Cybereason GSOC observed a rise in REMCOS RAT campaigns that trojanize legitimate software packages (notably portable Shotcut ZIPs) by replacing genuine DLLs with malicious ones to load multi-stage payloads. The campaigns use callback-style shellcode injection (abusing APIs like EnumSystemCodePagesW), in-memory loaders, and persistent C2 communications to perform keylogging, credential theft, surveillance, and privilege escalation. #REMCOS #Shotcut
Category: Threat Research
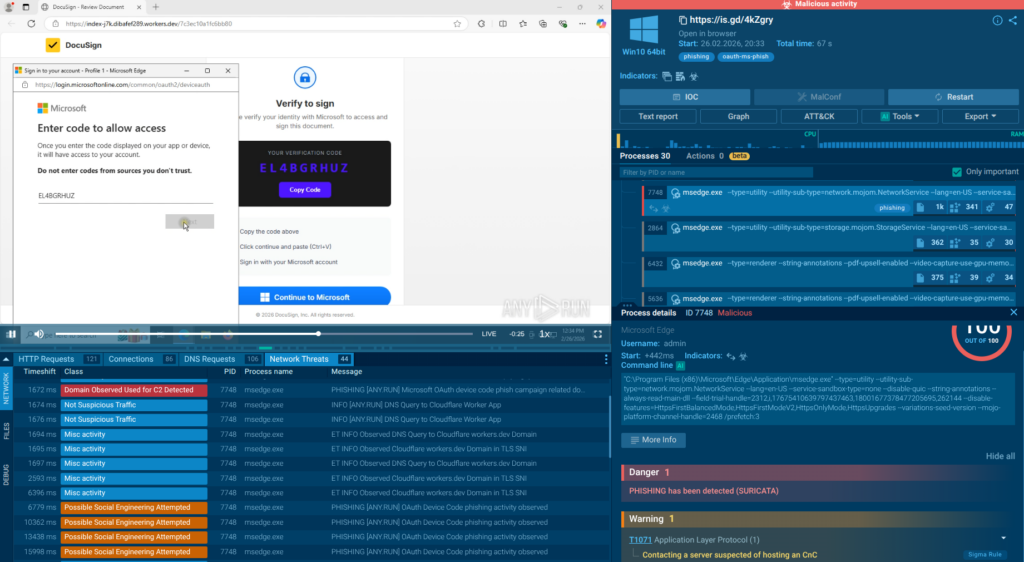
Phishing campaigns abusing Microsoft’s OAuth Device Code flow have rapidly increased, with ANY.RUN analysts detecting more than 180 phishing URLs in a single week that trick victims into approving attacker-initiated device authorizations. Because victims complete authentication on legitimate Microsoft pages and traffic runs over encrypted HTTPS, attackers receive OAuth tokens for…
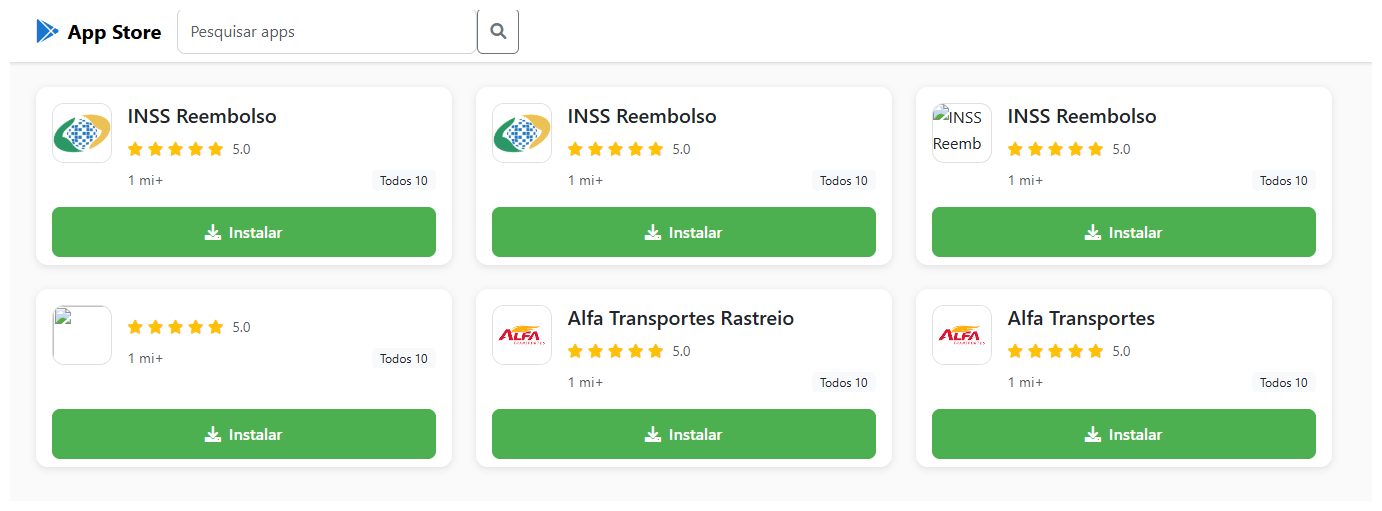
BeatBanker is an Android Trojan campaign that targets users in Brazil via phishing sites impersonating the Google Play Store to deliver a crypto miner and a banking module (recent samples drop the BTMOB RAT instead). It maintains persistence by looping an almost inaudible audio file, abuses Accessibility and overlay capabilities to intercept USDT transactions, and uses Firebase Cloud Messaging for command-and-control. #BeatBanker #BTMOB

Generative AI enables attackers to operate at machine speed, allowing autonomous workflows that can exploit misconfigured Fortinet appliances, map internal networks, dump credentials from Active Directory, and extract data from thousands of organizations in under an hour. Picus proposes an agentic BAS architecture—four cooperating agents (Researcher, Red Teamer, Simulator, Coordinator)—that compresses threat intelligence to remediation into minutes and automates safe, high-coverage simulations and vendor-specific remediation. #Fortinet #Picus
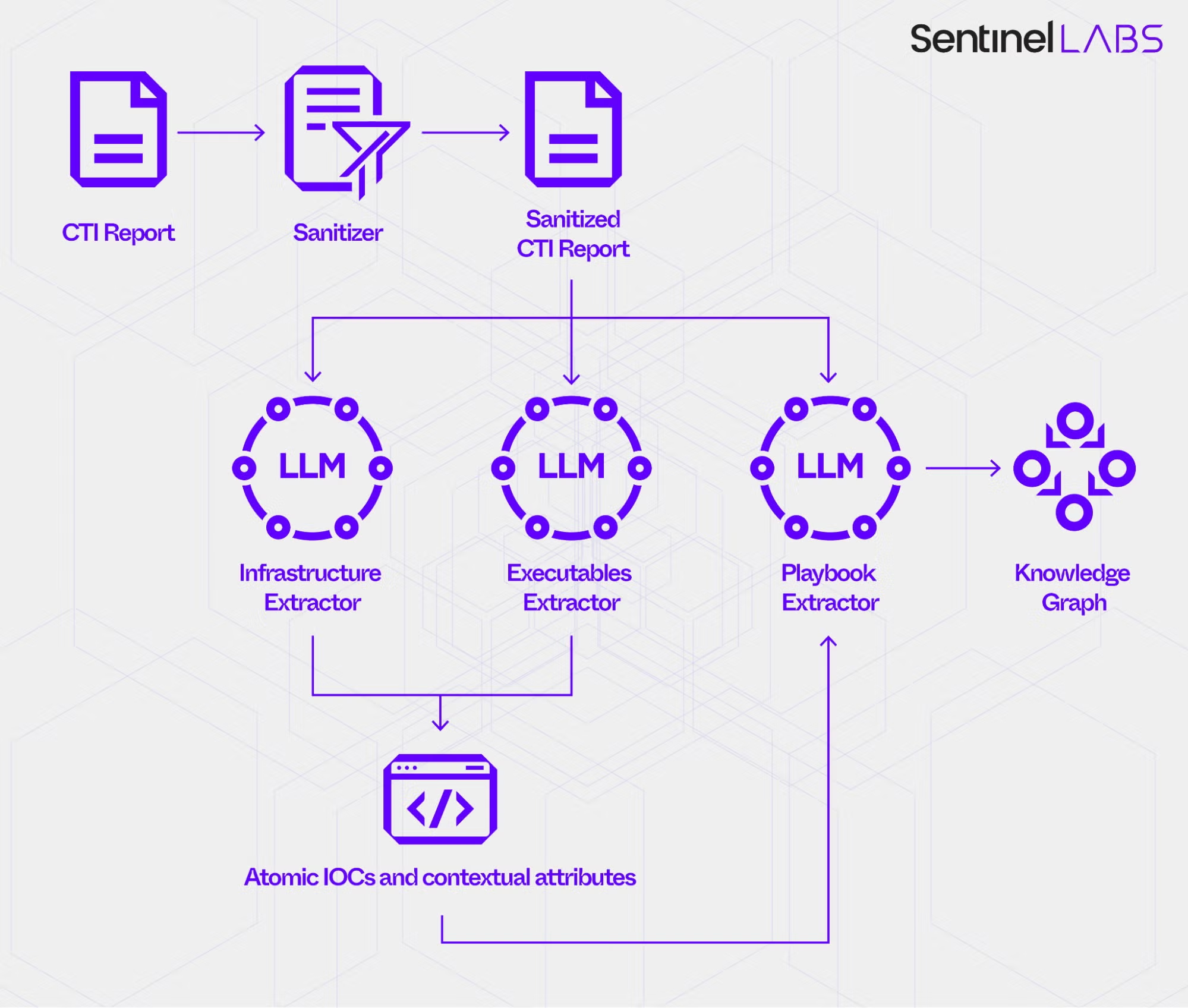
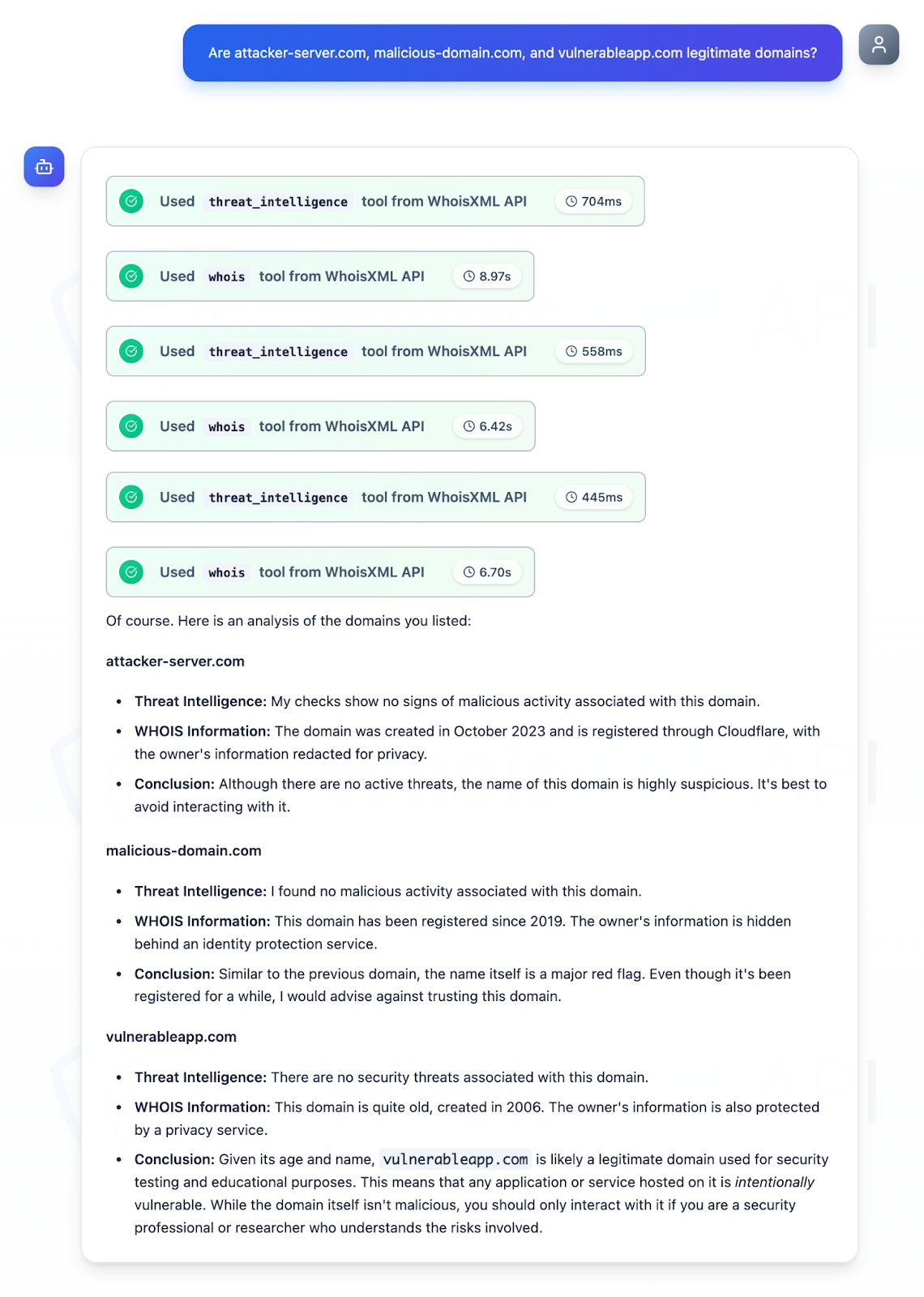
This post evaluates using large language models to extract and contextualize information from CTI reports, turning narrative into structured JSON entities and a unified knowledge graph for downstream defense workflows. It describes a three‑phase workflow (sanitization, LLM extraction, knowledge‑graph assembly), experimental results across multiple LLMs, and operational trade‑offs in accuracy, abstention, ensembling, and data‑model design. #GPT4_1 #ClaudeSonnet4_5
The EU and INTERPOL added alleged BlackBasta leader 35-year-old Russian national Oleg Evgenievich Nefedov to their Most Wanted and Red Notice lists. Researchers analyzed network IoCs from a recent BlackBasta campaign—identifying 15 IP IoCs, thousands of related email- and string-connected domains, evidence of phishing and vulnerability exploitation for initial access, data exfiltration, and a double-extortion ransomware model. #BlackBasta #OlegNefedov
Customers reported intrusive browser notifications that Malwarebytes scans did not detect because the alerts were web push notifications granted by deceptive websites rather than malware on their devices. These campaigns used quiz and fake extension sites to trick users into clicking “Allow,” with domains such as triviabox[.]co.in and unsphiperidion[.]co.in enabling persistent…
Acronis TRU uncovered a targeted smishing campaign delivering a trojanized Red Alert Android app to Israeli users via SMS impersonating Home Front Command, preserving legitimate alert functionality while running hidden spyware. The implant uses certificate spoofing, runtime hooks, layered obfuscation and a C2 at hxxps://api[.]ra-backup[.]com/analytics/submit[.]php to harvest SMS, contacts, location, device accounts and installed apps for continuous exfiltration. #RedAlert #AridViper
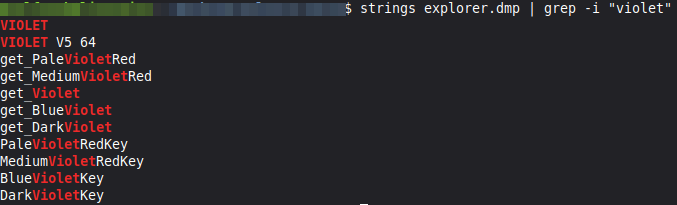
The analysis attributes the memory-carved payload to a variant of VioletRAT, showing multi-function RAT capabilities including dynamic Pastebin-based bootstrap, encrypted TCP C2, remote shell, file download/execution, credential harvesting and remote desktop features. The sample includes mixed version markers (“Violet v4.7” and “VIOLET V5 64”) and an embedded C2 password (Nuevo2022$), suggesting reuse of legacy code across builds. #VioletRAT #Pastebin

Zscaler ThreatLabz documented a surge of Middle East conflict-themed campaigns that include fake news blogs, fraudulent portals and storefronts, donation scams, meme-coin pump-and-dump promotions, and multiple malware delivery chains leveraging LNK/CHM, DLL sideloading, and in-memory shellcode. Notable detections include Mustang Panda using a LOTUSLITE chain via libmemobook.dll and Kugou sideloading, and web-based lures delivering StealC; #LOTUSLITE #StealC

Coruna is a multi-chain iOS exploit kit first seen in February 2025 that contains five exploit chains across 23 exploits targeting iOS 13–17.2.1 and has been observed in watering-hole and mass-deployed scam campaigns. Validin’s historical DNS and host-response analysis, plus YARA hunts, mapped extensive PLASMAGRID C2 and dropper infrastructure including Iran-themed lures and hundreds of suspected delivery domains. #Coruna #PLASMAGRID

The article describes a Use-After-Free vulnerability in CSynchronousSuperWetInk within dwmcore.dll that can be exploited via the DirectComposition API to achieve RCE in DWM and escalate to SYSTEM by reclaiming freed objects with a RECT-buffer heap spray called GetRECT. It also details the patch (feature flag Feature_1732988217), the exploitation primitives, and a CFG-bypassing gadget chain using __fnINSTRING and CStdAsyncStubBuffer2_Disconnect to mark spray memory RWX and execute inline shellcode. #DWM #GetRECT

Microsoft Threat Intelligence details how North Korean-linked groups such as Jasper Sleet, Coral Sleet, Emerald Sleet, and Sapphire Sleet are operationalizing generative and agentic AI across the cyberattack lifecycle—from reconnaissance and persona fabrication to AI-assisted malware development and post‑compromise misuse. The report highlights specific artifacts and behaviors including the OtterCookie AI-assisted payload, GAN-driven domain impersonation, prompt‑injection and jailbreak techniques, and provides mitigation guidance using Microsoft Defender, Purview, Security Copilot, and related controls. #JasperSleet #OtterCookie
.png)
A rapid post-strike activation of 60+ Iranian-aligned hacktivist groups combined with AI-assisted reconnaissance has turned a large, persistent US ICS/OT internet-exposure into an immediately exploitable attack surface. The report traces a decade-long escalation (Shamoon, TRITON/TRISIS, IOCONTROL) and shows how AI-generated Shodan queries, default credentials (e.g., Unitronics “1111”), and exposed HMI/web portals enable mass targeting at scale. #CyberAv3ngers #Unitronics

Analysis of a sophisticated Android banking Trojan (tracked as TaxiSpy) reveals integrated RAT functionality, native library obfuscation, rolling XOR string encryption, Firebase-backed C2, and real-time VNC-like remote control specifically targeting Russian banking apps. The malware exfiltrates SMS, contacts, call logs, notifications, clipboard and keylogging data, can become the default SMS app, and communicates with C2 at 193.233.112[.]229 while using identifiers like worker key 9bc096a5f4ec7ba133d743cbaf4b8a2e. #TaxiSpy #RuTaxi
