Seqrite Labs identified a targeted phishing campaign that exploited a stored XSS in Zimbra Collaboration (CVE-2025-66376) by embedding obfuscated JavaScript directly in an HTML email to steal session tokens, credentials, backup 2FA codes, mailbox contents (90 days) and other account data. The campaign exfiltrated data over both DNS and HTTPS to a hardcoded C2 (zimbrasoft[.]com[.]ua) and is attributed with medium confidence to APT28 given tradecraft and targeting overlaps. #SpyPress.ZIMBRA #APT28
Category: Threat Research

Acronis TRU identified hundreds of GitHub repositories and associated campaigns distributing Vidar Stealer 2.0 and other infostealers disguised as “free game cheats,” leveraging GitHub Pages, Pastebin, Discord and Reddit to deliver staged payloads to gamers. Vidar 2.0 — a C rewrite with polymorphic builds, multithreading, advanced obfuscation and Telegram/Steam-based C2 — enables broad credential, wallet and file theft and has surged following takedowns of Lummastealer and Rhadamanthys. #Vidar #GitHub

Ransomware actors continued to evolve in 2025, with a record number of victims posted to data leak sites, increased use of data-theft extortion, continued targeting of VPNs/firewalls via vulnerability exploitation, and a notable prevalence of REDBIKE ransomware. The ecosystem showed signs of declining profitability and operational shifts—such as increased targeting of smaller organizations, use of tunnelers and RMM abuse, and integration of AI and Web3—with #REDBIKE #CLOP
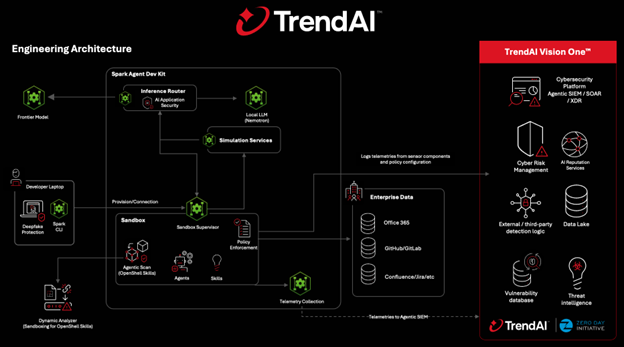
The article explains how NVIDIA OpenShell and TrendAI integrate to provide governance, runtime enforcement, and visibility for deploying autonomous agentic AI safely at enterprise scale. It outlines layered defenses—pre-execution policy distribution, Agentic Scan for skill/tool risk, dynamic behavioral analysis, inline runtime enforcement, AI-specific threat inspection, and continuous monitoring—enabling secure, auditable agent…
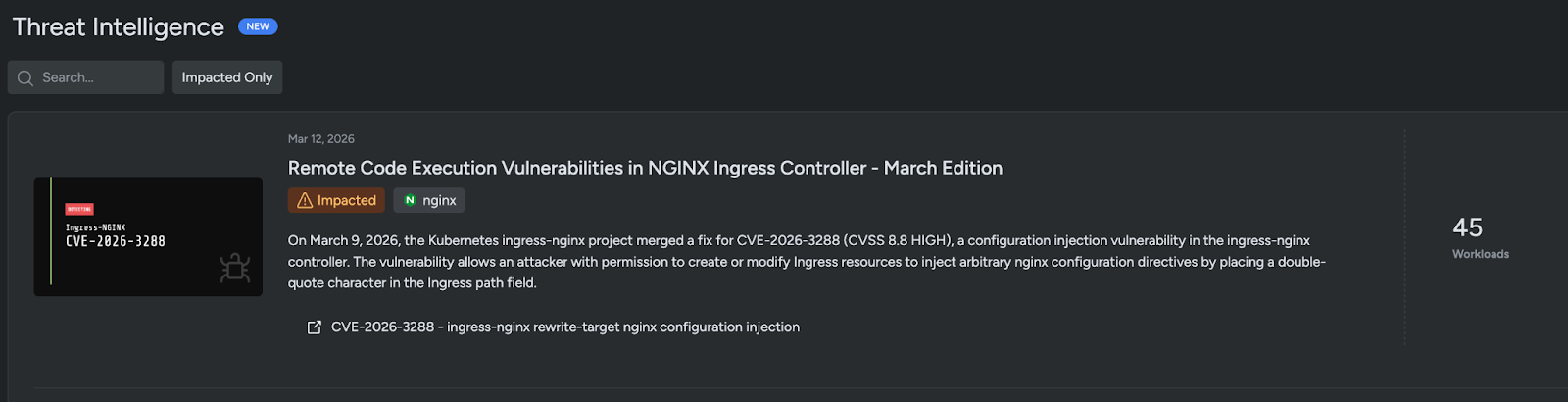
On March 9, 2026 the ingress-nginx project merged a fix for CVE-2026-3288, a configuration injection vulnerability in the NGINX Ingress Controller that allowed any user with permission to create or modify Ingress resources to inject arbitrary nginx directives by placing a double-quote character in the Ingress path. The flaw resulted from a missed sanitization in buildProxyPass() after a prior fix for CVE-2026-24512, can lead to RCE and secret disclosure, and Sysdig TRT published analysis plus a Falco rule to detect Ingress paths containing a double-quote. #CVE-2026-3288 #ingress-nginx
SpiderLabs, using LevelBlue OTX threat intelligence integrated with Cybereason XDR behavioral analytics, detected and blocked a suspected North Korea-linked operative who was hired through a help wanted ad after anomalous EntraID logins triggered alerts. The account was terminated within ten days following authentication anomalies from IPs 142[.]214.202.2 and 155[.]94.199.59 and an investigation found no residual access. #AstrillVPN #LazarusGroup
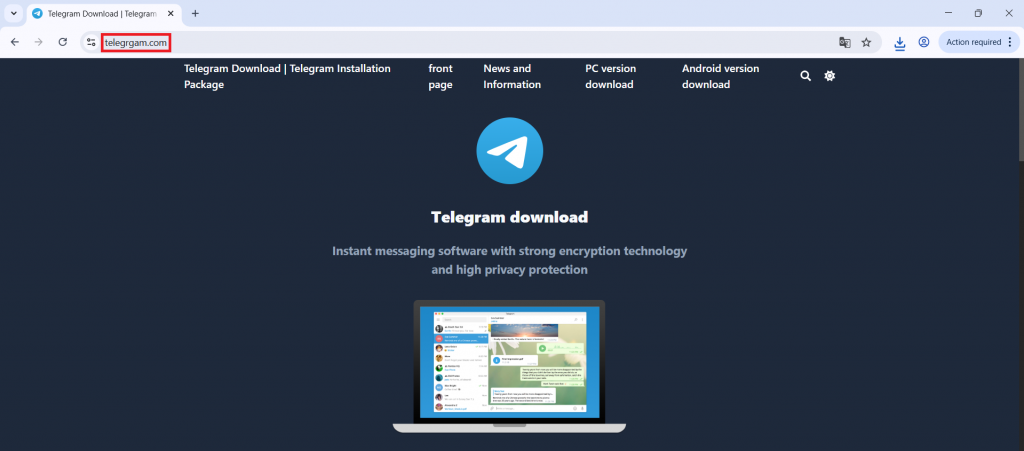
Fake Telegram Malware Campaign: Analysis of a Multi-Stage Loader Delivered via Typosquatted Websites
A typosquatted Telegram download site (telegrgam[.]com) distributed a malicious installer tsetup-x64.6.exe that modifies Windows Defender exclusions, drops staged payload files, and executes a DLL loader to reconstruct and run a PE payload from XML in memory. The in-memory payload communicates with a C2 at jiijua[.]com / 27.50.59.77:18852 for commands and runtime updates while using registry markers for persistence. #tsetup_x64_6_exe #AutoRecoverDat_dll
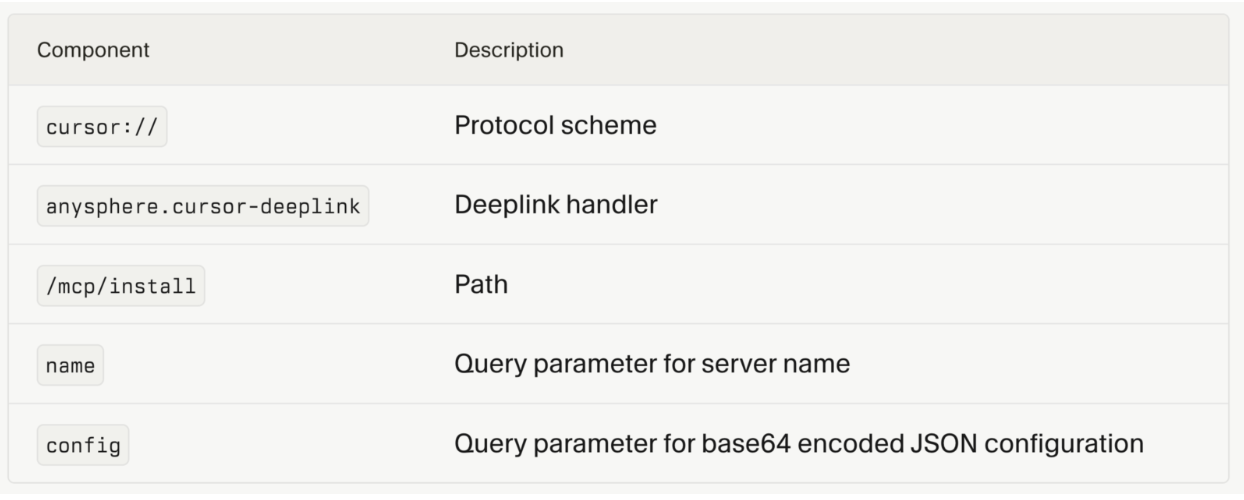
Proofpoint researchers disclosed “CursorJack”, a proof‑of‑concept showing how Cursor IDE’s cursor:// MCP deeplinks can be abused via social engineering to install malicious MCP servers or execute arbitrary commands. In tests a single user click plus acceptance of the install prompt could fetch and run staged scripts that retrieve a Metasploit/Meterpreter payload…
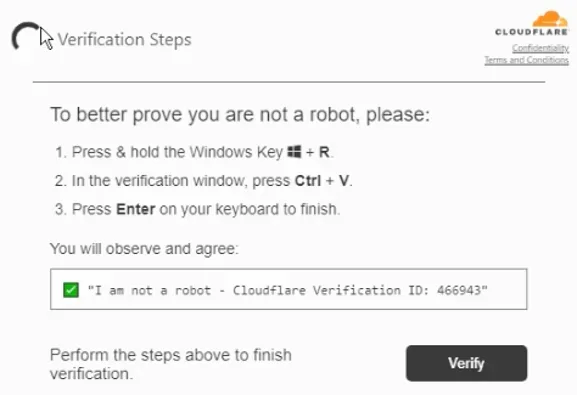
Ransomware operator LeakNet has shifted from buying access to running ClickFix lures on compromised legitimate websites and introduced a Deno-based, in-memory loader that executes base64-encoded payloads, fingerprints hosts, and establishes C2 with minimal disk artifacts. After initial access the group consistently uses jli.dll DLL sideloading in C:ProgramDataUSOShared, PsExec for lateral movement, and S3 buckets for payload staging, creating repeatable detection opportunities #LeakNet #Deno
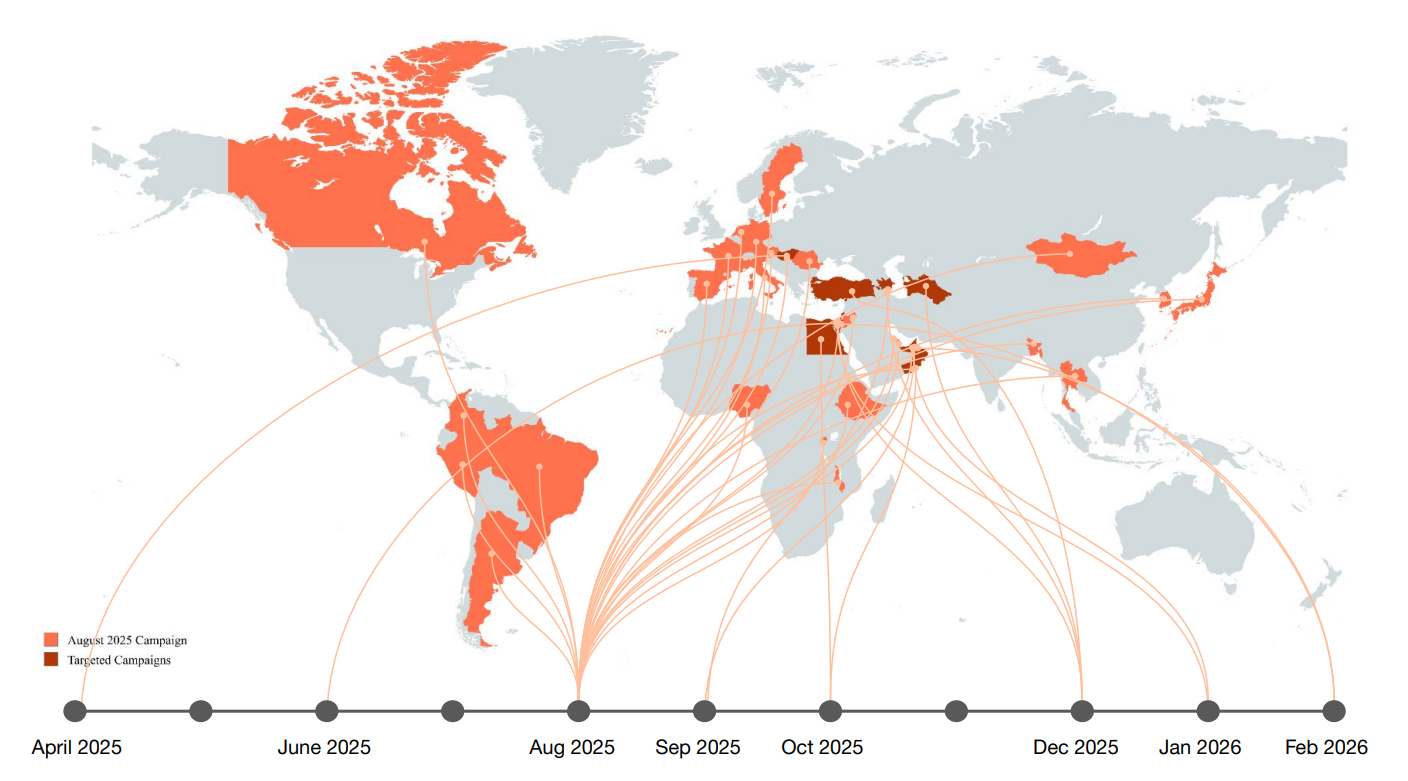
Boggy Serpens, an Iranian state-aligned cyberespionage group, has evolved its tradecraft to combine trusted-relationship compromises with AI-assisted and Rust-based tooling to target diplomatic and critical infrastructure worldwide, highlighted by a four-wave campaign against a UAE marine and energy company. Their toolkit and techniques include BlackBeard, LampoRAT, UDPGangster, Nuso and GhostBackDoor, use…
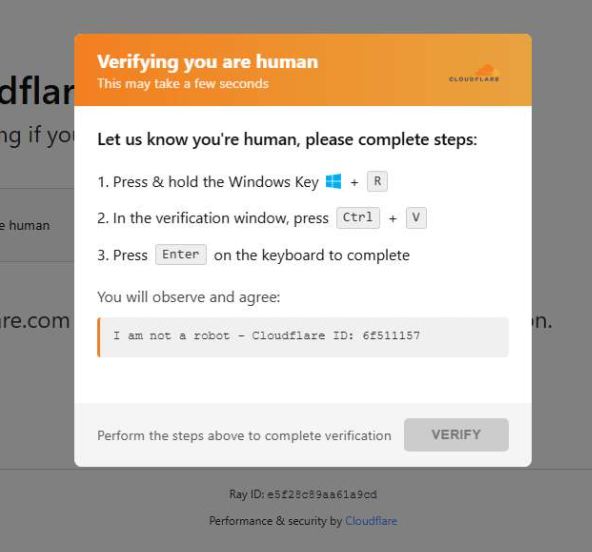
Researchers observed a campaign using fake CAPTCHA and ClickFix social engineering on compromised WordPress sites to trick users into running commands that launch an obfuscated HTA, download a malicious MSI, and ultimately load the Vidar infostealer in memory. The chain leverages built-in Windows binaries (mshta, curl, msiexec), WMI checks, XOR obfuscation,…
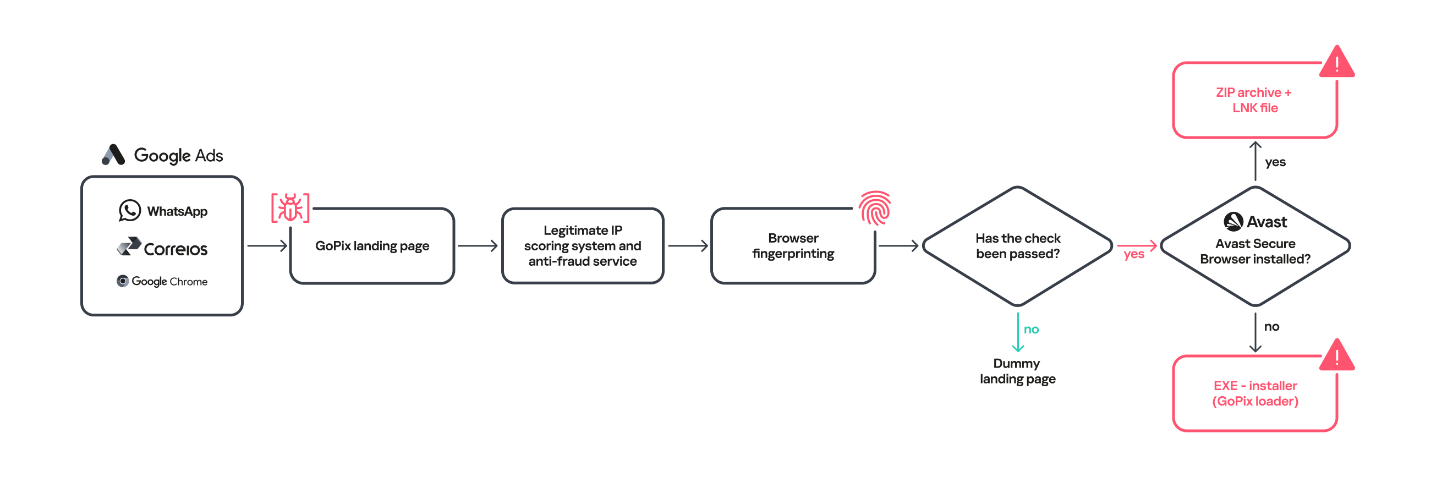
GoPix is an advanced Brazilian banking trojan that uses malvertising via Google Ads, stolen code-signing certificates, obfuscated PowerShell, memory-only implants, and short-lived C2s to target internet banking users, Pix transactions, Boleto slips, and cryptocurrency wallets. The malware executes a novel man-in-the-middle attack by using malicious PAC files and injecting trusted root certificates into browser memory while evading analysis with anti-fraud checks and in-memory execution. #GoPix #Pix
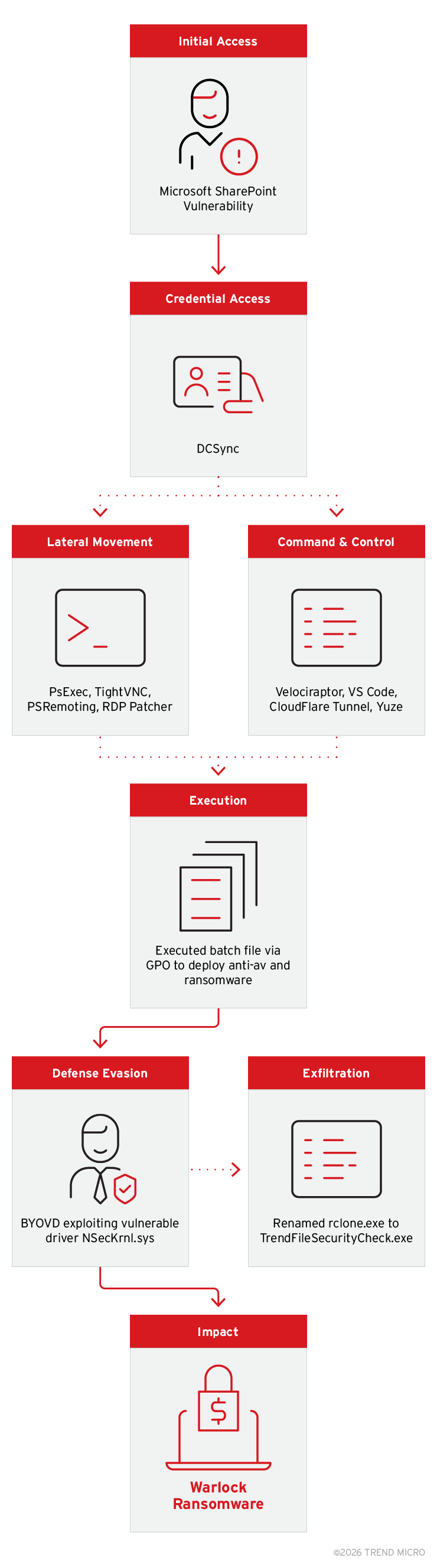
Warlock has expanded its post‑exploitation toolkit—adding TightVNC, the Yuze tunneling tool, and a persistent BYOVD technique that abuses the NSecKrnl.sys driver—to improve persistence, lateral movement, and kernel‑level defense evasion. The group continues to reuse legitimate tools (Velociraptor, VS Code tunnels, Cloudflare Tunnel, Supabase hosting, and renamed rclone) and deploys ransomware via…
Cofense PDC observed a phishing campaign that uses the LiveChat SaaS platform to impersonate brands (PayPal and Amazon) and engage victims in real-time chat to harvest credentials, credit card details, MFA codes, and PII. The campaign leverages branded chat pages and redirects (lc[.]chat and other domains) to capture data and bypass MFA, demonstrating social engineering combined with SaaS abuse. #PayPal #LiveChat
The Konni APT ran a multi-stage campaign using spear-phishing archives that delivered malicious LNK files to install AutoIt-based RATs (EndRAT, RftRAT, RemcosRAT), maintain long-term persistence, and steal internal documents. The actor also abused compromised KakaoTalk PC sessions to redistribute malicious files to selected contacts, highlighting the need for EDR-centered, behavior-based detection and response. #Konni #KakaoTalk