Three days after disclosure of a pre-auth remote code execution in the marimo Python notebook platform (GHSA-2679-6mx9-h9xc / CVE-2026-39987), multiple actors exploited the flaw to harvest credentials, run reverse shells, pivot to PostgreSQL/Redis, and deploy a previously undocumented NKAbuse variant hosted on a typosquatted HuggingFace Space. Defenders should look for the VS Code typosquat vsccode-modetx.hf.space, the kagent implant and installer, rotated credentials, and runtime behaviors such as reverse shells and systemd/crontab persistence #NKAbuse #marimo
Category: Threat Research

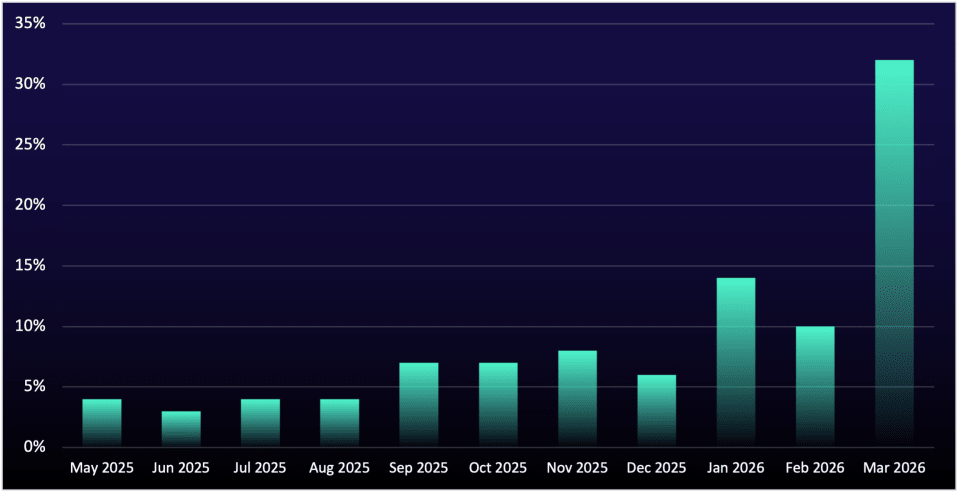
Germany became the primary focus for cyber extortion in Europe in 2025, with data leak site postings affecting the country rising 92% year‑over‑year and outpacing the regional average. The disruption of major ransomware brands rebalanced the criminal ecosystem, enabling mid‑tier groups like SafePay and Qilin to aggressively target the German Mittelstand and professional services. #SafePay #Qilin

Cyble Blaze AI unifies enterprise telemetry and dark web signals using an AI-native, dual-brain architecture to convert scattered data into actionable intelligence and automated response. It correlates external dark web monitoring with internal systems through autonomous agents, prediction, and orchestration to reduce alert fatigue and enable proactive risk management. #CybleBlazeAI #DarkWeb
.jpg)
Operation Epic Fury and subsequent multi-day Iranian missile/drone strikes across seven countries have been accompanied and preceded by extensive APT35 cyber reconnaissance and pre-positioned access in GCC targets, with active webshell activation and malware deployment observed. Defenders should prioritize immediate blocking of listed domains/IP ranges, emergency patching of exploited CVEs, credential rotations, and hunts for indicators such as Plink.exe, Adminer.php, and TOR-linked Sagheb RAT activity. #APT35 #BellaCiao

MacSync Stealer is an active macOS infostealer campaign leveraging SEO poisoning and ClickFix fake CAPTCHA social engineering to trick U.S. SLTT users into pasting Terminal commands that fetch and execute Zsh and AppleScript payloads. The campaign features a Loader-as-a-Service model with API key‑gated C2 infrastructure and in-memory AppleScript execution to evade…
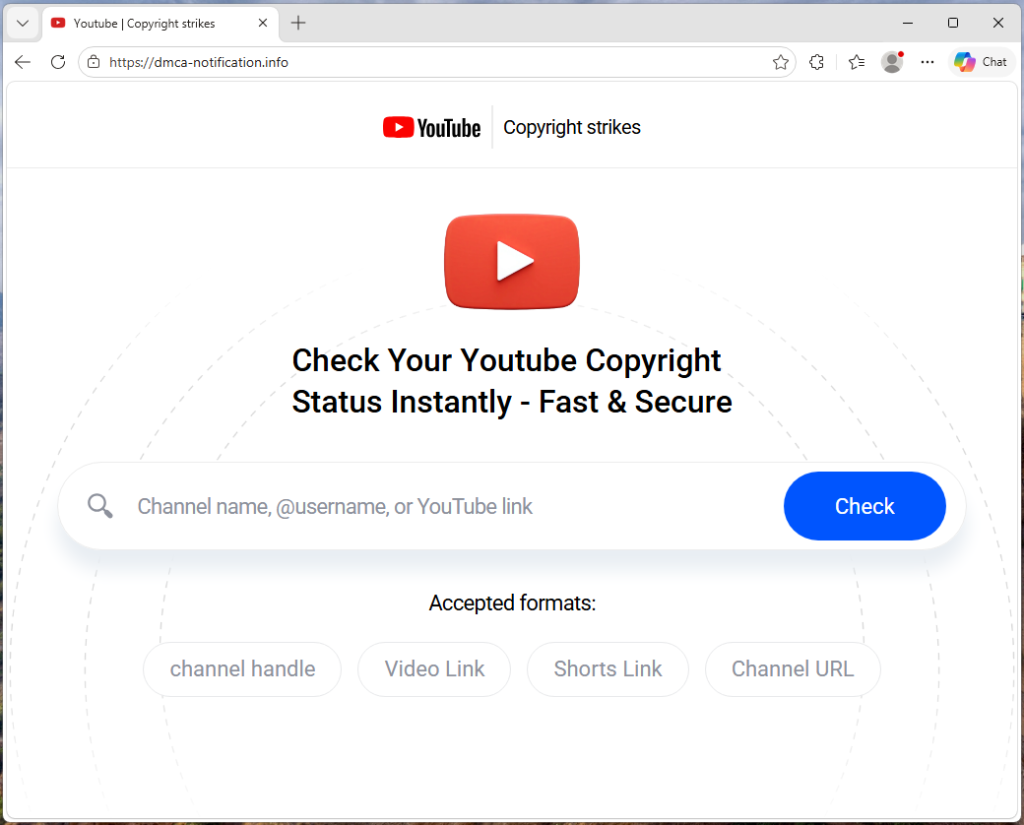
Attackers run a phishing-as-a-service campaign targeting YouTube creators with a highly personalized fake copyright strike page that pulls real channel data and uses a Browser-in-the-Browser Google sign-in overlay to harvest credentials. The platform rotates phishing domains, uses affiliate tracking and evasion tactics (skipping very large channels), and enables hijackers to take…
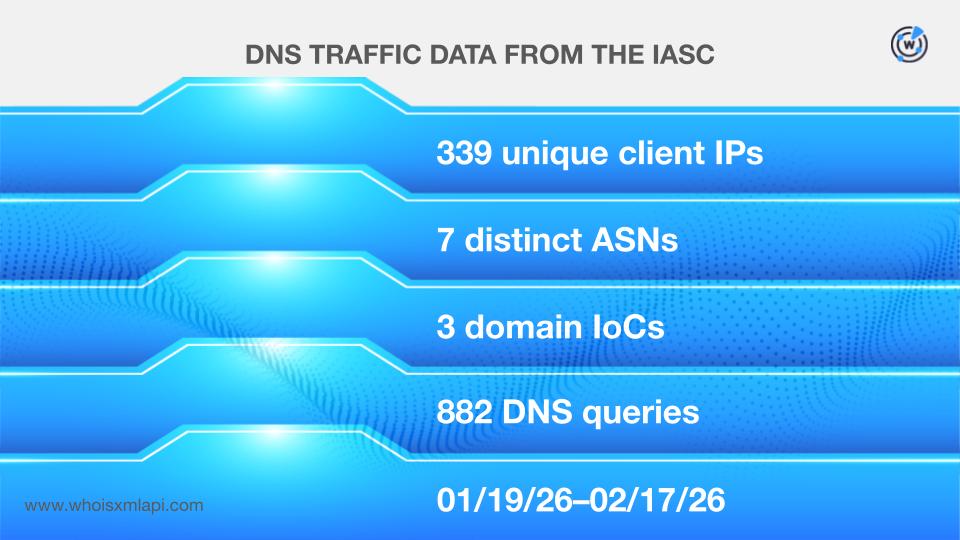
Keenadu, a backdoor found in Android firmware, appears to have been introduced via a malicious static library linked to libandroid_runtime.so during firmware builds and, in other cases, pushed through OTA updates; it acts as a multistage loader enabling remote control, search hijacking, monetized app installs, and stealthy ad interactions. Extensive DNS and WHOIS analysis uncovered 29 primary IoCs (five subdomains, 20 domains, four IPs), dozens of associated email- and IP-connected domains, and additional weaponized IPs—highlighting infrastructure tied to istaticfiles[.]com. #Keenadu #istaticfiles

DragonBreath (APT-Q-27) is a persistent, evolving threat actor targeting Chinese-speaking users with a modified variant of the open-source gh0st RAT and has focused on cryptocurrency-related and gaming VPN software since at least 2022. AttackIQ published a RoningLoader emulation in its AEV platform to reproduce the group’s post-compromise TTPs and help organizations…

Socket’s Threat Research Team discovered 108 malicious Chrome extensions that share a single C2 infrastructure at cloudapi[.]stream and collectively account for about 20k installs under five publisher identities, exfiltrating Google identities, Telegram Web sessions, browsing data, and opening attacker-specified URLs. The campaign includes OAuth-based identity harvesting, a Telegram Web session stealer (Telegram Multi-account) that exfiltrates sessions every 15 seconds, a universal loadInfo() backdoor, and header-stripping declarativeNetRequest rules used to inject ads and bypass protections; #TelegramMultiAccount #cloudapi_stream

The March 2026 AhnLab report summarizes ransomware sample counts, victimized systems, DLS-based statistics, and major Korean and global ransomware incidents, noting a methodological change in December 2025 that limits direct monthly comparisons. March was marked by attacks on critical infrastructure—including manufacturing, healthcare, and finance—with continued activity from groups such as Qilin,…
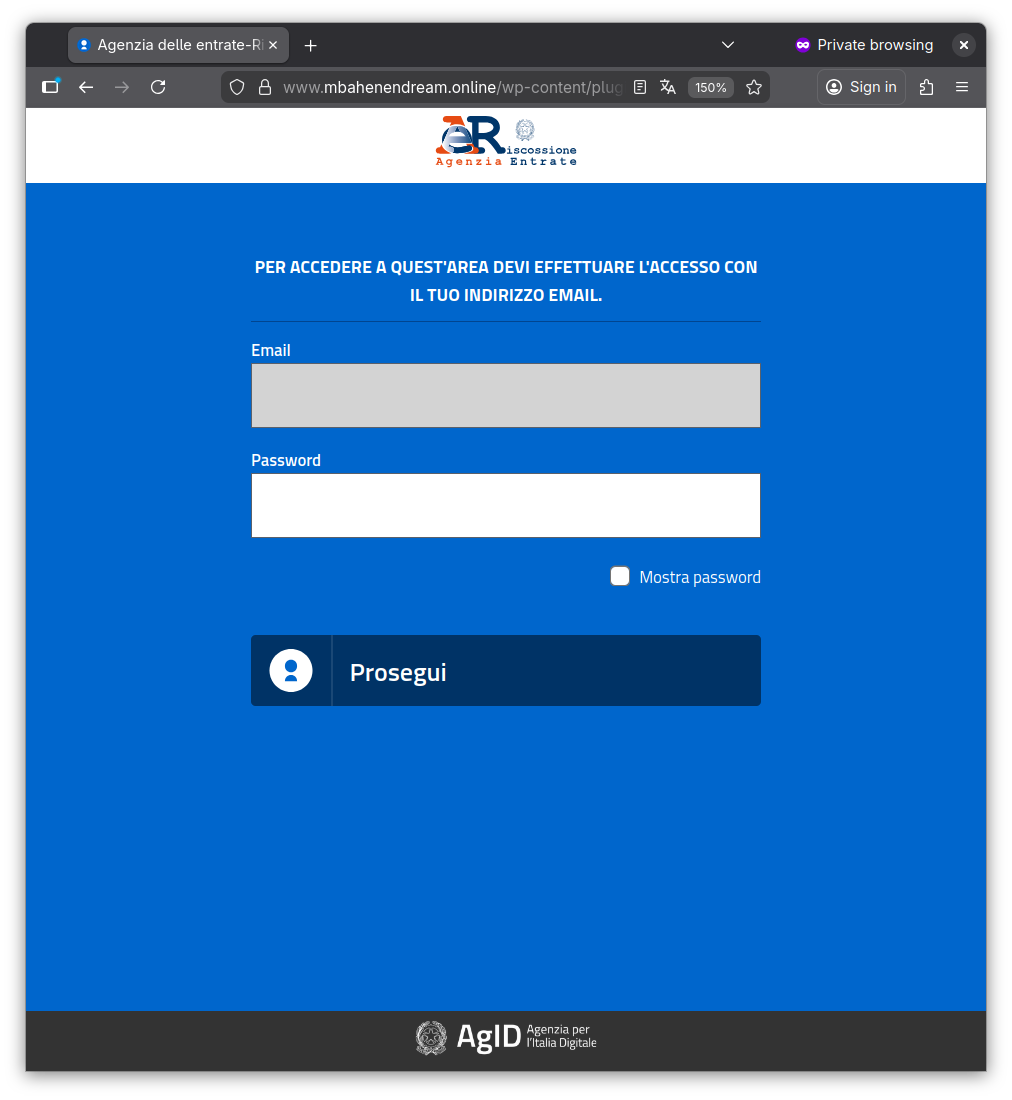
CERT-AGID detected a targeted phishing campaign impersonating the Agenzia delle Entrate–Riscossione that uses deceptive communications to direct victims to a fake SPID login page designed to harvest credentials. The campaign is especially aimed at public administrations and private organizations, CERT-AGID notified affected parties, requested takedown of the phishing site, and distributed IoCs via its feed. #AgenziadelleEntrate #CERT-AGID
A refined, highly automated campaign by likely former Black Basta affiliates combines mass email bombing with Microsoft Teams help-desk impersonation to gain remote access to senior leaders within minutes, often using RMM tools like Supremo and Quick Assist. Defenders are advised to implement out-of-band verification for remote-access requests, tighten RMM allow-listing, and run targeted simulations for executives. #BlackBasta #Supremo
Genians Security Center analyzed a multi-stage social engineering campaign by APT37 that used Facebook for target reconnaissance and a tampered Wondershare PDFelement installer to execute embedded shellcode and stage follow-on payloads delivered as a JPG file from a legitimate website. The report emphasizes that the campaign abused Zoho WorkDrive for C2 and that behavior-based EDR and threat hunting are essential to detect process injection, tampered installers, and cloud-abused communications. #APT37 #WondersharePDFelement
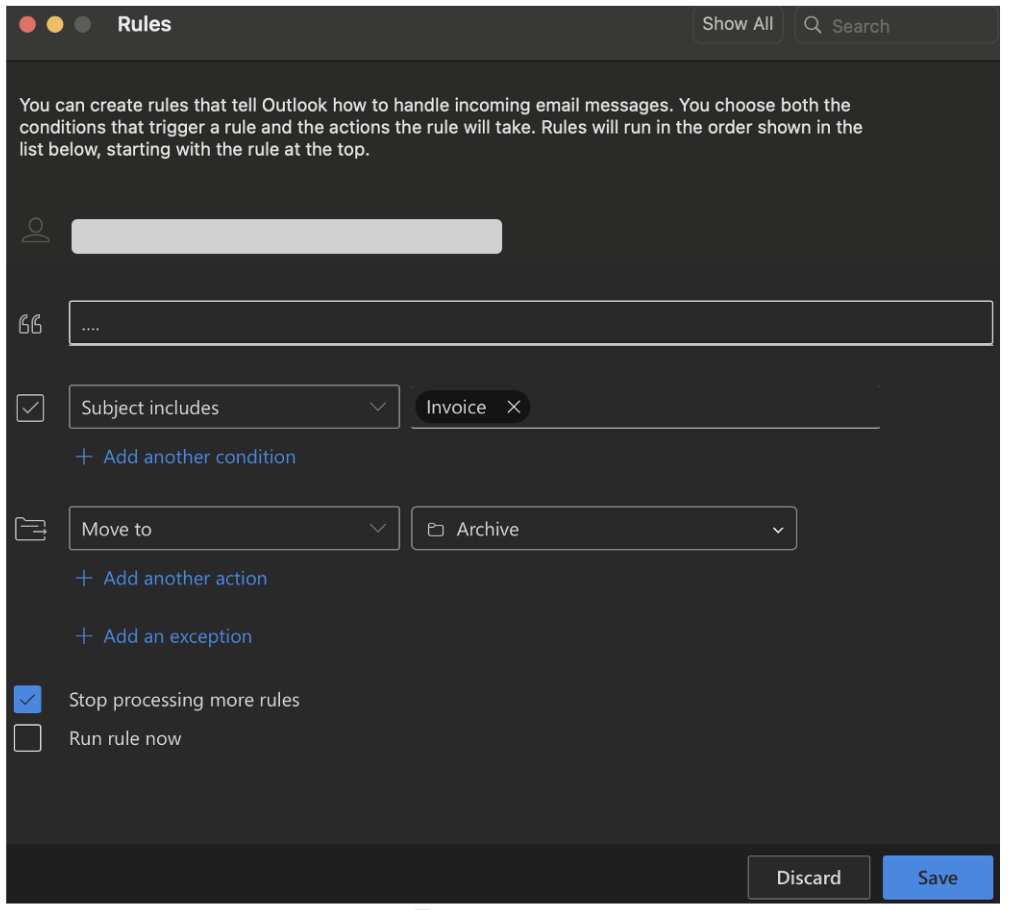
Attackers increasingly abuse native Microsoft 365 mailbox rules for stealthy persistence, exfiltration, thread hijacking, and vendor impersonation without deploying malware or network interception. The report highlights automation (e.g., ATOLS), common indicators like terse rule names (., …, ;), and recommends controls such as disabling external auto-forwarding and revoking sessions. #Microsoft365 #ATOLS…

Elastic Security Labs tracked REF6598, a targeted social-engineering campaign that abused Obsidian’s community plugin sync to execute a cross-platform intrusion chain culminating in a novel Windows RAT named PHANTOMPULSE with blockchain-based C2 resolution. The campaign used LinkedIn/Telegram lures, trojanized Obsidian Shell Commands and Hider plugins for initial access, an in-memory loader called PHANTOMPULL on Windows, and an obfuscated AppleScript dropper with Telegram fallback on macOS. #PHANTOMPULSE #Obsidian
