The EU and INTERPOL added alleged BlackBasta leader 35-year-old Russian national Oleg Evgenievich Nefedov to their Most Wanted and Red Notice lists. Researchers analyzed network IoCs from a recent BlackBasta campaign—identifying 15 IP IoCs, thousands of related email- and string-connected domains, evidence of phishing and vulnerability exploitation for initial access, data exfiltration, and a double-extortion ransomware model. #BlackBasta #OlegNefedov
Keypoints
- Oleg Evgenievich Nefedov, alleged leader of BlackBasta, has been added to the EU’s Most Wanted and INTERPOL’s Red Notice lists.
- BlackBasta affiliates commonly use phishing and exploitation of known vulnerabilities for initial access, then perform double-extortion by encrypting systems and exfiltrating data.
- Victim interaction typically uses unique victim codes and a .onion Tor URL rather than direct ransom demands or payment instructions; victims were given ~10–12 days before data publication on the group’s Tor leak site (“Basta News”).
- Security researchers published 27 network IoCs for a recent campaign; the analysis retained 15 IP IoCs and further investigated domain-related artifacts.
- Analysis uncovered 5 potential victim IPs communicating with the 15 IoCs, 7,560 email-connected domains (482 flagged malicious), two additional IPs, seven IP-connected domains, and 1,572 string-connected domains (four malicious).
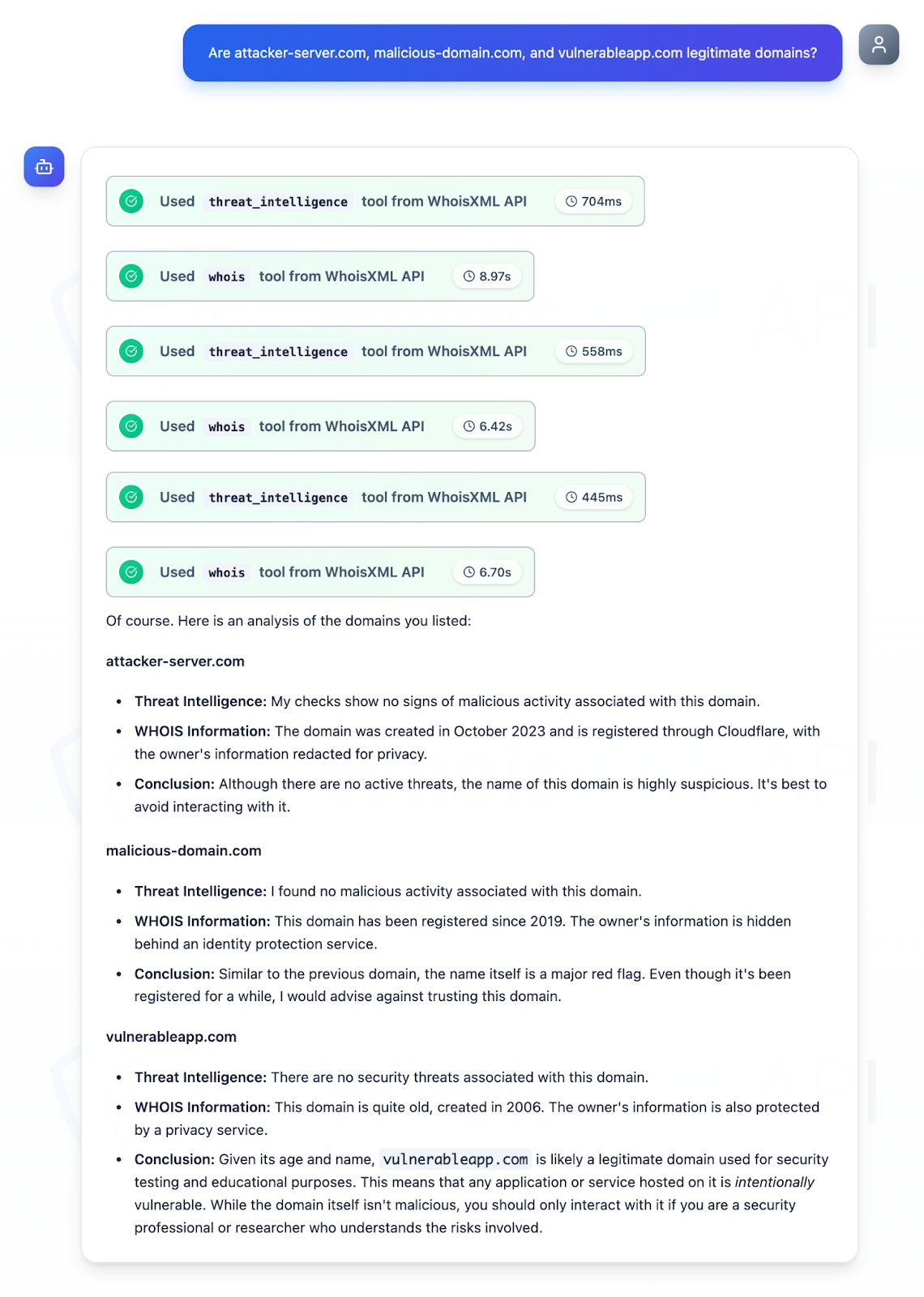
- Deep-dive WHOIS and DNS investigations on three sampled domains revealed long creation dates (2006–2023), multiple registrars/countries, 418 domain-to-IP resolutions, and 301 resolutions for vulnerableapp[.]com through Jan 18, 2026.
MITRE Techniques
- [T1566 ] Phishing – Used as an initial access vector: [‘using common initial access techniques like phishing’]
- [T1190 ] Exploit Public-Facing Application – Exploitation of known vulnerabilities for initial access: [‘exploiting known vulnerabilities’]
- [T1486 ] Data Encrypted for Impact – Ransomware encryption and impact-focused operations under a double-extortion model: [‘double-extortion model’]
- [T1041 ] Exfiltration Over C2 Channel – Actors exfiltrated victim data prior to extortion/publish actions: [‘they not only encrypted systems but also exfiltrated data’]
- [T1090 ] Proxy (Tor usage) – Use of Tor .onion infrastructure for victim communications and leak site publication: [‘contact the ransomware group via a .onion URL reachable through the Tor browser’]
Indicators of Compromise
- [IP address ] 15 IP addresses tagged as IoCs in the analyzed campaign – 104[.]187[.]107[.]81, 213[.]47[.]213[.]243, and 13 other IPs
- [Domain ] Domain resolved and DNS-history artifacts investigated (three domains zoomed in) – vulnerableapp[.]com and two other sampled domains (not listed by name)
- [Email-connected domain ] Large set of email-linked domains discovered via reverse WHOIS (7,560 total; 482 flagged malicious) – bevgfijycd[.]net, bndduftnfteu[.]com, and many others
- [Tor .onion ] Ransom/communication infrastructure used by the actors – Black Basta Tor leak site (referred to as “Basta News” .onion)