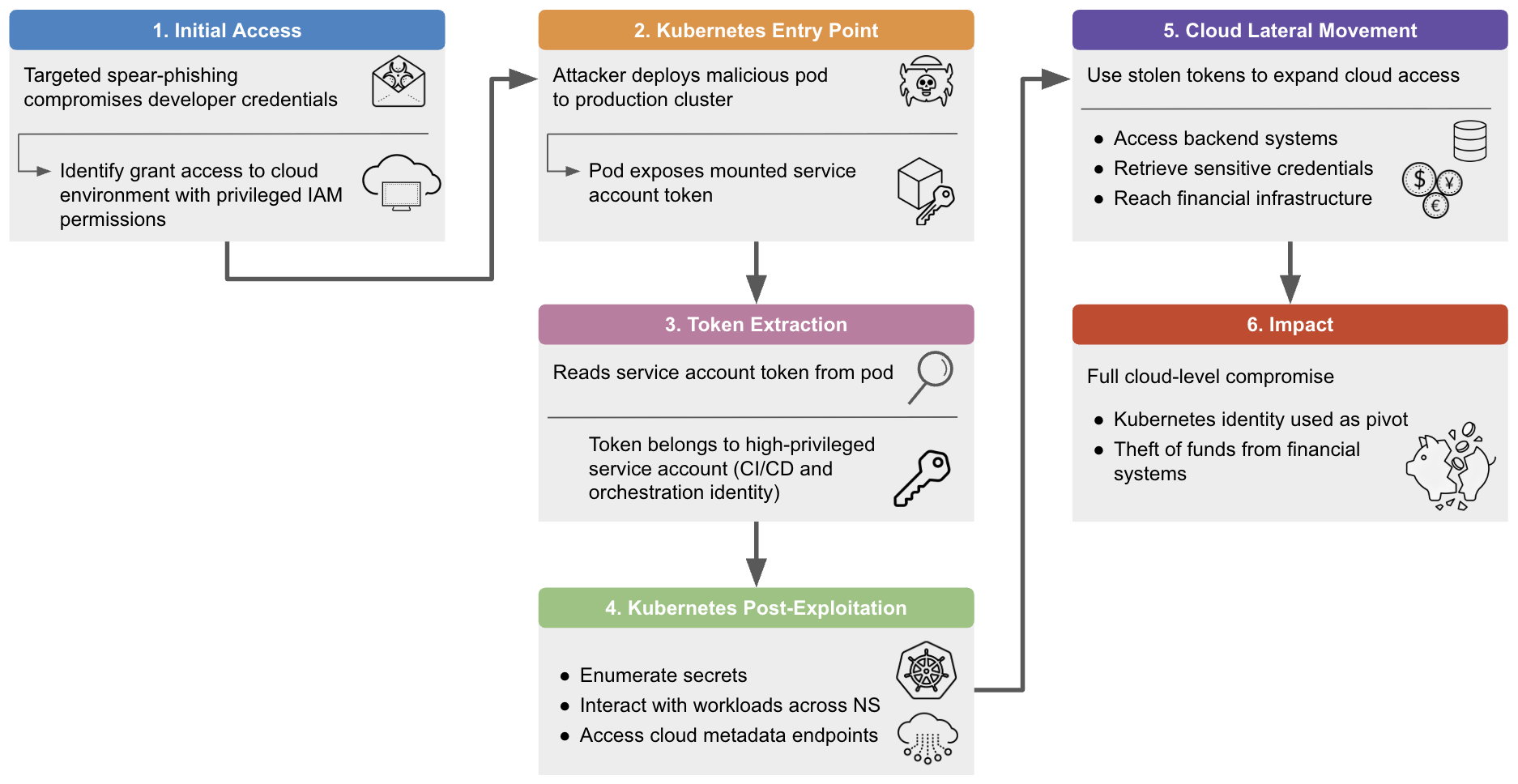
Kubernetes clusters are being actively targeted to steal service account tokens and pivot from compromised pods into cloud-hosted backend systems, with token-theft activity up 282% year-over-year and the IT sector representing over 78% of observed activity. Two representative cases—token theft enabling lateral movement in a cryptocurrency exchange by the Slow Pisces…
Category: Threat Research

Team Cymru discovered an open directory on 5.78.84[.]144 that contained a full Beast ransomware operator toolkit, revealing tools and binaries used across reconnaissance, credential theft, lateral movement, exfiltration, and cleanup. The collection included Windows and Linux Beast binaries, scripts to disable backups and wipe traces, and evidence of data exfiltration workflows…
A RAR archive exceeding 500 MB containing exactly 500 scanned Italian identity documents (identity cards, passports, driving licences) and selfie identification photos was published on a Telegram channel signing as “Anonymous Algeria”, active since November 2025. CERT-AGID notes most files date from 2020–2021, that the dataset may be recycled material consistent with INPS-themed smishing campaigns, and urges reporting, SPID checks, and careful monitoring of bank accounts. #AnonymousAlgeria #CERTAGID

Elastic announced nine new Elastic Security integrations that expand visibility and normalization across macOS, cloud services, email protection, identity and SIEM platforms, each shipping with ingest pipelines and prebuilt dashboards for immediate use. Highlights include macOS Security Events, IBM QRadar migration, Proofpoint Essentials, AWS Security Hub, JupiterOne, Airlock Digital, Island Browser, Ironscales, and Cyera with ECS/OCSF normalization and built-in support for ES|QL, Attack Discovery and the AI Assistant. #macOS #IBMQRadar

March 2026 saw a wave of high-profile software supply-chain attacks, including an Axios NPM compromise and malicious PyPI releases of LiteLLM that were used to deliver cross-platform RATs and credential-harvesting payloads. Both incidents involved maintainer account compromise or malicious publishes that executed code at install/startup and contacted C2 infrastructure. #Axios #LiteLLM

Team Cymru analyzed internet-exposed ICS/OT devices and presented three case studies showing nation-state actors targeting Hitachi RTU560, Moxa NPort, and Rockwell 1756 modules using default credentials, corrupted firmware uploads, device lockout, and protocol exploits. The research highlights thousands of exposed devices—particularly Rockwell and Moxa components—being scanned and targeted, and recommends using…
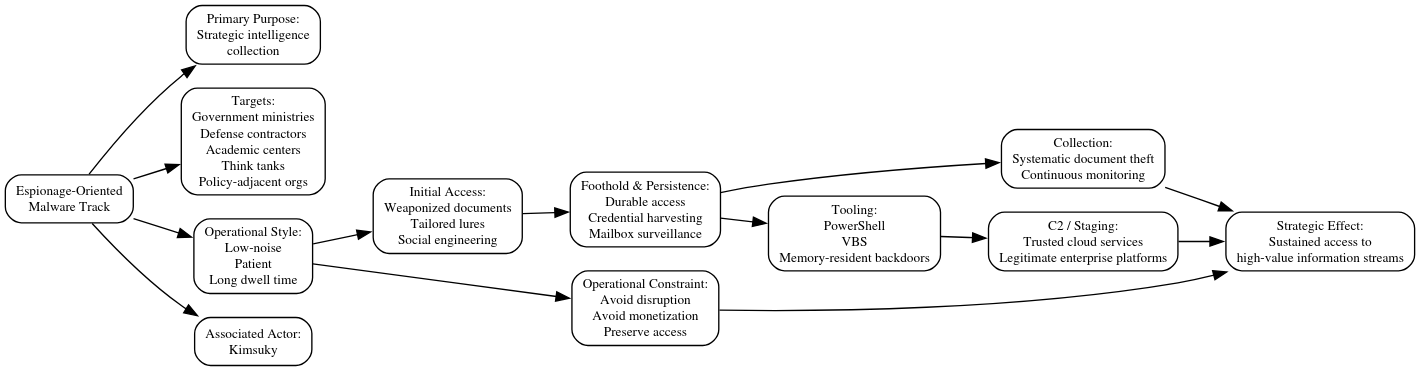
North Korea’s cyber program is a deliberately fragmented, mission-aligned malware ecosystem that treats toolchains as consumable assets to enable parallel espionage, revenue generation, and disruptive operations. This compartmentalized portfolio model increases operational resilience, complicates attribution, and prioritizes rapid tool churn over long-lived platforms #Lazarus #Kimsuky
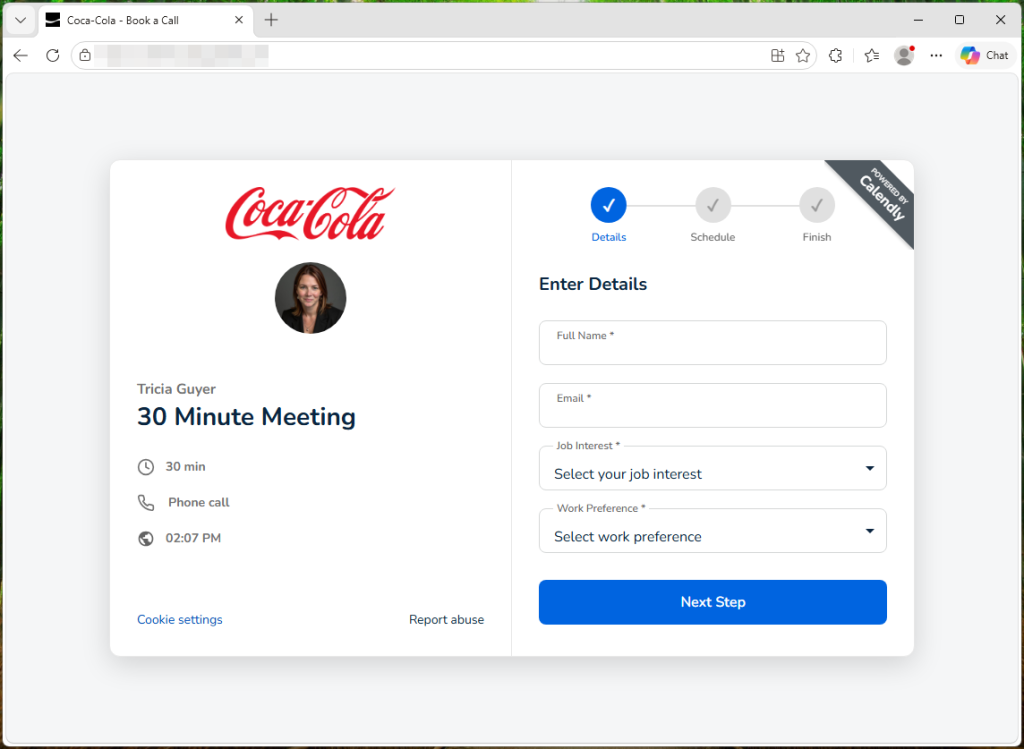
Two coordinated phishing campaigns impersonating Coca-Cola and Ferrari use polished booking and careers pages to harvest credentials via fake login prompts and social-login pages. The Coca-Cola kit notably includes a fake Chrome window that relays credentials and MFA challenges in real time to an attacker-controlled backend, enabling account takeover; the Ferrari…
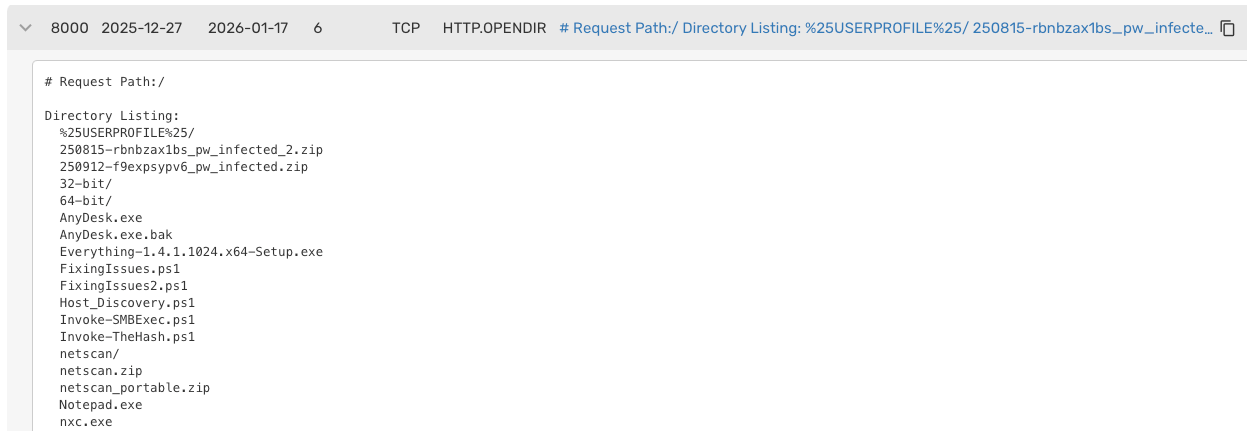
Yurei is a double-extortion ransomware campaign active since September 2025 that appears derived from the open-source Prince Ransomware and contains references to SatanLockv2; researchers found samples first submitted from Morocco and a Tor leak site with only a few victims. Team Cymru discovered open directories on 44.210.101[.]86 and 44.223.40[.]182 hosting a…

The loader component of ReflectPulse extracts configuration from Dropper 2, optionally encrypts and stores the agent module in memory, and uses configured polling intervals to initiate C2 communication over HTTP GET or POST. ReflectPulse supports a stealth mode that encrypts configuration and XOR-repacks each parameter to hinder process memory dump analysis, and the loader can wait for an encrypted agent module from the C2 before authorizing decryption and execution #ReflectPulse #Dropper2

This week’s intelligence highlights critical vulnerabilities across AI frameworks, VMware environments, Kubernetes, EV charging platforms, and industrial control systems that expand the global attack surface and increase exploitation risk. Notable high-risk flaws include RCEs in Wazuh and Cisco FMC, a critical deserialization bug in Langflow, and widespread ICS/EV exposures now tracked in CISA’s KEV catalog. #Wazuh #Langflow

The full source code for Anthropic’s Claude Code CLI was accidentally exposed via debug .map files in the public npm package @anthropic-ai/claude-code 2.1.88, revealing roughly 1,900 files and 512,000+ lines that detail architecture, tools, and guardrails. The leak exposes how permissions and guardrails can be bypassed, prompted rapid mirroring and reimplementations…
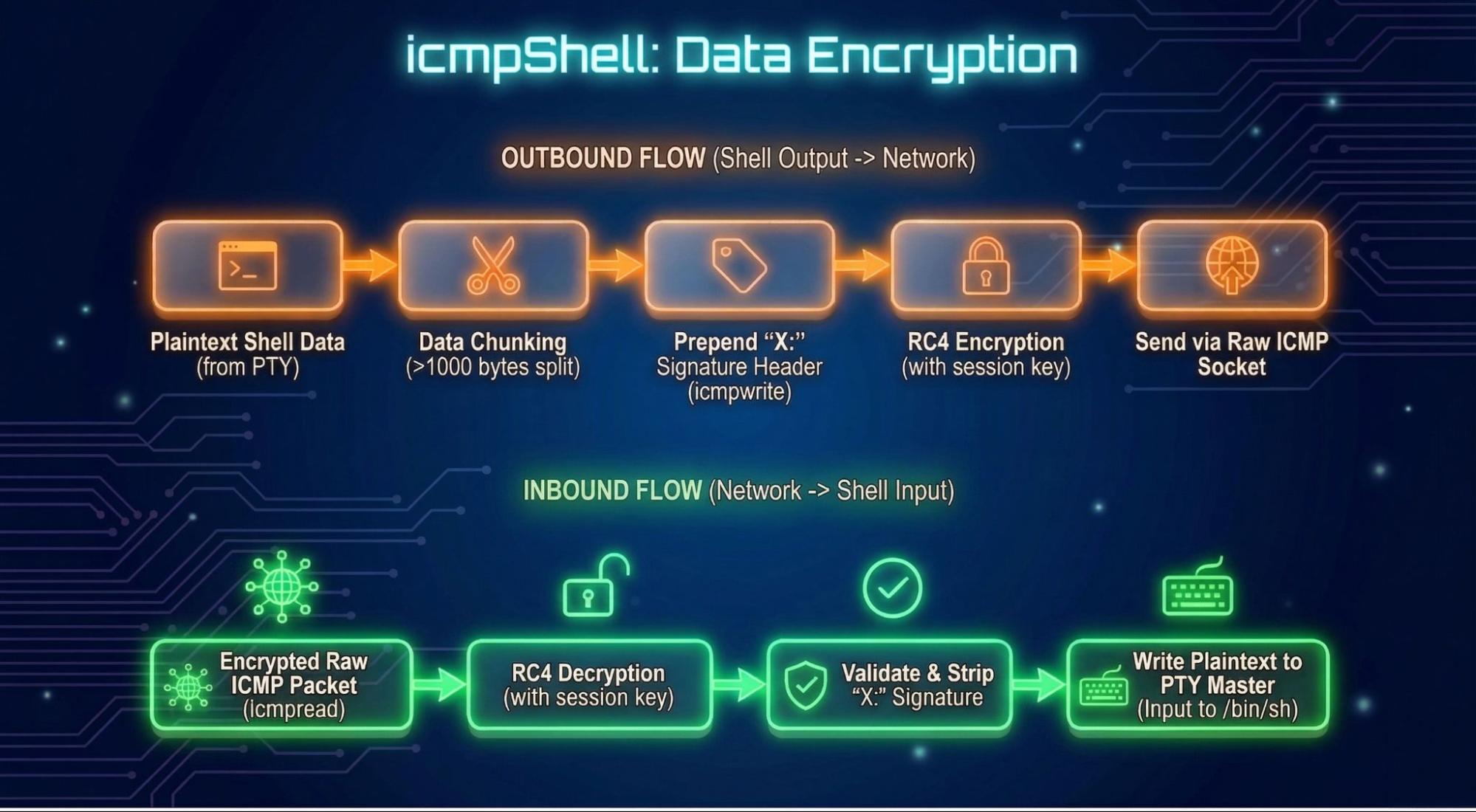
The article analyzes BPFDoor-derived implants (icmpShell/httpShell and multiple Rapid7 variants) that use custom BPF filters, protocol sniffing, and protocol-tunneling C2 to achieve stealthy remote shells and persistence. It highlights key artifacts such as the RC4 key “icmp”, hardcoded ICMP Sequence Number 1234, and active beaconing domains that masquerade as NTP-over-SSL. #BPFDoor #icmpShell
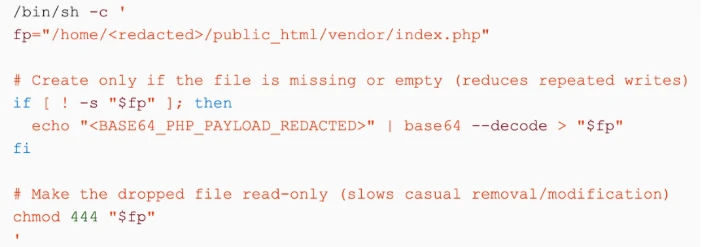
Microsoft Security Copilot augments Microsoft Defender capabilities to help security teams investigate web shell and post-compromise incidents by analyzing obfuscated or encoded scripts and accelerating triage. Defender coverage and prebuilt/hunting queries target cron-based persistence, PHP webshells (e.g., index.php), base64-encoded payloads, and hosting-control-panel abuse to detect and block threats. #WebShell #MicrosoftSecurityCopilot

The author built a proof-of-concept AI-driven monitor that diffs package releases and flagged a malicious npm compromise of Axios that used a phantom dependency with a postinstall hook to deploy cross-platform malware. The incident ties into a wider supply-chain campaign (Trivy → LiteLLM → Telnyx → Axios) attributed to TeamPCP, prompting coordinated detection, takedown, and recommendations for registry monitoring and release soak times. #Axios #TeamPCP