This report describes how threat actors abuse WebDAV access via Windows File Explorer to deliver remote access trojans (RATs) by hosting payloads on short-lived Cloudflare Tunnel demo domains. Campaigns use .url and .lnk shortcuts, UNC paths, and script chains to fetch payloads such as XWorm, Async RAT, and DcRAT from trycloudflare[.]com instances #WebDAV #CloudflareTunnel
Keypoints
- WebDAV is a legacy HTTP-based file management protocol natively accessible via Windows File Explorer (deprecated as of November 2023) and rarely recognized by typical users.
- Threat actors exploit File Explorer’s WebDAV support to bypass web browser download controls and sometimes evade EDRs by delivering files outside normal browser flows.
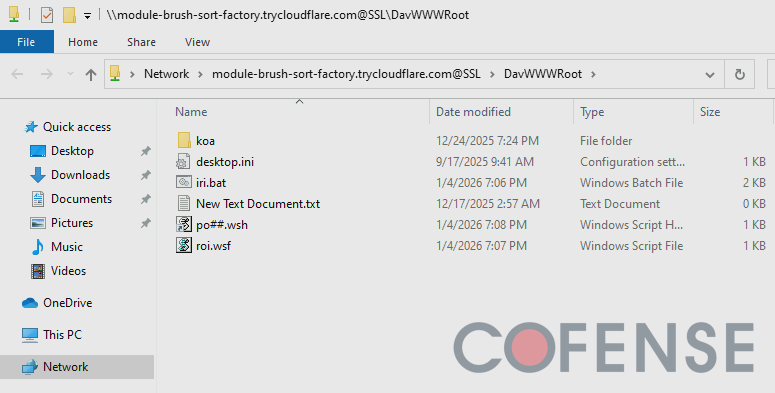
- Adversaries host short-lived WebDAV servers on Cloudflare Tunnel demo instances (trycloudflare[.]com) to expose payloads and make detection harder.
- Delivery chains commonly use .url and .lnk shortcut files, UNC paths, direct File Explorer links, and multiple script payloads to download and execute RATs (notably XWorm, Async RAT, and DcRAT); 87% of observed ATRs delivered multiple RATs.
- URL shortcut files with UNC paths can trigger automatic DNS lookups and outbound connections (example resolved to 104[.]16[.]231[.]132), potentially notifying threat actors when a victim browses a directory.
- Mitigations include user education to check File Explorer address bars, EDR behavioral detections for .url/.lnk that execute remote files, and threat hunting for demo Cloudflare Tunnel domains on trycloudflare[.]com.
MITRE Techniques
Indicators of Compromise
- [Domain ] WebDAV servers and Cloudflare Tunnel demo hosts – module-brush-sort-factory[.]trycloudflare[.]com, frontier-shops-timothy-cal[.]trycloudflare[.]com, and many other trycloudflare[.]com demo domains
- [IP Address ] Observed network artifact from a demo domain resolution – 104[.]16[.]231[.]132
- [File Name ] Malicious script and payload filenames referenced in delivery chains – rec.wsh, dat.wsh, and other WSH script files
- [Shortcut/File Type ] Shortcut types used to invoke File Explorer retrieval and execution – .url (InternetShortcut) and .lnk files used to open/run remote files
- [UNC Path ] Windows UNC/WebDAV path examples used to access remote files – harbor-microwave-called-teams[.]trycloudflare[.]comnew, exampledomain[.]comDavWWWRootMy_Files
Read more: https://cofense.com/blog/abusing-windows-file-explorer-and-webdav-for-malware-delivery
.png?language=en)