Seqrite Labs identified a targeted phishing campaign that exploited a stored XSS in Zimbra Collaboration (CVE-2025-66376) by embedding obfuscated JavaScript directly in an HTML email to steal session tokens, credentials, backup 2FA codes, mailbox contents (90 days) and other account data. The campaign exfiltrated data over both DNS and HTTPS to a hardcoded C2 (zimbrasoft[.]com[.]ua) and is attributed with medium confidence to APT28 given tradecraft and targeting overlaps. #SpyPress.ZIMBRA #APT28
Keypoints
- Attack used a single HTML email with no attachments or external links; malicious JavaScript was embedded in a hidden div and triggered when viewed in a vulnerable Zimbra Classic web UI.
- The exploit leverages CVE-2025-66376, a stored XSS caused by insufficient sanitization of @import/CSS-related tag-name constructs, enabling reconstruction of an eval(atob(…)) payload via AntiSamy bypass.
- Stage-1 loader decodes Base64 + XOR (key “twichcba5e”) then injects a Stage-2 browser-resident stealer that inherits the victim’s session context and SOAP API rights.
- The stealer performs nine parallel collection tasks (credentials, CSRF token, 2FA scratch codes, app-specific passwords, device and OAuth consumer lists) and exfiltrates via DNS (Base32 chunks) and HTTPS POSTs to zimbrasoft[.]com[.]ua.
- The payload creates persistent access by minting an app-specific password named “ZimbraWeb”, enables IMAP (zimbraPrefImapEnabled: TRUE), and streams 90 days of email exports (/home/~/?fmt=tgz) to C2.
- Infrastructure included recently registered C2 domains (created 2026-01-20) and generated subdomains (js-*.i.zimbrasoft[.]com[.]ua); targeting was a Ukrainian government hydrology agency.
- Seqrite assesses medium-confidence attribution to APT28 (Operation GhostMail) based on code/technique overlaps with prior Zimbra-focused campaigns targeting Eastern Europe.
MITRE Techniques
- [T1583.001 ] Acquire Infrastructure: Domains – C2 domain registration used to host exfiltration endpoints (‘C2 domain registered just before the attack’)
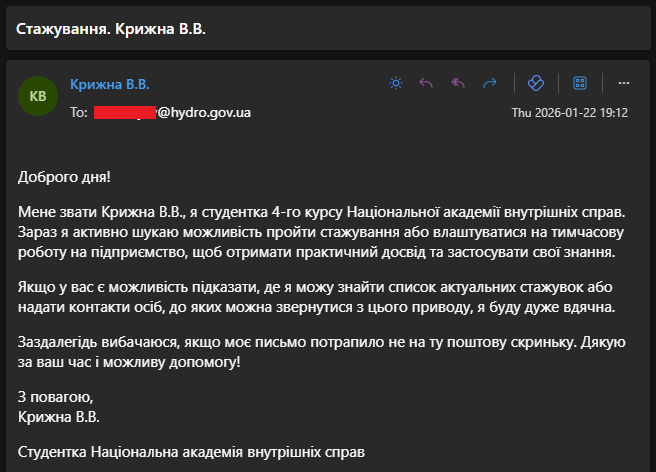
- [T1586.002 ] Compromise Accounts: Email Accounts – Phishing message originated from a NAVS student mailbox likely compromised (‘Phishing email sent from NAVS email’)
- [T1566.001 ] Phishing: Spearphishing Attachment – HTML email with embedded XSS payload used as the initial access vector (‘HTML email with embedded XSS payload’)
- [T1059.007 ] Command and Scripting Interpreter: JavaScript – Browser-resident JavaScript loader and stealer executed in the victim’s webmail session (‘Browser-resident payload’)
- [T1203 ] Exploitation for Client Execution – CVE-2025-66376 stored XSS in Zimbra exploited to execute script in the user’s session (‘CVE-2025-66376 XSS exploited’)
- [T1098.001 ] Account Manipulation: Additional Cloud Credentials – CreateAppSpecificPasswordRequest used to mint persistent credential ‘ZimbraWeb’ (‘CreateAppSpecificPasswordRequest mints a new persistent credential’)
- [T1027 ] Obfuscated Files or Information – Payload layered encoding (XOR + Base64) and @import token bypass to evade detection (‘XOR + Base64 layered encoding, @import token’)
- [T1564.001 ] Hide Artifacts: Hidden Files and Directories – Malicious code hidden inside display:none HTML blocks to avoid visual inspection (‘Payload hidden from visual inspection’)
- [T1528 ] Steal Application Access Token – GetOAuthConsumersRequest used to enumerate OAuth consumers and steal tokens (‘GetOAuthConsumersRequest’)
- [T1539 ] Steal Web Session Cookie – CSRF token stolen from localStorage to perform authenticated SOAP calls (‘CSRF token from localStorage’)
- [T1111 ] Multi-Factor Authentication Interception – Backup 2FA recovery codes harvested via GetScratchCodesRequest (‘Backup 2FA code theft via GetScratchCodesRequest’)
- [T1555.003 ] Credentials from Password Stores: Credentials from Web Browsers – Autocomplete DOM injection used to harvest browser-saved credentials (‘Autocomplete DOM injection harvest’)
- [T1082 ] System Information Discovery – GetInfoRequest used to fingerprint the server and dump configuration (‘GetInfoRequest server fingerprint’)
- [T1087.003 ] Account Discovery: Email Account – Account identities and aliases gathered via GetIdentitiesRequest and DOM scraping (‘GetIdentitiesRequest and DOM scraping’)
- [T1069 ] Permission Groups Discovery – GetOAuthConsumersRequest used to enumerate permissions and authorized apps (‘GetOAuthConsumersRequest’)
- [T1120 ] Peripheral Device Discovery – GetDeviceStatusRequest used to list ActiveSync-connected mobile devices (‘GetDeviceStatusRequest’)
- [T1114.002 ] Email Collection: Remote – 90-day email sweep using Zimbra export endpoint to collect mailbox archives (’90-day sweep’)
- [T1185 ] Browser Session Hijacking – Script escapes iframe sandbox to access top-level document and session context (‘window.top.document iframe escape’)
- [T1213 ] Data from Information Repositories – Server config and analytics dumped as zimbra_batch_analytics.json (‘Config dump zimbra_batch_analytics.json’)
- [T1041 ] Exfiltration Over C2 Channel – HTTPS POSTs to /v/d and /v/p used to upload large and small payloads to C2 (‘HTTPS POST /v/d and /v/p’)
- [T1071.004 ] Application Layer Protocol: DNS – Base32-encoded data exfiltrated via constructed DNS hostnames to i.zimbrasoft[.]com[.]ua (‘Base32-encoded DNS exfiltration’)
Indicators of Compromise
- [Email Hash/ID ] Phishing message identifier – Emailc010f64080b0b0997b362a8e6b9c618e
- [Domain ] C2 and generated subdomains – zimbrasoft[.]com[.]ua, js-l1wt597cimk[.]i[.]zimbrasoft[.]com[.]ua, js-26tik3egye4[.]i[.]zimbrasoft[.]com[.]ua
- [Domain Pattern ] DNS exfiltration hostnames – d-…i[.]zimbrasoft[.]com[.]ua (pattern used for Base32-chunked exfiltration)
- [File Name / Endpoint ] Mail export and config dump artifacts – /home/~/?fmt=tgz (daily .tgz mailbox exports), zimbra_batch_analytics.json (server config dump)
- [Account Setting / Credential Label ] Persistent credential and preference indicators – App-specific password name “ZimbraWeb”, zimbraPrefImapEnabled: TRUE
Read more: https://www.seqrite.com/blog/operation-ghostmail-zimbra-xss-russian-apt-ukraine/