ForceHound is an open-source Python collector that builds a BloodHound CE identity graph to help audit Salesforce orgs by visualizing profiles, permission sets, roles, connected apps, field- and record-level sharing, and system capabilities. The post details collection modes (API, Aura, both), empirical CRUD probing, BloodHound CE integration, audit logging, scope-control flags, and frames urgency after the UNC6040 campaign that abused malicious Connected Apps. #ForceHound #UNC6040
Keypoints
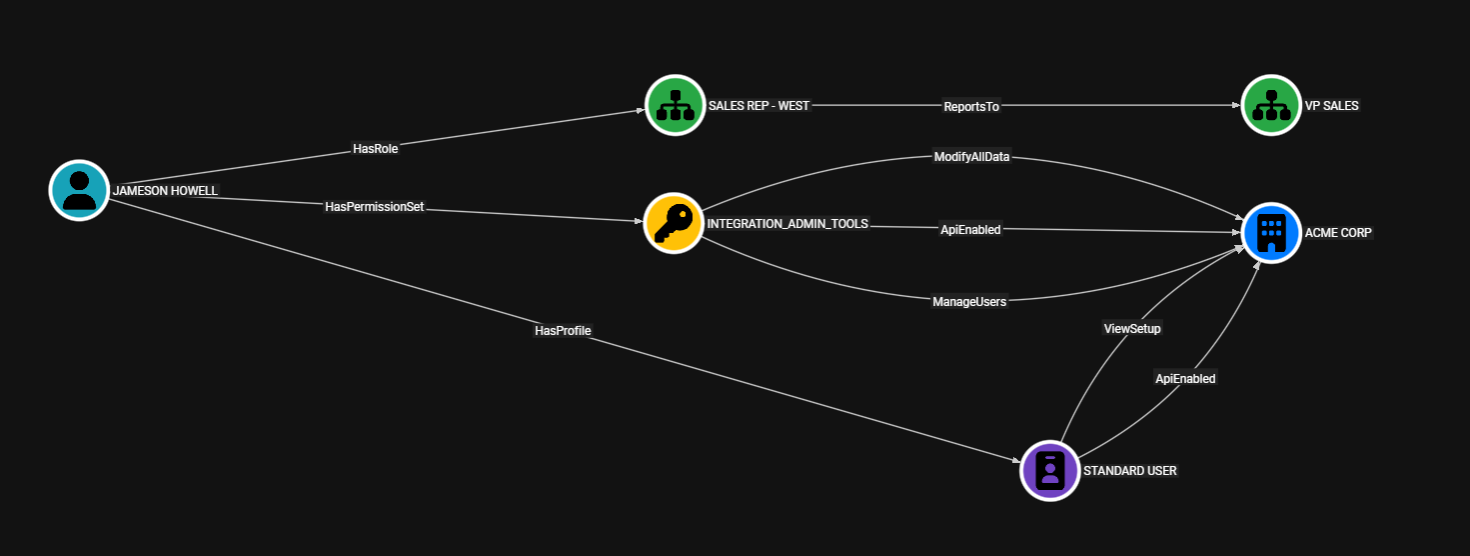
- ForceHound is an open-source Python collector that outputs a BloodHound CE–compatible identity graph for Salesforce, enabling graph queries of profiles, permission sets, roles, groups, connected apps, and sharing objects.
- Three collection modes—API (privileged), Aura (low-privilege browser session), and both—let assessors collect varying depths of metadata depending on available credentials and session artifacts.
- The tool models capability edges (15 system permissions like ModifyAllData), CRUD edges per object, field-level security edges, Connected App access edges, share object edges, and organization-wide default properties to reveal attack paths.
- Empirical CRUD probing (–crud, –aggressive) tests actual create/read/edit/delete behavior to generate proven access edges, complementing metadata-derived permissions.
- BloodHound CE integration supports upload, custom node registration (–setup), OpenGraph v1 output (–new-format), and database clearing (–clear-db) for visualization and Cypher queries.
- Audit logging (–audit-log 1/2/3) produces JSONL records aligned to OCSF for forensic review, and scope-control flags (–skip-*) help manage performance and output size in large orgs.
MITRE Techniques
- [None ] No MITRE ATT&CK techniques were explicitly mentioned in the article – ‘The post does not reference ATT&CK technique names or IDs.’
Indicators of Compromise
- [Domain/URL ] tool distribution and source – pypi.org/project/forcehound/, github.com/NetSPI/ForceHound
- [Instance URLs ] example Salesforce endpoints used for collection and testing – https://yourorg.my.salesforce.com, https://yourorg.lightning.force.com
- [File names ] output and forensic artifacts produced by ForceHound – forcehound_audit_.jsonl, forcehound_deletions_.json
- [Credentials / Session Tokens ] session and token artifacts required for collection (sensitive) – SID cookie, aura.token, and example token/env names like FORCEHOUND_BH_TOKEN_ID / FORCEHOUND_BH_TOKEN_KEY