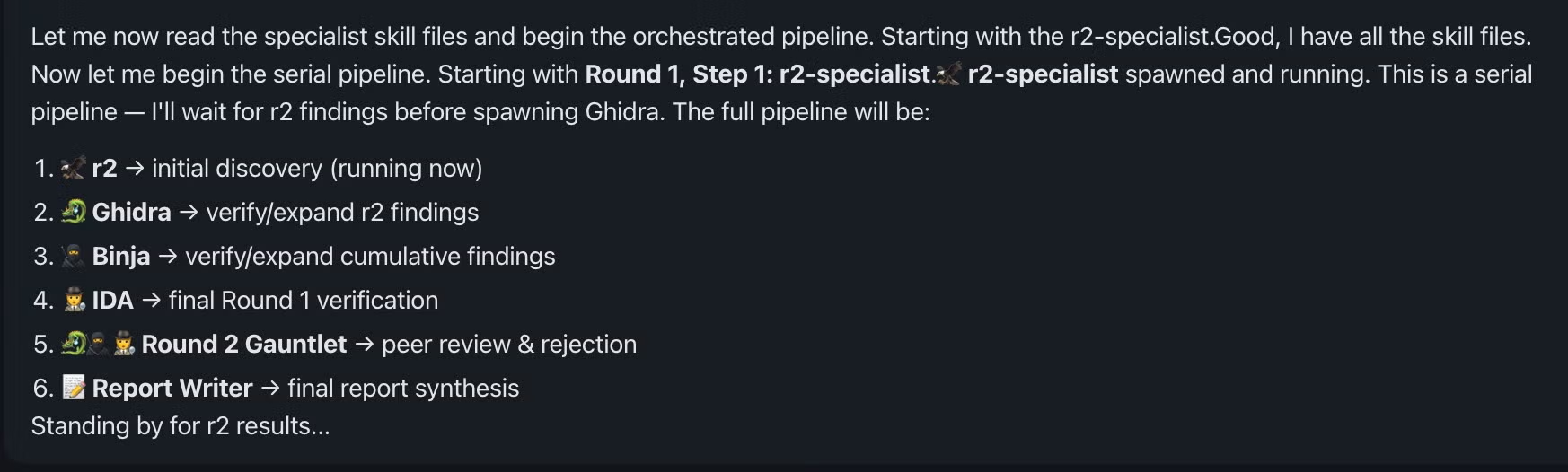
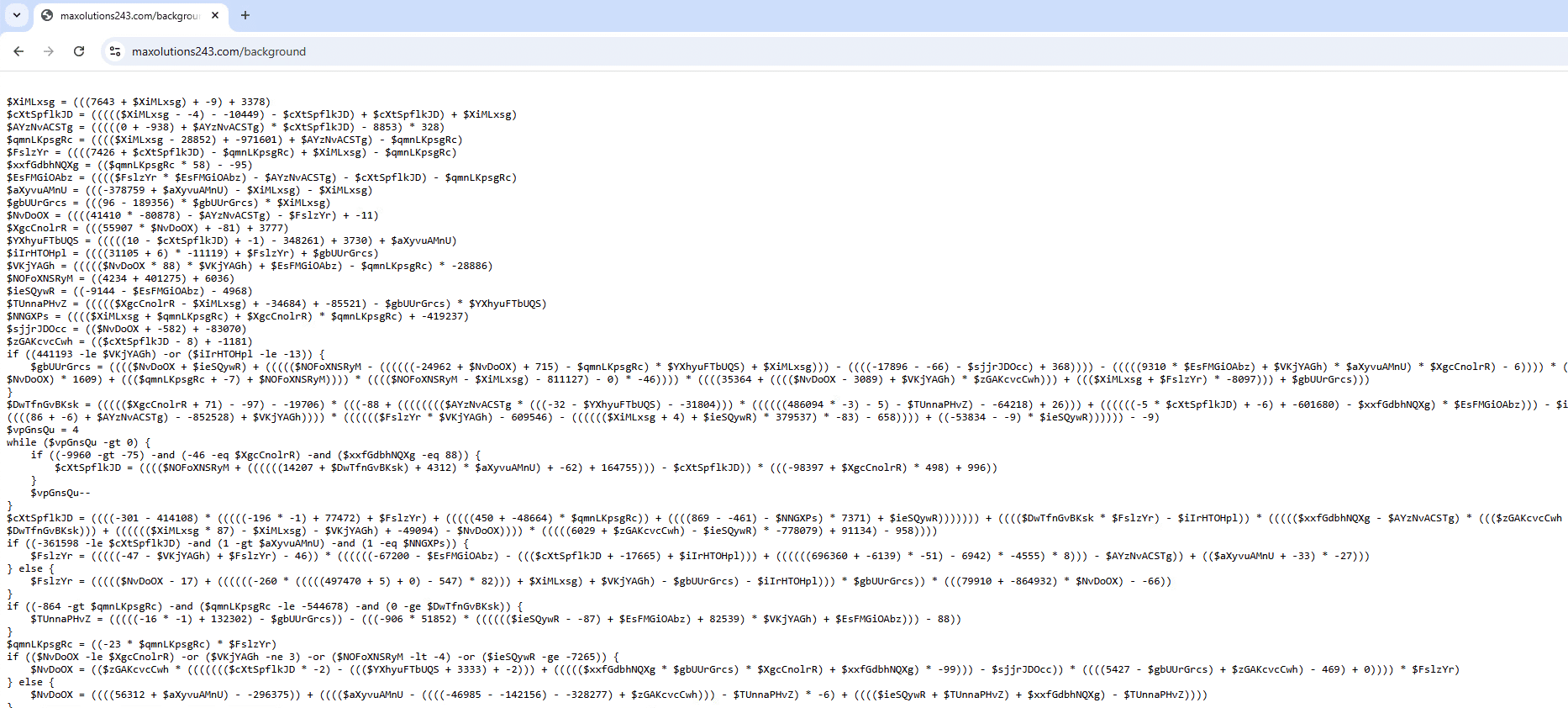
The article describes a serial, multi-agent pipeline that treats each reverse-engineering tool (radare2, Ghidra, Binary Ninja, IDA Pro) as an independent, skeptical analyst to cross-validate findings and reject decompiler artifacts and parsing errors before report synthesis. It also explains why deterministic bridge scripts were chosen over the Model Context Protocol to reduce latency, non-determinism, and token costs, and documents token economics, tiered model allocation, and operational lessons from early runs. #WizardUpdate #SysJoker
Category: Threat Research
Lookout Threat Labs uncovered DarkSword, a complete iOS exploit chain and JavaScript-based infostealer deployed via watering‑hole attacks that targeted Ukrainian websites to rapidly collect and exfiltrate credentials, crypto‑wallet data, and other sensitive device content on iOS 18.4–18.6.2 devices. The campaign is attributed to a likely Russian-linked actor identified as UNC6353 and uses compromised domains and a hardcoded C2 (sqwas.shapelie[.]com) to receive stolen data before removing traces. #DarkSword #UNC6353
.png)
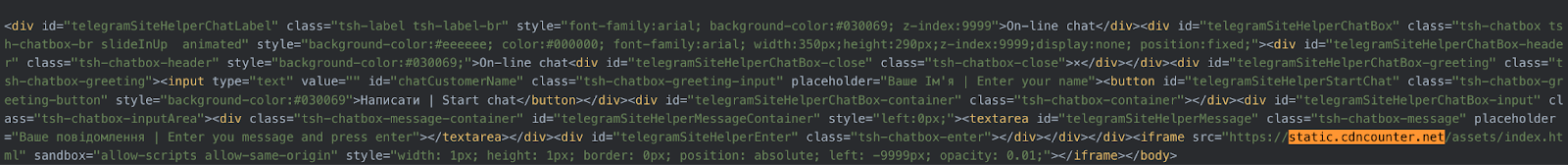
CloudSEK researchers uncovered a multi-stage macOS campaign that uses SEO poisoning and ClickFix-style social engineering to trick users into running a malicious Terminal command which installs a staged loader and an AppleScript information stealer. The malware harvests browser credentials, cryptocurrency wallets, SSH keys, cloud configs and files, exfiltrates data via chunked HTTP PUT to attacker infrastructure, and can modify Ledger Live to enable transaction manipulation and persistence. #MacSyncStealer #LedgerLive

Threat actors used SEO poisoning to place fake KakaoTalk download pages at the top of search results and distributed a malicious installer that infected over 5,000 PCs. The installer uses an invalid NetEase signature, decrypts and drops components (Verifier.exe, AutoRecoverDat.dll, GPUCache.xml/GPUCache2.xml) to establish persistence, add Windows Defender exclusions, and connect to…

Defend for Containers (Elastic Stack 9.3.0) is a runtime security integration that captures container process and file telemetry, enriches events with container and orchestration context, and provides a policy-driven model (selectors and responses) for detection and response in Kubernetes environments. The integration ships pre-built detection rules, supports Elastic Agent deployment on clusters (EKS/GKE; limited AKS support), and emphasizes runtime behavior such as interactive execution, file modifications, capability exposure, and privilege escalation for workload-aware detections. #DefendForContainers #Kubernetes
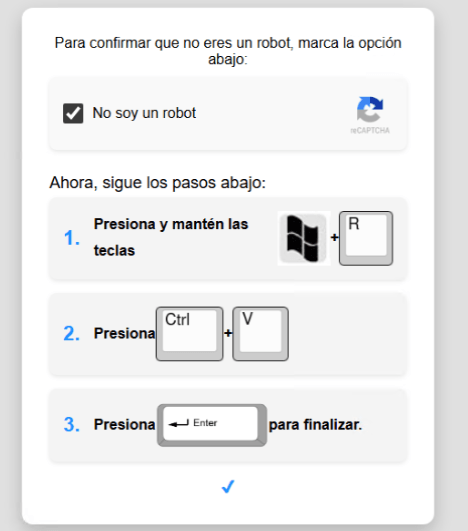
A targeted Horabot campaign used a fake CAPTCHA lure that tricked victims into running a remote HTA via mshta, which then staged multiple polymorphic VBScript loaders and downloaded AutoIt components that decrypted and loaded a Delphi banking Trojan in memory. The operation performed environment checks, credential harvesting via browser SQL queries, MAPI-based email harvesting and mass-phishing with malicious PDFs, and communicated with C2 infrastructure over HTTP and a custom encrypted socket protocol. #Horabot #Casbaneiro

In December 2025 Zscaler ThreatLabz discovered SnappyClient, a C++-based command-and-control implant delivered via HijackLoader that provides remote access, keylogging, screenshot capture, browser/extension and application data theft, and targeted cryptocurrency theft. The implant uses multiple evasion techniques (AMSI bypass, Heaven’s Gate, direct syscalls, transacted hollowing), a custom ChaCha20-Poly1305 encrypted protocol, and configurable EventsDB/SoftwareDB payloads—strongly suggesting ties between SnappyClient and HijackLoader. #SnappyClient #HijackLoader

At Fal.Con Gov 2026, CrowdStrike announced expanded GovCloud capabilities including Falcon Flex, new Charlotte AI investigator features, Falcon for XIoT, External Attack Surface Management in Falcon Exposure Management, and behavioral malware analysis to accelerate modernization and strengthen federal defenses within a FedRAMP-authorized environment. These innovations are designed to reduce procurement friction,…
Cato CTRL researchers observed a vishing-driven delivery that used Microsoft Teams helpdesk impersonation and screen sharing to coax a victim into executing staged PowerShell, which loaded an in-memory payload and established a WebSocket-based backdoor. Defenders are advised to treat collaboration tools as attack surfaces and apply controls such as ticket validation, restricting external Teams access, and PowerShell hardening. #PhantomBackdoor #MicrosoftTeams
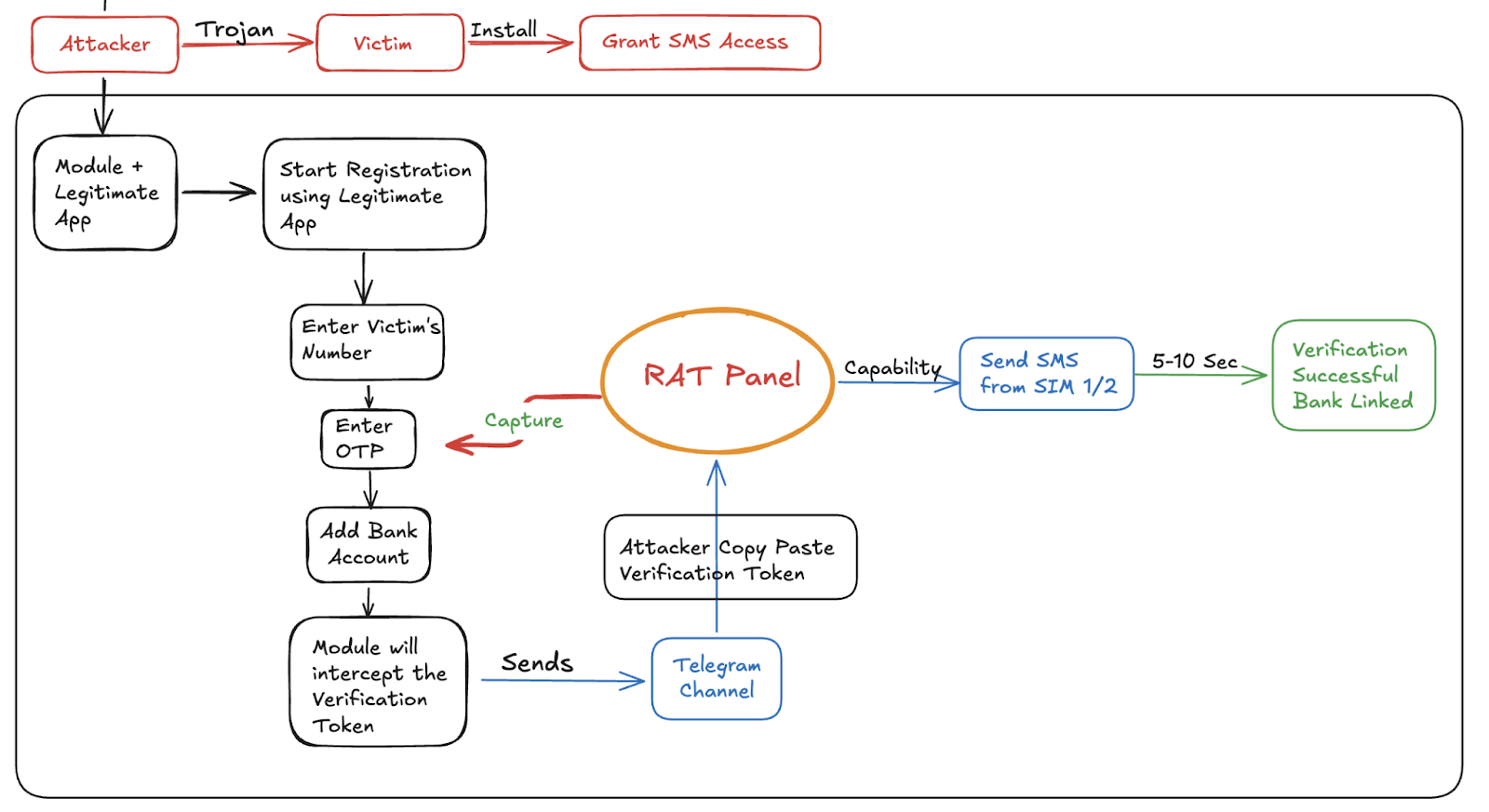
The article describes a shift from APK repacking to runtime environment manipulation using the LSPosed framework—allowing the “Digital Lutera” LSPosed module to hook system APIs, intercept and exfiltrate SMS tokens, spoof SIM identity, and inject fake SMS records while leaving payment apps’ signatures intact, bypassing Play Protect. To mitigate this, banks must enforce strong device attestation (Play Integrity API MEETS_STRONG_INTEGRITY), move critical validation to carrier-side checks, and implement runtime self-protection and native verification to detect or prevent OS-level hooking. #DigitalLutera #LSPosed #AxisBank #ProtecttAI #Berlin
More than 20,000 fraudulent online stores—many running on Sellvia WordPress templates and concentrated on 36 IP addresses—were mapped as part of an industrialized scam ecosystem that harvests payment credentials and personal data under polished storefronts and aggressive sale tactics. Researchers linked large campaigns such as FraudWear and BogusBazaar to this activity…

Cyble Research & Intelligence Labs (CRIL) describes a widespread web-based phishing campaign hosted on edgeone.app that social-engineers users into granting browser camera, microphone, contact, and location permissions to harvest photos, videos, audio, device metadata, and contacts. Collected multimedia and telemetry are exfiltrated to attacker-controlled Telegram bots, and the scripts show indicators of possible AI-assisted code generation. #EdgeOnePages #TelegramBotAPI
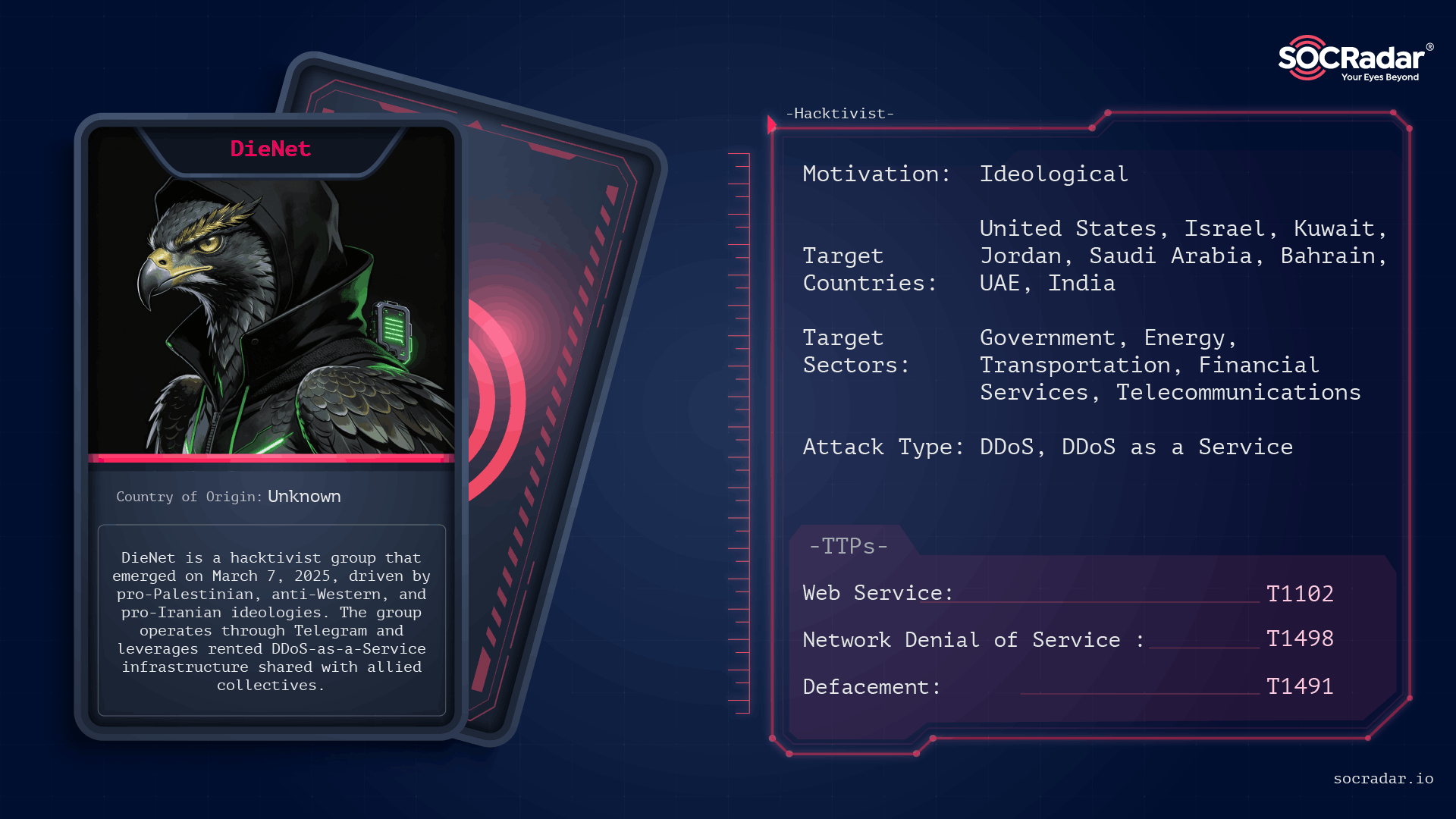
DieNet emerged in March 2025 as a fast‑growing pro‑Iranian hacktivist franchise that leverages rented DDoS‑as‑a‑Service infrastructure to claim large volumes of disruption, including 59 distinct attack claims across March 2–3, 2026, and a major share of 149 hacktivist DDoS claims against 110 organizations. The group targets governments, critical infrastructure, and high‑visibility Western firms, has made unverified claims of ransomware and OT/ICS access (Locknet, VeroPoint), and operates inside a broader “Electronic Operations Room” of aligned actors. #DieNet #Locknet

CIS CTI identified an ongoing ZPHP (SmartApeSG) campaign targeting U.S. SLTT organizations that uses fake CAPTCHAs and the ClickFix social engineering technique to deliver remote access tools, including Remcos RAT. The campaign’s kill chain leverages injected JavaScript (middleware-render.js), mshta/PowerShell execution, DLL sideloading, steganography, and persistence named “Intel PLLQ Components,” and is…

Andrew MacPherson’s LABScon 2025 talk unpacks the technical realities of crypto crime, explaining how front-end wallets, developer environments, and supply-chain weaknesses have enabled roughly $9 billion in illicit funds to be stolen. He details major attack patterns including the $1.5 billion Bybit heist, developer machine compromises and production JavaScript tampering, and discusses laundering methods like cross-chain swaps and Tornado Cash. #Bybit #TornadoCash