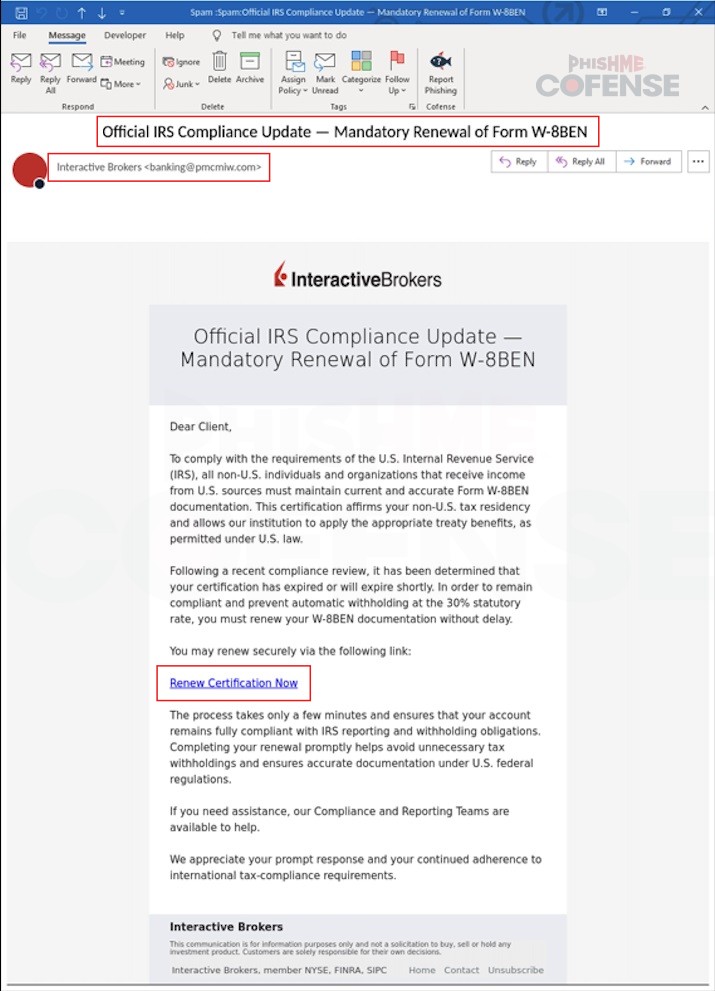
Cofense Phishing Defense Center uncovered a phishing campaign impersonating Interactive Brokers that uses tax-related lures to trick users into renewing a Form W-8BEN and clicking a malicious login link. The phishing emails originate from suspicious senders (e.g., [email protected]) and direct victims to hXXps://wbnoebe[.]com where submitted credentials are sent to a threat actor-controlled C2 server. #InteractiveBrokers #FormW8BEN
Category: Threat Research
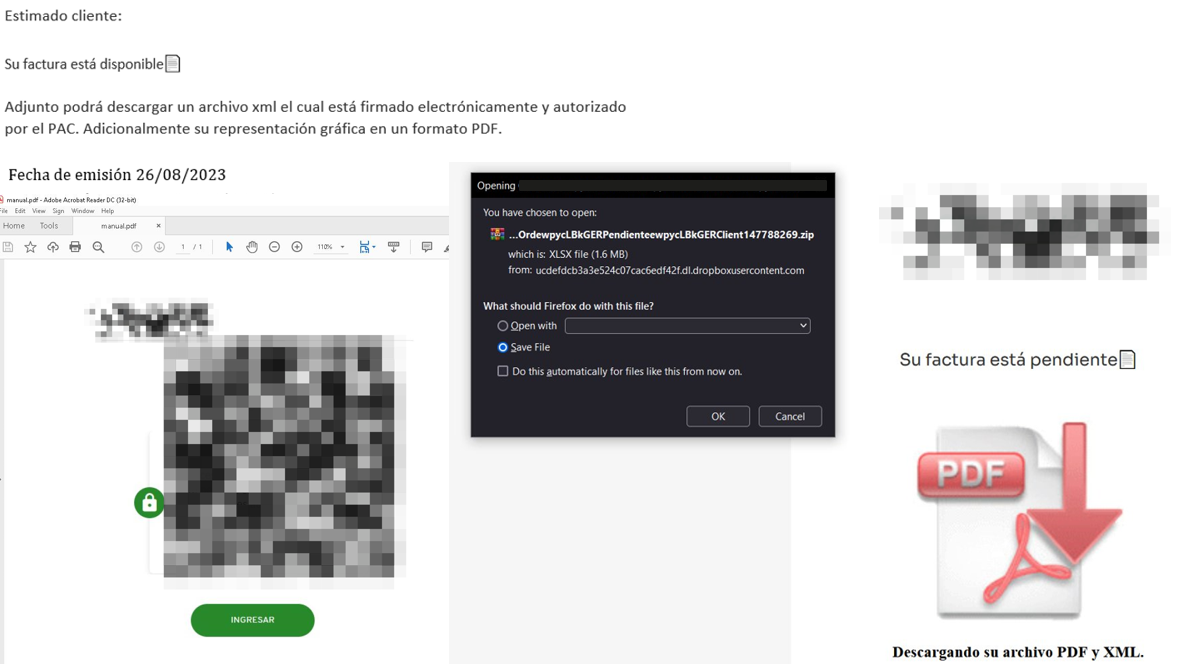
JanelaRAT is a banking-focused remote access Trojan campaign active since mid-2023 that uses multi-stage phishing lures, evolving droppers (including MSI-based sideloading), and dynamic C2 infrastructure to target banking users in Latin America. The malware performs real-time session hijacking with overlays, input injection, and extensive monitoring while using obfuscation and anti-analysis techniques to evade detection. #JanelaRAT #Brazil

Since the introduction of LLM-powered agentic browsers, researchers at Varonis Threat Labs have shown that embedding autonomous AI agents in browsers creates new high-privilege attack surfaces that convert standard web flaws into full browser takeovers. The analysis highlights concrete abuse paths (XSS, agentic CSRF, IPC/Mojo bridge compromises, data-voids, and indirect prompt…
Two backdoored Axios npm releases ([email protected] and [email protected]) were published from a compromised maintainer account and, during a roughly three‑hour window, introduced a malicious dependency that installed a cross‑platform RAT via a postinstall hook. The campaign, attributed to UNC1069, deployed SILKBELL to fetch the WAVESHAPER RAT and led to detections across Windows and macOS with 19 affected eSentire customers; #WAVESHAPER #UNC1069

Elastic recounts its role as the core defensive platform provider for Defence Cyber Marvel 2026 (DCM26), delivering a single, space-based multi-tenanted Elastic Cloud deployment for 40 Blue Teams, separate Red Team and NSOC deployments, large-scale automation with Terraform/Catapult, and a guarded on-range AI service backed by AWS Bedrock. The exercise validated the architecture at scale (ingesting up to 800,000 EPS), supported custom AI agents (GrantPT, REDRock, RefPT), extensive partner integrations (Tuoni, Tines, Endace, AWS), and strict audit/guardrail controls. #DefenceCyberMarvel #Elastic
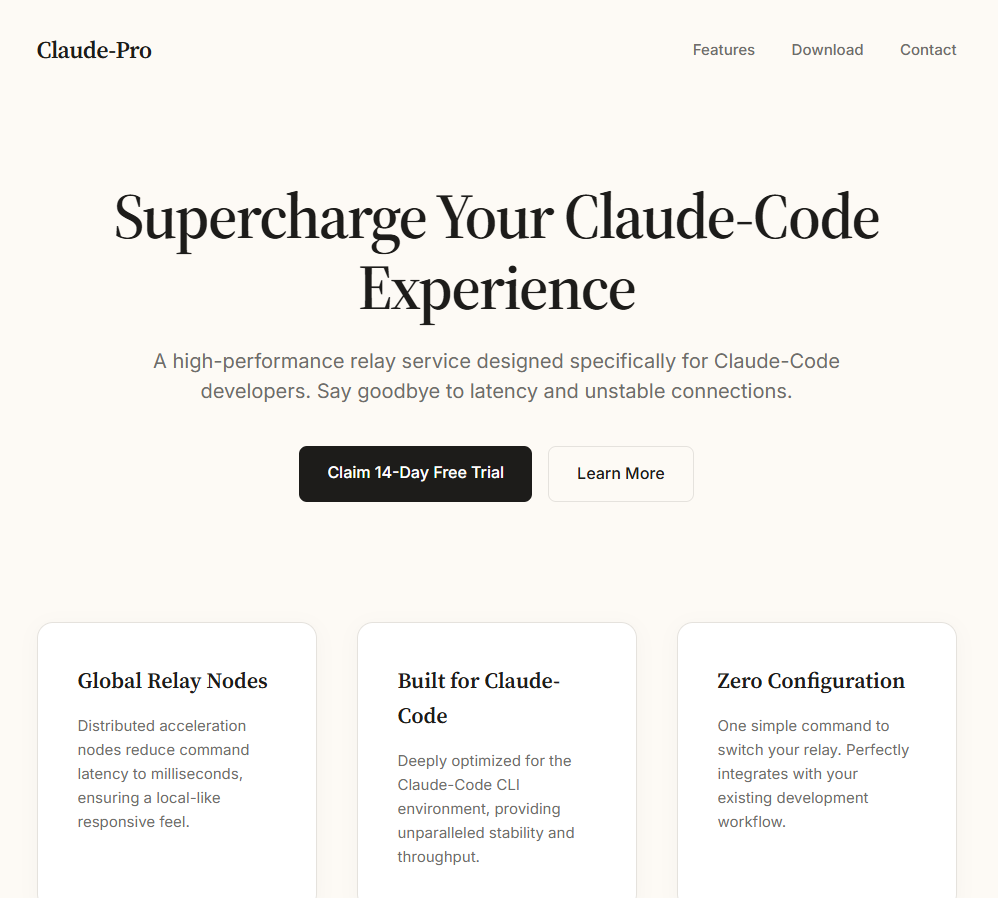
A fake website impersonating Anthropic’s Claude distributed a trojanized installer (Claude-Pro-windows-x64.zip) that installs a working Claude application while secretly deploying a PlugX sideloading chain. The dropper uses a signed G DATA updater (NOVUpdate.exe), a malicious avk.dll, and an encrypted payload (NOVUpdate.exe.dat) to perform DLL sideloading and rapidly call back to 8.217.190.58,…
MuddyWater conducted “Operation Olalampo,” targeting organizations and individuals across the MENA region using new malware variants and Telegram bots for command-and-control, with Group-IB publishing an initial set of seven network IoCs. Investigations found four domain IoCs (recently registered and administered via Namecheap in Iceland), three IP IoCs (geolocated to the U.S.), extensive DNS/WHOIS linkage including 2,530 email-connected domains, and downloadable sample artifacts. #MuddyWater #OperationOlalampo

The article analyzes adoption and operational coverage of immutable backups using Acronis telemetry and public surveys, finding meaningful but limited deployment (about 170,000 tenants protecting ~49PB, roughly 1.4% of a 3,600PB estate). It recommends pragmatic rollouts—start with one recent immutable copy for critical workloads (weekly fulls, 14–30 day retention), prefer cloud or dual-destination patterns, improve backup design to reduce storage waste, and monitor quota, duration and restore tests. #PlayRansomware #Acronis

The March 2026 analysis of Infostealer samples shows Windows samples were predominantly EXE with notable DLL side-loading activity, while macOS campaigns relied on rapidly mutating Bash scripts and a ClickFix clipboard method to trigger terminal execution. Major families identified include ACRStealer, Vidar, and LummaC2, with distribution via cracked software/SEO poisoning, forum/WordPress…

A trojanized CPUID HWMonitor installer was used to deliver a multi-stage, fileless malware chain that leverages trusted Windows binaries (PowerShell, MSBuild, regsvr32) to execute scriptlet payloads such as Clippy.sct which reconstructs and runs a .NET assembly entirely in memory. The reconstructed payload is deserialized and dynamically invoked (with likely follow-on shellcode execution via VirtualAlloc/CreateThread), and organizations are advised to validate installers, deploy EDR, and monitor for regsvr32/MSBuild/scriptlet usage and large embedded arrays. #HWMonitor #Clippy.sct
APT35 (IRGC-IO) maintained pre-positioned access across multiple GCC environments and its reconnaissance activity correlated with kinetic strikes following Operation Epic Fury, causing combined cyber and physical impacts across Jordan, UAE, Saudi Arabia, Kuwait, and Israel. Defenders are urged to block listed domains/IPs, patch critical vulnerabilities (ConnectWise, ProxyShell, Ivanti, Telerik), hunt for webshells and Plink.exe, rotate Domain Admin credentials, and monitor for BellaCiao and Sagheb RAT activity. #APT35 #BellaCiao

The article analyzes how threat actors abuse the Microsoft-signed MSBuild.exe to run inline C# project files and perform fileless operations such as reverse shells, downloading payloads, and DLL sideloading to evade detection. It reviews proof-of-concept and real-world campaigns demonstrating Windows Defender bypasses via automatic project-file execution and recommends behavior-based, multi-layered detection…

The article explains how agentic AI with a dual‑brain architecture—combining a real‑time processing layer and a neural memory layer—enables predictive, autonomous cybersecurity that both reacts instantly and reasons with historical context. It uses Cyble Blaze AI as an example platform that correlates signals, investigates autonomously, and can forecast risks up to six months ahead to reduce alert fatigue and enable rapid containment. #CybleBlazeAI #AgenticAI

Zscaler ThreatLabz detailed a multi-stage campaign that used a fake Adobe Acrobat Reader download to deliver a heavily obfuscated VBScript loader which staged PowerShell and an in-memory .NET loader to install ConnectWise ScreenConnect. The chain used runtime string reconstruction, heavy obfuscation, PEB image-name spoofing, and abuse of auto-elevated COM objects to evade detection and obtain elevated privileges. #ScreenConnect #VBS_Downloader

CVE-2020-8562 is a TOCTOU vulnerability in the Kubernetes API server proxy that can be combined with DNS rebinding to bypass an IP-based filter and reach internal services like the control plane metadata or kube-proxy config endpoints. The issue is most concerning for managed Kubernetes control planes because exploitation requires creating Node objects and using the API server proxy, and mitigations include enforcing minimum DNS TTLs or using Konnectivity. #CVE-2020-8562 #Kubernetes