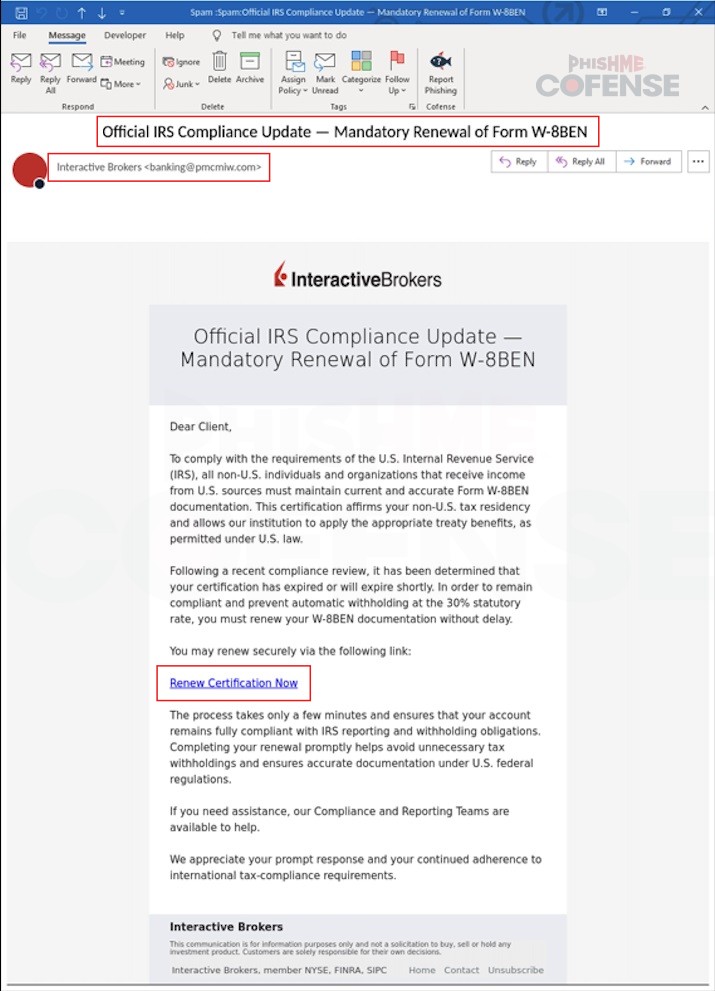
Cofense Phishing Defense Center uncovered a phishing campaign impersonating Interactive Brokers that uses tax-related lures to trick users into renewing a Form W-8BEN and clicking a malicious login link. The phishing emails originate from suspicious senders (e.g., [email protected]) and direct victims to hXXps://wbnoebe[.]com where submitted credentials are sent to a threat actor-controlled C2 server. #InteractiveBrokers #FormW8BEN
Keypoints
- Threat actors sent emails impersonating Interactive Brokers requesting renewal of Form W-8BEN to lure non-US account holders.
- The sender address (e.g., [email protected]) is not from the official interactivebrokers.com domain, indicating phishing.
- Emails contained a “Renew Certification Now” link that led to a fake Interactive Brokers login page hosted on wbnoebe[.]com.
- When victims entered credentials, those credentials were transmitted to the attacker’s C2 server (hXXps://wbnoebe[.]com?token=…).
- Observed infrastructure includes the phishing domain wbnoebe[.]com and IPs 104.21.64.219 and 172.67.187.230.
- Recommendations include validating sender addresses and URLs, and enabling multi-factor authentication to reduce account takeover risk.
MITRE Techniques
- [T1566.002 ] Spearphishing Link – Attackers delivered a malicious link via email that directed recipients to a credential-harvesting page (‘Included in the email body is a link with “Renew Certification Now”, prompting the receiver to click the URL to proceed.’)
- [T1078 ] Valid Accounts – Stolen credentials from the fake login page can be used to access victim accounts as legitimate users (‘If the recipient attempts to log in using their username and password, their credentials are sent over to the threat actor’s C2 server…’)
- [T1041 ] Exfiltration Over C2 Channel – Collected credentials are transmitted to the attacker-controlled server via the phishing site’s URL and token parameters (‘their credentials are sent over to the threat actor’s C2 server, ‘)
Indicators of Compromise
- [Email Address ] sender used in phishing – [email protected]
- [Domain / URL ] phishing landing page and observed infection URL – wbnoebe[.]com, hXXps://wbnoebe[.]com?token=eIqv7TknECn4EImFVxFD1
- [IP Address ] hosting / C2 infrastructure – 104.21.64.219, 172.67.187.230
- [Email Subject / Lure ] social engineering bait used in messages – “IRS Compliance Requirement” and requests to “renewal of Form W-8BEN”
Read more: https://cofense.com/blog/interactive-brokers-phishing-scam-fake-irs-w-8ben-renewal-alert