Cyble CRIL tracked 1,641 vulnerabilities between March 4–10, 2026, with 175 having public PoC exploits and 200 rated critical under CVSS v3.1; CISA added multiple legacy and actively exploited flaws to its KEV catalog. High-impact issues include authentication bypasses and remote code execution in Juniper Junos, Cisco SD‑WAN, pac4j‑jwt, Qwik, IDC SFX, and several EV charging platforms, disproportionately impacting Energy and Transportation sectors. #JuniperJunos #CiscoSDWAN
Category: Threat Research
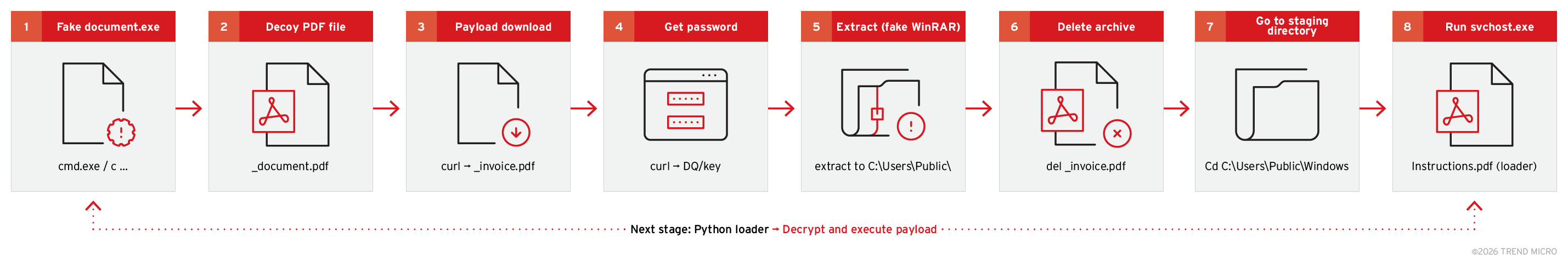
Attackers are using malicious Google Forms linking to business-themed ZIP files (job interviews, project briefs, financial documents) to distribute a multi-stage infection chain that ultimately installs the PureHVNC .NET RAT. The campaign employs DLL hijacking, obfuscated Python/Donut shellcode, scheduled tasks and process injection (into SearchUI.exe) while using services like Dropbox and…

Socket’s Threat Research Team uncovered a worm-enabled npm supply chain attack that compromised legitimate publisher namespaces including @emilgroup and @teale.io, replacing package contents with a Python implant that polls an ICP canister for rotatable second-stage payloads. The campaign, dubbed CanisterWorm, uses postinstall hooks, a systemd –user persistent service named pgmon, and a deploy.js republishing worm that leverages npm publishing tokens (often published with –tag latest) to propagate. #CanisterWorm #EmilGroup

CYFIRMA identified an ongoing phishing campaign using invoice- and payment-themed emails with malicious PDF attachments and QR codes that redirect finance and procurement staff to credential-harvesting sites. The campaign employs multi-stage document-based delivery, reusable phishing templates, and rotating backend infrastructure to evade detection and sustain credential theft. #CYFIRMA #Quishing
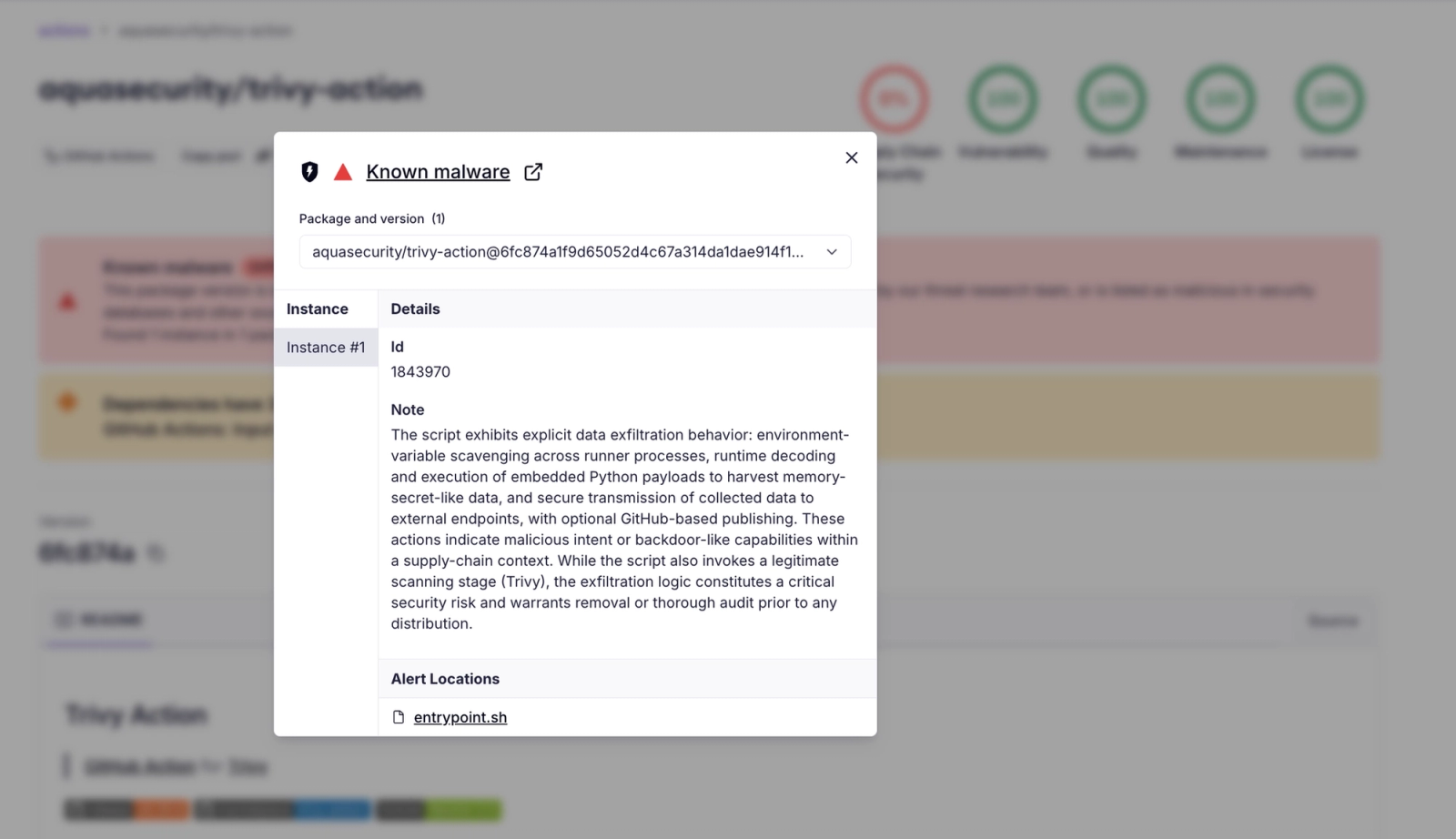
A supply chain attack compromised the aquasecurity/trivy-action GitHub Action by force-updating 75 version tags to point to malicious commits that replaced the action entrypoint with an infostealer, putting over 10,000 workflows at risk. The payload collects secrets (including SSH keys, cloud credentials, and runner memory dumps), encrypts them, and exfiltrates to a typosquatted domain or to victim-created GitHub repositories; attribution points to TeamPCP. #TeamPCP #trivy-action

CVE-2026-33017 is an unauthenticated remote code execution flaw in Langflow’s public flow build endpoint that attackers weaponized within ~20 hours of disclosure to execute arbitrary Python and exfiltrate credentials. Sysdig’s honeypots recorded rapid, multi-stage exploitation—nuclei-based scanning, custom Python exploit scripts, and staged dropper/C2 infrastructure—that harvested environment variables, .env files, and database artifacts. #Langflow #CVE-2026-33017

Between November 2025 and February 2026, targeted spear-phishing campaigns delivered a VBS downloader and PowerShell droppers that ultimately installed the AsyncRAT backdoor on Libyan organizations including an oil refinery, a telecoms provider and a state institution. The campaign used Libya-themed lure filenames and a KrakenFiles-hosted downloader to persist via a scheduled task named ‘devil’, suggesting focused targeting that could be state sponsored. #AsyncRAT #LibyanOilRefinery
AhnLab ASEC attributes a 2026 campaign against publicly exposed, improperly managed MS-SQL servers to the Larva-26002 threat actor, which gains access via brute-force/dictionary attacks, abuses the MS-SQL BCP utility to write a downloader, and deploys a Go-based scanner called ICE Cloud Client. The actor has previously distributed Trigona and Mimic ransomware…
A targeted, multi‑stage campaign delivers PureLog Stealer using localized phishing lures and an evasive, encrypted delivery chain that extracts and executes payloads entirely in memory. The attack employs fileless techniques including a Python loader, dual .NET loaders, AMSI bypass, remote key retrieval, and C2 exfiltration, impacting organizations running Windows in healthcare,…
Keitaro Tracker is being widely abused by threat actors to perform domain cloaking, conditional traffic routing, and large-scale investment and tech-support scams, often leveraging AI-generated content and deepfakes to increase credibility and scale. Collaborative research by Infoblox and Confiant found thousands of malicious Keitaro instances, extensive domain registration patterns (RDGAs), and active abuse by actors including TA2726. #Keitaro #TA2726
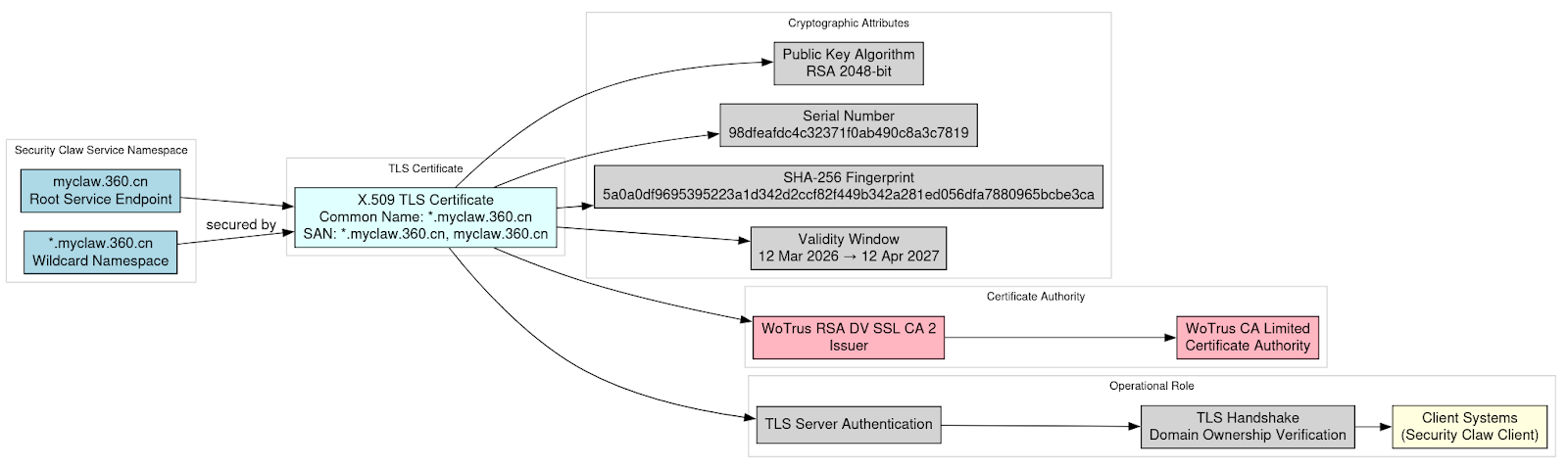
Cryptographic analysis confirms a legitimate RSA private key matching the wildcard TLS certificate for *.myclaw[.]360[.]cn was exposed in distributed installer material, enabling potential namespace-wide impersonation and interception if used in production. The certificate (issued by WoTrus RSA DV SSL CA 2) appears to have been rotated on 16 March 2026 after discovery, and the namespace is attributed to Qihoo 360. #SecurityClaw #Qihoo360

LevelBlue documents a multi-stage, fileless ClickFix campaign that compromises legitimate websites to present fake CAPTCHA prompts which coerce users into executing clipboard-pasted PowerShell commands, enabling in-memory payload delivery via Donut shellcode. The infrastructure is payload-agnostic and rotates multiple commodity stealers and a cryptocurrency clipboard hijacker across numerous C2 servers and fake crypto-exchange sites. #ClickFix #LummaStealer

Symantec and Carbon Black researchers uncovered Infostealer.Speagle, a stealthy .NET infostealer that hijacks the functionality and infrastructure of the legitimate Cobra DocGuard client and uses compromised Cobra DocGuard servers to exfiltrate stolen data while appearing as legitimate client-server traffic. Speagle targets systems with Cobra DocGuard installed, performs staged collection (system info, WMI, file and user data, browser artifacts, and targeted searches for Chinese ballistic missile–related documents), encrypts and hexlifies the data, transmits it over HTTP to a hijacked server, and then attempts to self-delete. #Infostealer.Speagle #CobraDocGuard

This article walks through a simulated container attack chain based on the TeamPCP cloud-native cryptojacking and ransomware operation, showing how Defend for Containers (D4C) telemetry surfaces each stage from initial execution through persistence, lateral movement, tunneling, and miner deployment. By mapping observable runtime behavior to detection logic and correlating D4C runtime events with Kubernetes audit logs, the analysis demonstrates how to detect complex, multi-stage compromises across containers and the control plane. #TeamPCP #Kubernetes

Unit 42 analyzed two malware samples that integrate large language models: a ConfuserEx‑packed .NET infostealer that calls OpenAI GPT‑3.5‑Turbo for logging and superficial evasion/obfuscation suggestions, and a dropper that queries GPT‑4 to gate execution before deploying a Sliver payload. Both samples show experimental AI use—LLM outputs are largely unimplemented or used…
