Cato CTRL researchers observed a vishing-driven delivery that used Microsoft Teams helpdesk impersonation and screen sharing to coax a victim into executing staged PowerShell, which loaded an in-memory payload and established a WebSocket-based backdoor. Defenders are advised to treat collaboration tools as attack surfaces and apply controls such as ticket validation, restricting external Teams access, and PowerShell hardening. #PhantomBackdoor #MicrosoftTeams
Keypoints
- Attack used vishing/helpdesk impersonation via a Microsoft Teams meeting invite and guided screen sharing to obtain user trust and execution.
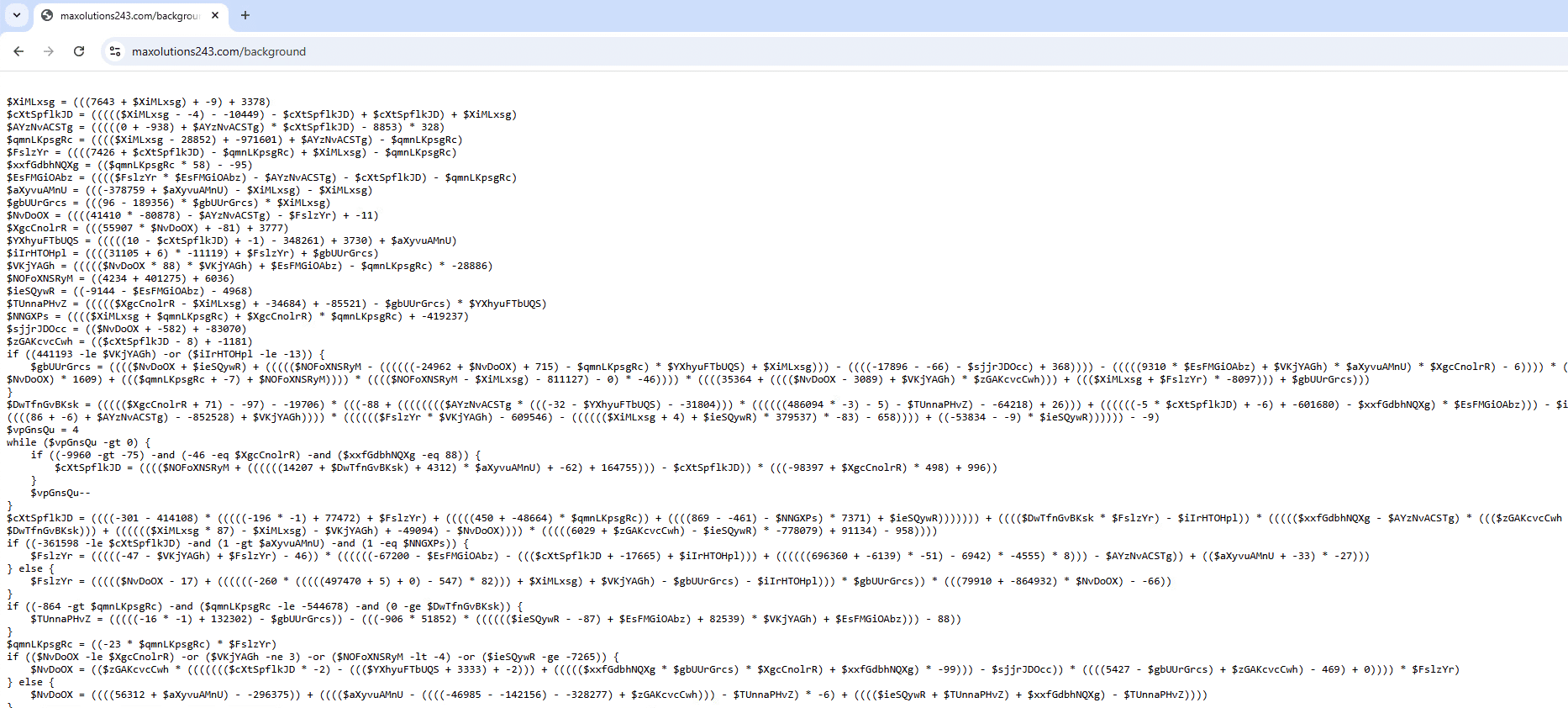
- Initial execution launched obfuscated PowerShell from hxxps://maxolutions243[.]com/background, performing in-memory, fileless staging to reduce on-disk artifacts.
- Payloads performed system reconnaissance (computer name, domain, username, PID, UUID), XOR-encrypted and Base64-encoded the data, and sent it to C2 using a hardcoded XOR key.
- Final stage established an interactive WebSocket-based C2 channel to ws://maxsolutions243[.]com:80 enabling remote access and control.
- Observed behaviors overlap with SentinelOne’s PhantomBackdoor/PhantomCaptcha reporting but used Teams-based vishing instead of traditional email spearphishing.
- Cato MDR/XOps flagged lateral movement and follow-on stages; recommended mitigations include helpdesk verification workflows, restricting external Teams features, and PowerShell monitoring/hardening.
MITRE Techniques
- [T1566.003 ] Spearphishing via Service – Initial access was achieved through a collaboration service meeting invite and interaction (‘The victim reported that the engagement occurred through Teams and began with a meeting invite.’)
- [T1204 ] User Execution – The attacker relied on the victim to execute staged PowerShell following guided screen sharing (‘During or shortly after the Teams interaction, the victim’s device executed PowerShell consistent with staged payloading.’)
- [T1059.001 ] Command and Scripting Interpreter: PowerShell – Obfuscated PowerShell was retrieved and executed to perform in-memory staging (‘A malicious request initiated a malicious PowerShell on: hxxps[://]maxolutions243[.]com/background’)
- [T1105 ] Ingress Tool Transfer – Next-stage payloads and code were downloaded from attacker-controlled domains for follow-on execution (‘The request to maxsolutions243[.]com initiated retrieval of the next-stage payload’)
- [T1055 ] Process Injection – Payloads were loaded into memory to avoid writing files to disk and reduce forensic artifacts (‘This stage initiated in-memory, fileless execution’ and ‘The next payload was loaded into memory’)
- [T1071.001 ] Application Layer Protocol: Web Protocols – WebSocket was used as the interactive command-and-control channel (‘The final stage established a WebSocket session to the threat actor-controlled endpoint, enabling interactive C2 :ws://maxsolutions243[.]com:80’)
- [T1082 ] System Information Discovery – The malware collected host identifiers and runtime context such as computer name, domain, username, PID, and UUID (‘After de-obfuscating the PowerShell, we observed system reconnaissance and collection of: Computer name, Domain information, Username, Process identification (PID), System universally unique identifier (UUID)’)
- [T1021 ] Remote Services (Lateral Movement) – Post-compromise activity included lateral movement detections as identified by Cato MDR/XOps (‘Cato MDR flagged the lateral movement and follow-on stages, and Cato XOps correlated the activity into a Story’)
Indicators of Compromise
- [Domain ] C2 and staging infrastructure – maxsolutions243[.]com, halungroup[.]com
- [IP Address ] Threat actor hosting / infrastructure – 104[.]238[.]133[.]25, 162[.]252[.]172[.]74
- [SHA256 ] Observed payload hashes – 1497ad4cd9b3f009904896464b090ad2ff4c932f2bb57752bb19b53b2ec65ea0, b0c07b265c9d9046038ffa48d5b8e17b8ba0791503beba85196cdbe0ac2fcb27