The report assesses that the Homeland Justice, Karma, and Handala personas are coordinated layers of a single MOIS-aligned cyber influence ecosystem that integrates intrusion, destructive tooling, surveillance, and narrative operations rather than representing independent hacktivist groups. The campaign evolved from 2022 Albania destructive intrusions into a modular hack-and-leak and Telegram-driven surveillance apparatus implicated in events including the Stryker Intune-based mass wipe and multiple targeted leak and doxxing operations. #Handala #MOIS
Keypoints
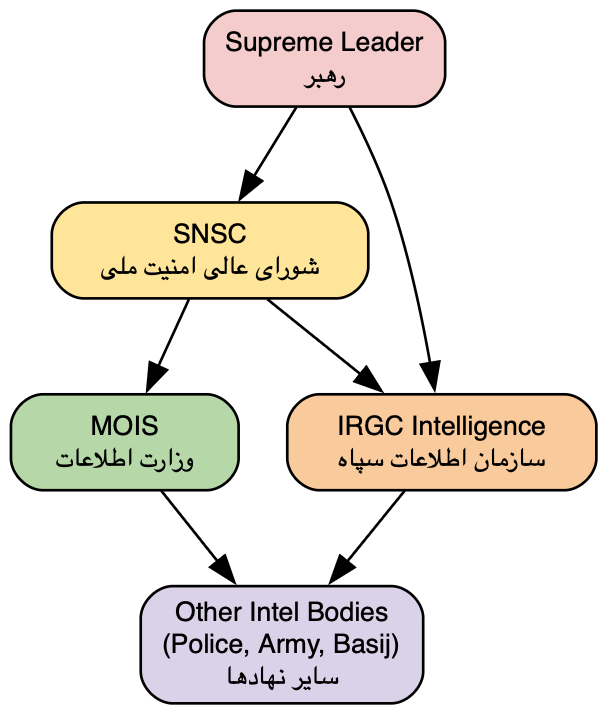
- Homeland Justice, Karma (KarmaBelow80), and Handala are assessed as a single, centrally coordinated operational ecosystem aligned with Iran’s Ministry of Intelligence and Security (MOIS), sharing infrastructure, tradecraft, and objectives.
- The campaign’s lifecycle follows repeatable phases: long-dwell access (exploitation, webshells), credential harvesting and lateral movement, data exfiltration, and then either destructive action or curated public leaks amplified via domains and Telegram.
- Tooling evolved from bespoke ransomware/wipers (GoXML, cl.exe, No-Justice Wiper, BiBi Wiper, handala.exe) to a hybrid model using living-off-the-land techniques, signed binaries, enterprise tooling (NetBird, ADRecon), and abuse of management planes (Microsoft Intune in the Stryker incident).
- Telegram is used dual-use: as covert command-and-control via the Bot API for exfiltration and control, and as an overt amplification channel (channels/handles and domain anchors) for influence, intimidation, and narrative shaping.
- Operational effects are primarily psychological and reputational (hack-and-leak influence), with selective but significant disruptive incidents (notably Stryker) and person-centric surveillance/doxxing targeting dissidents and officials.
- Domain rotation and persona rebranding (handala-hack[.]to/.tw/.ps, handala-redwanted, homelandjustice[.]org/info, karmabelow80) provide resilience, segmentation of narrative roles, and attribution obfuscation while preserving a persistent backend capability.
- The campaign demonstrates increasing sophistication and convergence: surveillance implants, Telegram-based C2, enterprise-control-plane abuse, and coordinated multi-vector destruction enable rapid, scalable impact aligned with state objectives.
MITRE Techniques
- [T1190 ] Exploit Public-Facing Application – Used for initial long-dwell access (e.g., “exploiting an internet-facing Microsoft SharePoint vulnerability”) [‘exploiting an internet-facing Microsoft SharePoint vulnerability’]
- [T1059 ] Command and Scripting Interpreter – PowerShell and CLI used throughout for payload delivery and execution [‘PowerShell-based propagation reflects a growing reliance on native system capabilities’]
- [T1059.001 ] PowerShell – PowerShell scripts used for propagation, execution, and destructive actions [‘PowerShell-based propagation reflects a growing reliance on native system capabilities’]
- [T1505.003 ] Web Shell – Webshells deployed to maintain durable access on IIS/web servers [‘Webshells were deployed on compromised servers, providing durable and low-friction access’]
- [T1078 ] Valid Accounts – Credential harvesting and reuse for lateral movement and privileged access [‘obtained privileged credentials that enabled lateral movement and escalation’]
- [T1070 ] Indicator Removal on Host – File deletion and other cleanup to evade detection [‘file deletion’ and defenses impaired during operations] [‘file deletion’ quoted as part of defense evasion’]
- [T1003.001 ] LSASS Memory – Memory dumping to extract credentials for escalation and lateral movement [‘dump LSASS memory and obtain plaintext credentials or hashes’]
- [T1087 ] Account Discovery – Internal reconnaissance to enumerate accounts and trust relationships [‘systematic internal reconnaissance, enumerating network topology, identifying key systems’]
- [T1021.001 ] Remote Desktop Protocol (RDP) – RDP used for lateral movement and administrative access [‘Movement across the environment was conducted using … RDP’]
- [T1021.002 ] Server Message Block (SMB) – SMB used for lateral movement and propagation [‘Movement across the environment was conducted using … SMB’]
- [T1114.002 ] Remote Email Collection – Exchange compromises used to harvest mailboxes for intelligence and leak material [‘The compromise of Microsoft Exchange infrastructure … access and manipulate mailboxes’]
- [T1105 ] Ingress Tool Transfer – Tools and payloads staged and transferred into targets for execution [‘Files are typically staged locally, compressed, and transferred’]
- [T1041 ] Exfiltration Over C2 – Data exfiltration over C2 channels including Telegram-based channels [‘the actors leverage Telegram-based exfiltration, using the platform’s API to transmit data’]
- [T1486 ] Data Encrypted for Impact – Ransomware-style encryption used as part of disruptive sequencing [‘encryption and wiping components were deployed in sequence’]
- [T1561.001 ] Disk Wipe – Destructive wiping (No-Justice, BiBi Wiper, handala.exe) to prevent recovery [‘designed for rapid and irreversible disruption’]
- [T1485 ] Data Destruction – Manual and scripted deletion and formatting to ensure sustained damage [‘manual file deletion and disk formatting to perform destructive actions’]
- [T1218 ] System Binary Proxy Execution – Abuse of signed/system binaries and rundll32 to evade defenses [‘use of signed binaries suggests an increased emphasis on evasion and trust abuse’]
- [T1036 ] Masquerading – Trojanized apps and masqueraded binaries used as lures and persistence [‘trojanized applications masquerading as legitimate software’]
- [T1490 ] Inhibit System Recovery – Techniques to prevent recovery, including boot corruption and wiping [‘preventing successful operating system boot’ and ‘Inhibit Recovery’]
- [T1018 ] Remote System Discovery – Discovery of remote systems to map network and targets [‘operators conducted systematic internal reconnaissance, enumerating network topology’]
- [T1562 ] Impair Defenses – Actions to disable or impair endpoint defenses and evade detection [‘Defense Evasion … AV disable’ and ‘impair defenses’]
- [T1005 ] Data from Local System – Collection of files and email data from local systems for exfiltration [‘Data is typically staged locally, compressed, and transferred’]
- [T1566 ] Phishing – Targeted lures and phishing for initial access in surveillance and person-centric operations [‘Initial access is commonly achieved through trojanized applications… and phishing’]
- [T1218.011 ] Rundll32 – Use of rundll32 for execution observed in Handala phase [‘Execution … T1218.011 Rundll32’]
- [T1547 ] Boot or Logon Autostart Execution – Registry/run keys and scheduled tasks used for persistence [‘Registry modifications and scheduled tasks are used to ensure execution at startup’]
- [T1555 ] Credentials from Password Stores – Extraction from credential stores and browser stores for account access [‘Actors extract credentials from configuration files, email systems, and browser stores’]
- [T1069 ] Permission Groups Discovery – Enumeration of groups and permissions to map actor access and targets [‘Account Discovery and Permission Groups referenced as discovery techniques’]
- [T1204 ] User Execution – Social engineering and user-executed trojans used as lures [‘trojanized applications tailored to the target’s context’]
- [T1113 ] Screen Capture – Screen capture used by surveillance implants for continuous monitoring [‘staged malware chains that establish … screen capture’]
- [T1123 ] Audio Capture – Audio interception including conferencing platforms [‘audio interception (with specific capability to monitor conferencing platforms)’]
- [T1071.001 ] Web Protocols (Telegram API) – Telegram Bot API abused for encrypted C2 and exfiltration [‘use of the Telegram Bot API, which allows malware to communicate with operator-controlled bots’]
- [T1583.001 ] Domains – Domain provisioning and rotation for narrative nodes and resilience [‘Core domains such as Homeland Justice[.]org, handala-hack[.]to … operate as visible nodes’]
- [T1583.003 ] VPS – Use of VPS/back-end hosting to support alternate infrastructure and resilience [‘additional domains … likely function as alternate or backend infrastructure’]
- [T1585.001 ] Social Media Accounts – Establishment and use of Telegram/X accounts and channels for amplification [‘Telegram channels … distribute propaganda, operational claims, and references to leaked data’]
- [T1608 ] Stage Capabilities (Upload/Stage Data) – Staging and uploading stolen data to sites and channels for publication [‘Files are typically staged locally, compressed, and transferred using standard protocols’]
- [T1102 ] Web Service – Use of web services (Telegram as platform) for both C2 and public dissemination [‘Telegram occupies a central and multifaceted role … covert command-and-control and an overt platform for messaging’]
Indicators of Compromise
- [Domain ] public-facing narrative and leak sites – handala-hack[.]tw, homelandjustice[.]org, and other registered domains such as handala-redwanted[.]cc and karmabelow80[.]org (and multiple additional handala/karma/homeland domains)
- [File Hash (MD5) ] destructive and payload artifacts – GoXML.exe (bbe983dba3bf319621b447618548b740), handala.exe (5986ab04dd6b3d259935249741d3eff2), and several other MD5 hashes (and 15+ other hashes across campaigns)
- [File Hash (SHA-256) ] signed wiper sample – Ptable.exe / NACL.exe (36cc72c55f572fe02836f25516d18fed1de768e7f29af7bdf469b52a3fe2531f)
- [Filenames / Tools ] known payloads and loaders – Telegram_Authenticator.exe, RuntimeSSH.exe, NetBird installer, and handala.exe (representative artifacts referenced across phases)
- [Telegram / Social Handles ] amplification and C2 channels – @HANDALA_INTEL, @HomelandJustice1 (channels used for publication and coordination) and api.telegram.org as abused C2 endpoint
- [Command-and-Control ] platform endpoints – api.telegram.org (Telegram Bot API used for C2 and exfiltration) and referenced bot-based control infrastructure