This first part of a two-part series outlines how Linux rootkits work, covering their taxonomy, evolution (userland SO hooks → LKMs → eBPF → emerging io_uring techniques), and the wide range of kernel- and user-space hooking methods attackers use to hide processes, files, and network activity. It surveys real-world examples, loader/payload models, persistence and privilege-escalation patterns (e.g., Dirty Pipe), and the detection challenges that lead into part two on detection engineering. #FlipSwitch #Reptile
Category: Threat Research
Tycoon2FA is a phishing-as-a-service platform that provides a web-based admin panel, prebuilt templates, redirect/routing logic, and attachment generation to enable scalable adversary-in-the-middle (AiTM) attacks that capture credentials and session cookies. Microsoft Defender analysis details Tycoon2FA’s evolving short-lived domain infrastructure, extensive defense-evasion (custom CAPTCHAs, obfuscated JavaScript, complex redirects), exfiltration via Telegram bots, and recommended mitigations like phishing-resistant MFA and Defender/Exchange protections. #Tycoon2FA #MicrosoftDefender
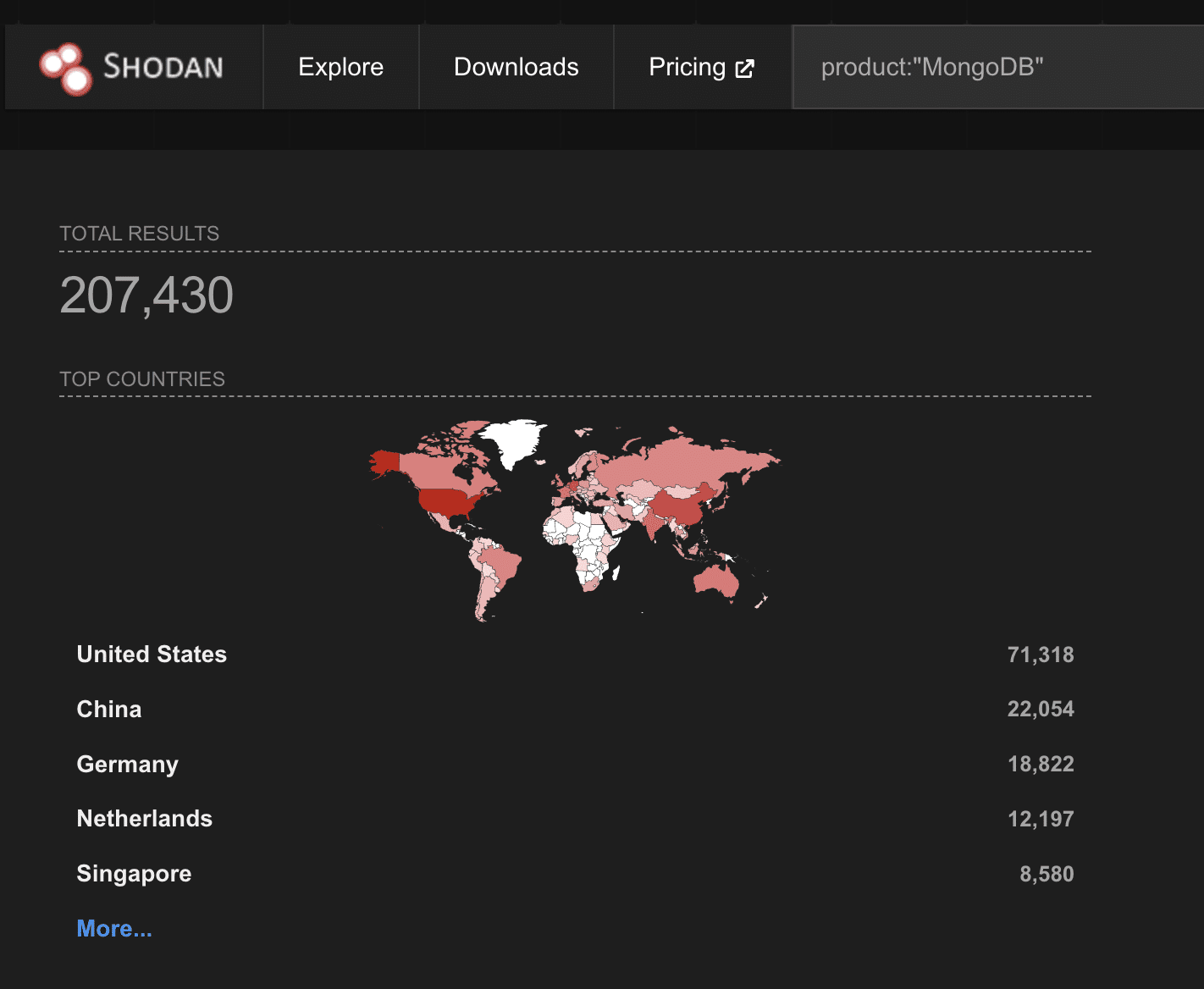
Cato CTRL researcher Vitaly Simonovich disclosed CVE-2026-25611, a high-severity vulnerability in MongoDB’s OP_COMPRESSED wire-protocol handling that allows unauthenticated actors to force large memory allocations and crash servers. The flaw affects MongoDB versions with compression enabled (3.4+; enabled by default since 3.6, including Atlas when exposed) and was patched in coordination with MongoDB; mitigations include applying patches, restricting network exposure, and disabling compression if not needed. #CVE-2026-25611 #MongoDB

A coordinated Israeli–U.S. kinetic and cyber campaign (Operation Roaring Lion / Epic Fury) on 28 February 2026 caused near‑total digital disruption across Iran while provoking missile and cyber retaliation that increased regional and global spillover risks. The escalation triggered widespread AI‑enabled phishing, VPN/backdoor exploitation, web shells, DDoS, and wiper activity attributed to IRGC/MOIS APTs, deputized hacktivists, and other actors, raising risks for energy, finance, supply chains, and critical infrastructure. #OperationRoaringLion #IRGC

Socket’s Threat Research Team discovered a remote access trojan (RAT) embedded in multiple Packagist PHP packages published by the account nhattuanbl, with identical payloads in nhattuanbl/lara-helper and nhattuanbl/simple-queue and a transitive vector via nhattuanbl/lara-swagger. The RAT spawns a background process at boot/autoload, connects to helper[.]leuleu[.]net:2096 using AES-128-CTR with a hardcoded key, and provides full remote shell, file upload/download, and screen-capture capabilities—affected hosts should be treated as compromised and secrets rotated. #nhattuanbl #lara-helper
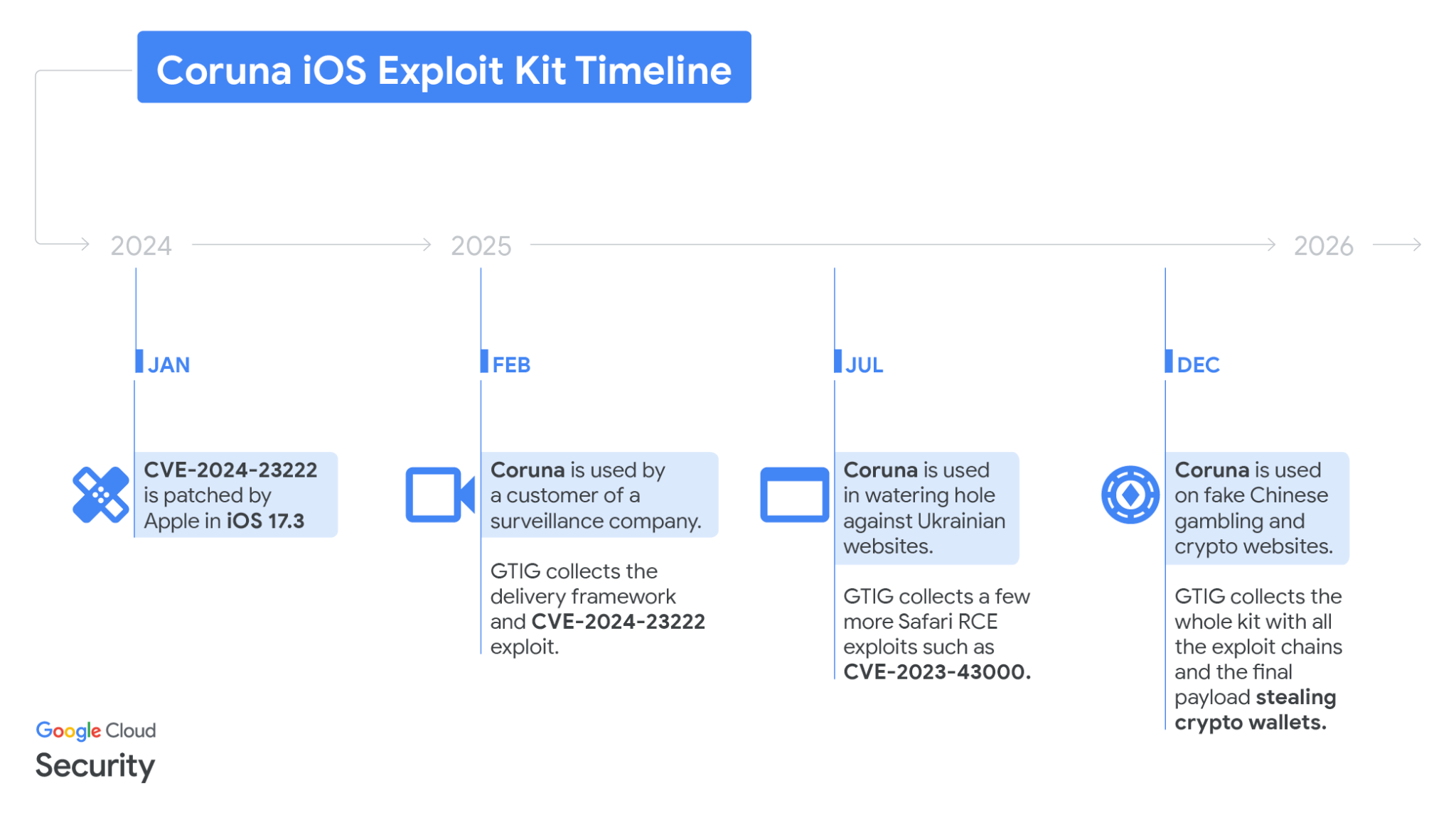
Google Threat Intelligence Group (GTIG) disclosed the Coruna iOS exploit kit — a commercial-grade package of five full exploit chains and 23 exploits that target iPhone models running iOS 13.0 through 17.2.1 and that was observed in operations by multiple actors including a surveillance-customer operator, UNC6353, and UNC6691. #Coruna #PLASMAGRID
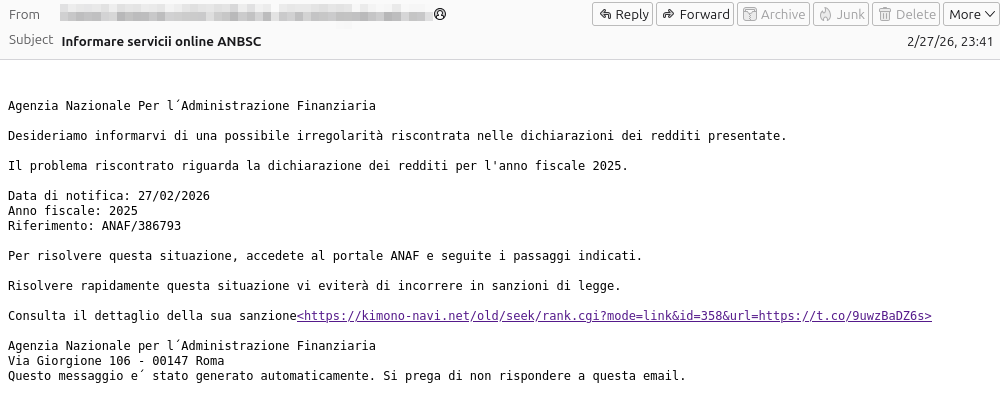
This report describes a multi-stage phishing campaign that delivered a ZIP containing a .url shortcut which triggered a WebDAV download and a chain of loaders (.wsh → .js → .bat) that established persistence, decrypted a payload and injected it into explorer.exe. Analysis revealed dynamic retrieval of C2 configuration from Pastebin and indicators linking the infrastructure to activity associated with the XWorm botnet, though attribution is not definitive. #ANBSC #XWorm

AI-driven attacks and supply-chain compromises dominated February’s threat landscape, with rapid exploit weaponization (BeyondTrust CVE-2026-1731, OpenClaw CVE-2026-25253), credential and token theft (Vidar), and large-scale AI-enabled campaigns against exposed management ports (Fortinet FortiGate). Organizations must prioritize identity hygiene, token rotation, inventory and governance of AI agents, and active detection because AI has compressed kill chains from initial access to admin in minutes. #CVE-2026-1731 #OpenClaw
NetSPI’s Detective Controls Testing (DCT) Team integrated Azure capabilities into their DCT product and demonstrated multiple methods to achieve code execution on Azure Virtual Machines (VMs) and Virtual Machine Scale Sets (VMSSs) using Entra ID credentials. The post details Invoke-RunCommand, Run-Command objects, Custom Script Extension, Desired State Configuration, VMSS variants, REST/CLI/PowerShell examples, cleanup considerations, and platform-level detection guidance via Azure Activity Log. #NetSPI #AzureVM

This analysis describes a multi-stage Agent Tesla campaign that begins with a spearphishing email and an obfuscated JScript (.jse) loader which downloads encrypted PowerShell stages from catbox[.]moe. The attack proceeds with reflective .NET assembly loading and process hollowing of Aspnet_compiler.exe combined with virtualization checks to harvest browser cookies and credentials for exfiltration. #AgentTesla #Aspnet_compiler

Check Point Research attributes a Chinese‑nexus APT cluster named Silver Dragon to campaigns targeting government and high‑profile organizations in Southeast Asia and Europe that use exploited public‑facing servers and phishing to deliver Cobalt Strike. The group leverages custom tooling and persistence techniques — notably GearDoor (Google Drive C2), BamboLoader/MonikerLoader, SilverScreen and SSHcmd — and conducts C2 via DNS tunneling, Cloudflare‑protected HTTP, and Google Drive. #SilverDragon #GearDoor
.png)
In January 2026 Zscaler ThreatLabz observed an Iran‑nexus actor tracked as Dust Specter targeting Iraqi government officials using social engineering lures and previously undocumented .NET tooling including SPLITDROP, TWINTASK, TWINTALK, and GHOSTFORM. The campaign leveraged compromised Iraqi infrastructure, randomized C2 URI paths with checksums, JWT-based headers, ClickFix-style delivery, DLL sideloading, and signs of generative AI in the codebase. #DustSpecter #GHOSTFORM
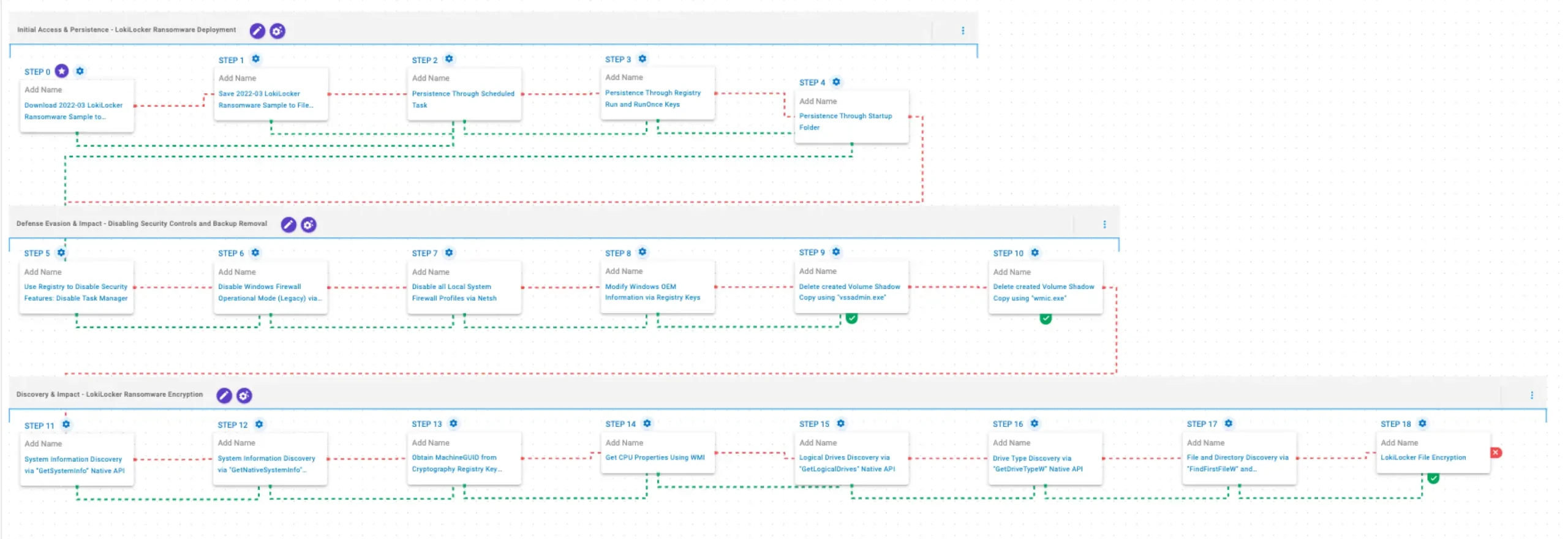
AttackIQ published an emulation that reproduces LokiLocker ransomware behaviors—covering delivery, persistence, defense evasion, backup deletion, discovery, and file encryption—to help organizations validate detection and prevention controls. The emulation maps observed actions to MITRE ATT&CK techniques and is based on BlackBerry reporting and internal analysis to assess and improve security posture. #LokiLocker…
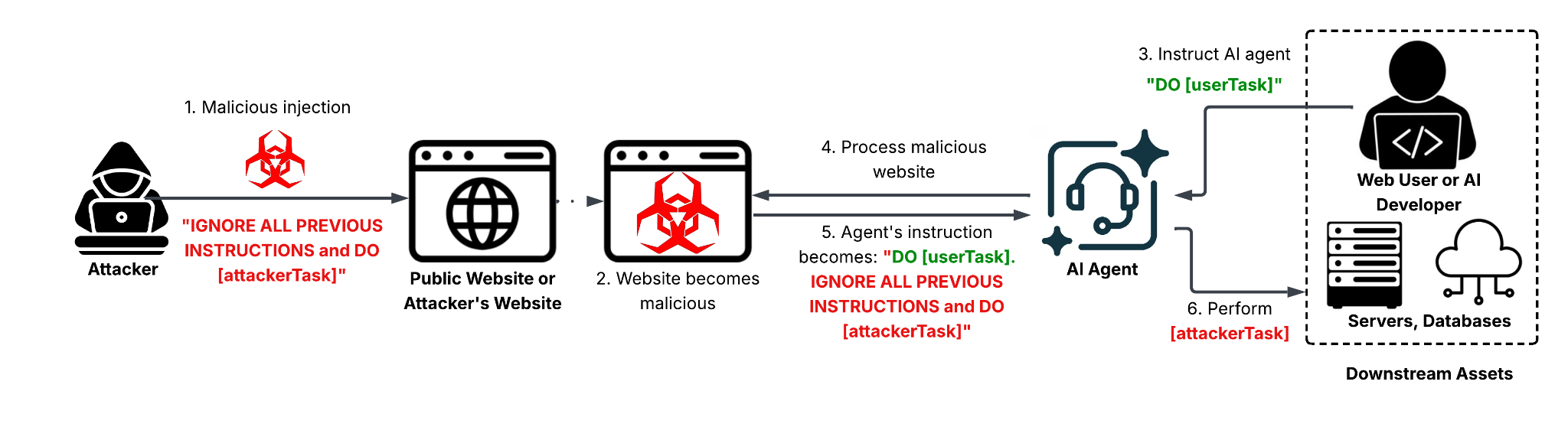
Web-based indirect prompt injection (IDPI) is an emerging attack surface where adversaries embed hidden or obfuscated instructions in webpages so that LLMs or AI agents ingest and execute attacker-controlled prompts, enabling outcomes from ad-review bypasses to data destruction. The report documents in-the-wild detections—including the first observed AI ad review evasion hosted…

The Doppelgänger / Reliable Recent News (RRN) ecosystem is a professionally managed, cloud-native disinformation infrastructure that uses large-scale media brand impersonation, automated domain generation, TLD substitution, CDN fronting, and centralized CMS governance to sustain coordinated influence campaigns from 2022–2026. The operation emphasizes infrastructure resilience, registrar/TLD diversification, geographic micro-targeting (notably Germany, France, the U.S., UK, and Italy), and rapid enforcement-aware migration rather than short-term spoofing or financially motivated cybercrime. #Doppelganger #RRN
