Recent incidents — the Anthropic source-code leak and the Mercor supply-chain compromise — demonstrate that AI security failures are occurring now and expose sensitive data, internal systems, and proprietary technology. Enterprises must prioritize preventing human-error and supply-chain exposures across AI integrations, dependencies like LiteLLM, and cloud ecosystems such as Microsoft 365….
Category: Threat Research

Gen Threat Labs attributes a new x64 infostealer called Remus to the Lumma Stealer family, presenting multiple lines of evidence including identical string obfuscation, AntiVM checks, direct syscalls, indirect control-flow obfuscation, and a near-identical Application-Bound Encryption (ABE) bypass. Remus evolves Lumma’s design with 64-bit builds, EtherHiding (Ethereum smart-contract) dead-drop C2 resolution, new anti-analysis checks, and test builds named Tenzor that link the two families; #Remus #Lumma
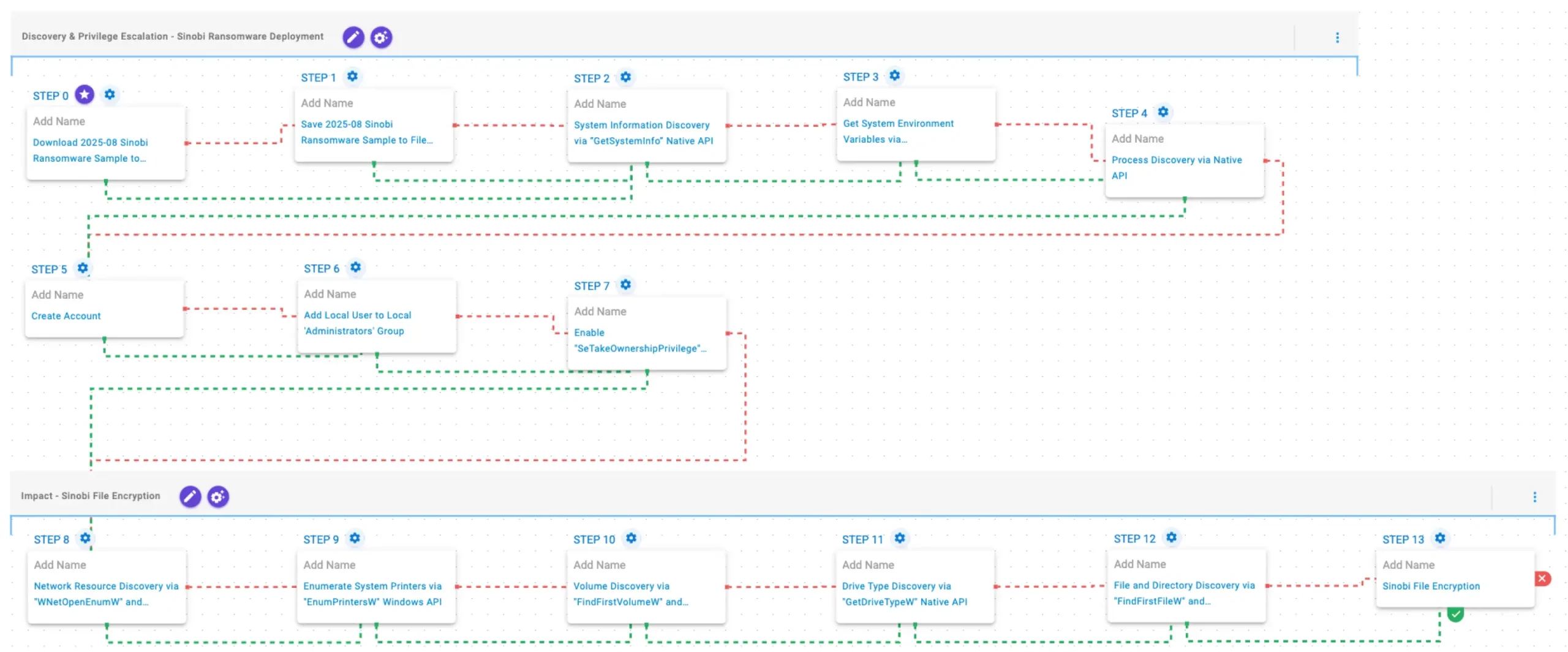
Sinobi is a financially motivated ransomware group that emerged in June 2025 operating a closed, hybrid Ransomware-as-a-Service model and likely represents a rebrand or direct successor to the Lynx and INC families. AttackIQ released an emulation of Sinobi’s TTPs for its Adversarial Exposure Validation (AEV) platform to help organizations validate detection,…

Iranian-affiliated APT actors have been exploiting internet-facing programmable logic controllers (PLCs), particularly Rockwell Automation/Allen-Bradley devices, to extract project files and manipulate data on HMI and SCADA displays, causing operational disruption and financial loss across multiple U.S. critical infrastructure sectors. U.S. organizations are urged to review the TTPs and IOCs, remove PLCs…
LummaStealer resurfaced after a 2025 law-enforcement disruption by rapidly migrating hosting, adopting alternative loaders and delivery techniques (including ClickFix), and pairing with CastleLoader to enable in-memory execution and heavy obfuscation. Bitdefender’s analysis identified 211 IoCs (2 subdomains, 180 domains, 29 IPs), thousands of historical domain/IP resolutions, 103,038 potential victim IPs communicating with IoC IPs, and numerous email-connected and weaponized domains — artifacts and the full report are available for download. #LummaStealer #CastleLoader

Threat actors exploited Anthropic’s Claude Code npm release packaging error to host malicious GitHub releases that distributed Vidar, GhostSocks, and PureLog Stealer via trojanized archives and a Rust-compiled dropper. TrendAI Research tracked the campaign to the repository github[.]com/leaked-claude-code/leaked-claude-code (GitHub account idbzoomh1), published detection guidance, IOCs, and immediate mitigation steps including endpoint…
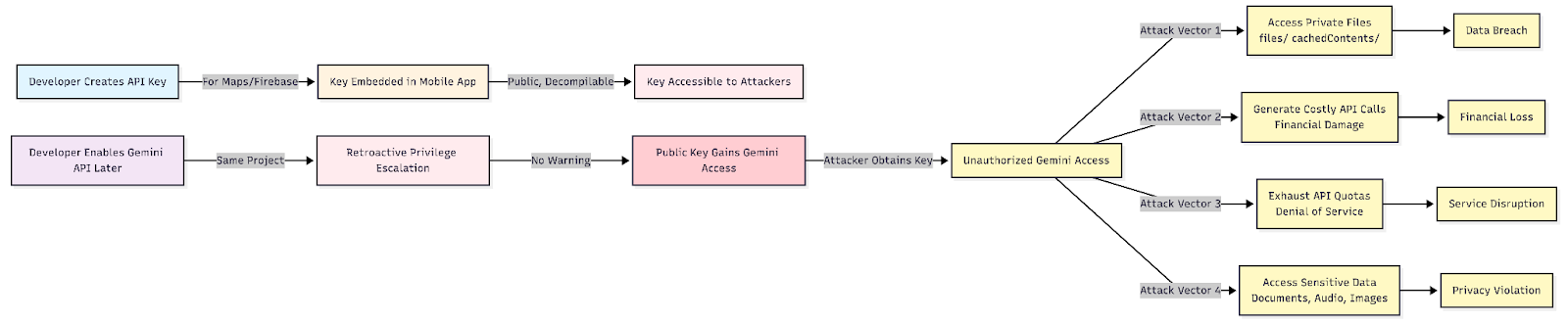
Google’s long-standing public API key format (AIza…) was silently elevated to grant access to the Gemini Generative Language API whenever Gemini is enabled on a Google Cloud project, turning keys embedded in mobile apps into live AI credentials. CloudSEK’s BeVigil scan of the top 10,000 Android apps found 32 live keys across 22 high-install apps (500M+ installs) with confirmed file exposure in ELSA Speak. #Gemini #ELSA
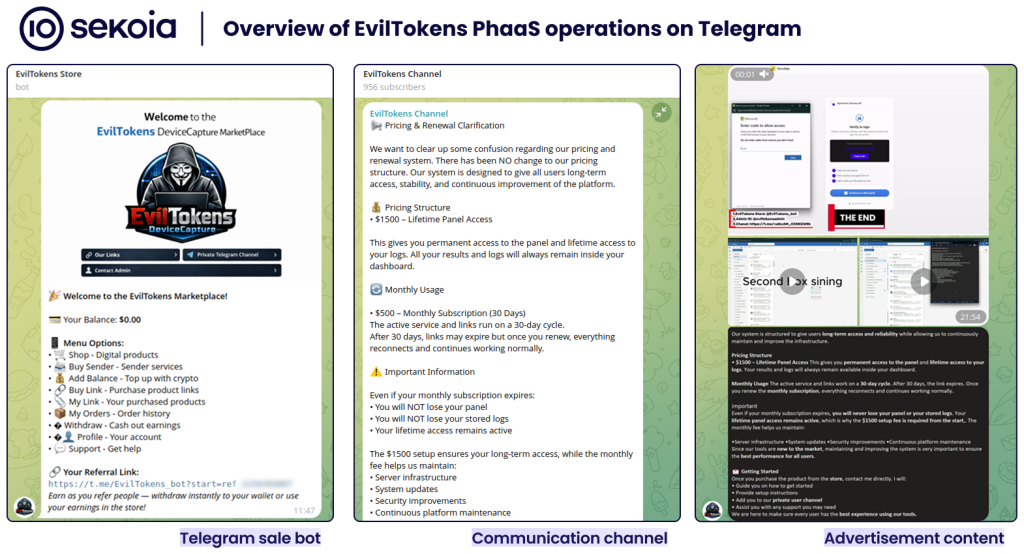
EvilTokens is a Phishing-as-a-Service (PhaaS) that provides turnkey Microsoft device code phishing pages, a centralised affiliate administration panel, and a custom browser to weaponise harvested access and refresh tokens for mailbox access and persistence. Its backend integrates an AI-driven pipeline that uses Microsoft Graph API and chained LLM prompts to automatically identify exploitable payment threads and draft tailored BEC emails, dramatically accelerating post-compromise fraud. #EvilTokens #MicrosoftGraphAPI
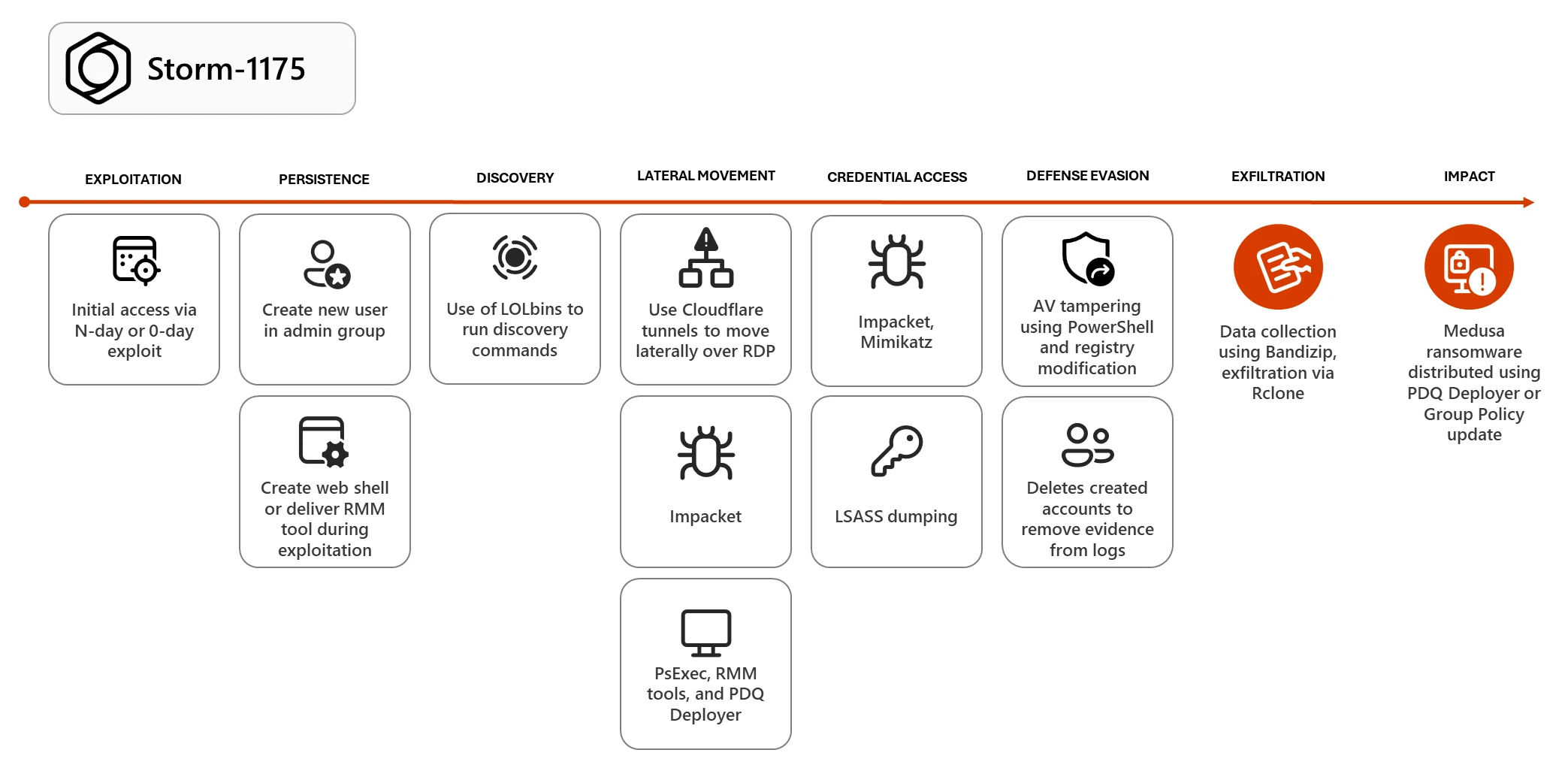
Storm-1175 (reported alongside the public label “OWASSRF”) has exploited multiple public-facing application vulnerabilities—including CVE‑2022‑41080/CVE‑2022‑41082 in Exchange OWA—to gain initial access, deploy web shells or remote access payloads, and rapidly move to Medusa ransomware deployment. The actor has also leveraged zero-days and N-day flaws (e.g., CVE‑2026‑23760 in SmarterMail and CVE‑2025‑10035 in GoAnywhere MFT), abused LOLBins, RMM tools, Impacket, PDQ Deployer, and Rclone for credential theft, lateral movement, exfiltration, and Defender tampering to enable double-extortion operations. #Storm-1175 #Medusa
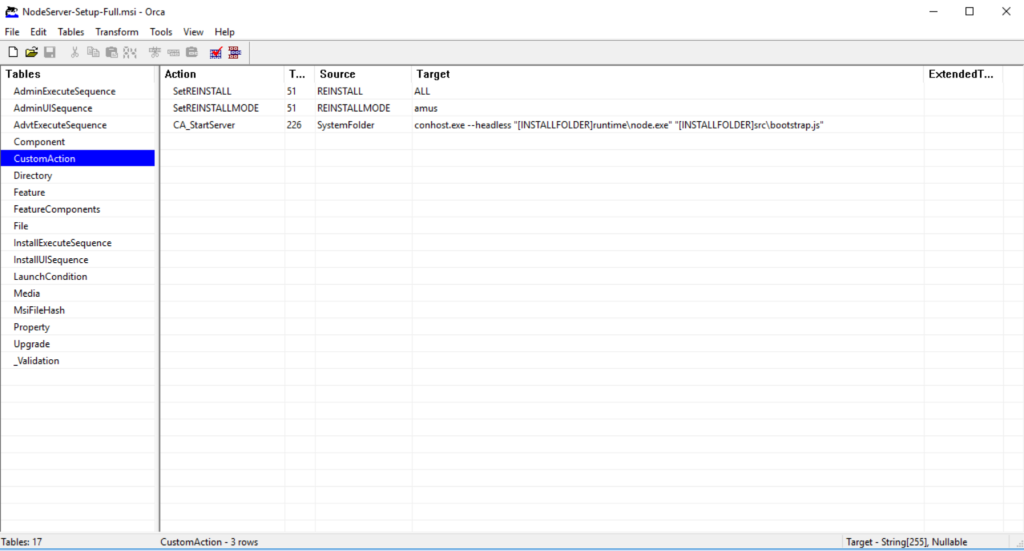
Netskope Threat Labs uncovered a ClickFix campaign that delivers a modular Node.js-based infostealer to Windows users via malicious MSI installers that install silently, persist via a Registry Run key, and execute stealing modules in-memory after establishing a gRPC-over-Tor C2 channel. An OPSEC failure exposed support.proto and admin.proto files, revealing a MaaS backend with multi-operator management, automated wallet tracking, and module deployment capabilities. #ClickFix #NodeJSInfostealer
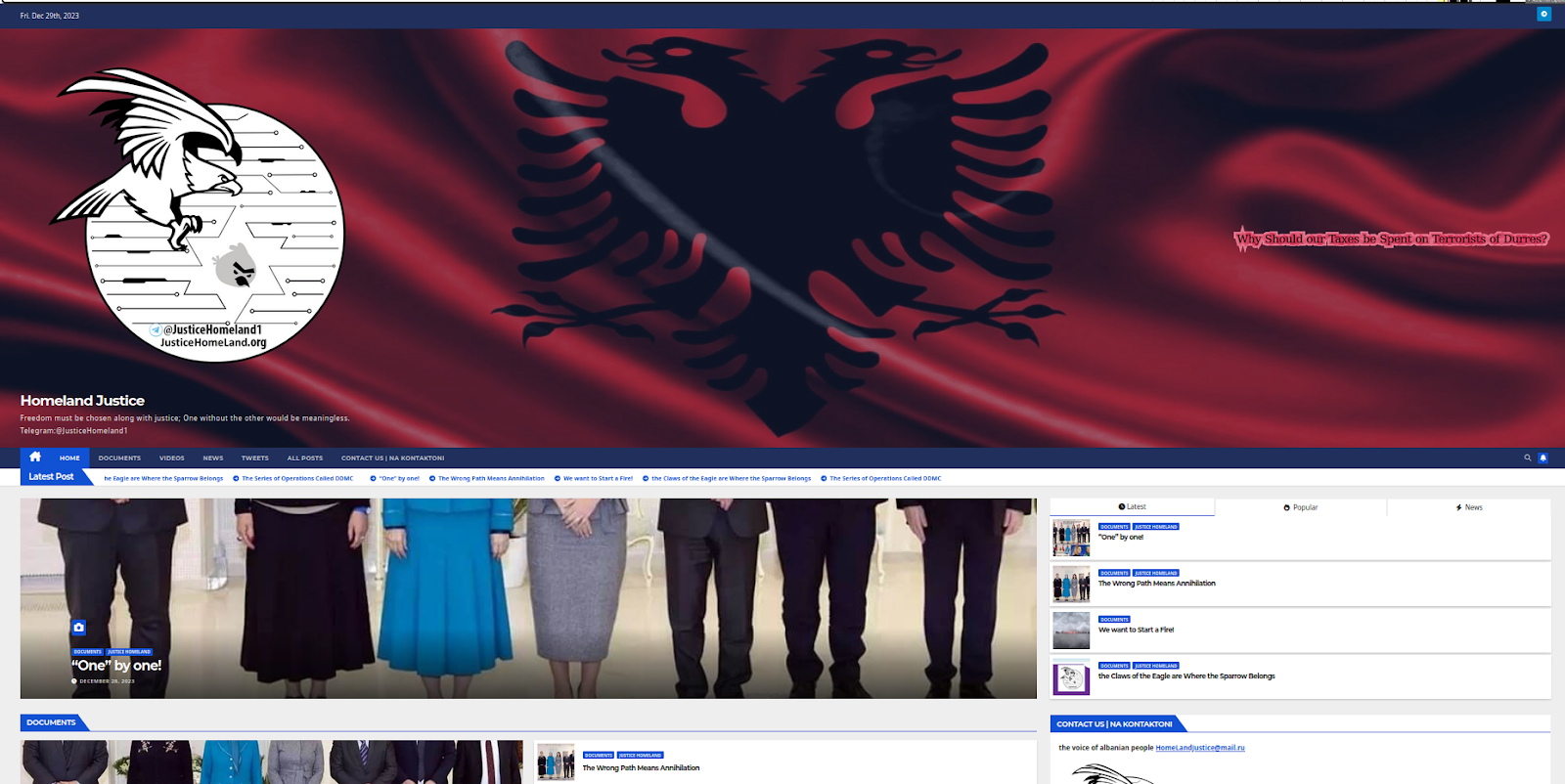
The report assesses Homeland Justice, Karma/KarmaBelow80, and Handala as a single, state-aligned cyber influence ecosystem directed by Iran’s MOIS that fuses low-to-moderate intrusion capability with coordinated information operations to generate high-impact narratives. The actors rely on identity- and access-focused compromises, ephemeral domains, and Telegram-based command-and-control and amplification to convert modest technical access into widely publicized “hack-and-leak” events. #HomelandJustice #Handala #KarmaBelow80
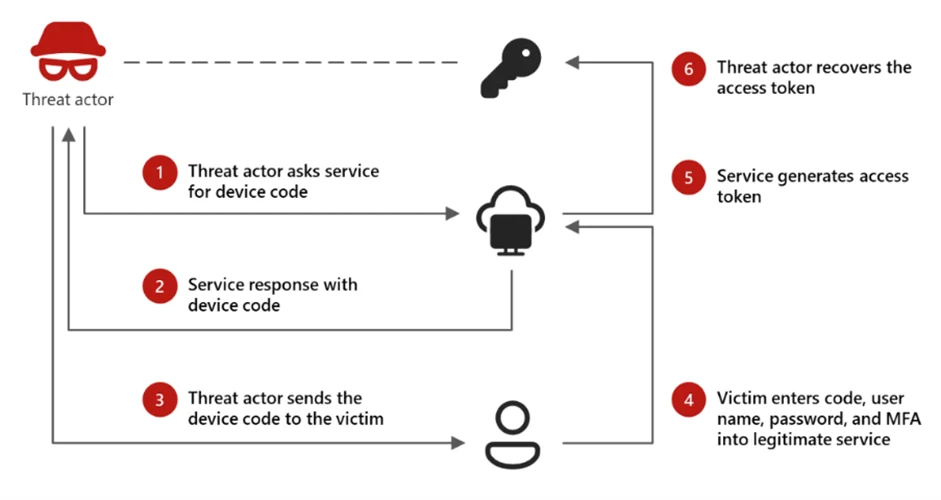
Microsoft Defender observed the Storm-2372 device code phishing campaign that abused the OAuth device code flow, dynamic on-demand code generation, and short-lived cloud infrastructure to bypass MFA and evade signature- and reputation-based controls. The campaign used automation platforms (e.g., Railway.com), cloud hosting (Vercel, Cloudflare Workers, AWS Lambda), clipboard hijacking, Microsoft Graph reconnaissance, and malicious inbox rules to maintain persistence and exfiltrate high-value email data. #Storm2372 #RailwayCom

Cyble Blaze AI uses agentic AI with a dual-memory architecture (neural and vector memory) and coordinated autonomous agents to forecast threats up to six months in advance while automating detection and remediation across endpoints, cloud systems, and external intelligence sources. By correlating signals from dark‑web marketplaces, leaked credentials, new vulnerabilities, and behavioral anomalies into decision-ready actions and reports, it shifts security from reactive alerting to predictive prevention. #CybleBlazeAI #agenticAI

March saw rapid, machine-speed exploitation of public-facing services and AI infrastructure—critical flaws in Pac4j, Ingress‑NGINX, and Langflow enabled authentication bypasses and unauthenticated RCE that were weaponized within hours. A supply‑chain campaign attributed to TeamPCP abused GitHub Actions to spread credential‑stealing backdoors across Trivy, Checkmarx, PyPI packages, and more, highlighting the need for runtime detection and AI‑infrastructure inventorying. #TeamPCP #Langflow
.png?language=en)
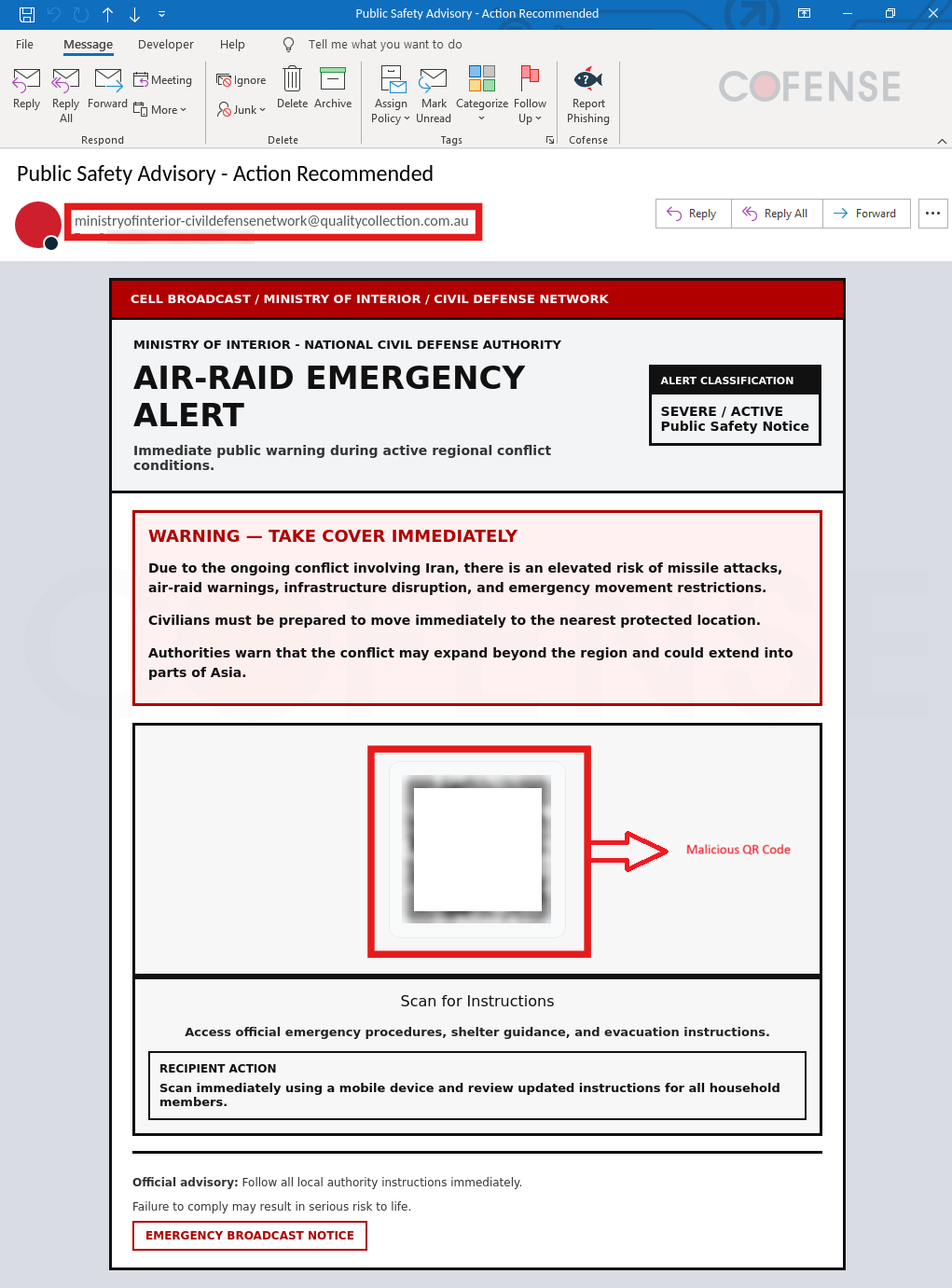
Cofense PDC identified a phishing campaign impersonating a government emergency alert (labeled “SEVERE / ACTIVE”) that used a QR code to redirect victims to a Microsoft-themed credential-harvesting page. The campaign leveraged fear of regional conflict and authoritative impersonation to drive quick user action and credential compromise. #MinistryOfInterior #CofensePDC
