CERT-AGID detected a targeted phishing campaign impersonating the Agenzia delle Entrate–Riscossione that uses deceptive communications to direct victims to a fake SPID login page designed to harvest credentials. The campaign is especially aimed at public administrations and private organizations, CERT-AGID notified affected parties, requested takedown of the phishing site, and distributed IoCs via its feed. #AgenziadelleEntrate #CERT-AGID
Keypoints
- CERT-AGID identified a phishing campaign targeting the Agenzia delle Entrate–Riscossione that seeks to steal login credentials.
- The campaign is particularly targeted at public administrations in addition to private companies.
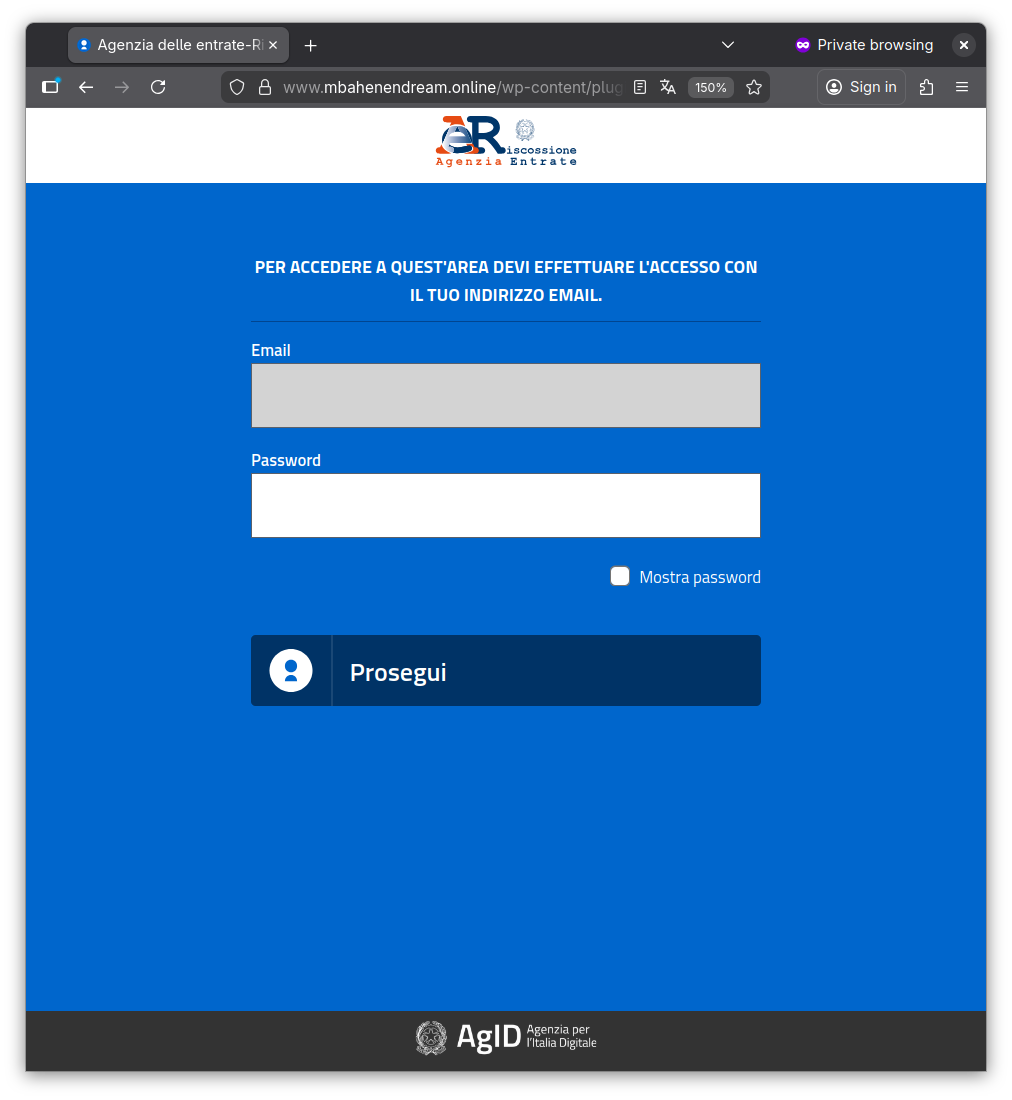
- Phishing messages contain a link to a fraudulent website that mimics the Agenzia delle Entrate SPID login and displays the AgID logo.
- The fake page pre-fills the victim’s email via a personalized link and asks only for the password, facilitating credential theft.
- Compromised credentials could allow unauthorized access to mailboxes and institutional systems, leading to data exfiltration, document tampering, and legal/reputational impacts.
- CERT-AGID notified the affected entity, requested takedown of the phishing site, and published IoCs through its feed (Download IoC link referenced).
MITRE Techniques
- [T1566.002 ] Phishing: Spearphishing Link – Attackers sent deceptive communications containing a link to a fraudulent site created to steal credentials (‘deceptive communications that invite users to access their reserved area … these communications include a link that leads to a site specifically created to steal credentials’).
- [T1078 ] Valid Accounts – Stolen credentials are used (or could be used) to gain unauthorized access to mailboxes and institutional systems, enabling data exfiltration or alteration (‘compromised credentials can allow unauthorized access to mailboxes or institutional systems, with consequent exfiltration of sensitive data or alteration of official documents’).
Indicators of Compromise
- [URL ] Phishing site link – fraudulent SPID login page and hosting site referenced; specific phishing URLs not listed in the article (IoCs available via the referenced “Download IoC” feed).
- [Email address ] Pre-filled victim emails used in personalized phishing links – article notes victim email addresses are prepopulated but no example addresses were published.
- [IoC feed/file ] CERT-AGID IoC distribution – the article references a CERT-AGID feed and a “Download IoC” link where the campaign’s IoCs were published (exact feed URL/file not included in the article).