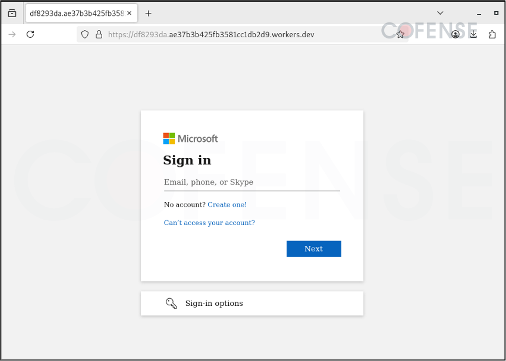
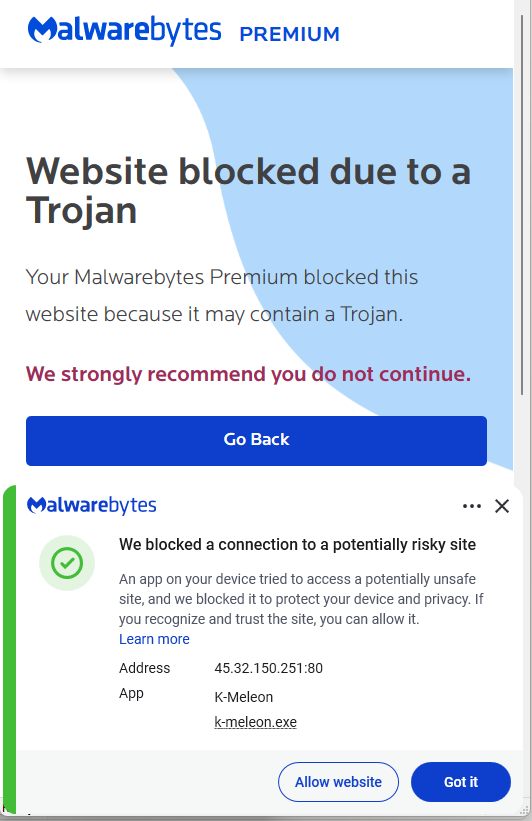
Cloudflare services — particularly Workers and Tunnels — are being abused by threat actors to host convincing AiTM phishing pages and to stage covert connections that deliver malware, including Xeno RAT and XWorm RAT. These attacks leverage trusted Cloudflare domains and free tiers (e.g., *.workers[.]dev, *.trycloudflare[.]com, *.pages[.]dev, *.r2[.]dev) to bypass email and network defenses and evade detection. #XenoRAT #XWormRAT
Category: Threat Research
Cofense PDC uncovered a phishing campaign targeting Xiaomi users that uses convincing emails impersonating Xiaomi HR/IT to direct victims to a counterfeit Mi Account login page. When victims enter credentials on the fake page hosted at amolikhousing.co[.]in (observed infection URL and IP 43.225.54.162), those credentials are captured and may provide attackers unauthorized access. #Xiaomi #Cofense
EclecticIQ TIP Bundles are time-limited, no-cost integrations that let SOC and CTI teams trial vendor services in their real workflows to validate signal quality, enrichment usefulness, and operational impact before committing commercially. The lineup includes integrations such as Bitdefender Sandbox Analyzer, ReversingLabs Spectra, VMRay, EUVD vulnerability intelligence, Modat Magnify Device DNA, TruePattern, and IntelFinder for takedowns. #EclecticIQ #Bitdefender
GlassWorm infiltrates developer ecosystems by distributing malicious or compromised npm/PyPI/VS Code packages that run hidden preinstall scripts to fingerprint systems and retrieve secondary payload locations from the Solana blockchain. After initial execution it deploys an infostealer, a Ledger/Trezor phishing binary, and a Node.js RAT that gains persistence, force‑installs a fake Chrome…
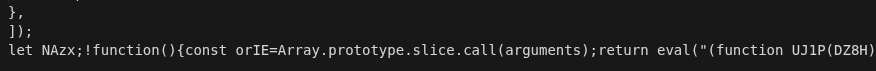
A large-scale Magecart campaign operated for over 24 months using a resilient infrastructure of 100+ domains to deliver multi-stage JavaScript loaders that dynamically fetched skimmers and exfiltrated card data via WebSocket. The attackers used high-fidelity payment page mimicry (notably Redsys) and checkout hijacking to embed fraud into legitimate transaction flows, shifting…
Pawn Storm (APT28) deployed a modular malware suite called PRISMEX to target the Ukrainian defense supply chain and allied logistics, combining steganography, COM hijacking, and abuse of legitimate cloud services for resilient fileless execution and C2. The campaign weaponized newly disclosed vulnerabilities (CVE-2026-21509 and CVE-2026-21513), used spear-phishing lures tied to hydrometeorological…

The Trivy supply chain was weaponized on March 19, 2026 when the actor identifying as TeamPCP used previously compromised credentials to inject credential‑stealing malware into official Trivy releases and related GitHub Actions, poisoning CI/CD pipelines and developer environments. Microsoft observed the attack exfiltrating harvested secrets to a typosquatted domain (scan.aquasecurtiy[.]org) and urges immediate remediation steps including pinning actions to immutable SHAs and updating to verified safe versions. #TeamPCP #Trivy

The leaked source code reveals VoidLink as a multigenerational, hybrid LKM–eBPF Linux rootkit developed with AI-assisted workflows that provides ICMP-based covert C2, delayed initialization, anti-debugging, module masquerading, and memfd-aware boot persistence. The analysis documents eBPF Netlink-buffer “swallowing” to hide ss entries, multiple kernel-targeted hooking strategies across CentOS 7 to kernel 5/6, and operational artifacts tied to Alibaba Cloud infrastructure. #VoidLink #AlibabaCloud
.png)
A high-interaction honeypot emulating an unpatched Oracle WebLogic Server (v14.1.1.0.0) recorded immediate and widespread exploitation attempts against the newly disclosed unauthenticated RCE CVE-2026-21962, plus continued scans targeting older critical WebLogic RCEs over a 12-day period (Jan 22–Feb 3, 2026). Attackers quickly weaponized the public exploit and used rented VPS (e.g., DigitalOcean, HOSTGLOBAL.PLUS), automated scanners (libredtail-http, Nmap NSE) and common techniques like path traversal and Java deserialization to gain RCE, underscoring urgent patching and layered defenses. #CVE-2026-21962 #OracleWebLogic

On March 24, 2026, legitimate LiteLLM PyPI releases 1.82.7 and 1.82.8 were compromised and distributed malicious payloads that collected credentials, installed persistence, and exfiltrated data. Datadog links the LiteLLM incident to a five-day TeamPCP supply-chain campaign that began with the Trivy compromise and spread through npm, Checkmarx, and other ecosystems; treat any host or CI that installed these versions as a full-credential exposure. #LiteLLM #TeamPCP
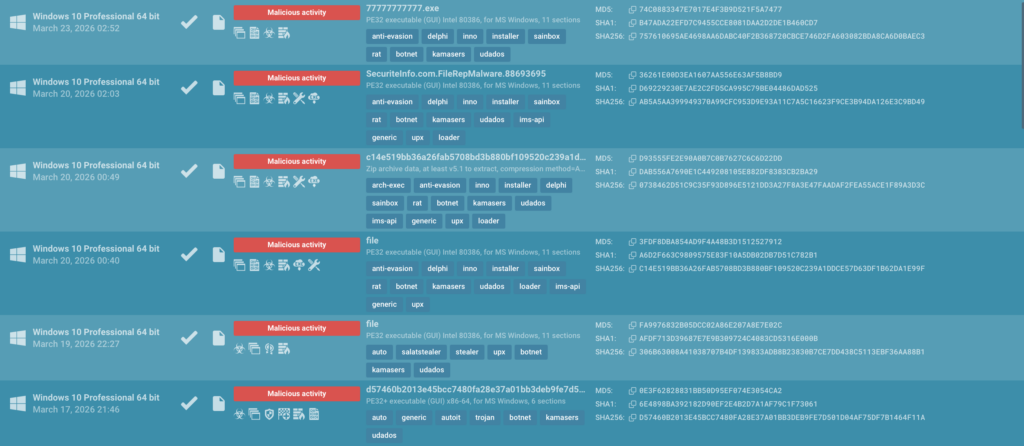
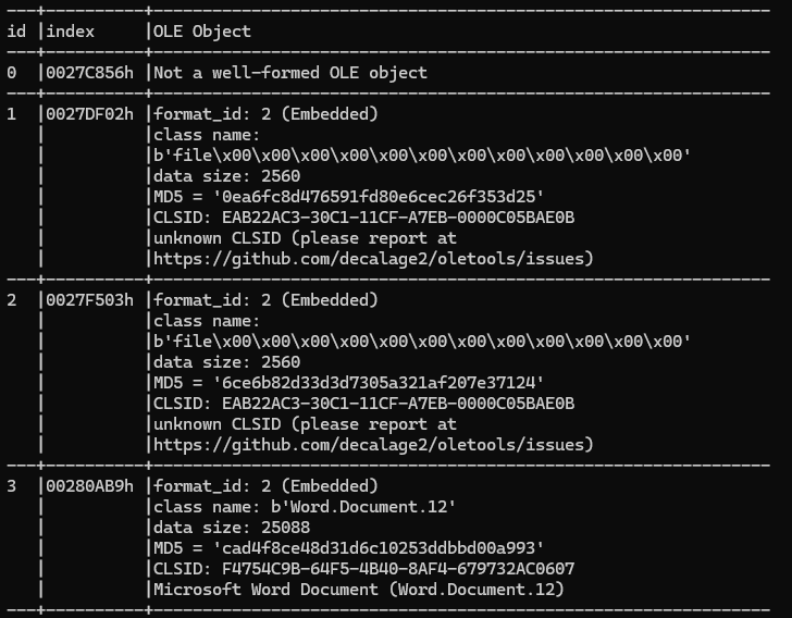
The report analyzes the Kamasers botnet, describing its multi-vector DDoS capabilities, resilient Dead Drop Resolver C2 mechanism using public services, and loader functionality that enables follow-on payloads. It highlights infrastructure ties (notably Railnet-linked ASN), targeted sectors, and actionable IOCs to support detection and response. #Kamasers #Railnet…

TeamPCP compromised Aqua Security’s trivy-action and injected a credential-stealing payload that harvested CI runner memory, queried cloud instance metadata, enumerated webhook URLs, and exfiltrated encrypted secrets to typosquat domains. The identical stealer appeared days later in Checkmarx’s ast-github-action (v2.3.28), indicating stolen credentials from the Trivy compromise were used to poison additional GitHub Actions; #TeamPCP #Trivy

Insikt Group tracked five ClickFix clusters that use fraudulent human‑verification lures to trick victims into copying and executing obfuscated commands in native tools like the Windows Run dialog and macOS Terminal. These campaigns leverage living‑off‑the‑land binaries and in‑memory execution to stage payloads such as NetSupport RAT and MacSync while operating via disposable, often Cloudflare‑protected infrastructure to maintain continuity. #ClickFix #NetSupportRAT

Dead Infrastructure Hijacking (DIH) is the exploitation of residual trust relationships left when services, domains, or cloud storage are decommissioned, allowing an attacker who reclaims those endpoints to inherit trust and receive sensitive traffic without exploiting vulnerabilities. The report details three confirmed variants—SaaS CNAME subdomain takeover, expired domain registration, and cloud bucket squatting—corrects misconceptions about CAA and DNSSEC, and recommends organizational and technical mitigations including AWS Account Regional Namespaces and CT/historical DNS auditing. #AWSAccountRegionalNamespaces #CloudBucketSquatting
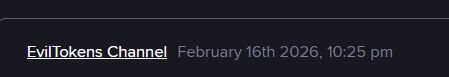
Huntress linked a large-scale Microsoft 365 device-code phishing campaign to the EvilTokens Phishing-as-a-Service ecosystem and Railway.com PaaS infrastructure, which provided token-harvesting backends and scalable phishing tooling. The campaign used multi-hop redirect chains and trusted third-party services (including Cloudflare workers and email-security URL rewriters) to evade filters, prompting Huntress to block Railway IP ranges and push Conditional Access mitigations. #EvilTokens #Railway