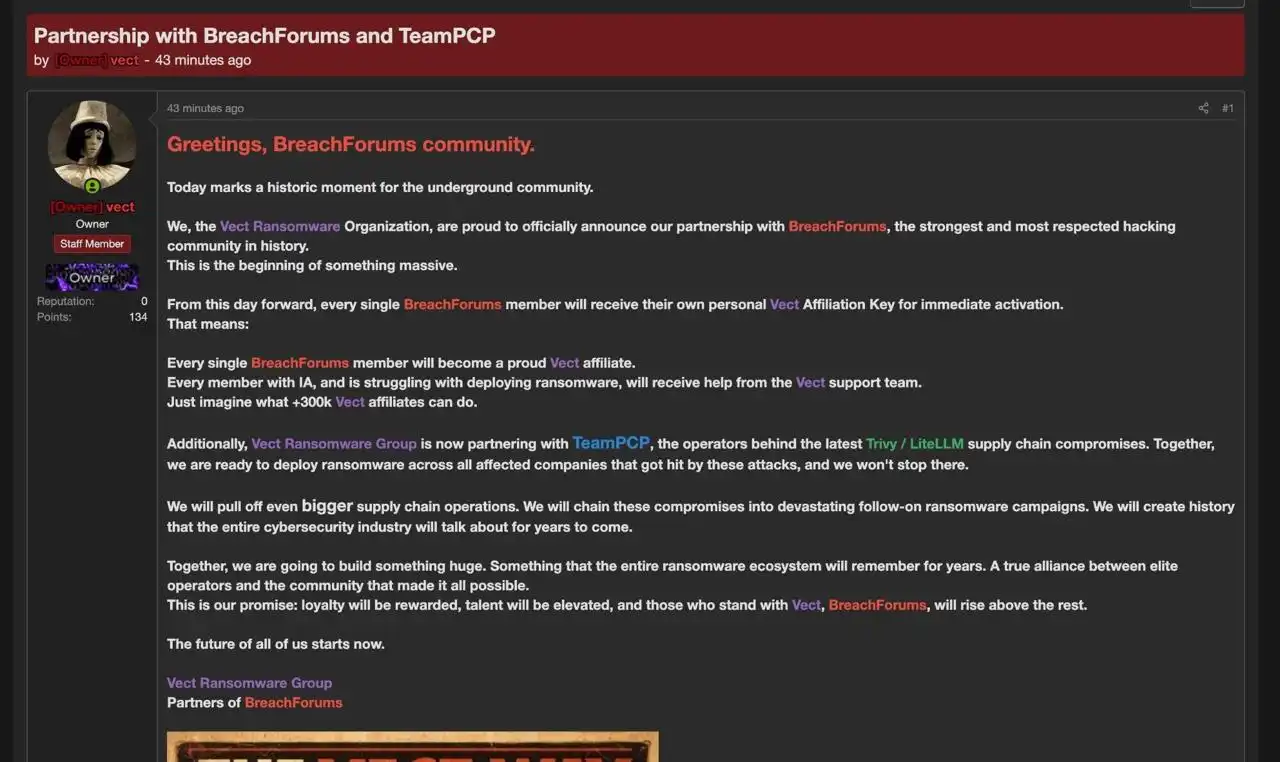
Between late February and March 2026, TeamPCP executed multi-wave supply chain compromises that poisoned widely trusted open-source security and developer tooling — including Aqua Security Trivy, Checkmarx KICS, BerriAI LiteLLM and the Telnyx Python SDK — to plant infostealer payloads into GitHub Actions and PyPI packages. The operation exfiltrated cloud access…
Category: Threat Research
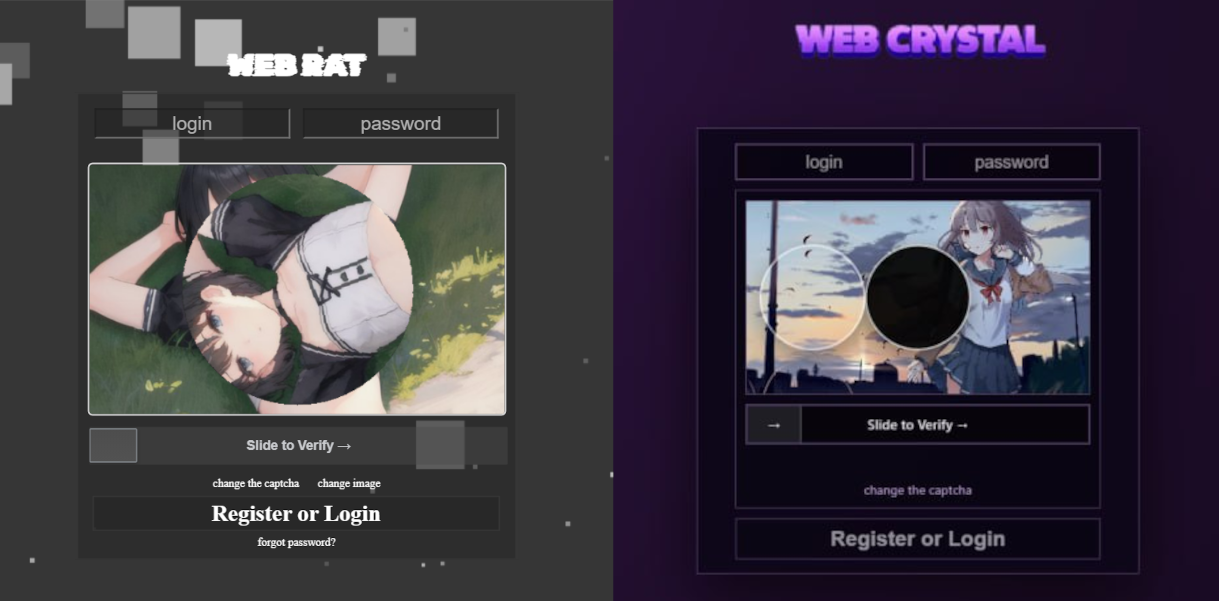
In March 2026 researchers uncovered an active MaaS campaign promoting CrystalX (initially marketed as Webcrystal/WebRAT) via private Telegram chats and a YouTube channel; the RAT offers a builder and a wide feature set including stealer, keylogger, clipper, remote access, spyware, and extensive prankware. Kaspersky detects it as Backdoor.Win64.CrystalX.*, Trojan.Win64.Agent.*, and Trojan.Win32.Agentb.gen, telemetry shows active development and dozens of victims so far. #CrystalXRAT #Webcrystal

Elastic Security Labs disclosed a supply-chain compromise of the widely used axios npm package in which a compromised maintainer account published backdoored versions that used a malicious plain-crypto-js postinstall hook to download a cross-platform RAT. The implants (PowerShell, C++, Python) share an identical C2 protocol and beacon behavior and were delivered from sfrclak[.]com:8000, enabling large-scale, automated compromise via npm installs. #Axios #UNC1069

Check Point Research discovered a zero-day in the TrueConf client (CVE-2026-3502, CVSS 7.8) that allows an attacker controlling an on‑premises TrueConf server to distribute and execute arbitrary files to connected endpoints via the product’s update mechanism. The flaw was abused in a targeted campaign dubbed “TrueChaos” to deploy the Havoc payload against government entities in Southeast Asia. #TrueConf #Havoc
This report analyzes large-scale abuse of the Keitaro tracking platform across spam, malvertising, and traffic-distribution ecosystems, documenting bulk domain registrations, conditional redirects, cloaking, and cookie-based correlations used by threat actors. Researchers found widespread use of cracked/stolen Keitaro licenses tied to malicious campaigns (including activity attributed to TA2726), confirmed Keitaro’s responsiveness to abuse reports, and published domains, IPs, and cookie signatures to aid detection. #Keitaro #TA2726

The Zscaler ThreatLabz analysis details Xloader (rebranded from FormBook), highlighting enhanced obfuscation since version 8.1 and a comprehensive breakdown of its multi-layered HTTP network protocol and encryption. The report describes runtime function decryption, opaque predicates, multiple RC4 encryption stages, decoy C2 IP lists, and HTTP GET/POST commands used to exfiltrate browser and email credentials and to download and execute secondary payloads. #Xloader #Formbook

An attacker used compromised credentials of an Axios maintainer to publish poisoned npm packages that added a malicious dependency and executed a postinstall script to deploy a platform-specific Remote Access Trojan. Developers who ran npm install for the affected versions should treat build machines as fully compromised and rotate secrets immediately….
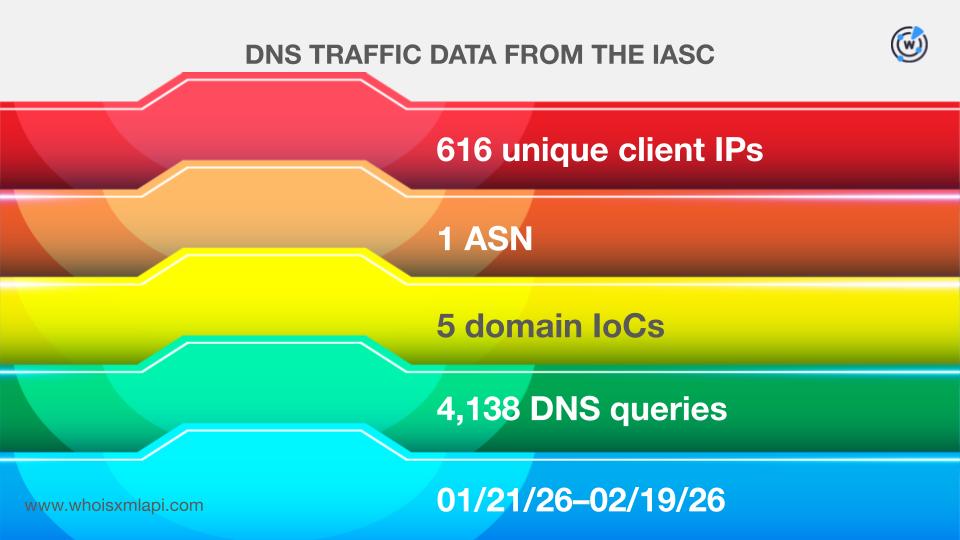
Picus Security’s Red Report 2026 analysis examined 11 attacks that illustrated six of the top 10 MITRE ATT&CK techniques abused in 2025, linking specific groups and malware to tactics such as process injection, scripting interpreters, masquerading, credential theft, and firewall manipulation. Follow-up IOC analysis of 147 network indicators (104 domains, 26 subdomains, 17 IPs) revealed mass bulk-registrations, early signs of malicious intent for many domains, and thousands of email- and client-connected domains and IPs tied to the campaigns #XLoader #EarthAmmit

On March 31, 2026, an attacker hijacked an axios npm maintainer account and published malicious releases ([email protected] and 0.30.4) that added a typosquatted dependency plain-crypto-js which executed a cross-platform RAT during npm install. The compromise was active for about three hours before npm removed the packages; the RAT communicated with C2 sfrclak[.]com and delivered macOS, Windows, and Linux payloads (all containing bugs), while maintainers and npm revoked tokens and mitigations followed. #axios #plain-crypto-js
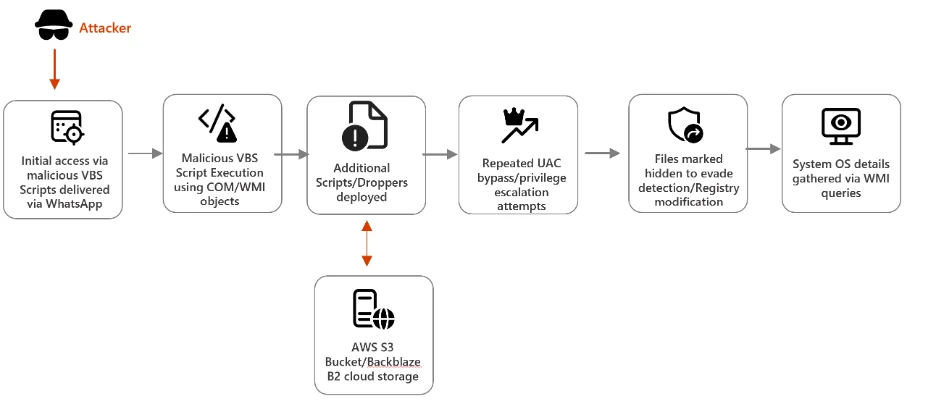
Microsoft Defender Security Research details a campaign in which malicious VBS scripts delivered via WhatsApp download additional VBS payloads and MSI installers from cloud storage, leveraging renamed system utilities and UAC bypass attempts to evade detection and escalate privileges. The report provides Microsoft Defender detections, hunting queries, mitigation recommendations (EDR in block mode, network and web protection, tamper protection, attack surface reduction rules), and IOCs including SHA-256 hashes, cloud storage URLs, and C2 domains. #TrojanVBS_ObfuseKPP #Neescil_top

Nulled WordPress plugins are pirated, cracked copies of premium plugins that frequently contain injected malware, backdoors, and code changes that break update paths and expose sites to compromise. Installing them leads to infections, SEO blacklisting, legal takedowns, and costly recovery—remove nulled plugins and replace them with legitimate or trusted free alternatives. #NulledPlugins #WordPress
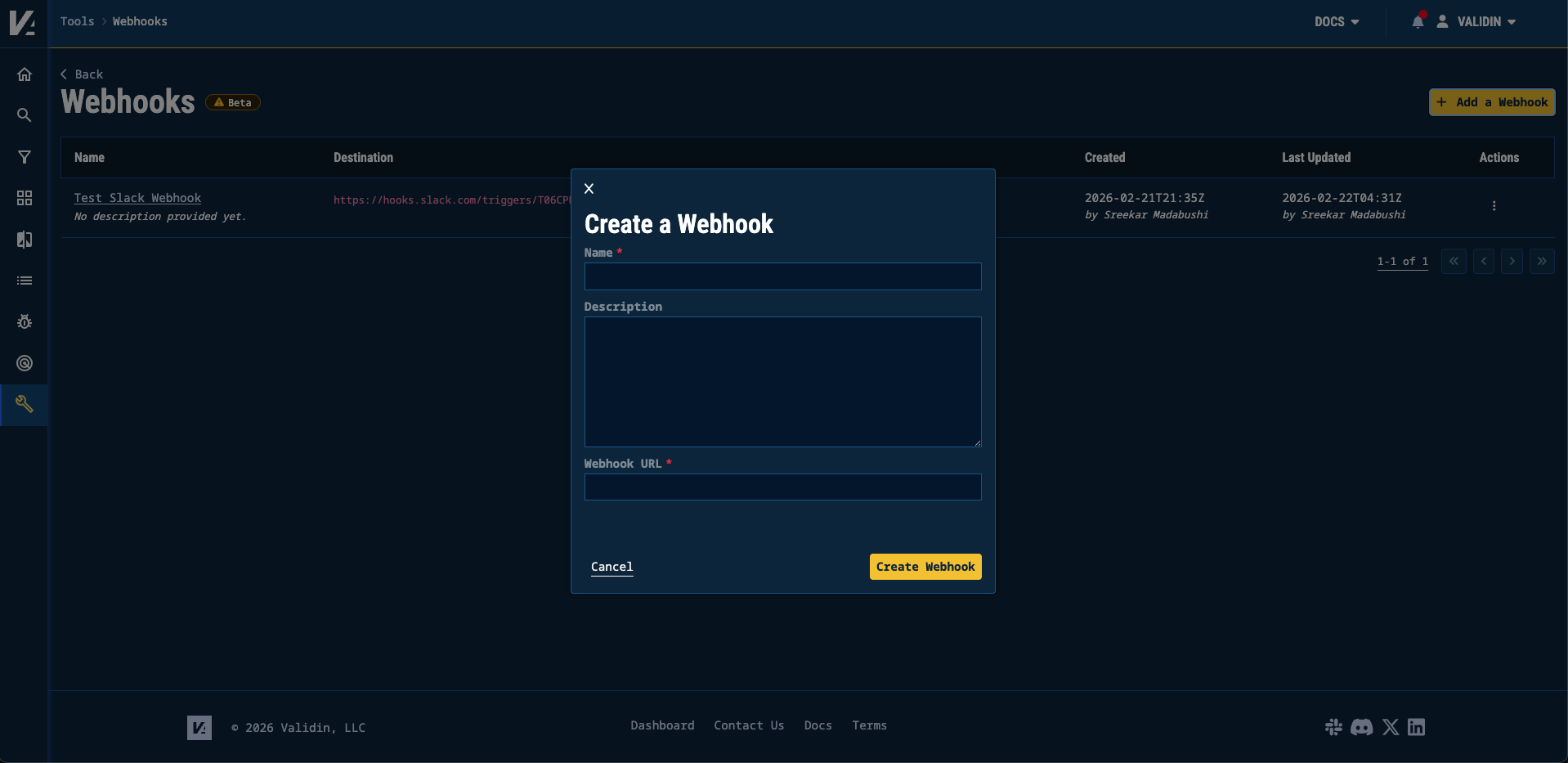
Validin has launched Webhooks in Beta for Enterprise users to enable real-time event ingestion for YARA rule matches and additions to threat profiles. Users can configure endpoints (including Slack) to receive HMAC SHA256-signed payloads, customize event fields, test deliveries, and build automated workflows. #Validin #YARA
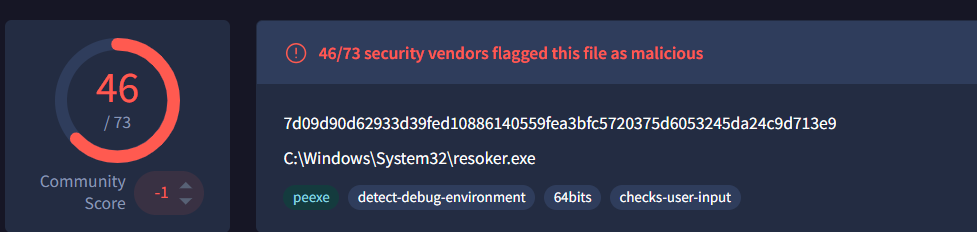
ResokerRAT is a Telegram-controlled Remote Access Trojan that uses the Telegram Bot API as its command-and-control channel to receive commands and exfiltrate data, while implementing persistence, privilege escalation, anti-analysis, and system monitoring features. It supports commands such as /screenshot, /download, /block_taskmgr, and /startup and uses hidden PowerShell execution, registry modifications, keyboard hooks, and process termination to maintain stealth. #ResokerRAT #TelegramBot
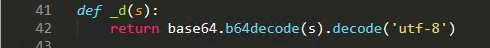
TeamPCP published trojanized Telnyx Python SDK releases (4.87.1 and 4.87.2) to PyPI that execute on import and employ split-file injection, runtime Base64 decoding, and WAV-based steganography to fetch credential‑stealing payloads. The campaign adds Windows persistence (dropped msbuild.exe in user Startup folders) and defenders should downgrade to Telnyx 4.87.0 and treat any…
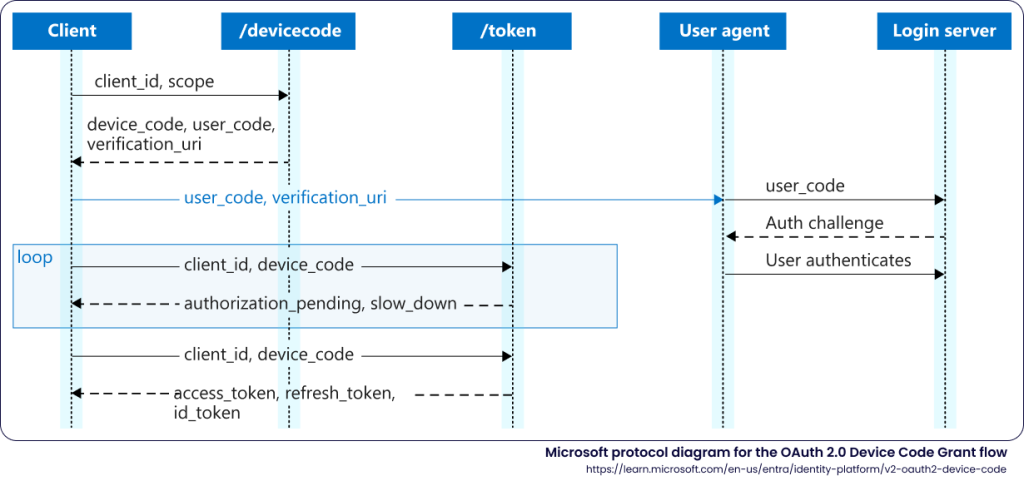
Sekoia discovered EvilTokens, a new Phishing-as-a-Service that provides turnkey Microsoft device code phishing pages and a full backend for token harvesting, PRT conversion, cookie generation, and post-compromise reconnaissance. The kit has been rapidly adopted by affiliates for BEC campaigns and is tracked across 1,000+ domains deployed via Cloudflare Workers and affiliate hosting. #EvilTokens #Microsoft365