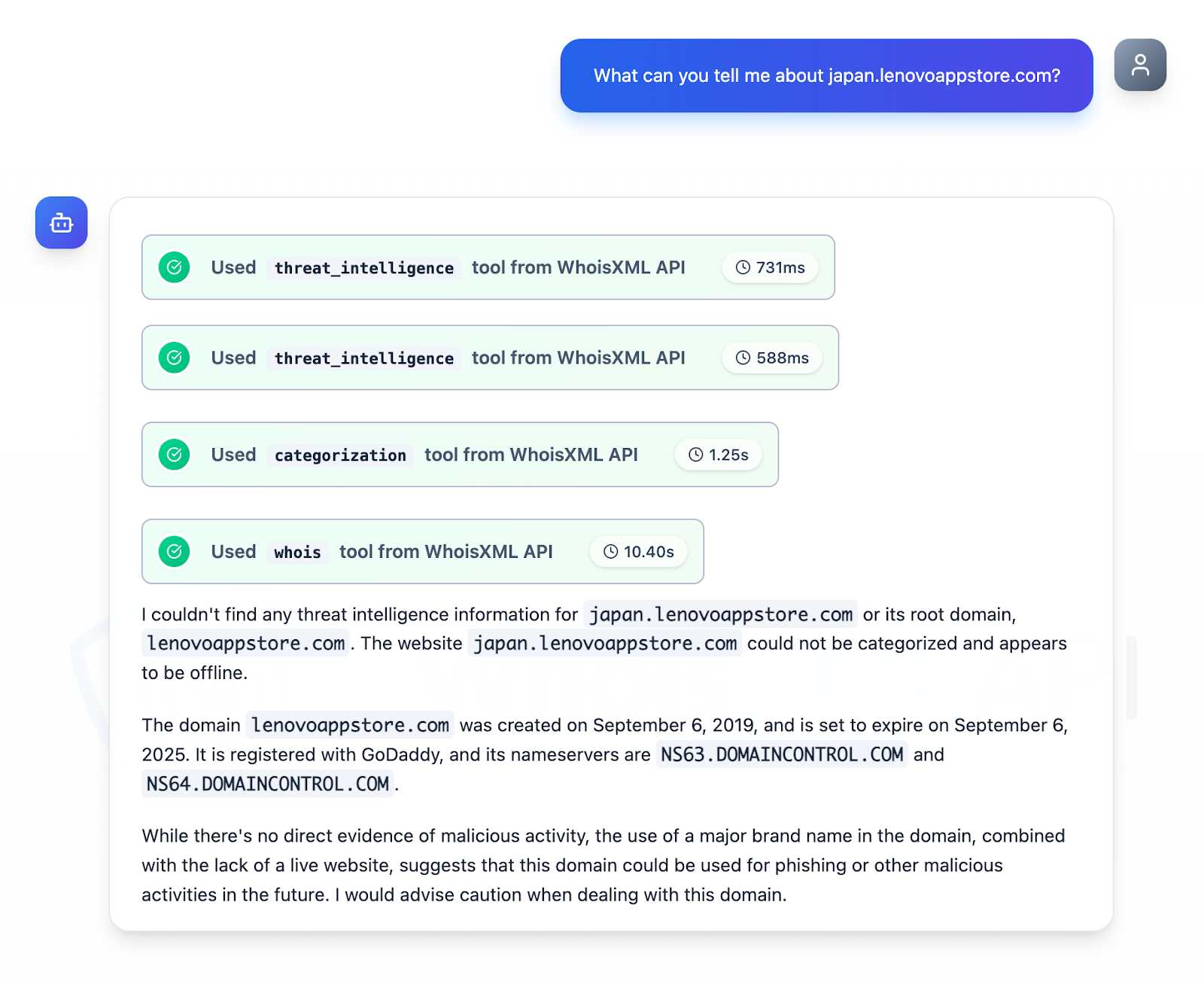
Securelist uncovered a new HoneyMyte campaign that uses an updated CoolClient backdoor to deploy browser login stealers and multiple data-theft and reconnaissance scripts. Researchers refined the initial CoolClient network IoCs to six verified indicators (three domains, two subdomains, one IP) and identified additional related artifacts including 57 email-connected domains and two IPs linked to malicious activity. #HoneyMyte #CoolClient
Category: Threat Research
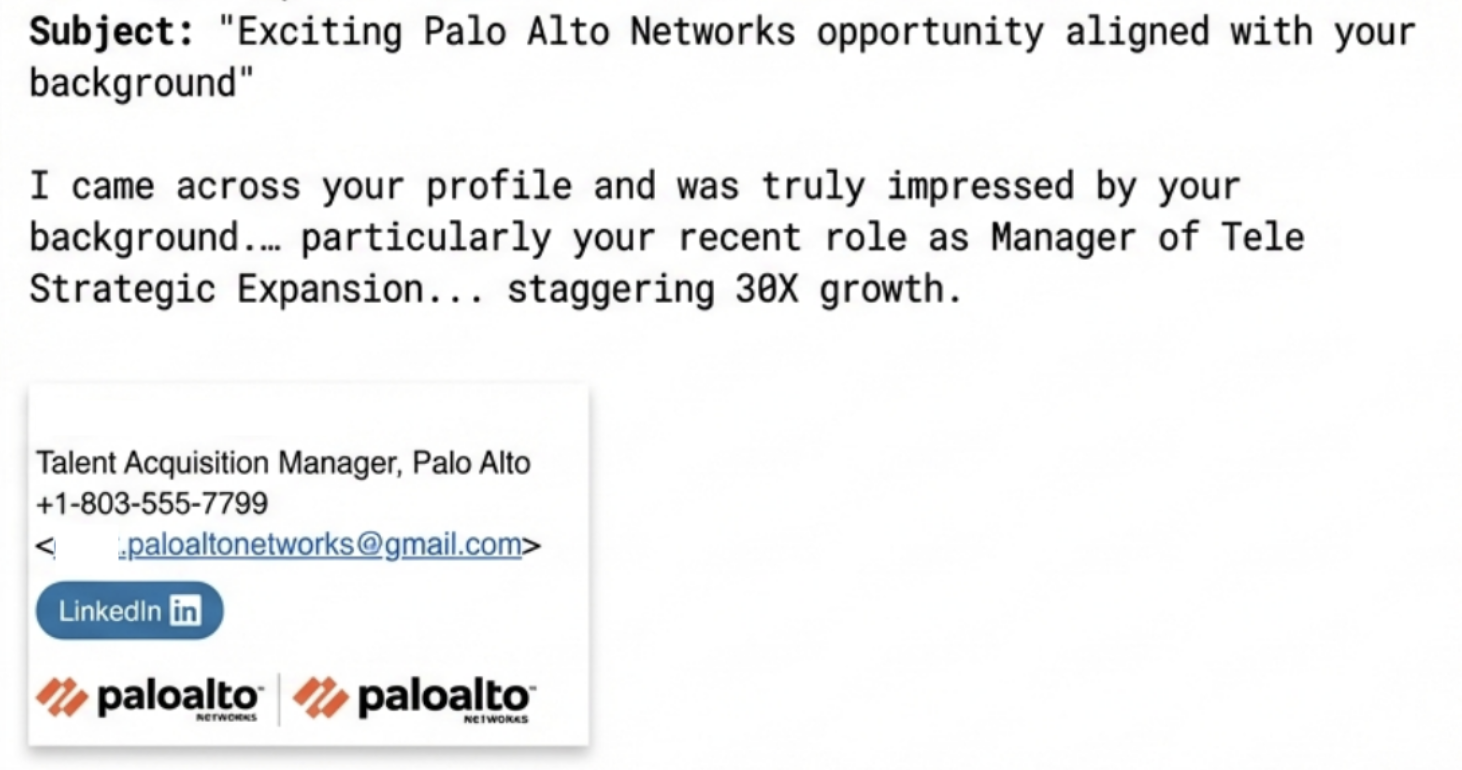
Since August 2025, Unit 42 has tracked spear-phishing campaigns that impersonate Palo Alto Networks talent acquisition staff to target senior professionals using scraped LinkedIn data and highly personalized lures. The attackers manufacture a faux ATS compliance barrier to pressure candidates into paying for resume “alignment” services; Palo Alto Networks and Unit…
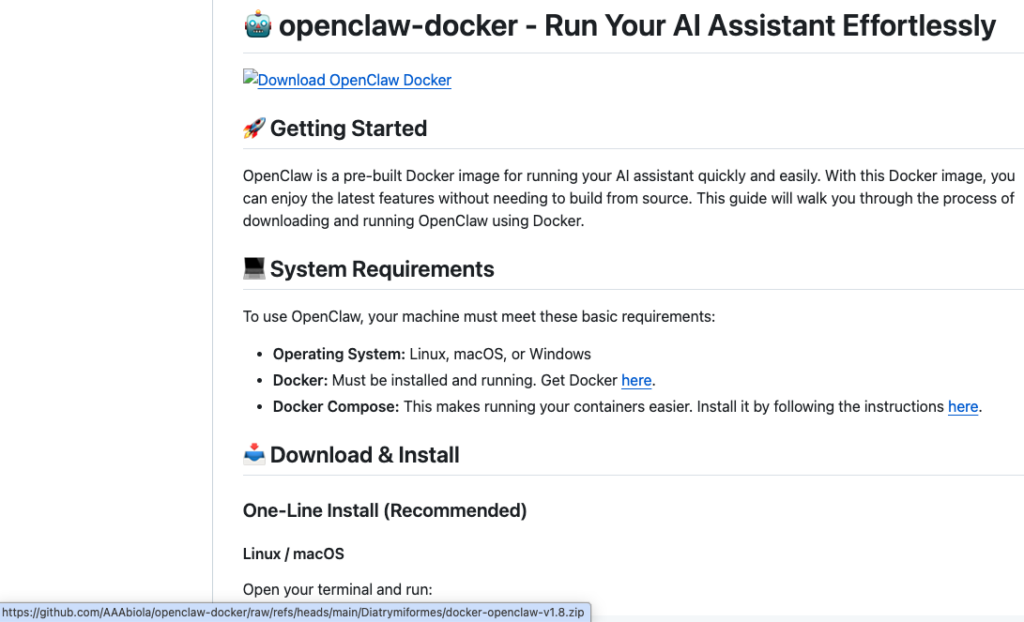
Netskope Threat Labs discovered a coordinated malware campaign—tracked as TroyDen’s Lure Factory—using trojanized GitHub repositories (300+ delivery packages) that deliver a two‑component LuaJIT loader and encrypted script designed to evade automated analysis and exfiltrate full desktop screenshots and likely credentials. The same toolchain and identical binaries appear across lures targeting developers, gamers, phone‑tracker users, and more, with C2 infrastructure in Frankfurt and delivery patterns consistent with AI‑assisted lure generation. #TroyDen #OpenClaw

This investigation details a multi-stage, reusable malware delivery framework that used obfuscated VBS launchers, a fileless PowerShell loader, PNG-embedded .NET loaders (PhantomVAI), and openly hosted directories to stage and deliver multiple payload families. The campaign delivered and rotated payloads including Remcos RAT and XWorm variants from attacker-controlled infrastructure such as news4me[.]xyz and Cloudflare-backed hosts, enabling additional infection paths via a weaponized “PDF” and batch scripts #PhantomVAI #RemcosRAT
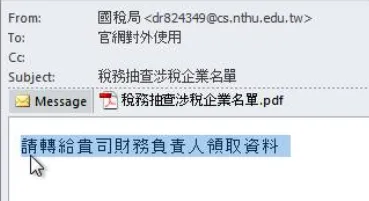
Since early 2025, China-based intrusion set Silver Fox has combined APT-style operations (using modular backdoors like ValleyRAT and HoldingHands) with opportunistic financially motivated campaigns across South Asia. The group evolved delivery from malicious PDFs and DLL side-loading to abusing a misconfigured Chinese RMM tool and a compiled Python stealer that exfiltrates data to xqwmwru[.]top. #SilverFox #ValleyRAT

The Ghost campaign abused malicious npm packages that display realistic fake npm install logs to phish for sudo passwords and then download and execute a final-stage RAT that steals crypto wallets and sensitive data. ReversingLabs discovered multiple malicious packages (published by user “mikilanjillo”) that retrieve decryption keys and payload URLs from a Telegram channel or a teletype.in web3 post and execute the RAT using the phished sudo credentials. #GhostCampaign #ReversingLabs

Elastic Workflows brings automation into Kibana to handle repetitive alert triage by running YAML-defined workflows that enrich alerts, query Elasticsearch, consult threat intel (e.g., VirusTotal), create cases, and notify responders. The article demonstrates a step-by-step alert triage playbook that includes ES|QL queries, connector-backed actions, conditional branching, and AI steps (classify, summarize, agent) to scale investigations and persist reasoning trails. #ElasticWorkflows #VirusTotal
FriendlyDealer is a large-scale social-engineering campaign that uses a reusable web kit to create fake Google Play and Apple App Store pages (deployed across 1,500+ domains) which trick users into installing Progressive Web Apps that redirect them to gambling offers via affiliate links. The operation phones home to ihavefriendseverywhere[.]xyz for telemetry…

CrowdStrike announced that Falcon Next-Gen SIEM will support third-party EDR solutions beginning with Microsoft Defender, allowing organizations to modernize their SOC without installing a Falcon sensor. The release adds Falcon Onum for real-time data control, federated search across LogScale/ExtraHop/S3, third-party indicator management, and a Query Translation Agent to accelerate migrations and…
M-Trends 2026 reports a bifurcation in adversary behavior: cybercriminals optimized for rapid, high-impact operations and recovery denial while espionage groups and insiders prioritized extreme persistence by targeting unmonitored edge devices and native network functions. The report highlights rising median dwell time, the collapse of hand-off windows to seconds, the surge in voice phishing and SaaS token theft, and recommends defenders prioritize identity controls, extended log retention, and behavior-based detection. #BRICKSTORM #UNC3944

Elastic Security XDR centralizes endpoint-native protection, unified telemetry, and AI-driven investigative workflows so analysts can detect, pivot, and respond across endpoints, workloads, identities, and cloud services. The platform combines Elastic Defend endpoint prevention, Osquery-enabled forensics, Device Control, and Elastic Workflows to automate containment and evidence collection for faster incident resolution; #ElasticSecurityXDR #ElasticDefend
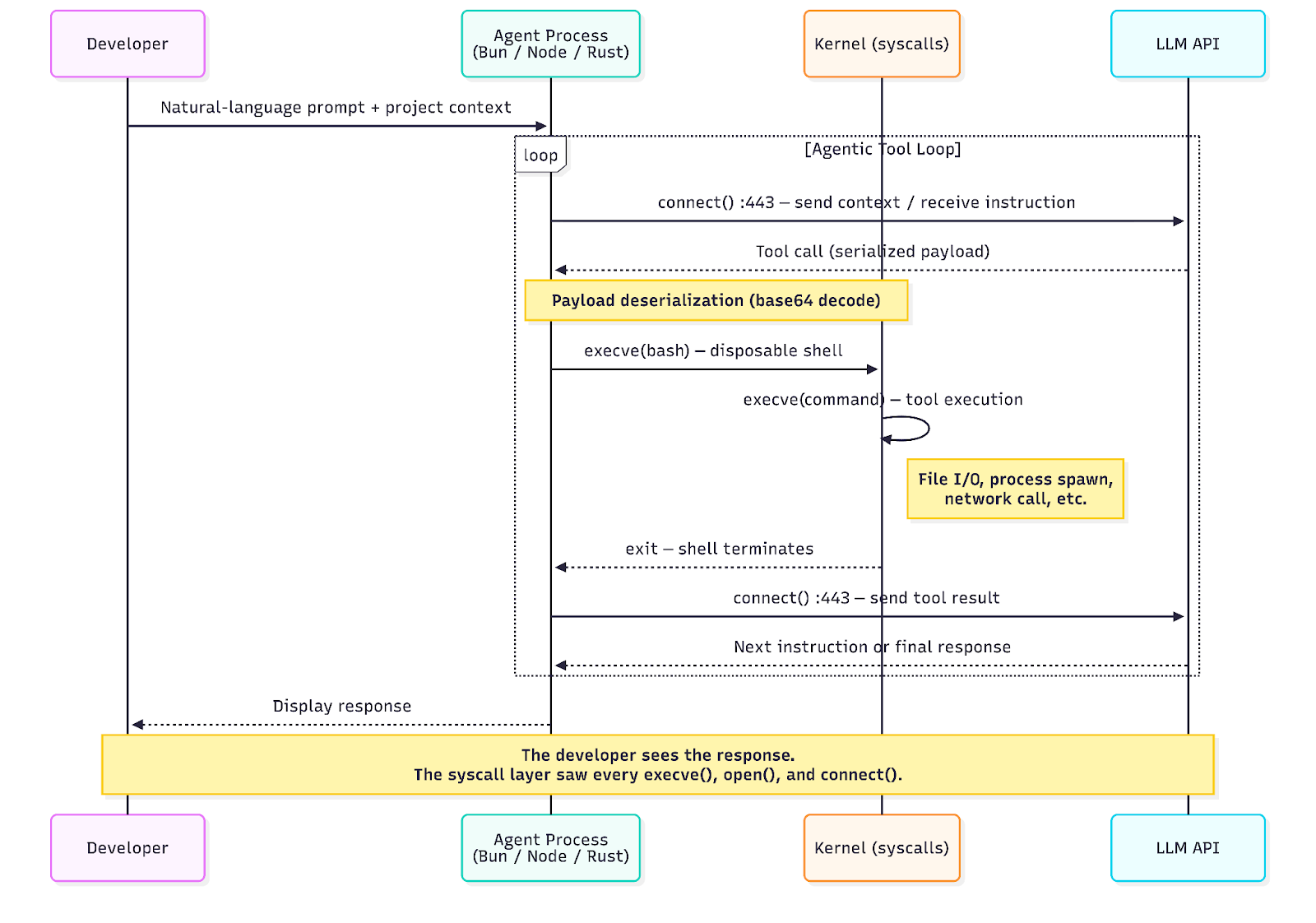
Sysdig TRT instrumented Claude, Gemini, and Codex at the syscall level and built Falco rules to detect agent activity by observing installation events, unauthorized config access, sensitive file reads, and safety-control bypasses. Their approach maps observable agent behaviors to MITRE ATLAS/ATT&CK and flags threats such as prompt injection, credential theft (SesameOp), and MCP supply‑chain risks. #Claude #Gemini #Codex #SesameOp #Cursor #SlackAI #MCP #CVE-2025-53109 #CVE-2025-53110

AhnLab ASEC reports that the Larva-26002 actor continues to target internet‑exposed, improperly managed MS‑SQL servers and uses the BCP utility or downloaders to create and deploy scanner malware. The latest campaign installs a Go‑based scanner called ICE Cloud Client that authenticates with a C2, receives MSSQL scanning targets and credentials, and…
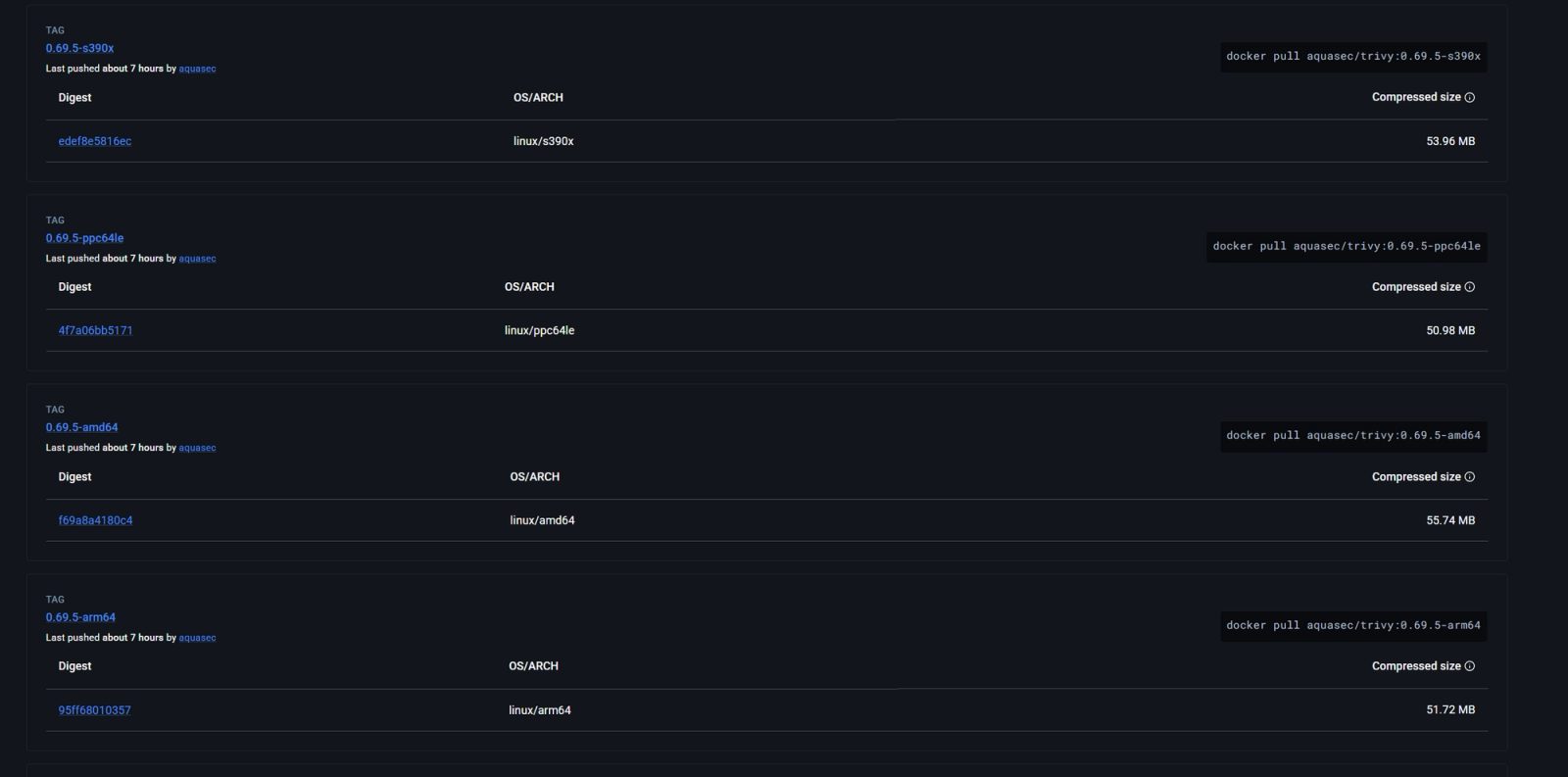
Socket’s threat research team discovered additional compromised Trivy Docker images (tags 0.69.5 and 0.69.6) pushed without corresponding GitHub releases, both containing indicators tied to the TeamPCP infostealer. The incident also exposed Aqua Security GitHub resources and prompted recommendations to avoid affected Trivy versions and treat recent executions as potentially compromised. #TeamPCP #Trivy
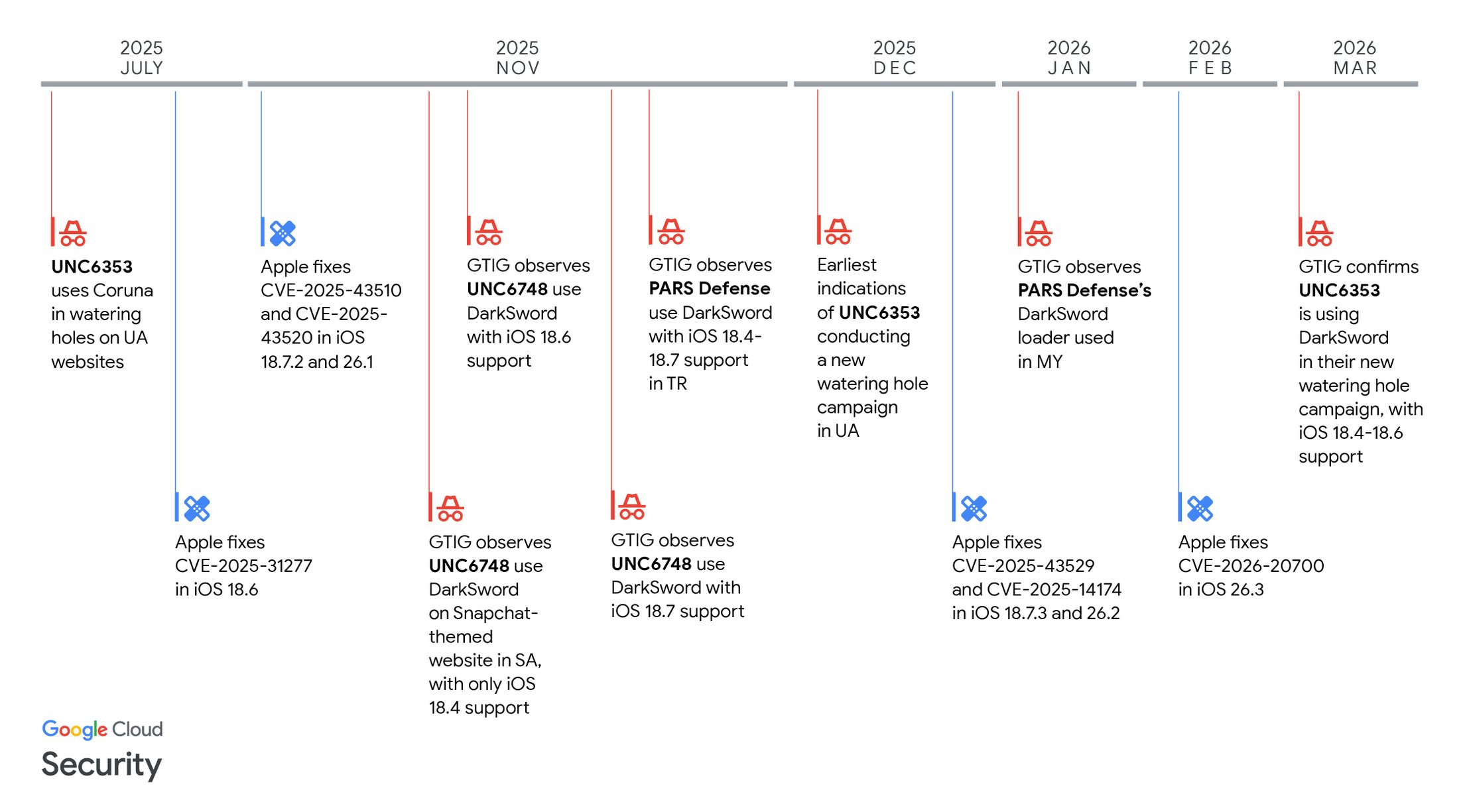
Google Threat Intelligence Group (GTIG) disclosed DarkSword, a JavaScript-based iOS full‑chain exploit that chained six vulnerabilities (including multiple zero‑days) to achieve kernel privileges and deliver post‑exploitation payloads GHOSTBLADE, GHOSTKNIFE, and GHOSTSABER against targets in Saudi Arabia, Turkey, Malaysia, and Ukraine. GTIG attributes use of DarkSword to multiple commercial surveillance vendors and suspected state actors (including UNC6353, UNC6748, and PARS Defense), published mitigation guidance, and added delivery domains to Safe Browsing. #DarkSword #GHOSTBLADE