch OPLOCK, VSS monitoring, and a junction (mount point) swap to reliably achieve elevation without kernel exploits or admin privileges. #RedSun #WindowsDefender
CYFIRMA discovered a multi-stage, APT-grade post-exploitation framework that hijacks the .NET AppDomainManager to execute attacker code inside the legitimately signed Intel utility IAStorHelp.exe and load a reflective, encrypted payload. The framework combines sandbox exhaustion, JIT trampoline in-memory execution, direct ntdll syscalls, and CloudFront domain fronting for resilient C2 while employing anti-forensic memory teardown techniques. #IAStorHelp #CloudFront
NightSpire is a financially motivated ransomware and data extortion group that emerged in early 2025, using double extortion via a dedicated leak site and has recently launched a RaaS program to expand operations. Its Go-based payload appends the .nspire extension, uses hybrid partial/full encryption, leverages living-off-the-land tools (PowerShell, WMI, PsExec) and…

Multiple malware campaigns in March 2026 targeted Korean and global financial institutions using phishing (Korean-language attachments, HTML/JS), web shells, droppers, backdoors, downloaders, infostealers, and CoinMiner to achieve compromise and persistence. Notable incidents included a Lazarus watering‑hole exploit of AnySign4PC causing RCE, Telegram API account compromises (~4% financial sector impact), large dark‑web…

Payouts King is a ransomware family that emerged in April 2025 and is attributed to former BlackBasta affiliates, using social-engineering (spam bombing, phishing, vishing) and misuse of Microsoft Teams/Quick Assist to gain initial access. The malware employs extensive obfuscation, direct system calls to evade EDR, scheduled-task persistence, and 4096-bit RSA + AES-256-CTR for selective file encryption. #PayoutsKing #BlackBasta
