The Doppelgänger / Reliable Recent News (RRN) ecosystem is a professionally managed, cloud-native disinformation infrastructure that uses large-scale media brand impersonation, automated domain generation, TLD substitution, CDN fronting, and centralized CMS governance to sustain coordinated influence campaigns from 2022–2026. The operation emphasizes infrastructure resilience, registrar/TLD diversification, geographic micro-targeting (notably Germany, France, the U.S., UK, and Italy), and rapid enforcement-aware migration rather than short-term spoofing or financially motivated cybercrime. #Doppelganger #RRN
Category: Threat Research

Acronis H2 2025 telemetry shows median Microsoft patch install time of 185 hours (7.7 days) with a long P90 tail of 926 hours (38.6 days), while third‑party patches are faster on median (136 hours) but still exhibit a substantial long tail. The report concludes that operational improvements—staged rollouts, reboot discipline, endpoint reachability, and weekly tail management—are the most effective ways MSPs can shrink exposure and reduce support costs. #Acronis #Microsoft
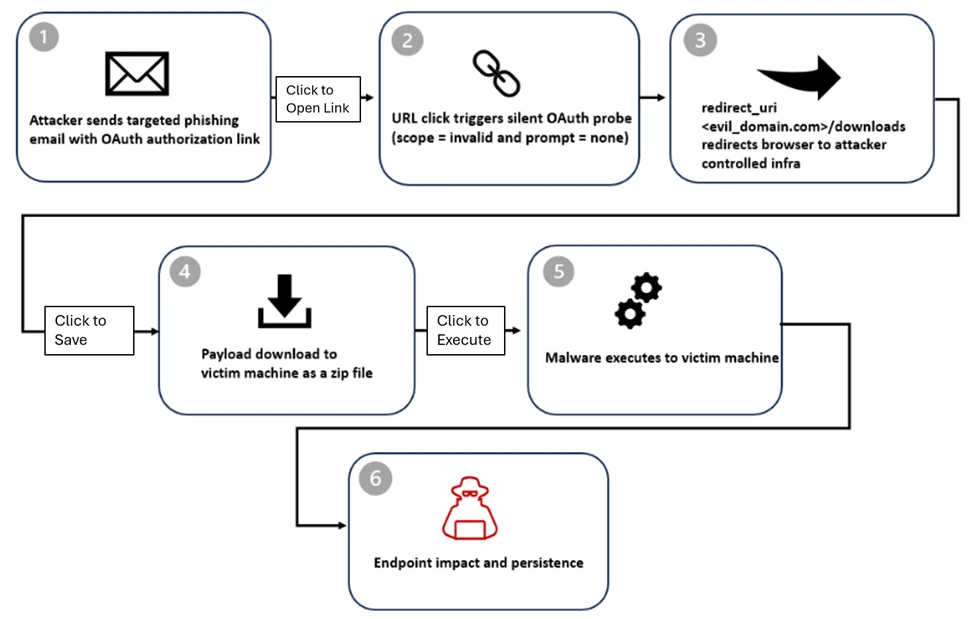
Microsoft Defender researchers observed phishing campaigns that abuse OAuth’s built-in redirection and silent authentication behavior (e.g., prompt=none and invalid scope) to redirect government and public-sector users to attacker-controlled landing pages without stealing tokens. Microsoft flagged malicious activity across email, identity, and endpoint signals, Microsoft Entra disabled the observed OAuth applications, but related OAuth redirect activity and malicious redirects (including use of EvilProxy and malware delivery) persist and require ongoing monitoring. #MicrosoftEntraID #EvilProxy

The RedAlert campaign distributes a trojanized version of the official Israeli Home Front Command “Red Alert” app via targeted SMS phishing, tricking users into sideloading a malicious APK that mirrors the legitimate UI while embedding a multi-stage spyware payload. The malware spoofs signing certificates and installer metadata, requests high-risk permissions to harvest SMS, contacts, and GPS, and exfiltrates data to attacker-controlled infrastructure; immediate quarantine, network blocking, and factory resets are recommended. #RedAlert #HomeFrontCommand
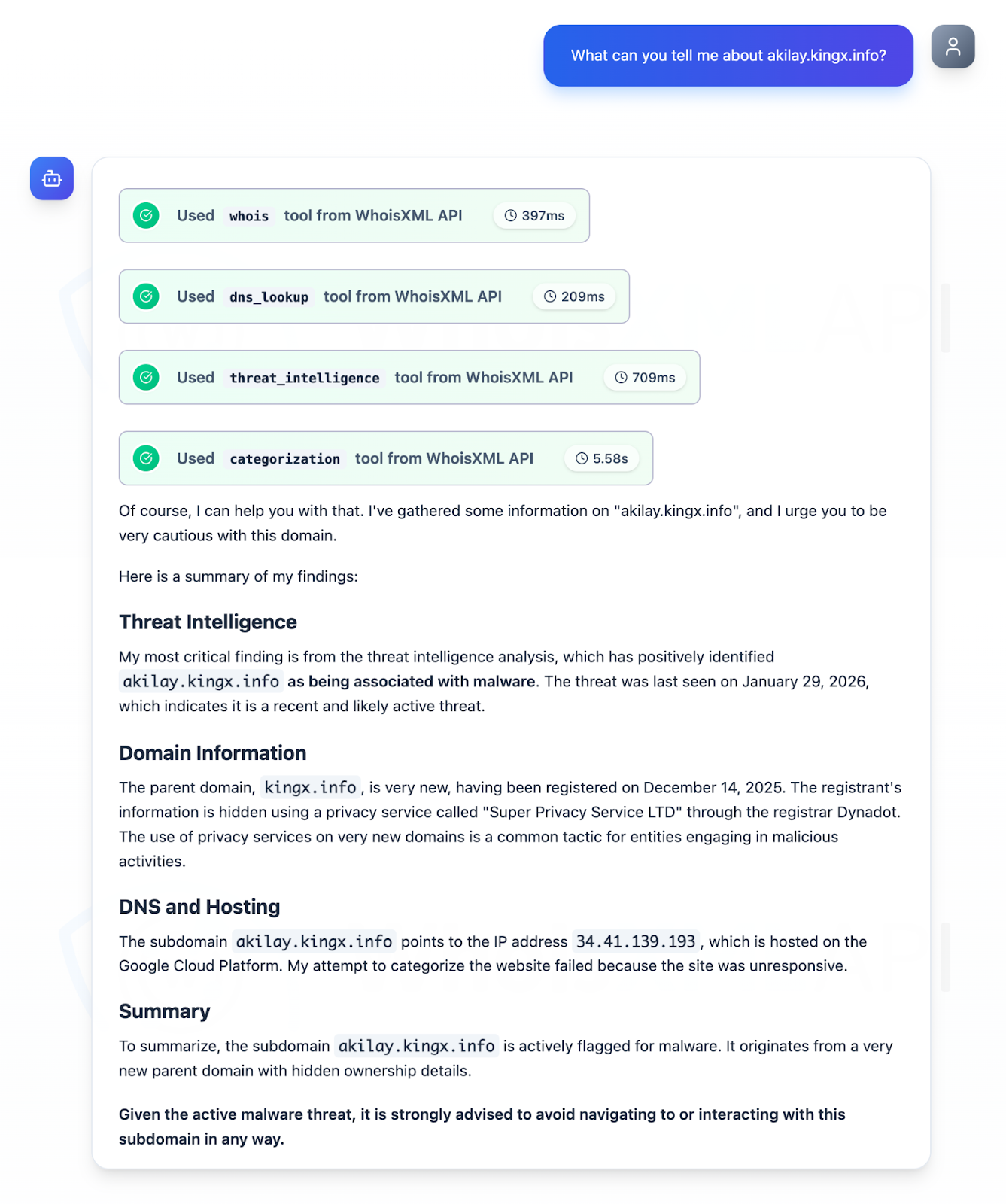
CIS published the top 10 malware of Q4 2025 and identified network IoCs for seven of them, with 46 IoCs analyzed after excluding domains tied to legitimate entities. The investigation uncovered malicious domains and subdomains (including a confirmed malicious subdomain akilay[.]kingx[.]info), 145 unique client IPs contacting IoC domains, hundreds of email- and IP-connected domains, and multiple artifacts tied to campaigns. #SocGholish #AgentTesla
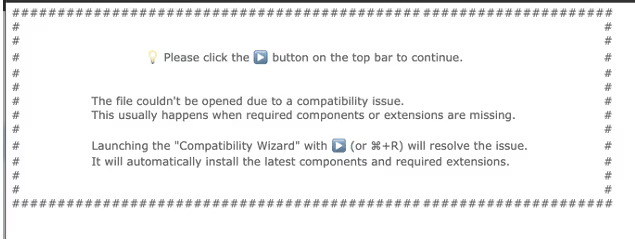
Darktrace researchers uncovered a multistage AppleScript campaign targeting macOS users that uses phishing lures and social engineering to deliver a Node.js-based loader and attempt abuse of the macOS TCC privacy database to inherit permissions for trusted binaries. The campaign communicates with a C2 at sevrrhst[.]com, establishes persistence via LaunchAgents, and can fetch and execute additional Base64-encoded payloads and binaries. #TCC #sevrrhst
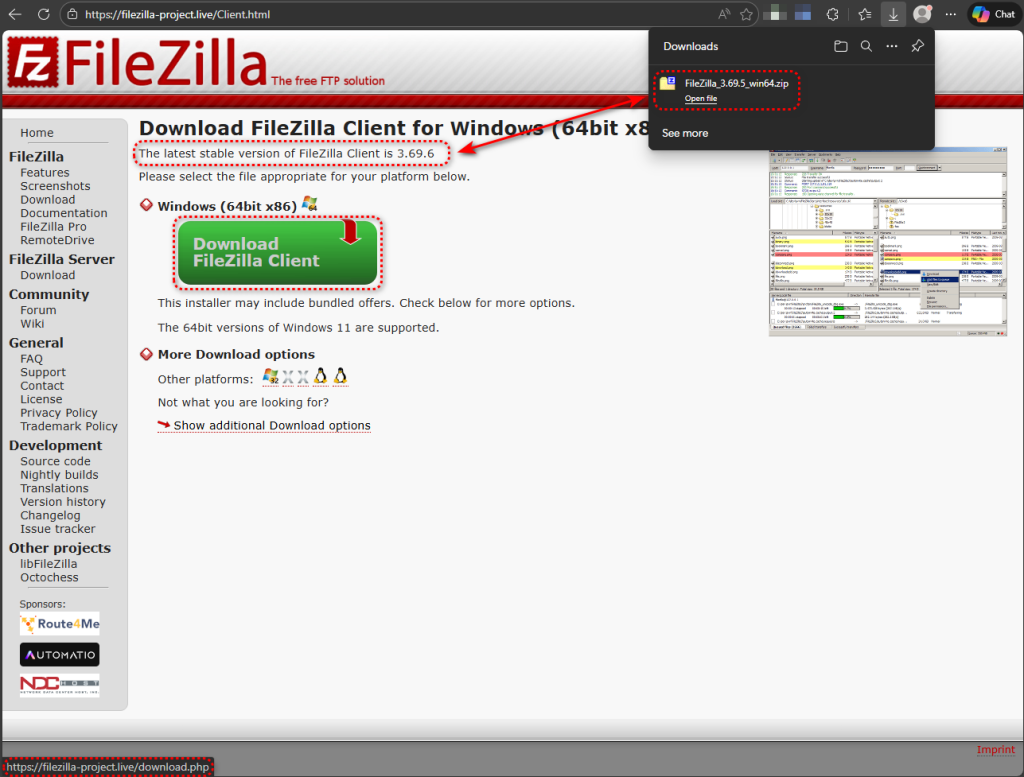
A trojanized portable build of FileZilla 3.69.5 is circulating on a lookalike site and contains a malicious version.dll that is loaded via DLL search-order hijacking, allowing the malware to run inside filezilla.exe and steal saved FTP credentials. The loader uses sandbox-evasion checks and DNS-over-HTTPS to contact its C2 infrastructure (welcome.supp0v3[.]com and…

Versions 1.8.12 and 1.8.13 of the Aqua Trivy VS Code extension published to OpenVSX contained injected code that launched local AI coding assistants (Claude, Codex, Gemini, GitHub Copilot CLI, Kiro CLI) in permissive modes to perform broad system reconnaissance and attempted exfiltration. Users and maintainers are advised to uninstall the affected versions, check for REPORT.MD and any repository creation named posture-report-trivy, rotate exposed credentials, and audit local AI and shell activity. #Trivy #AquaSecurity
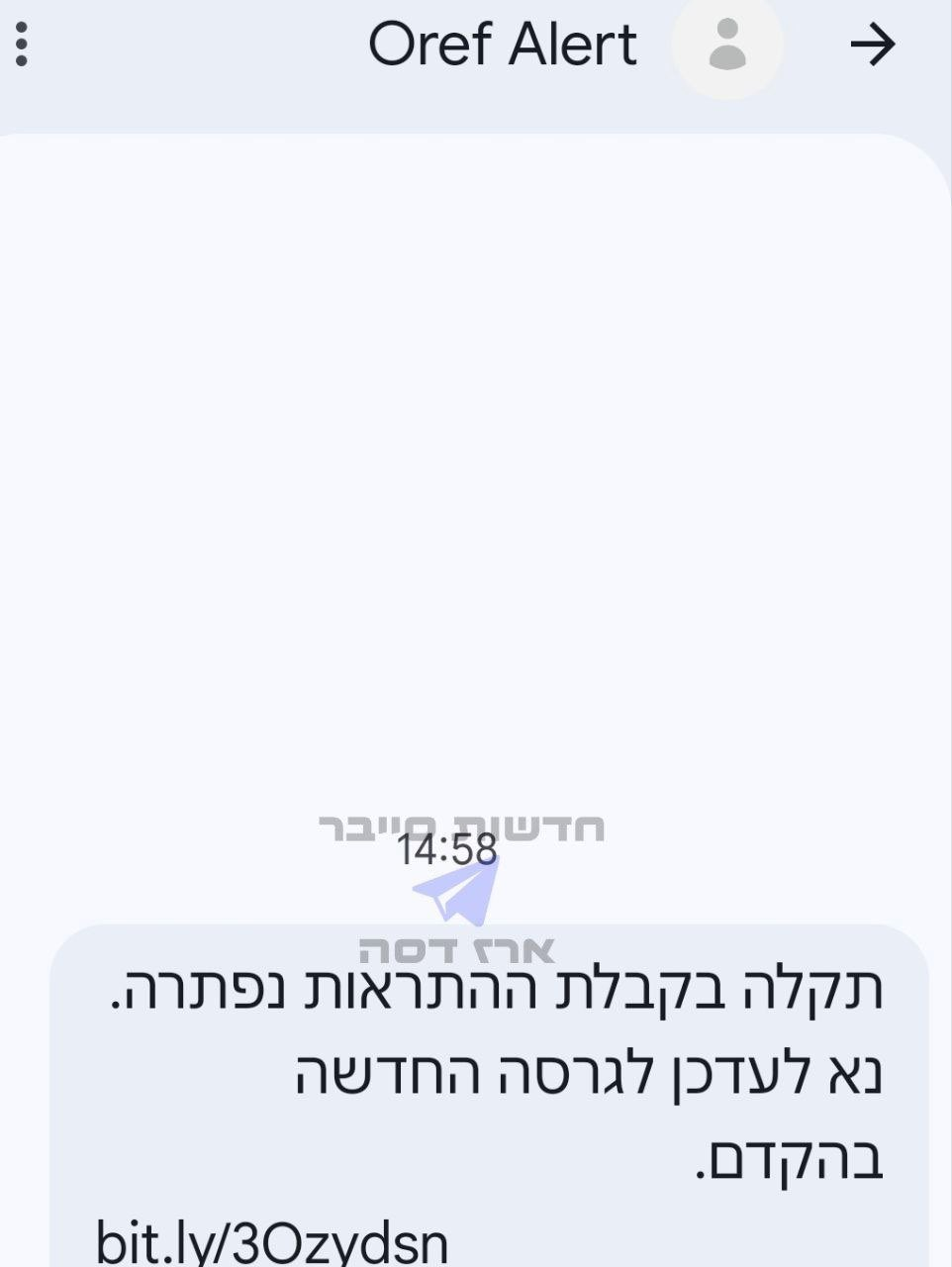
On Feb. 28, 2026, the United States and Israel launched coordinated strikes (Operation Epic Fury / Operation Roaring Lion), triggering a multi-vector Iranian retaliatory campaign and a severe national internet outage that reduced connectivity to 1–4%. Unit 42 observed active SMS/phishing campaigns delivering a malicious RedAlert APK and a widespread surge…
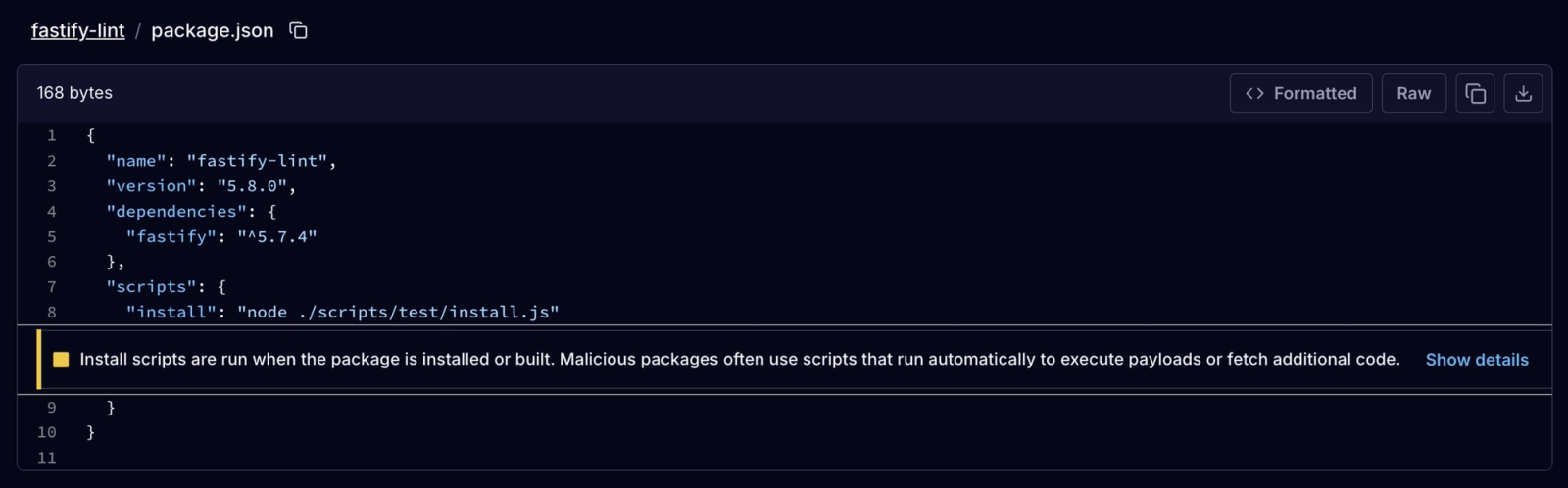
Socket detected a coordinated typosquatting npm campaign dubbed “StegaBin” that published 26 malicious packages which use Pastebin-based character-level steganography to hide Vercel C2 infrastructure and deliver a multi-stage installer that ultimately deploys a RAT and a nine-module infostealer targeting developer artifacts. The activity is consistent with the North Korean-aligned cluster tracked as FAMOUS CHOLLIMA / Contagious Interview and includes a shared loader (vendor/scrypt-js/version.js, SHA256: da1775d0…) and live C2 at 103[.]106[.]67[.]63:1244. #StegaBin #FAMOUS_CHOLLIMA

Agentic AI is moving from pilots to production in enterprise SOCs in 2026, enabling automated triage, correlated attack discovery, and auditable response while governance and tooling mature. Elastic positions its platform — including Attack Discovery, Agent Builder, and Workflows — to operationalize agentic SOCs that detect LOLBins activity (e.g., certutil.exe) and automatically investigate and remediate threats. #Elastic #certutil.exe
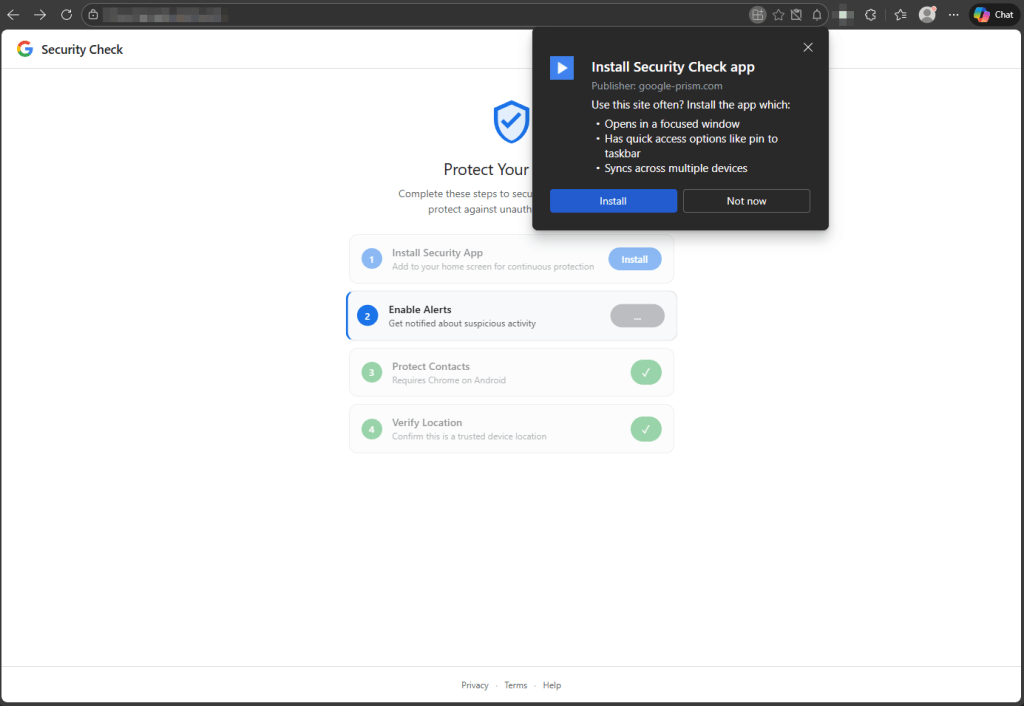
A phishing site impersonating a Google Account security page uses a Progressive Web App (PWA) and service worker to harvest contacts, push notifications, GPS, clipboard contents, intercept OTPs, scan local networks, and proxy traffic through the victim’s browser without a native app. If a victim follows all prompts the site also…

The Elastic Stack Terraform provider now enables security-as-code by letting teams manage detection rules, exception lists, prebuilt rules, ML anomaly detection jobs, synthetics monitors, and AI connectors in HCL for versioned, peer-reviewed workflows. This centralizes configuration, reduces drift, and adds cross-cluster API key and .bedrock/.gen-ai connector support for consistent, auditable deployments across environments #ElasticStack #Terraform

The 1Phish phishing kit evolved from a simple credential harvester in September 2025 into a multi-stage, MFA-aware, REST-API-driven phishing application by February 2026 that captures emails, secret keys, passwords, OTPs, and recovery codes while employing browser fingerprinting, bot scoring, and JavaScript obfuscation. #1Phish #1Password
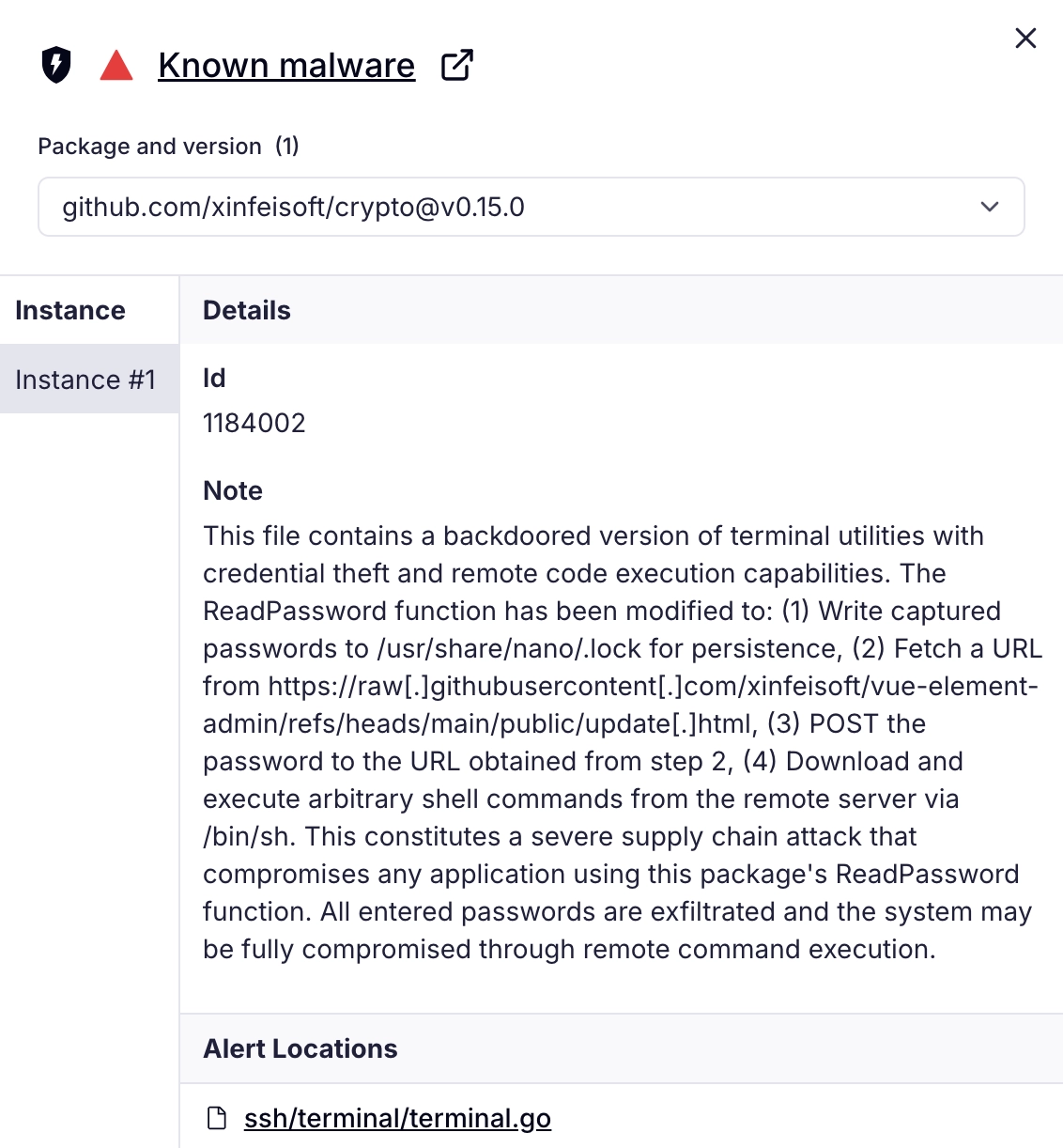
Socket’s Threat Research Team discovered a malicious Go module (github[.]com/xinfeisoft/crypto) that impersonates golang.org/x/crypto and inserts a backdoor in ssh/terminal/terminal.go to capture ReadPassword inputs and exfiltrate them. The backdoor uses a GitHub-hosted pointer to fetch a curl | sh stager that installs an SSH key, disables firewall restrictions, and ultimately delivers Rekoobe Linux backdoor payloads from img.spoolsv[.]cc. #Rekoobe #xinfeisoft
