Socket’s Threat Research Team identified six malicious Composer packages under the ophimcms namespace on Packagist that bundle trojanized JavaScript (disguised as jQuery) to exfiltrate URLs, inject ads, hijack clicks, and redirect mobile users to gambling and adult sites. The campaign uses userstat[.]net and FUNNULL-operated infrastructure (notably union[.]macoms[.]la) as C2/redirect hosts and remains live despite OFAC sanctions; #FUNNULL #OphimCMS
Category: Threat Research
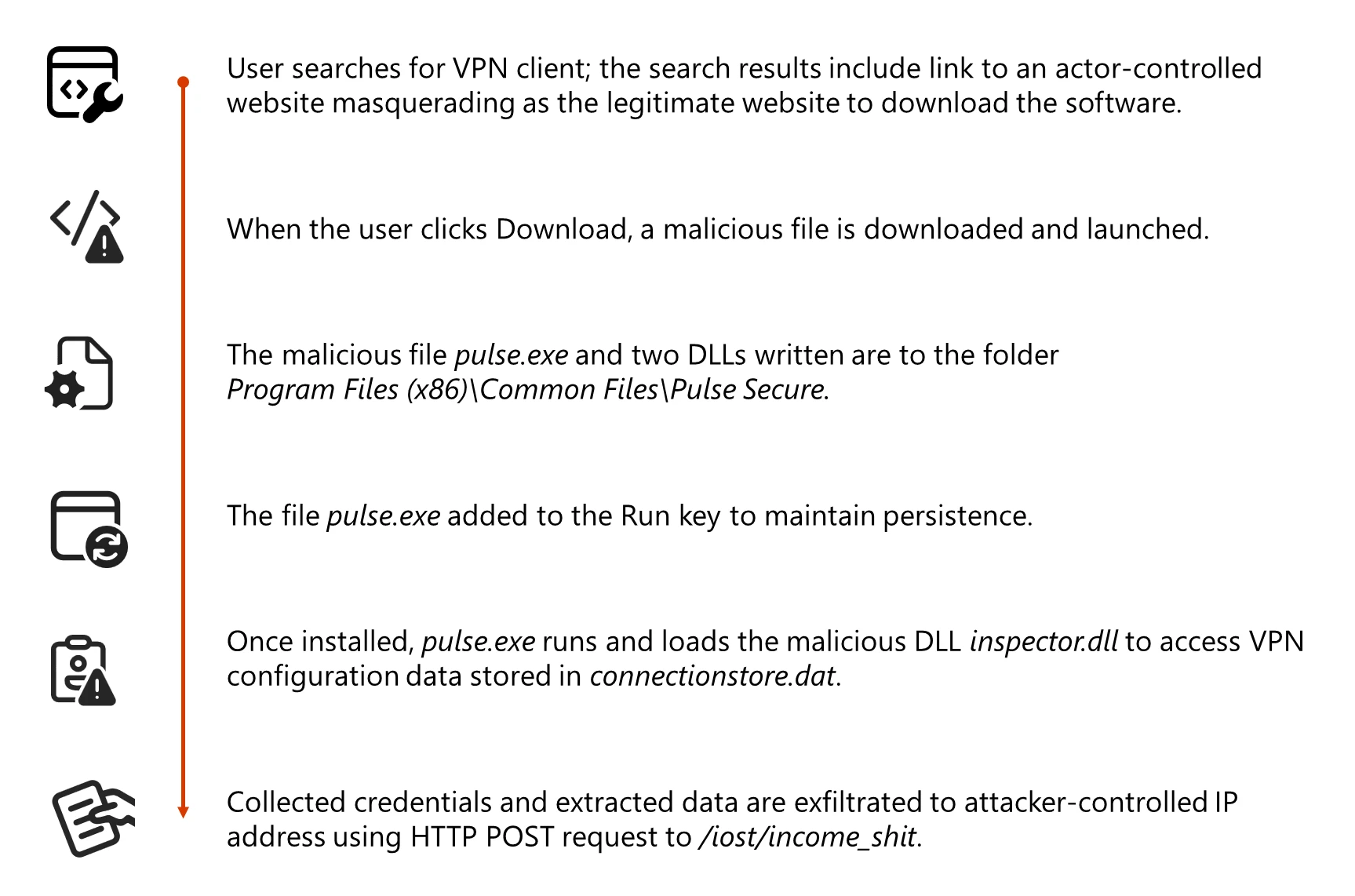
Storm-2561 used search-engine–poisoned pages to redirect users to spoofed VPN download sites and a malicious GitHub repository that distributed signed MSI installers which side‑loaded malicious DLLs. The dropped components (dwmapi.dll and inspector.dll, a Hyrax infostealer variant) captured VPN credentials and connection data from Pulse Secure directories and exfiltrated them to attacker-controlled infrastructure (194.76.226[.]93:8080). #Storm-2561 #Hyrax

Handala Hack is an online persona operated by Void Manticore, an Iranian MOIS‑affiliated actor responsible for multiple destructive wiping and hack‑and‑leak operations against targets in Israel, Albania, and the United States. The group conducts hands‑on intrusions using compromised VPN credentials, RDP and NetBird for lateral movement, and deploys multiple concurrent destructive techniques including a custom Handala wiper, an AI‑assisted PowerShell wiper, MBR corruption, and VeraCrypt disk encryption. #HandalaHack #VoidManticore
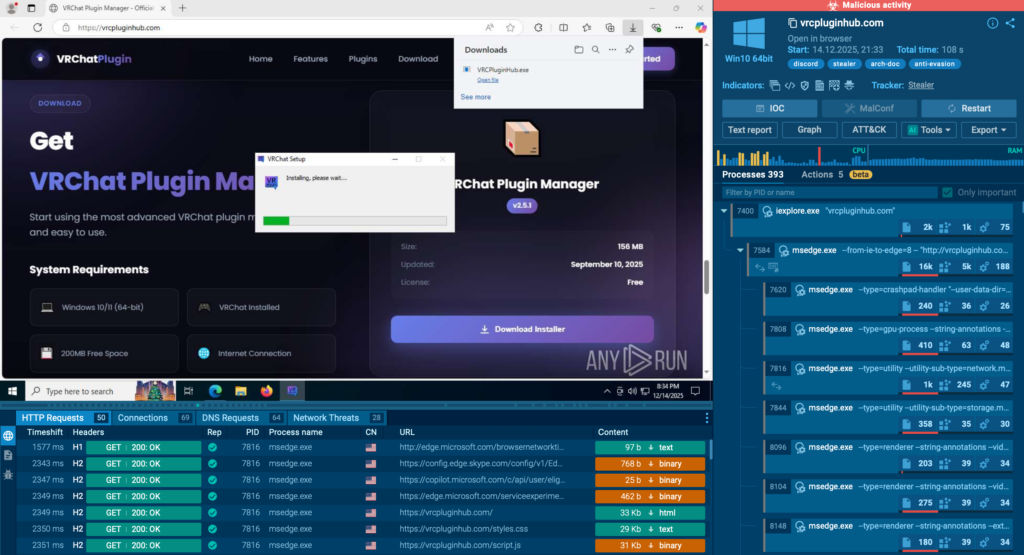
MicroStealer is an info‑stealer that uses a layered NSIS → Electron → Java delivery chain to harvest browser credentials, session cookies, screenshots, and wallet files, exfiltrating collected data to Discord webhooks and attacker-controlled servers. ANY.RUN observed the family in 40+ sandbox sessions, noted distribution via compromised or impersonated accounts, and warned…

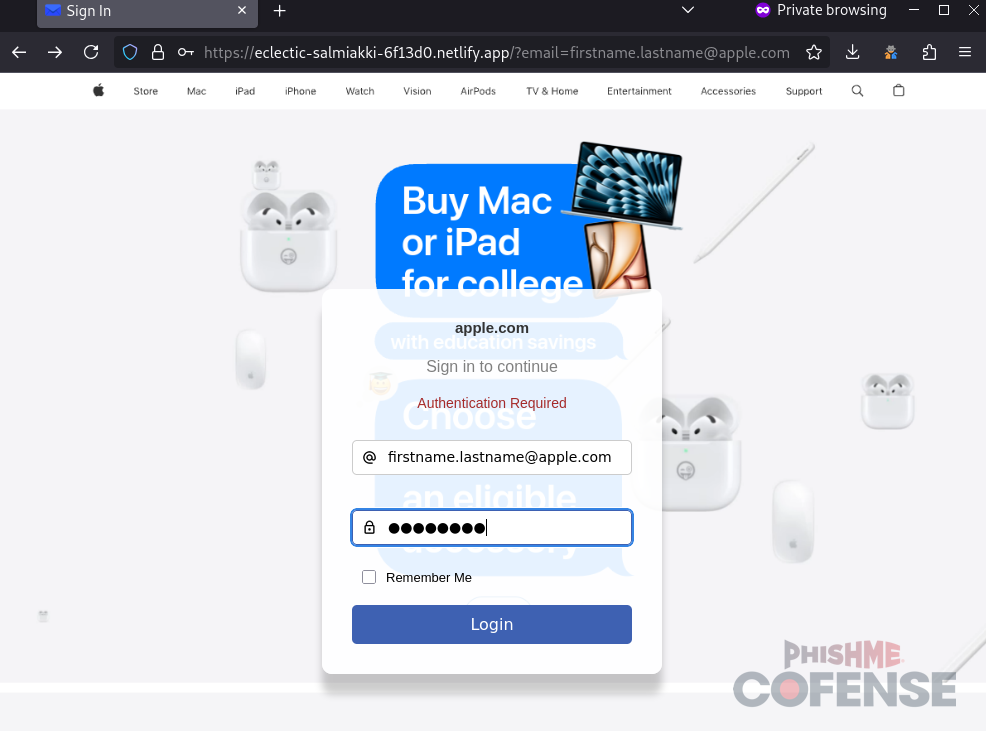
Datadog Security Research identified an active adversary-in-the-middle (AiTM) phishing campaign using typosquatted domains and a reverse-proxy phishing kit to harvest validated AWS Console credentials and likely one-time passwords (OTPs). The operation used AWS SES click-tracking links, rapid infrastructure rotation, and post-compromise access from a Mullvad VPN egress node with console logins observed within 20 minutes of credential submission. #AWS #MullvadVPN
The article describes how threat actors abuse the Telegram Bot API to exfiltrate credentials and files from phishing pages and malware families such as Agent Tesla, WSH RAT, and Pure Logs Stealer. It details sample POST requests that reveal bot authorization tokens and chat IDs, outlines investigation methods using getMe/getUpdates/forwardMessage, and recommends blocking api.telegram.org/bot endpoints and user training. #AgentTesla #LoneNone
PixRevolution is a novel Android banking trojan that streams victims’ screens in real time and uses an operator (human or AI) to replace PIX recipients during a transfer, redirecting funds instantly. It is distributed via convincing fake Google Play Store pages and impersonated Brazilian brands, exploiting Accessibility and MediaProjection APIs to operate stealthily and evade signature-based detection. #PixRevolution #PIX
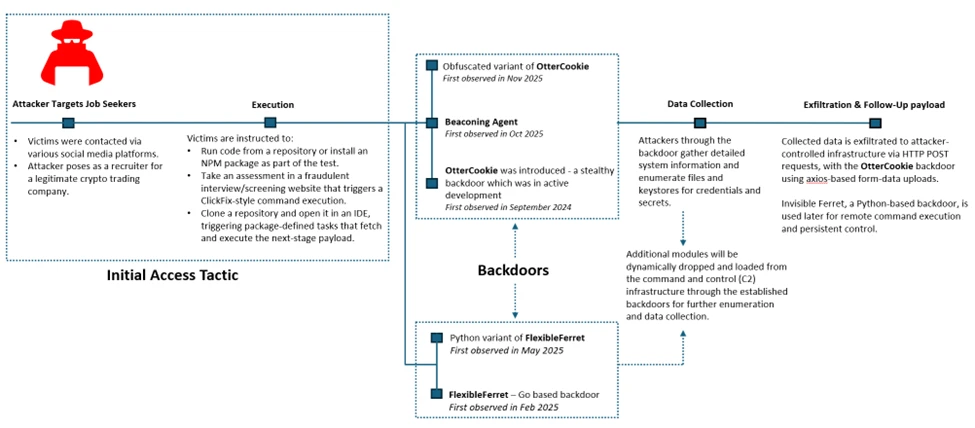
Microsoft Defender Experts documented the Contagious Interview campaign that uses fake technical interview workflows to trick developers into running malicious NPM packages and Visual Studio Code tasks, delivering backdoors like Invisible Ferret and FlexibleFerret. The attackers harvest API tokens, cloud credentials, and signing keys while maintaining persistence via modular backdoors and registry RUN key modifications #InvisibleFerret #FlexibleFerret
Phishing emails impersonating United Healthcare promise a free Oral‑B toothbrush to lure recipients to malicious landing pages that harvest PII and payment card data. Attackers have moved from Azure Blob Storage links to obfuscated IPv6‑mapped IPv4 URLs (e.g., http://[::ffff:5111:8e14]/ → 81.17.142.20) and use domains such as redirectingherenow[.]com and redirectofferid[.]pro. #UnitedHealthcare #OralB…

A joint advisory from the Australian Cyber Security Centre (ACSC), New Zealand NCSC, and CERT Tonga warns that the INC Ransom affiliate-driven RaaS ecosystem is increasingly targeting healthcare and other high-value organizations across Australia, New Zealand, and Pacific Island states, using tactics like spear-phishing, exploitation of unpatched internet-facing systems, purchased credentials, and legitimate tools for exfiltration. The advisory links disruptive incidents — including a June 15, 2025 attack on Tonga’s Ministry of Health — to INC Ransom (also known as Tarnished Scorpion / GOLD IONIC) and identifies Roman Khubov (aka blackod) as controlling infrastructure used in data exfiltration; #INCRansom #CERTTonga

Datadog found that from at least August 29, 2025 to September 25, 2025 Microsoft Copilot Studio did not log certain administrative actions involving sharing, authentication, App Insights, and publication of agents. Datadog reported the issue to the Microsoft Security Response Center (MSRC) on September 2, 2025, MSRC remediated logging by October 5, 2025, but later regressions left two of the originally reported events intermittently unlogged and Datadog continues to report this to MSRC. #CopilotStudio #MSRC
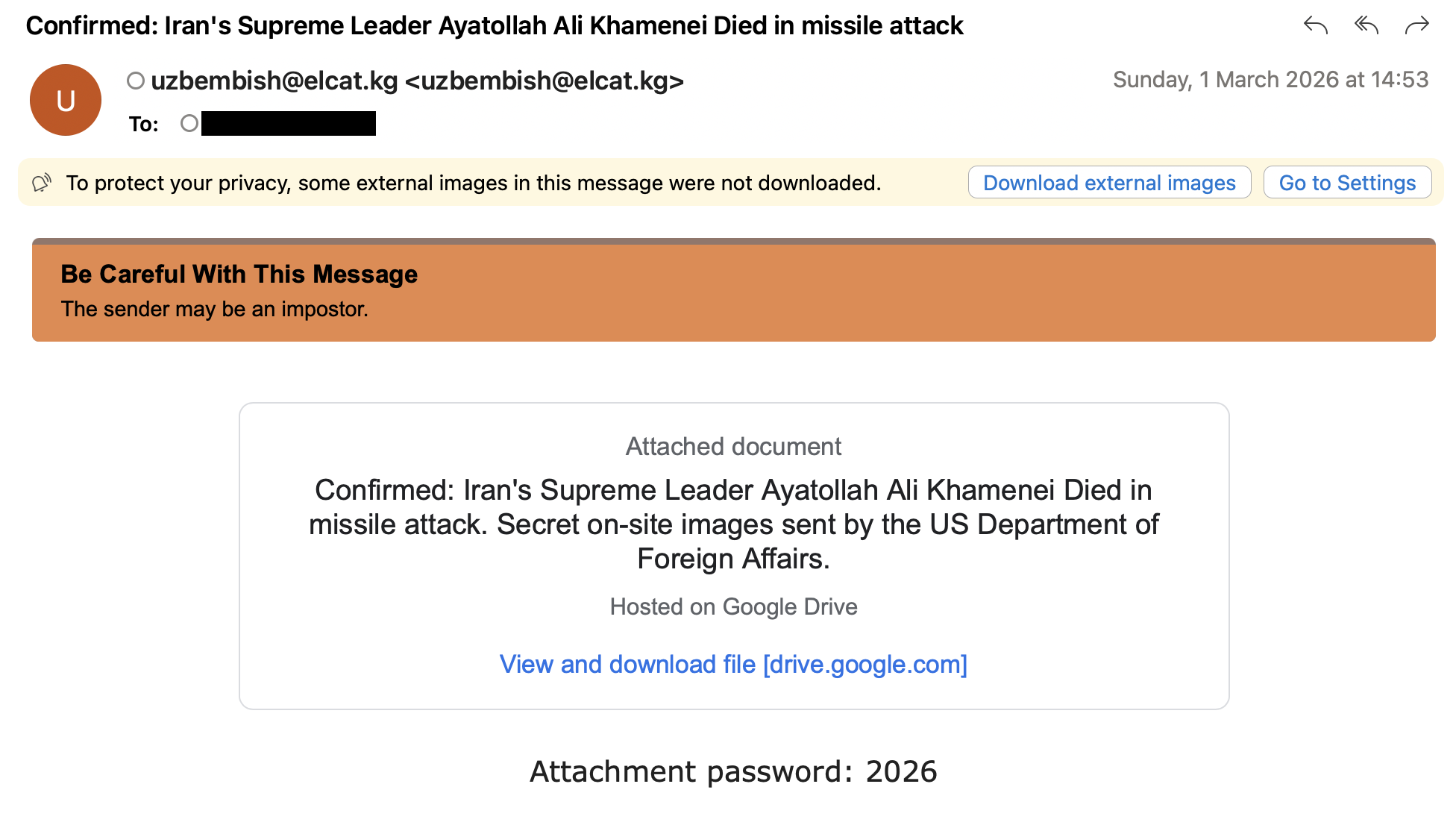
Proofpoint observed multiple state-aligned and opportunistic threat actors using Iran-conflict-themed lures to conduct credential-phishing, malware delivery, and intelligence-collection campaigns against Middle Eastern governments, diplomatic entities, and Western think tanks. Tracked activity includes clusters UNK_InnerAmbush, TA402, UNK_RobotDreams, UNK_NightOwl, TA473, and TA453 leveraging LNK-based loaders, DLL sideloading, PowerShell-retrieved Rust backdoors, and Cobalt Strike…
Earth Lusca (aka FishMonger) is a China-linked threat actor active since 2019 that conducts long‑term cyber-espionage against government, media, telecommunications, academic, and religious organizations while also running financially motivated campaigns against cryptocurrency platforms. Recent campaigns show expanded tooling and tradecraft — including the new Go-based, multi-platform backdoor KTLVdoor, extensive use of ShadowPad/Winnti toolsets, and a large, cloud-hosted, rotating C2 infrastructure to maintain stealth. #EarthLusca #KTLVdoor
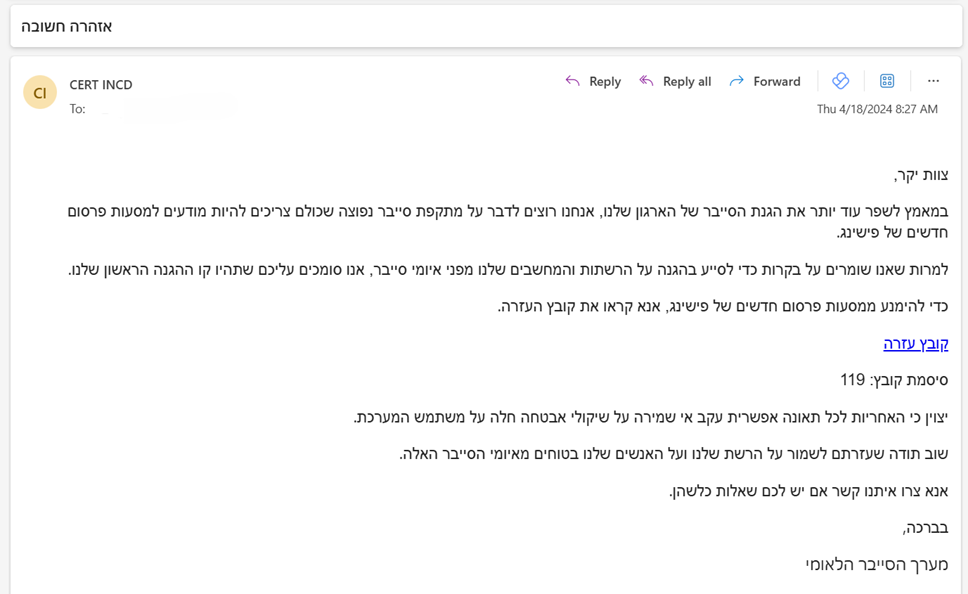
Iran-linked actors—particularly MOIS-associated groups such as Void Manticore and MuddyWater—are increasingly using criminal tools, malware-as-a-service, and cybercrime infrastructure to further state objectives while complicating attribution. This trend includes use of infostealers (Rhadamanthys), botnets (Tsundere/DinDoor), code-signing certificates shared across families, and ransomware branding (Qilin) in incidents such as the Shamir Medical Center intrusion. #VoidManticore #Rhadamanthys

Socket’s Threat Research Team discovered a coordinated supply chain campaign in the Rust ecosystem where five malicious crates (chrono_anchor, dnp3times, time_calibrator, time_calibrators, time-sync) posed as time utilities but covertly exfiltrated .env secrets to attacker-controlled infrastructure. Four crates were rapidly yanked from crates.io while chrono_anchor used minor obfuscation to remain live until reported and removed. #chrono_anchor #timeapis
