Attackers increasingly abuse native Microsoft 365 mailbox rules for stealthy persistence, exfiltration, thread hijacking, and vendor impersonation without deploying malware or network interception. The report highlights automation (e.g., ATOLS), common indicators like terse rule names (., …, ;), and recommends controls such as disabling external auto-forwarding and revoking sessions. #Microsoft365 #ATOLS
Keypoints
- Mailbox rules are a common post-exploitation technique in Microsoft 365, used for exfiltration, persistence, and manipulation of communications.
- Approximately 10% of compromised accounts in Q4 2025 had malicious mailbox rules created shortly after initial access, sometimes within seconds.
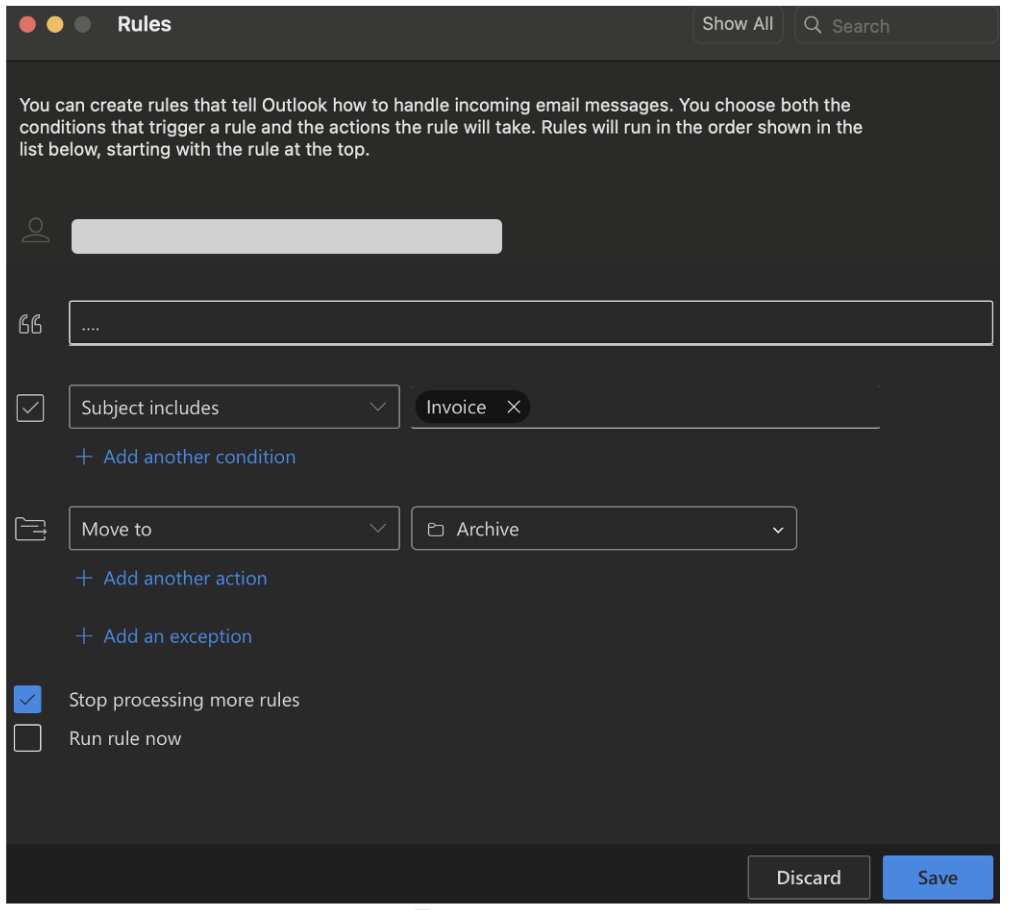
- Attackers favor minimal or nonsensical rule names (e.g., “.”, “…”, “;”) and actions that delete, move, or hide messages in seldom-checked folders like Archive or RSS Subscriptions.
- Forwarding and suppression rules can survive password resets, allowing continued data leakage until the rule is removed.
- Attackers combine mailbox rules with third-party services and domain homoglyphs (e.g., Zoho-based spoofed domains) to hijack threads and impersonate legitimate participants.
- Automation via Graph API, Exchange Online PowerShell, or tools like ATOLS enables scalable, rapid deployment of malicious rules across many accounts; mitigations include disabling external auto-forwarding, enforcing conditional access, and auditing OAuth grants.
MITRE Techniques
- [T0000 ] No explicit MITRE ATT&CK techniques mentioned – ‘Mailbox rules are a high-risk post-exploitation tactic. Attackers abuse native mailbox rules for exfiltration, persistence, and communication manipulation.’
Indicators of Compromise
- [Email / Domain ] Spoofed inboxes and homoglyph domains used to impersonate tenants and receive exfiltrated messages – example: user_name@tenant_name0.com (zero instead of letter O), and Zoho-related registration addresses.
- [Mailbox Rule Names ] Typical malicious rule name patterns observed shortly after compromise – example: ‘.’, ‘…’, and ‘..’ (most frequent names observed).
- [Folder / Mailbox Locations ] Attackers move or hide messages in seldom-checked folders to suppress alerts and verification emails – example: Archive, RSS Subscriptions, and Conversation History.
- [Session Tokens / OAuth Scopes ] Session cookie/token theft and overly permissive OAuth grants enable persistent access without MFA challenges – example contexts: captured session cookie/token, OAuth scopes Mail.Read and Mail.ReadWrite.