CIS published the top 10 malware of Q4 2025 and identified network IoCs for seven of them, with 46 IoCs analyzed after excluding domains tied to legitimate entities. The investigation uncovered malicious domains and subdomains (including a confirmed malicious subdomain akilay[.]kingx[.]info), 145 unique client IPs contacting IoC domains, hundreds of email- and IP-connected domains, and multiple artifacts tied to campaigns. #SocGholish #AgentTesla
Keypoints
- CIS ranked the top 10 malware of Q4 2025 and seven of those (SocGholish, CoinMiner, Agent Tesla, Calendaromatic, ZPHP, VenomRAT, ACR Stealer) had network IoCs identified and analyzed.
- From the original IoCs, 46 were analyzed after excluding 15 domains owned by legitimate entities; the final in-depth set included 32 domains and 14 subdomains.
- Analysis revealed 145 unique client IPs communicating with eight IoC domains via 501 DNS queries, and seven IoC domains were likely maliciously registered from inception.
- Historical DNS and WHOIS queries showed 3,550 domain-to-IP resolutions across 31 domains and 43 unique WHOIS email addresses (16 public), leading to 359 email-connected domains discovered.
- Threat intelligence validation found 25 of the email-connected domains already weaponized (examples: sou[.]top, as5yo[.]top), 19 of 29 queried IPs previously tied to malicious campaigns, and several domains showed early malicious activity 20–517 days before CIS reporting.
MITRE Techniques
- [T1047 ] Windows Management Instrumentation – Used by CoinMiner to move laterally: ‘Crypto miner that typically uses WMI to spread across networks’
- [T1189 ] Drive-by Compromise – JS downloaders delivered via malicious or compromised sites and fake browser updates: ‘JS downloader distributed via malicious or compromised sites as fake browser updates’
- [T1566 ] Phishing (Spearphishing/ Malspam) – Malware such as VenomRAT is noted as being dropped or spread via malspam: ‘Open-source RAT often dropped by other malware or spread via malspam’
- [T1204.002 ] User Execution: Malicious File – Social-engineering lures (fake browser updates, masqueraded calendar downloads) entice users to execute JS/backdoor payloads: ‘Backdoor that masquerades as a legitimate calendar download spread via malvertisements and SEO poisoning’
Indicators of Compromise
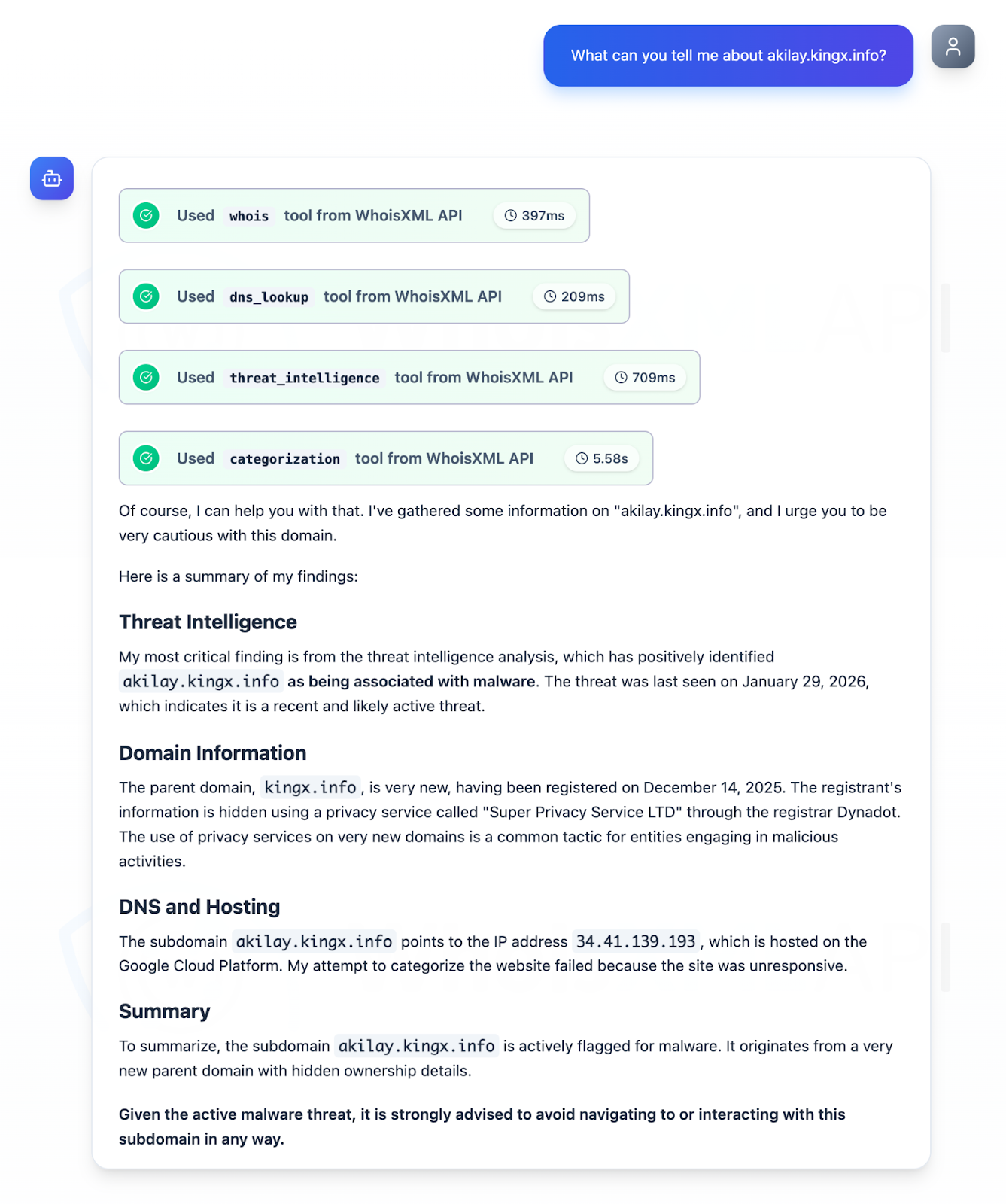
- [Domain ] Domains identified as IoCs and analyzed – paquetesparaorlando[.]com, kingx[.]info, and 30+ other domains analyzed
- [Subdomain ] Subdomains analyzed with one confirmed malicious – akilay[.]kingx[.]info, plus 13 other subdomains (11 unresponsive during checks)
- [Email-connected domain ] Domains discovered via historical WHOIS email linkage with confirmed weaponization – sou[.]top, as5yo[.]top, and 23 more malicious email-connected domains (359 total discovered)
- [IP addresses ] Network addresses communicating with IoCs – 145 unique client IPs contacted eight IoC domains; dataset references 29 IPs (19 confirmed malicious) — no specific IP values disclosed in the article
- [Historical domain-to-IP resolutions ] DNS history linking domains to IPs – 3,550 historical resolutions across 31 domains, first-resolution examples include paquetesparaorlando[.]com (first resolution 02/06/17) and karbowanec[.]com (first resolution 02/06/17)
Read more: https://circleid.com/posts/top-10-malware-of-q4-2025-a-dns-deep-dive