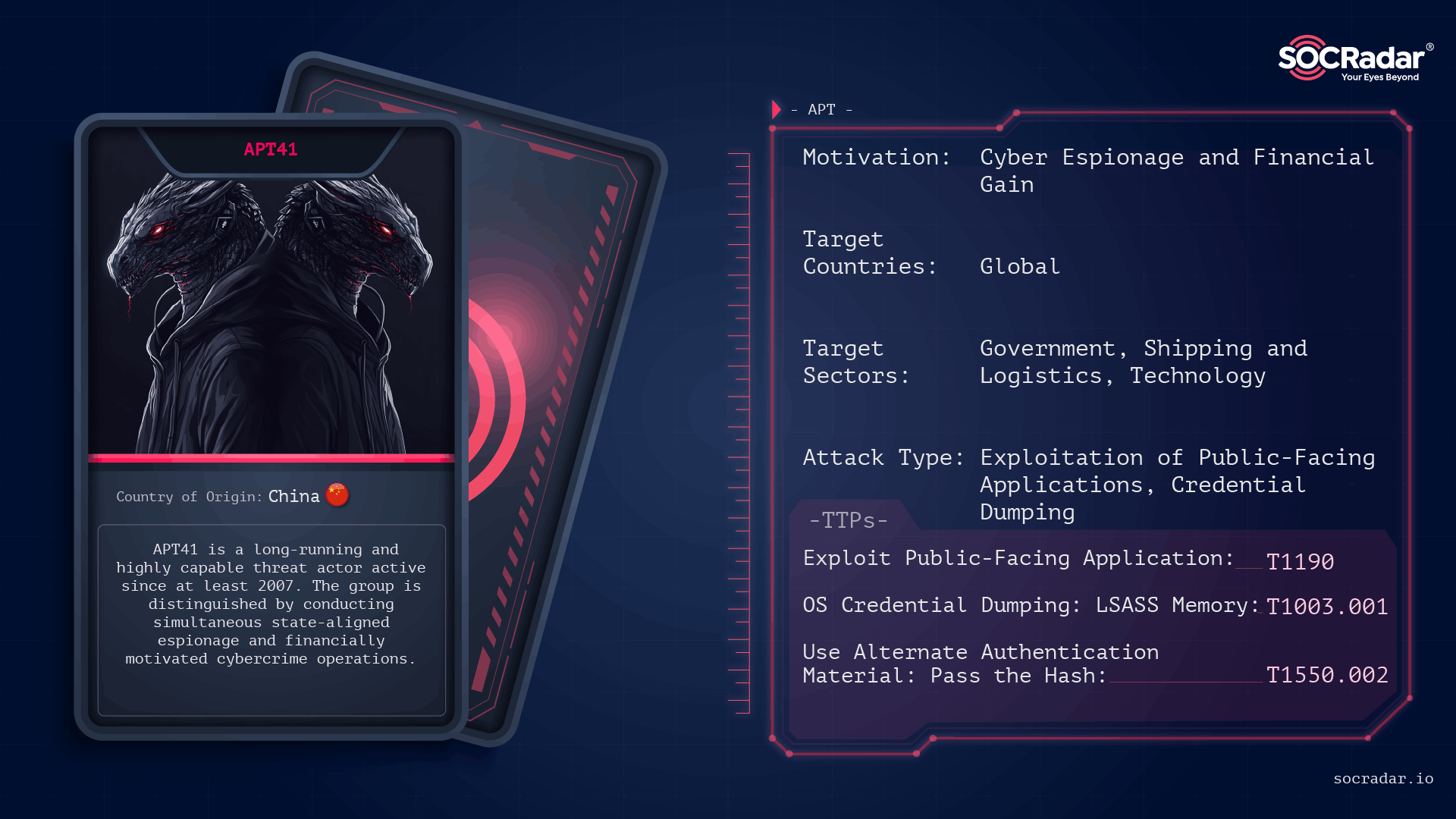
APT41 is a long-running, China-linked intrusion set that operates with a dual mission of state-aligned espionage and financially motivated cybercrime, using rapid vulnerability weaponization and long-dwell, living-off-the-land tradecraft. The group has exploited a range of public-facing systems and cloud services (including Log4Shell and Google Calendar-based C2) and has been tied to campaigns such as TOUGHPROGRESS and U.S. state government intrusions. #APT41 #TOUGHPROGRESS
Keypoints
- APT41 performs exploit-first intrusions, rapidly weaponizing n-day and zero-day vulnerabilities in public-facing applications to gain initial access.
- The group combines state-aligned espionage with financially motivated operations, targeting government, trade-policy, and commercial sectors globally.
- Post-compromise tradecraft emphasizes living-off-the-land execution (PowerShell, certutil, rundll32), credential theft (Mimikatz, LSASS dumps), and long-term persistence (web shells, scheduled tasks, disguised services).
- APT41 has used unconventional C2 channels and cloud services to hide activity, including embedding encrypted commands in Google Calendar events and exfiltrating data to legitimate cloud storage like OneDrive.
- Notable campaigns include TOUGHPROGRESS (Google Calendar C2), targeted trade-policy phishing (impersonating a U.S. congressman), and rapid exploitation around Log4Shell and other enterprise vulnerabilities.
- Defensive recommendations focus on reducing exploit exposure (patching, hardening internet-facing apps), enforcing phishing-resistant MFA, detecting native-tool abuse, and monitoring cloud/OAuth abuse and anomalous uploads.
MITRE Techniques
- [T1190 ] Exploit Public-Facing Application – Exploited internet-facing appliances and services to gain initial access (‘exploiting public-facing applications’)
- [T1566.001 ] Phishing: Spearphishing Attachment – Used targeted spearphishing with malicious attachments and ZIPs delivered from compromised sites (‘spearphishing that delivered a ZIP from a compromised government website’)
- [T1133 ] External Remote Services – Leveraged or targeted external remote services as an access vector (‘External Remote Services’)
- [T1195.002 ] Supply Chain Compromise: Compromise Software Supply Chain – Exploited third-party applications and software supply-chain paths to reach victims (‘follow-on compromises in 2022 involving exploitation paths tied to third-party applications’)
- [T1059.001 ] Command and Scripting Interpreter: PowerShell – Relied on PowerShell for staged payload decoding and execution to blend with admin activity (‘PowerShell and the Windows command shell are frequently used’)
- [T1059.003 ] Command and Scripting Interpreter: Windows Command Shell – Used the Windows command shell for execution and staging steps (‘PowerShell and the Windows command shell are frequently used’)
- [T1059.004 ] Command and Scripting Interpreter: Unix Shell – Employed command interpreters as part of execution chains (‘Command and Scripting Interpreter: Unix Shell’)
- [T1059.007 ] Command and Scripting Interpreter: JavaScript – Used scripting interpreters where appropriate in execution chains (‘Command and Scripting Interpreter: JavaScript’)
- [T1197 ] BITS Jobs – Used BITS Jobs for asynchronous or stealthy execution and transfer (‘BITS Jobs’)
- [T1203 ] Exploitation for Client Execution – Rapidly exploited client and server vulnerabilities to achieve execution (e.g., Log4Shell exploitation) (‘rapid exploitation of Log4Shell (CVE-2021-44228) shortly after disclosure’)
- [T1218.001 ] System Binary Proxy Execution: Compiled HTML File – Abused system-supported proxies and binary execution methods to run malicious content (‘Compiled HTML File’)
- [T1218.011 ] System Binary Proxy Execution: Rundll32 – Used trusted binaries like rundll32 to execute payloads and blend with legitimate processes (‘trusted binaries such as rundll32’)
- [T1569.002 ] System Services: Service Execution – Executed payloads via service execution and created disguised Windows Services for persistence (‘Disguised Windows Services, sometimes named to resemble legitimate components’)
- [T1047 ] Windows Management Instrumentation – Leveraged WMI for remote execution and administrative tasks (‘Windows Management Instrumentation’)
- [T1547.001 ] Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder – Used autostart mechanisms to maintain persistence (‘persistence options depending on the environment and objective’)
- [T1037 ] Boot or Logon Initialization Scripts – Employed initialization scripts as part of persistence strategies (‘Boot or Logon Initialization Scripts’)
- [T1136.001 ] Create Account: Local Account – Created local accounts to maintain footholds and enable access (‘Create Account: Local Account’)
- [T1543.003 ] Create or Modify System Process: Windows Service – Modified or created Windows services for recurring execution (‘Disguised Windows Services, sometimes named to resemble legitimate components’)
- [T1546.008 ] Event Triggered Execution: Accessibility Features – Used event-triggered execution mechanisms to persist and evade detection (‘Event Triggered Execution: Accessibility Features’)
- [T1505.003 ] Server Software Component: Web Shell – Deployed web shells on exposed servers for command execution and payload delivery (‘Web shells on exposed servers (including long-lived shells used for command execution and follow-on payload delivery)’)
- [T1053.005 ] Scheduled Task/Job: Scheduled Task – Created scheduled tasks for recurring execution and persistence (‘Scheduled Tasks for recurring execution’)
- [T1542.003 ] Pre-OS Boot: Bootkit – Employed pre-OS techniques when available to maintain persistence (‘Pre-OS Boot: Bootkit’)
- [T1014 ] Rootkit – Used rootkit capabilities to conceal presence and maintain control (‘Rootkit’)
- [T1098.007 ] Account Manipulation: Additional Local or Domain Groups – Manipulated accounts and group memberships to increase access and persistence (‘Account Manipulation: Additional Local or Domain Groups’)
- [T1134 ] Access Token Manipulation – Abused token/impersonation mechanisms for privilege escalation and lateral movement (‘Access Token Manipulation’)
- [T1480.001 ] Execution Guardrails: Environmental Keying – Used environmental checks to limit execution to target environments (‘Execution Guardrails: Environmental Keying’)
- [T1562.006 ] Impair Defenses: Indicator Blocking – Attempted to block or reduce defensive visibility and indicator reporting (‘Impair Defenses: Indicator Blocking’)
- [T1070.001 ] Indicator Removal: Clear Windows Event Logs – Removed or cleared event logs to hinder forensic analysis (‘Indicator Removal: Clear Windows Event Logs’)
- [T1070.003 ] Indicator Removal: Clear Command History – Cleared command histories to remove traces of activity (‘Indicator Removal: Clear Command History’)
- [T1070.004 ] Indicator Removal: File Deletion – Deleted artifacts and staging files after use (‘Artifact cleanup, including deletion of tools and stolen-data staging files’)
- [T1574.001 ] Hijack Execution Flow: DLL – Performed DLL hijacking or manipulation to alter execution flow (‘Hijack Execution Flow: DLL’)
- [T1574.006 ] Hijack Execution Flow: Dynamic Linker Hijacking – Used linker hijacking techniques to redirect legitimate loads to malicious code (‘Hijack Execution Flow: Dynamic Linker Hijacking’)
- [T1036.004 ] Masquerading: Masquerade Task or Service – Named tasks or services to resemble legitimate components (‘Masquerading: Masquerade Task or Service’)
- [T1036.005 ] Masquerading: Match Legitimate Resource Name or Location – Masqueraded files or services to match legitimate resource names or locations (‘Masquerading: Match Legitimate Resource Name or Location’)
- [T1027 ] Obfuscated Files or Information – Employed obfuscation and packing to hide payloads (‘Obfuscation and packing of payloads’)
- [T1027.002 ] Obfuscated Files or Information: Software Packing – Packed software to evade detection (‘Software Packing’)
- [T1027.013 ] Obfuscated Files or Information: Encrypted/Encoded File – Used encrypted or encoded payload stages to avoid detection (‘Encrypted/encoded payload stages’)
- [T1140 ] Deobfuscate/Decode Files or Information – Used native tools to decode or deobfuscate staged payloads (e.g., certutil decoding) (‘decoding with native tools like certutil’)
- [T1001.003 ] Data Obfuscation: Protocol or Service Impersonation – Hid commands and exfiltration by impersonating legitimate services and protocols (’embedding encrypted commands and exfiltrated data inside calendar event content to camouflage traffic as routine cloud activity’)
- [T1553.002 ] Subvert Trust Controls: Code Signing – Abused or subverted code signing to increase trust of malicious binaries (‘Subvert Trust Controls: Code Signing’)
- [T1110 ] Brute Force – Employed brute-force techniques where applicable to gain credential access (‘Brute Force’)
- [T1555 ] Credentials from Password Stores – Harvested credentials from stored password locations and configuration files (‘searches for credentials in configuration files and can harvest stored browser credentials’)
- [T1555.003 ] Credentials from Web Browsers – Extracted stored browser credentials to support lateral movement (‘harvest stored browser credentials’)
- [T1003.001 ] OS Credential Dumping: LSASS Memory – Dumped credentials from LSASS using tools like Mimikatz (‘use of tools like Mimikatz to dump credentials from LSASS’)
- [T1003.002 ] OS Credential Dumping: Security Account Manager – Extracted credentials from the SAM database (‘OS Credential Dumping: Security Account Manager’)
- [T1003.003 ] OS Credential Dumping: NTDS – Extracted Active Directory data using native tooling (e.g., ntdsutil) (‘use of native tooling (e.g., ntdsutil) to extract Active Directory data’)
- [T1056.001 ] Input Capture: Keylogging – Used input-capture techniques such as keylogging to obtain credentials (‘Input Capture: Keylogging’)
- [T1055 ] Process Injection – Performed process injection and in-memory execution to reduce disk footprints (‘in-memory execution and techniques like process hollowing’)
- [T1112 ] Modify Registry – Modified registry settings to support persistence and configuration changes (‘Modify Registry’)
- [T1087.001 ] Account Discovery: Local Account – Enumerated local accounts during discovery (‘Account Discovery: Local Account’)
- [T1087.002 ] Account Discovery: Domain Account – Enumerated domain accounts and privileges for lateral planning (‘Account Discovery: Domain Account’)
- [T1069 ] Permission Groups Discovery – Enumerated permission groups to identify privilege relationships (‘Permission Groups Discovery’)
- [T1083 ] File and Directory Discovery – Searched file systems for valuable data and credentials (‘File and Directory Discovery’)
- [T1680 ] Local Storage Discovery – Looked for locally stored data and artifacts to collect (‘Local Storage Discovery’)
- [T1046 ] Network Service Discovery – Scanned for network services and exposed systems to expand access (‘scanning for exposed services and vulnerable internal systems’)
- [T1135 ] Network Share Discovery – Enumerated network shares as part of lateral movement and data collection (‘enumerating hosts, users, services, and network shares’)
- [T1012 ] Query Registry – Queried registry keys to gather configuration and system details (‘Query Registry’)
- [T1018 ] Remote System Discovery – Performed discovery of remote systems to map the environment (‘Remote System Discovery’)
- [T1595.002 ] Active Scanning: Vulnerability Scanning – Conducted vulnerability scans to find exploitable systems (‘Active Scanning: Vulnerability Scanning’)
- [T1595.003 ] Active Scanning: Wordlist Scanning – Performed broad scanning techniques to identify targets (‘Active Scanning: Wordlist Scanning’)
- [T1593.002 ] Search Open Websites/Domains: Search Engines – Searched open sources for reconnaissance and victim information (‘Search Open Websites/Domains: Search Engines’)
- [T1594 ] Search Victim-Owned Websites – Searched victim-owned sites to identify upload points or exposed content (‘Search Victim-Owned Websites’)
- [T1596.005 ] Search Open Technical Databases: Scan Databases – Used technical databases for discovery and targeting (‘Search Open Technical Databases: Scan Databases’)
- [T1082 ] System Information Discovery – Collected system information to guide follow-on activity (‘System Information Discovery’)
- [T1016 ] System Network Configuration Discovery – Gathered network configuration and routing information (‘System Network Configuration Discovery’)
- [T1049 ] System Network Connections Discovery – Enumerated network connections to map communications (‘System Network Connections Discovery’)
- [T1033 ] System Owner/User Discovery – Determined system owners and user context to tailor access (‘System Owner/User Discovery’)
- [T1021.001 ] Remote Services: Remote Desktop Protocol – Used RDP and remote services for lateral access when available (‘Remote Desktop Protocol’)
- [T1021.002 ] Remote Services: SMB/Windows Admin Shares – Used SMB and admin shares for lateral movement and tool transfer (‘SMB/Windows Admin Shares’)
- [T1570 ] Lateral Tool Transfer – Transferred tools across the network to enable remote execution (‘transferring tools across the network’)
- [T1550.002 ] Use Alternate Authentication Material: Pass the Hash – Used alternate auth materials (e.g., pass-the-hash) to move laterally (‘Use Alternate Authentication Material: Pass the Hash’)
- [T1119 ] Automated Collection – Automated collection of credentials and internal documents for exfiltration (‘Automated Collection’)
- [T1005 ] Data from Local System – Collected files and artifacts from local systems (‘Data from Local System’)
- [T1213.003 ] Data from Information Repositories: Code Repositories – Targeted code repositories and source code for collection (‘collection commonly targets … source code’)
- [T1213.006 ] Data from Information Repositories: Databases – Accessed databases to collect high-value data (‘Data from Information Repositories: Databases’)
- [T1074.001 ] Data Staged: Local Data Staging – Staged collected data locally before exfiltration (‘Data Staged: Local Data Staging’)
- [T1560.001 ] Archive Collected Data: Archive via Utility – Compressed and archived data using standard utilities for exfiltration (‘Collection commonly targets high-value internal data … using compression/archiving tools’)
- [T1560.003 ] Archive Collected Data: Archive via Custom Method – Used custom archiving methods to package data for exfiltration (‘Archive via Custom Method’)
- [T1071.001 ] Application Layer Protocol: Web Protocols – Used HTTP/HTTPS for C2 to blend with legitimate traffic (‘Communications often leverage HTTP/HTTPS’)
- [T1071.002 ] Application Layer Protocol: File Transfer Protocols – Used file transfer protocols where appropriate for C2 or exfiltration (‘Application Layer Protocol: File Transfer Protocols’)
- [T1071.004 ] Application Layer Protocol: DNS – Employed DNS-based channels for C2 in some operations (‘in some operations DNS-based channels have also been observed’)
- [T1090 ] Proxy – Used proxying techniques and legitimate services to hide command traffic (‘comfort using legitimate web services and common protocols to hide in plain sight’)
- [T1008 ] Fallback Channels – Implemented fallback or multi-stage channels to maintain resilience (‘Multi-Stage Channels’)
- [T1104 ] Multi-Stage Channels – Used multi-stage channels and staged payloads for execution and C2 (‘staged payload delivery approaches (encoding and chunking payloads)’)
- [T1568.002 ] Dynamic Resolution: Domain Generation Algorithms – Employed dynamic resolution techniques to evade static blocking (‘Dynamic Resolution: Domain Generation Algorithms’)
- [T1573.002 ] Encrypted Channel: Asymmetric Cryptography – Used encrypted channels and asymmetric cryptography to protect C2 and exfiltrated data (’embedding encrypted commands and exfiltrated data’)
- [T1102.001 ] Web Service: Dead Drop Resolver – Used web services as dead drop or rendezvous points for command delivery (‘Web Service: Dead Drop Resolver’)
- [T1583.007 ] Acquire Infrastructure: Serverless – Leveraged serverless or cloud-hosted infrastructure for command/control or staging (‘Acquire Infrastructure: Serverless’)
- [T1586.003 ] Compromise Accounts: Cloud Accounts – Compromised cloud accounts and OAuth apps to enable access and exfiltration (‘Compromise Accounts: Cloud Accounts’)
- [T1030 ] Data Transfer Size Limits – Used data transfer limits and chunking to avoid detection during exfiltration (‘writing them to disk in small pieces, then decoding with native tools like certutil’)
- [T1048.003 ] Exfiltration Over Alternative Protocol – Used alternative protocols and cloud services to move data out (‘exfiltrating to legitimate cloud storage services (for example, OneDrive) to blend outbound data movement’)
- [T1041 ] Exfiltration Over C2 Channel – Used C2 channels to exfiltrate data embedded in routine traffic (’embedding encrypted commands and exfiltrated data inside calendar event content to camouflage traffic’)
- [T1567.002 ] Exfiltration Over Web Service: Exfiltration to Cloud Storage – Exfiltrated collected data to cloud storage providers like OneDrive (‘exfiltrating to legitimate cloud storage services (for example, OneDrive)’)
- [T1486 ] Data Encrypted for Impact – Deployed or attempted to deploy ransomware or encryption for impact in some financially motivated campaigns (‘attempted ransomware deployment’)
- [T1496.001 ] Resource Hijacking: Compute Hijacking – Engaged in resource hijacking and other monetization activities (‘Resource Hijacking: Compute Hijacking’)
Indicators of Compromise
- [Malware ] campaign and tool names referenced – TOUGHPROGRESS (Google Calendar C2), DUST (dual-use operations)
- [Vulnerabilities ] exploited CVEs used as access vectors – CVE-2019-19781 (Citrix NetScaler/ADC), CVE-2021-44228 (Log4Shell), and CVE-2020-10189 (Zoho ManageEngine)
- [Artifacts/File Types ] initial delivery and persistence artifacts – ZIP attachment from a compromised government website, long-lived web shells on exposed servers
- [Services / Cloud Platforms ] abused cloud services used for C2/exfiltration – Google Calendar (used as covert C2 channel) and OneDrive (used for exfiltration)
- [Accounts / OAuth ] compromised account indicators and app abuse – compromised cloud accounts and new/suspicious OAuth applications enabling C2 or data access
- [Processes / Utilities ] native Windows tools frequently abused – PowerShell, certutil, rundll32 (used for staging, decoding, and execution)