JanelaRAT is a banking-focused remote access Trojan campaign active since mid-2023 that uses multi-stage phishing lures, evolving droppers (including MSI-based sideloading), and dynamic C2 infrastructure to target banking users in Latin America. The malware performs real-time session hijacking with overlays, input injection, and extensive monitoring while using obfuscation and anti-analysis techniques to evade detection. #JanelaRAT #Brazil
Keypoints
- Campaigns begin with phishing emails that lure victims to download a malicious archive which ultimately delivers an MSI dropper and a DLL sideloaded as the JanelaRAT implant.
- The MSI dropper obfuscates paths/names, creates a Startup LNK for persistence, deploys a legitimate executable (nevasca.exe) and PixelPaint.dll (the RAT), and executes the sideloading chain.
- JanelaRAT is a .NET backdoor (obfuscated with Eazfuscator/ConfuserEx) that collects system info, creates a mutex, encrypts strings (Base64 + AES), and establishes TCP/HTTP beaconing to C2 servers that rotate daily using dynamic DNS patterns.
- Core capabilities focus on banking fraud: active title-bar detection for targeted banks, screenshot capture, keylogging, input injection, overlay-based credential and MFA theft, and forced system actions (e.g., shutdown).
- The malware includes anti-analysis and sandbox detection (e.g., Magnifier components), adapts infection chains (adding MSI and other components), and the actor updates target lists and parameters such as detecting anti-fraud processes.
- Telemetry shows heavy targeting in Latin America with thousands of detections (e.g., ~14,739 in Brazil and ~11,695 in Mexico in 2025), and defenders are advised to block dynamic DNS services to disrupt C2 resolution.
MITRE Techniques
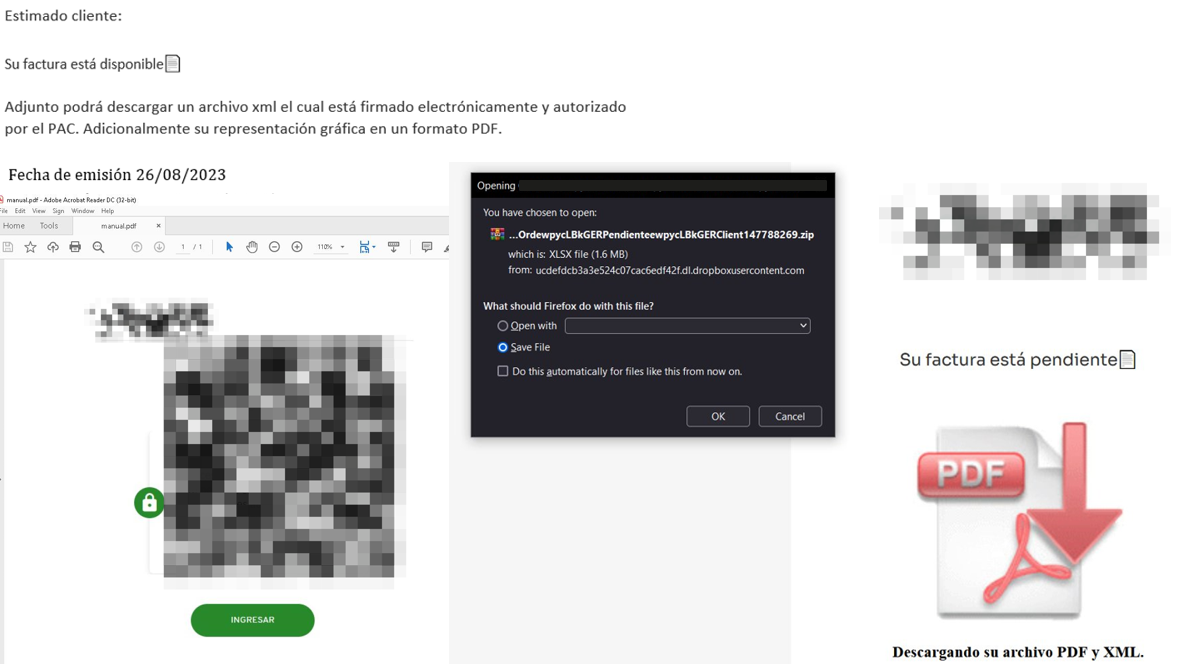
- [T1566.002 ] Spearphishing Link – Initial infection uses emails with malicious links to download PDFs and archives: ‘it starts with emails mimicking the delivery of pending invoices to trick victims into downloading a PDF file by clicking a malicious link.’
- [T1574.002 ] DLL Side-Loading – The MSI installs a legitimate executable that loads an attacker-controlled DLL (PixelPaint.dll) which is JanelaRAT: ‘This DLL is actually JanelaRAT, delivered as the final payload.’
- [T1547.001 ] Registry Run Keys / Startup Folder – Persistence via a shortcut placed in the user’s Startup folder to run the renamed executable at logon: ‘An LNK shortcut is created in the user’s Startup folder, pointing to the renamed nevasca.exe executable, ensuring persistence.’
- [T1059.001 ] PowerShell – Post-exploitation uses a downloaded PowerShell to re-establish persistence and download the PixelPaint.dll: ‘The first subroutine executes a PowerShell downloaded from a staging server during post-exploitation.’
- [T1027 ] Obfuscated Files or Information – Code and strings are obfuscated and encrypted (Eazfuscator/ConfuserEx, AES+Base64) to hinder analysis: ‘All JanelaRAT samples utilize encrypted strings for sending information to the C2 and obfuscating embedded data.’
- [T1057 ] Process Discovery – The malware checks for specific processes related to banking security to decide behavior and report via the “AN” parameter: ‘AN Yes or No depending on whether banking security software process exists.’
- [T1113 ] Screen Capture – The implant captures and exfiltrates desktop images or cropped regions to the C2: ‘Capture desktop image Send compressed screenshots to the C2.’
- [T1056.001 ] Input Capture: Keylogging – JanelaRAT captures keystrokes as part of credential harvesting: ‘Keylogging Keystroke capture.’
- [T1071.001 ] Application Layer Protocol: Web Protocols – The malware builds and executes periodic HTTP requests to beacon and download payloads: ‘builds and executes periodic HTTP requests to the C2, reporting the malware’s version and the victim machine’s security environment.’
- [T1497 ] Virtualization/Sandbox Evasion – Anti-analysis checks detect sandbox or automation environments using accessibility/screen components: ‘includes anti-analysis routines and computer environment checks, such as sandbox detection through the Magnifier and MagnifierWindow components.’
Indicators of Compromise
- [File Hash ] Dropper and payload samples – 808c87015194c51d74356854dfb10d9e (MSI dropper), d7a68749635604d6d7297e4fa2530eb6 (JanelaRAT DLL)
- [Domain ] Primary C2 – ciderurginsx[.]com (reported primary C2 domain)
- [File Name ] Deployed binaries/libraries – PixelPaint.dll (JanelaRAT implant), nevasca.exe (legitimate executable used to sideload the DLL)
Read more: https://securelist.com/janelarat-financial-threat-in-latin-america/119332/