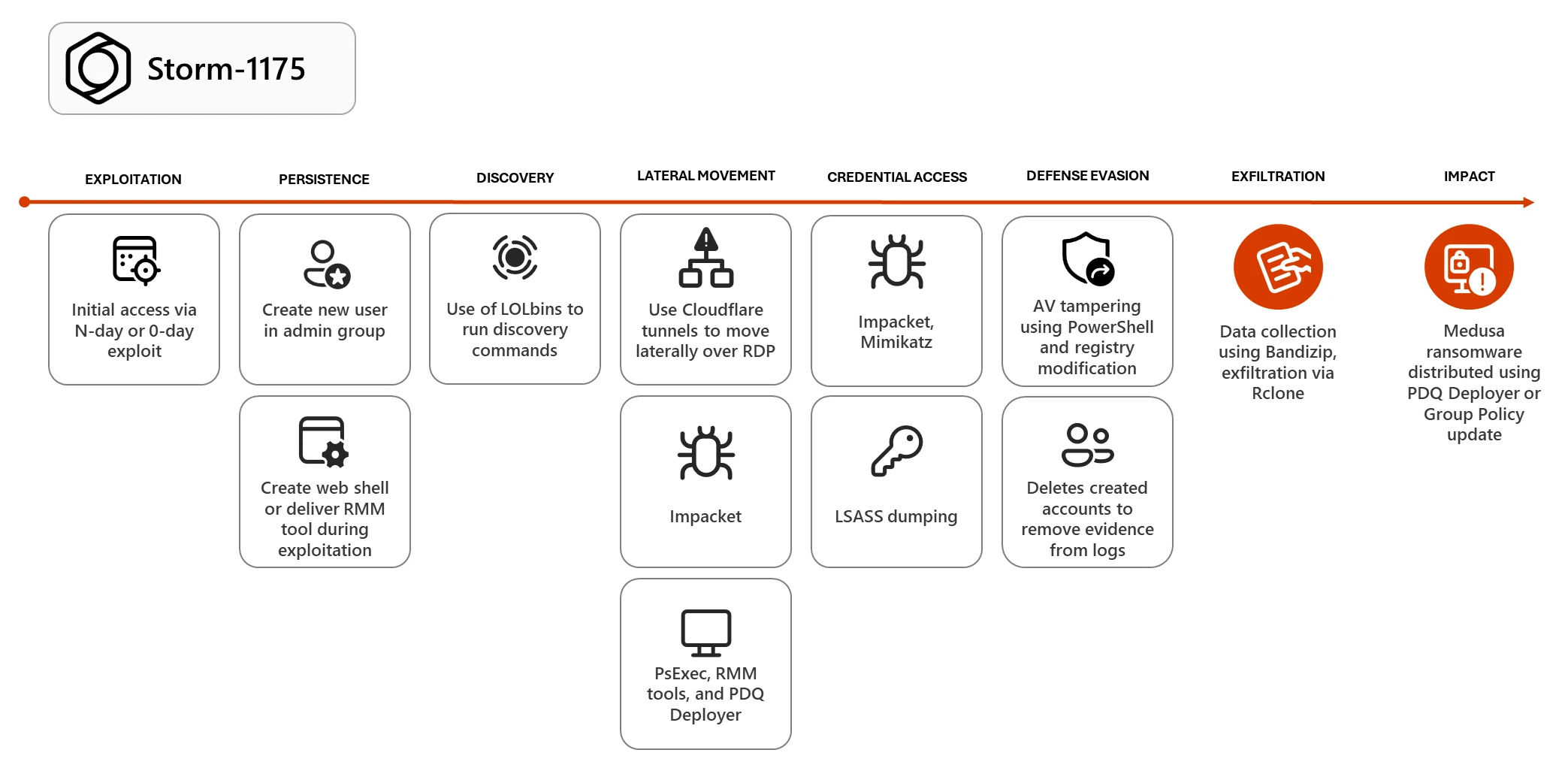
Storm-1175 (reported alongside the public label “OWASSRF”) has exploited multiple public-facing application vulnerabilities—including CVE‑2022‑41080/CVE‑2022‑41082 in Exchange OWA—to gain initial access, deploy web shells or remote access payloads, and rapidly move to Medusa ransomware deployment. The actor has also leveraged zero-days and N-day flaws (e.g., CVE‑2026‑23760 in SmarterMail and CVE‑2025‑10035 in GoAnywhere MFT), abused LOLBins, RMM tools, Impacket, PDQ Deployer, and Rclone for credential theft, lateral movement, exfiltration, and Defender tampering to enable double-extortion operations. #Storm-1175 #Medusa
Keypoints
- Initial access often achieved by exploiting web-facing application vulnerabilities (notably Exchange/OWA CVE‑2022‑41080/CVE‑2022‑41082) leading to web shell or remote access payload deployment.
- Storm-1175 has exploited both Windows and Linux targets (including suspected Oracle WebLogic exploitation) and used at least three zero-days, such as CVE‑2026‑23760 (SmarterMail) and CVE‑2025‑10035 (GoAnywhere MFT), often prior to public disclosure.
- After foothold, the actor establishes persistence by creating local admin accounts, modifying Defender settings, and using living-off-the-land binaries (PowerShell, PsExec) plus tools like Impacket and PDQ Deployer to move laterally and deliver payloads.
- Storm-1175 heavily abuses legitimate remote monitoring and management (RMM) products (Atera, Level RMM, N-able, DWAgent, MeshAgent, ConnectWise ScreenConnect, AnyDesk, SimpleHelp) for persistence, remote access, and payload deployment.
- Credential theft techniques include LSASS memory dumping, Mimikatz usage, enabling WDigest caching, extracting Veeam passwords, and dumping NTDS.dit/SAM from domain controllers to escalate and proliferate access.
- Data exfiltration commonly uses Bandizip for collection and Rclone for synchronization to attacker-owned cloud resources, followed by Medusa ransomware deployment via PDQ Deployer or Group Policy changes for broad impact.
- Defensive tampering includes modifying Microsoft Defender registry settings and adding drive exclusions via encoded PowerShell; recommended mitigations include perimeter scanning, isolation/WAF/VPN, Credential Guard, tamper protection, and attack surface reduction.
MITRE Techniques
- [T1190] Exploit Public-Facing Application – Used to gain initial access by exploiting Exchange/OWA vulnerabilities: ‘exploitation of CVE‑2022‑41080 provided initial access by exposing Exchange PowerShell via Outlook Web Access (OWA)’.
- [T1505.003] Server Software Component: Web Shell – Storm-1175 establishes persistence and control by deploying web shells: ‘typically creates a web shell or drops a remote access payload to establish their initial hold in the environment.’
- [T1136] Create Account – The actor creates new local accounts and elevates them to administrators for persistence: ‘creates a new user and adding that user to the administrators group’.
- [T1078] Valid Accounts – Storm-1175 uses obtained administrator credentials and valid accounts for lateral movement and privileged actions: ‘after gaining administrator credentials… used a script to recover passwords from Veeam backup software’.
- [T1059.001] Command and Scripting Interpreter: PowerShell – Encoded and regular PowerShell are used for execution, configuration, and adding AV exclusions: ‘encoded PowerShell commands to add the C: drive to the antivirus exclusion path’.
- [T1021] Remote Services – Remote Desktop Protocol (RDP) and related remote services are used for lateral movement; actor enables RDP by modifying firewall policy: ‘modify the Windows Firewall policy to enable Remote Desktop’.
- [T1036] Masquerading – Adversary renames tools/tunnels to mimic legitimate binaries to evade detection: ‘Cloudflare tunnels (renamed to mimic legitimate binaries like conhost.exe)’.
- [T1572] Protocol Tunneling – Cloudflare tunnels used to move laterally and relay remote sessions across network boundaries: ‘Cloudflare tunnels … to move laterally over Remote Desktop Protocol (RDP)’.
- [T1219] Remote Access Software – Legitimate RMM and remote access tools are repurposed for persistence and interactive remote control: ‘Storm-1175 has a rotation of tools… Atera RMM… AnyDesk… SimpleHelp’.
- [T1072] Software Deployment Tools – PDQ Deployer is abused for silent deployment and wide-scale payload distribution including ransomware: ‘relies on PDQ Deployer… for both lateral movement and payload delivery, including ransomware deployment throughout the network.’
- [T1003.001] OS Credential Dumping: LSASS Memory – Credential dumping from LSASS is used to collect credentials: ‘dumps credentials from LSASS… Mimikatz in identified intrusions in 2025.’
- [T1003.003] OS Credential Dumping: NTDS – Dumping NTDS.dit from Domain Controllers to obtain AD account hashes and passwords for offline cracking: ‘used tools like PsExec to pivot to a Domain Controller, where they have accessed the NTDS.dit dump’.
- [T1112] Modify Registry – The actor modifies registry settings to enable WDigest caching and to tamper with Microsoft Defender configuration: ‘modifying the registry entry UseLogonCredential to turn on WDigest credential caching’ and ‘modifies the Microsoft Defender Antivirus settings stored in the registry’.
- [T1562.001] Impair Defenses: Disable or Modify Tools – Attackers add AV exclusions and disable protections to prevent detection and blocking of payloads: ‘encoded PowerShell commands to add the C: drive to the antivirus exclusion path’ and ‘turn off Microsoft Defender Antivirus’.
- [T1567] Exfiltration Over Web Service / Cloud Storage – Rclone is used to synchronize and exfiltrate large volumes of data to attacker-controlled cloud resources: ‘often uses Bandizip to collect files and Rclone for data exfiltration’.
Indicators of Compromise
- [SHA-256 ] Ransomware & tool binaries – 0cefeb6210b7103fd32b996beff518c9b6e1691a97bb1cda7f5fb57905c4be96 (Gaze.exe, Medusa ransomware), e57ba1a4e323094ca9d747bfb3304bd12f3ea3be5e2ee785a3e656c3ab1e8086 (lsp.exe, Rclone), and 2 more hashes.
- [File name ] Malicious or renamed executables used in intrusions – Gaze.exe (Medusa ransomware), lsp.exe (Rclone) — observed as payloads or renamed tools used by the actor.
- [IP address ] SimpleHelp/C2 infrastructure – 185.135.86[.]149, 134.195.91[.]224, and 85.155.186[.]121 associated with SimpleHelp activity in identified intrusions.