BeatBanker is an Android Trojan campaign that targets users in Brazil via phishing sites impersonating the Google Play Store to deliver a crypto miner and a banking module (recent samples drop the BTMOB RAT instead). It maintains persistence by looping an almost inaudible audio file, abuses Accessibility and overlay capabilities to intercept USDT transactions, and uses Firebase Cloud Messaging for command-and-control. #BeatBanker #BTMOB
Keypoints
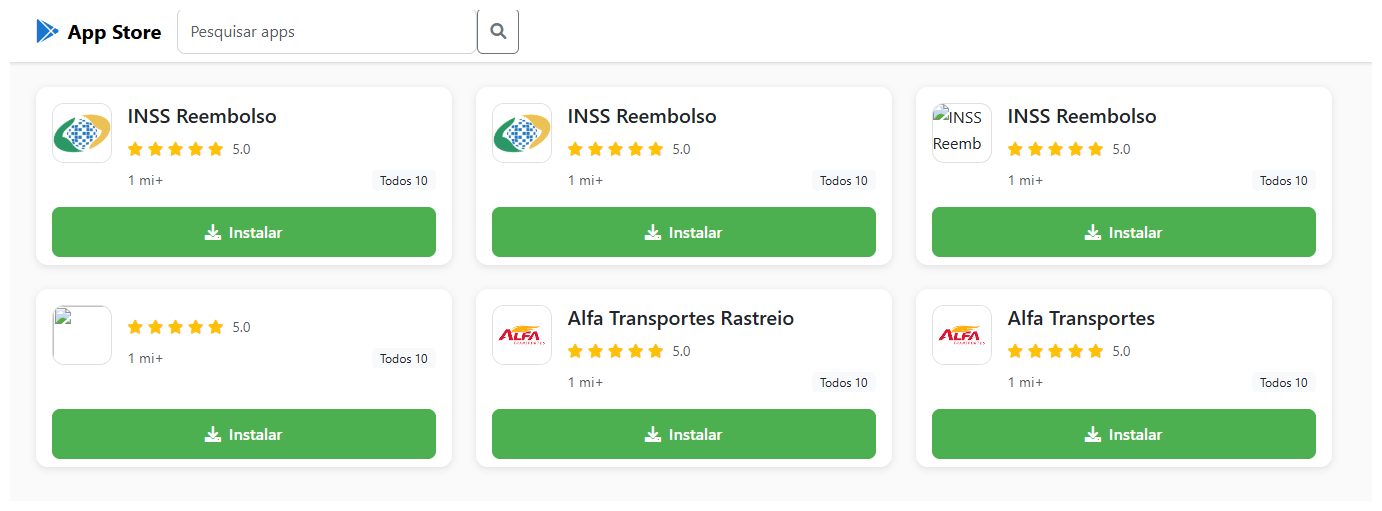
- Infection begins through a phishing site (cupomgratisfood[.]shop) that mimics the Google Play Store and hosts malicious APKs like “INSS Reembolso”.
- The initial APK is packed and uses a native library (libludwwiuh.so) and a DEX loader (l.so) that loads malicious code directly into memory to evade detection.
- BeatBanker deploys a Monero miner (XMRig) by downloading and decrypting an ELF miner (renamed d-miner) and connecting to pool.fud2026[.]com or pool-proxy.fud2026[.]com:9000.
- Persistence is achieved by running a foreground service that continuously plays a short, looped audio file (audio output8.mp3) and pins a system update notification to prevent termination.
- The banking module abuses Accessibility permissions and overlays to intercept and replace USDT transaction destinations in Binance and Trust Wallet, stealing funds silently.
- Recent variants replace the banking module with the BTMOB RAT (MaaS), which provides full remote control, keystroke/screen capture, silent installation, and additional persistence mechanisms.
MITRE Techniques
- [T1204 ] User Execution – Phishing via a fake Google Play Store to trick victims into installing malicious APKs. Quote: (‘a counterfeit website, cupomgratisfood[.]shop, that looks exactly like the Google Play Store.’)
- [T1105 ] Ingress Tool Transfer – Downloading and decrypting additional payloads (ELF miner, APKs) from attacker-controlled servers. Quote: (‘the malicious application downloads and executes an ELF file containing a cryptomining payload… hxxps://accessor.fud2026.com/libmine-.so’).
- [T1027 ] Obfuscated Files or Information – Packing, XOR stack strings, and string/ELF decryption to hide malicious code and runtime strings. Quote: (‘the loader… names are encrypted in the stack using XOR (stack strings technique) and restored at runtime’).
- [T1102 ] Web Service – Use of legitimate cloud messaging infrastructure (Firebase Cloud Messaging) as the primary C2 channel to receive commands and telemetry. Quote: (‘uses Google’s legitimate Firebase Cloud Messaging (FCM) as its primary command‑and‑control (C2) channel’).
- [T1543 ] Create or Modify System Process – Establishing a persistent foreground service and pinned notification with continuous media playback to prevent OS termination. Quote: (‘activates a foreground service with silent media playback… keeps a notification about a system update pinned to the foreground’).
- [T1531 ] Accessibility Features Abuse – Abusing Android Accessibility permissions to monitor the foreground app, capture text, set fields, and overlay transaction screens to replace wallet addresses. Quote: (‘substitutes the destination address with an attacker-controlled one using AccessibilityNodeInfo.ACTION_SET_TEXT’).
Indicators of Compromise
- [MD5 hashes ] payload identification – F6C979198809E13859196B135D21E79B (INSS Reebolso), D3005BF1D52B40B0B72B3C3B1773336B (StarLink)
- [Domains ] C2 / distribution infrastructure – cupomgratisfood[.]shop, fud2026[.]com, accessor.fud2026[.]com, pool.fud2026[.]com, pool-proxy.fud2026[.]com, bt-mob[.]net (and other domains listed)
- [Filenames / libraries ] components used by the malware – libludwwiuh.so, l.so (DEX loader), d-miner (decrypted miner), audio output8.mp3
- [Package names / APKs ] malicious apps and installers – com.destination.cosmetics (INSS Reebolso), INSS Reembolso app, StarLink APK (observed in newer campaign)
- [Network endpoints / pools ] mining endpoints – pool.fud2026[.]com:9000, pool-proxy.fud2026[.]com:9000
Read more: https://securelist.com/beatbanker-miner-and-banker/119121/