Analysis of a sophisticated Android banking Trojan (tracked as TaxiSpy) reveals integrated RAT functionality, native library obfuscation, rolling XOR string encryption, Firebase-backed C2, and real-time VNC-like remote control specifically targeting Russian banking apps. The malware exfiltrates SMS, contacts, call logs, notifications, clipboard and keylogging data, can become the default SMS app, and communicates with C2 at 193.233.112[.]229 while using identifiers like worker key 9bc096a5f4ec7ba133d743cbaf4b8a2e. #TaxiSpy #RuTaxi
Category: Threat Research

Socket’s Threat Research Team discovered a malicious Chrome extension, lmToken Chromophore (extension ID bbhaganppipihlhjgaaeeeefbaoihcgi), that impersonates imToken while posing as a hex color visualizer and immediately redirects users to threat actor-controlled phishing pages. The extension fetches a remote target from a hardcoded JSONKeeper endpoint and opens lookalike domains that capture 12/24-word seed phrases or private keys, enabling immediate wallet takeover. #imToken #lmTokenChromophore

This blog post provides comprehensive, practical guidance to prepare for, detect, and recover from destructive cyberattacks by hardening identity, backups, virtualization, cloud, OT/IT segmentation, and CI/CD/Kubernetes pipelines while listing detection opportunities and recommended controls. It also includes actionable detection rules and resilience practices (examples: BABYWIPER detection rules, domain controller backup commands) to reduce impact and speed recovery. #BABYWIPER #ActiveDirectory
Since at least 2020, a China‑communicating threat cluster tracked as CL-UNK-1068 has targeted high‑value organizations across South, Southeast and East Asia using web shells, custom and open‑source tools, DLL side‑loading, FRP tunneling and extensive credential theft. The group’s toolkit includes GodZilla, AntSword, Xnote, ScanPortPlus and custom FRP variants and the activity…
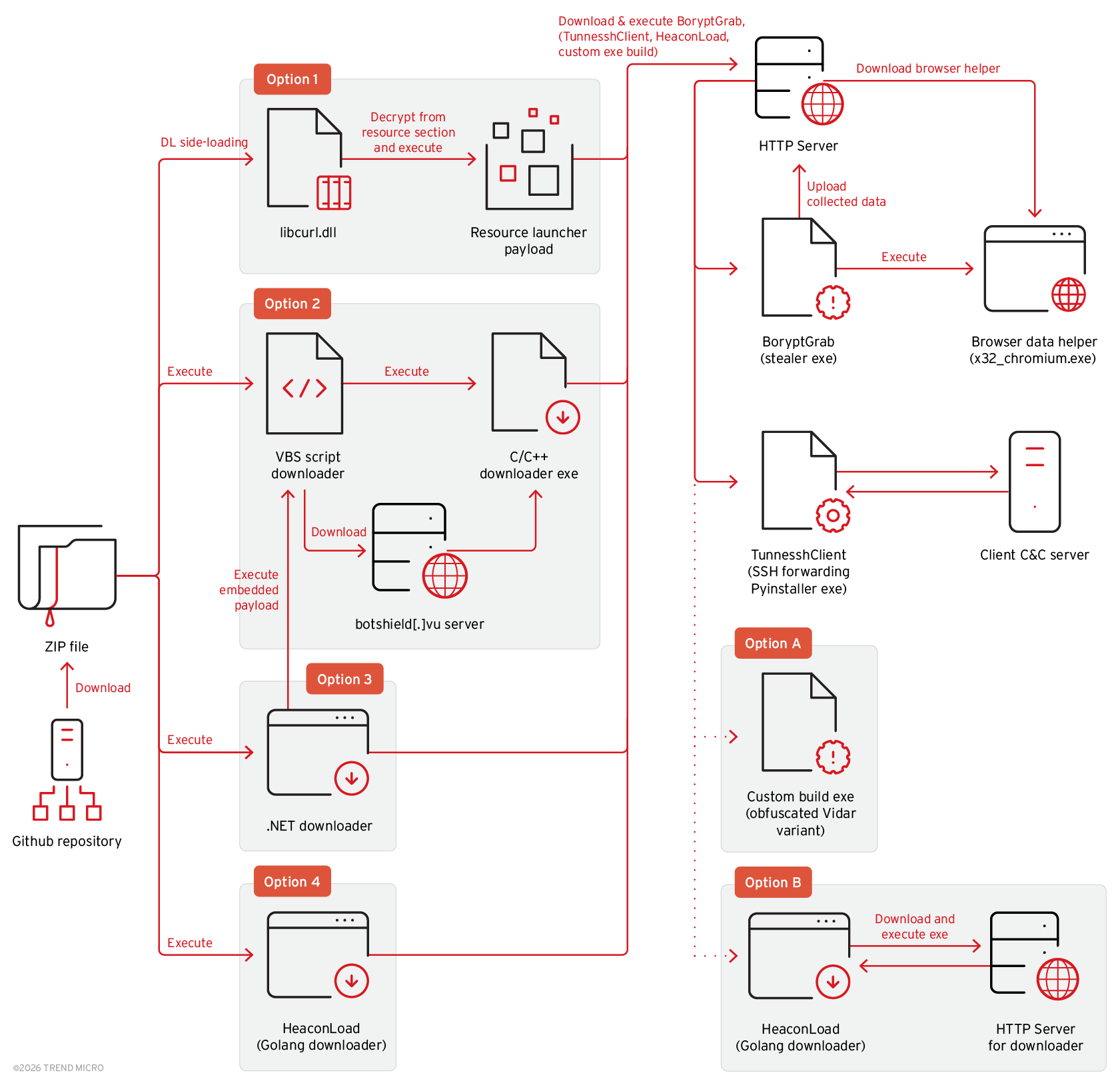
BoryptGrab is a newly identified data‑stealing stealer delivered via SEO‑optimized fake GitHub repositories and deceptive download pages that harvests browser data, cryptocurrency wallet information, system data, screenshots, Telegram/Discord tokens, and other files. The campaign uses multiple staged download routes (DLL side‑loading, VBS and .NET downloaders, Golang loaders) and delivers additional payloads…
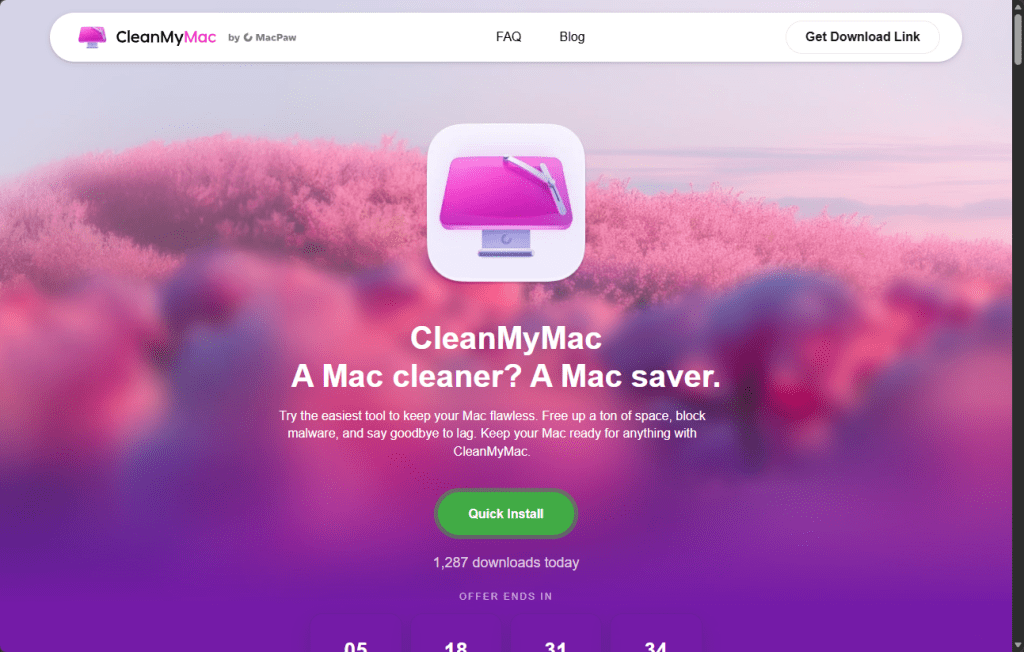
A fake CleanMyMac website tricks macOS users into pasting a Terminal command that downloads and executes a loader which installs SHub Stealer to harvest passwords, Keychain contents, browser data, cryptocurrency wallets, and Telegram sessions. The malware also backdoors Electron-based wallet apps (Exodus, Atomic Wallet, Ledger Wallet, Ledger Live, Trezor Suite), installs…
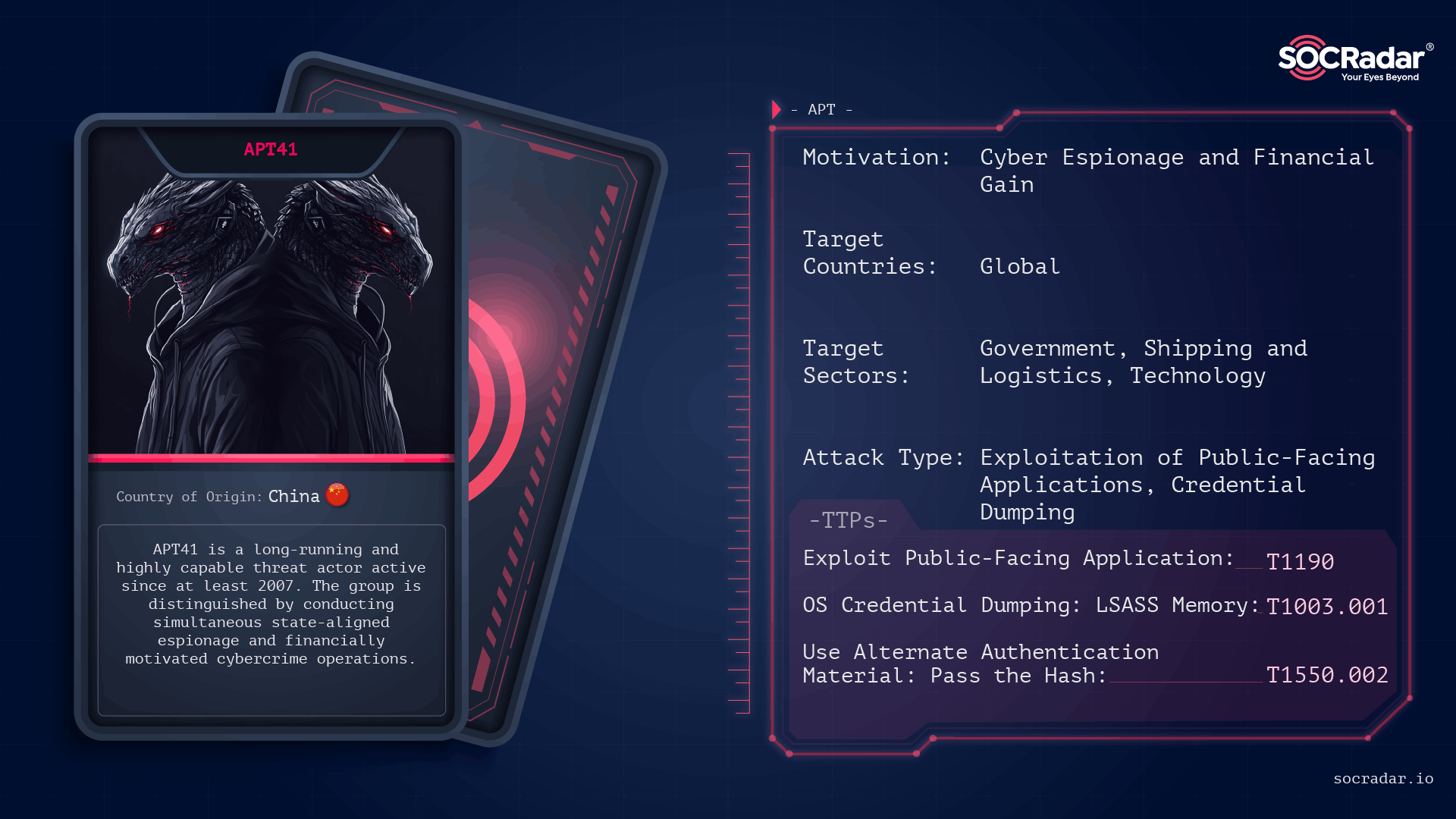
APT41 is a long-running, China-linked intrusion set that operates with a dual mission of state-aligned espionage and financially motivated cybercrime, using rapid vulnerability weaponization and long-dwell, living-off-the-land tradecraft. The group has exploited a range of public-facing systems and cloud services (including Log4Shell and Google Calendar-based C2) and has been tied to campaigns such as TOUGHPROGRESS and U.S. state government intrusions. #APT41 #TOUGHPROGRESS

Seedworm (aka MuddyWater/Temp Zagros/Static Kitten) has been observed active on multiple U.S. corporate and NGO networks since February 2026, deploying novel backdoors (Dindoor using Deno, and Python-based Fakeset) and attempting exfiltration via Rclone to cloud storage. The activity involved signed malware (certificates issued to “Amy Cherne” and “Donald Gay”), hosting on Backblaze S3 endpoints, and links to previously observed Stagecomp/Darkcomp activity, indicating a coordinated Iranian espionage campaign with potential for disruptive follow-on attacks. #Seedworm #Dindoor
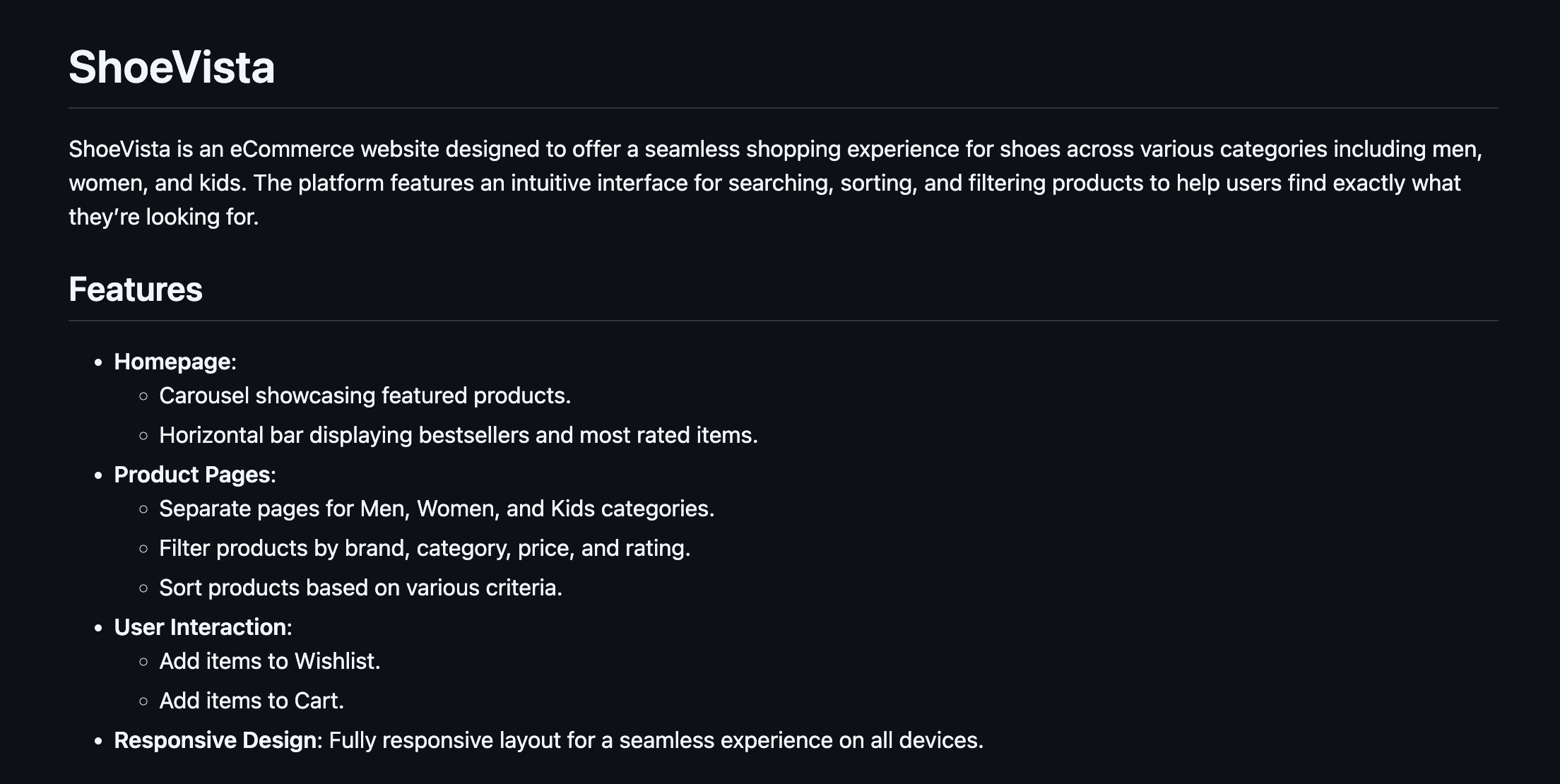
eSentire TRU analyzed a multi-stage supply-chain attack where a weaponized GitHub repository named “ShoeVista” deployed highly obfuscated Node.js and Python stagers to retrieve DEV#POPPER RAT and the OmniStealer payloads from blockchain transactions and remote C2 servers. The campaign—attributed with high confidence to a North Korean state-sponsored APT—focused on developer-targeted credential and crypto-wallet theft; eSentire published tooling (DEV#STOPPER.js), detection guidance, and remediation recommendations. #DEVPOPPER #OmniStealer

Cyble identified ClipXDaemon, an autonomous Linux clipboard hijacker that targets X11 sessions to intercept and replace copied cryptocurrency wallet addresses with attacker-controlled addresses, operating entirely without network command-and-control. The threat is delivered via a bincrypter-based encrypted shell loader, stages an in-memory dropper and a persisted ELF under ~/.local/bin, and uses ChaCha20-encrypted regexes, process masquerading, and Wayland avoidance to evade detection. #ClipXDaemon #X11
An email-based campaign delivers a RAR attachment that unpacks an executable which loads VIP_Keylogger entirely in memory via steganography, AES decryption, and process hollowing or CLR-based loading depending on the sample. K7Labs analysed two kill-chains, detailed the keylogger’s data-stealing features and exfiltration methods, and provided IOCs including hashes, C2 domains and an IP address. #VIP_Keylogger #K7Labs
.png)
The report warns that a long‑building cyber threat to US critical infrastructure has accelerated, driven by nation‑state APTs, proxies, and dozens of hacktivist groups exploiting internet‑exposed ICS devices, phishing OT personnel, and long‑dwell IT‑to‑OT intrusions. Immediate defensive actions recommended include removing ICS interfaces from the internet, changing default credentials (e.g., Unitronics 1111), blocking industrial protocol ports, and auditing MSP/RMM access #VoltTyphoon #Unitronics

GTIG tracked 90 zero-days exploited in the wild in 2025, with a record 48% targeting enterprise technologies and notable increases in OS and mobile exploitation while browser exploitation declined. The report highlights rising commercial surveillance vendor activity, sustained PRC‑nexus focus on edge/security appliances, high-profile chains such as the SonicWall full-chain and DNG-based Samsung exploits, and warns that AI will accelerate both exploit discovery and exploit development. #BRICKSTORM #SonicWall

The United States and Israel launched coordinated strikes on Iran (Operation Epic Fury / Operation Lion’s Roar) that killed Supreme Leader Ali Khamenei and senior commanders, triggering widespread Iranian missile and drone retaliation across the region and significant commercial disruption such as a 90% decline in Strait of Hormuz transits and Qatar declaring force majeure. Cyber and influence operations are already active and expected to escalate, with identified Iranian-aligned hacktivist and IO networks (e.g., Handala Hack Team, Storm-2035) likely to employ scanning, brute forcing, password spraying, DDoS, and targeted influence campaigns. #HandalaHackTeam #APT34
Tycoon 2FA is a high-volume adversary-in-the-middle (AiTM) phishing-as-a-service platform that harvests credentials and Microsoft 365 and Gmail session cookies to bypass MFA and enable account takeover. Microsoft and a coalition of private and public partners, including Proofpoint and Europol, disrupted Tycoon 2FA infrastructure, seized 330 control panel domains, and filed a…
