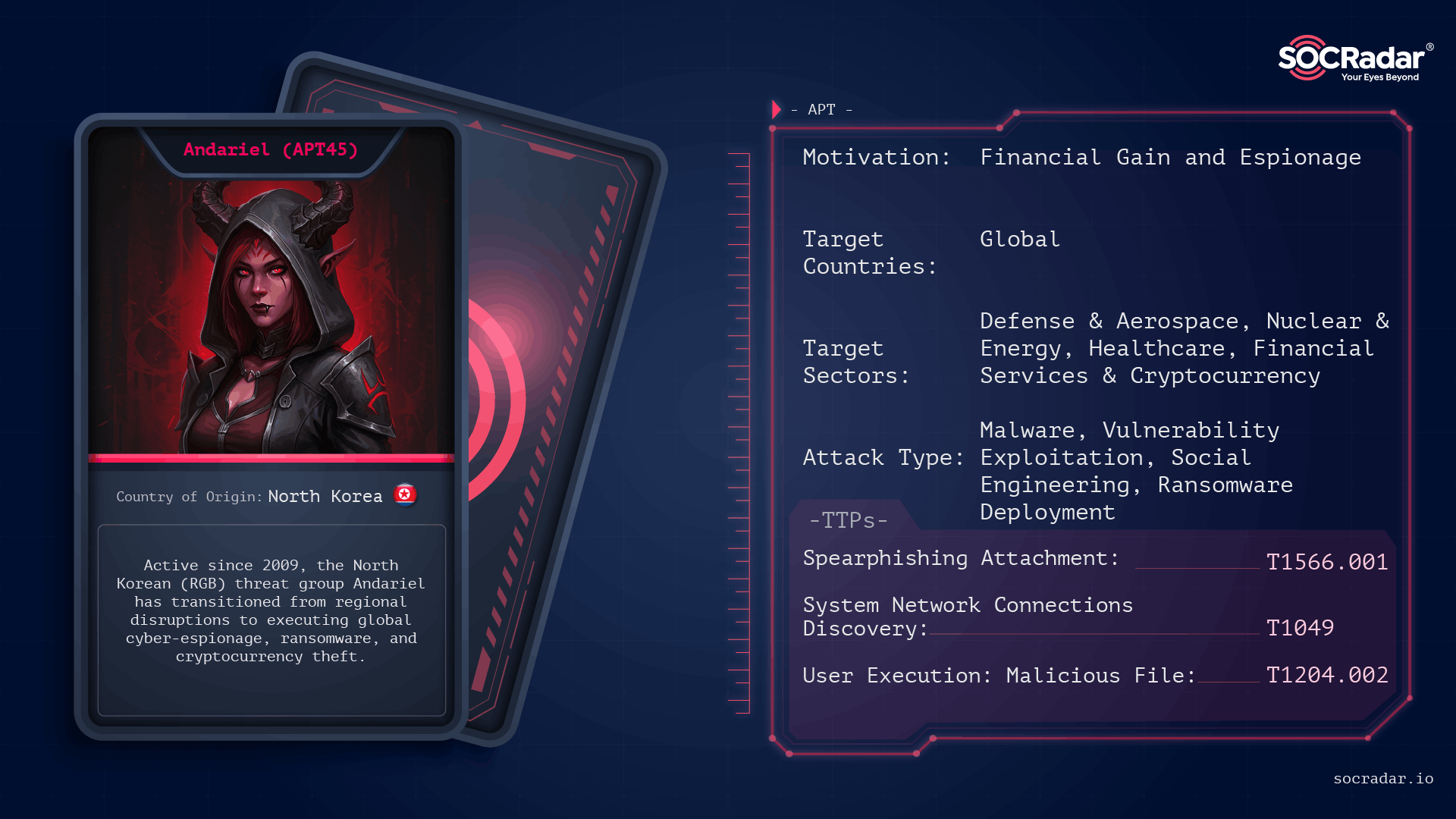
Andariel is a North Korea–linked RGB cyber cluster operating under the Lazarus umbrella that blends strategic espionage against defense, nuclear, aerospace, and supply-chain targets with revenue-driven operations such as ransomware and cryptocurrency theft. The group uses vulnerability exploitation, spear-phishing, living-off-the-land techniques, credential dumping, C2 tunneling and strains like Maui and DTrack to both collect intelligence and extract funds. #Andariel #Maui
Keypoints
- Andariel is assessed as a DPRK RGB unit and sub-cluster of Lazarus that conducts both cyber-espionage and financially motivated operations under centralized command.
- The group targets defense, nuclear, aerospace, healthcare, financial institutions, and software/ERP supply chains across South Korea, the U.S., Japan, Europe, and parts of Asia.
- Initial access tactics include exploitation of internet-facing N-day vulnerabilities (e.g., CVE-2021-44228/Log4Shell), spear-phishing with LNK/HTA payloads, and watering-hole compromises.
- Post-compromise activity emphasizes credential access and lateral movement using LotL tools (PowerShell, WMI), credential dumping (Mimikatz, ProcDump), and remote services (RDP/SSH/SMB).
- Data staging and exfiltration often use local compression and cloud uploads (MEGA, WinSCP/Putty), with C2 traffic tunneled via 3Proxy, PLINK, and Stunnel to mask communications.
- When aligned with regime priorities, Andariel pivots to ransomware and extortion (Maui, SHATTEREDGLASS) after data theft to maximize leverage and revenue.
MITRE Techniques
- [T1190 ] Exploit Public-Facing Application – Andariel leveraged N-day flaws including CVE-2021-44228 (Log4Shell) against VMware Horizon and other internet-facing services (‘leveraged N-day flaws, including CVE-2021-44228 (Log4Shell) affecting VMware Horizon, as well as vulnerabilities in Apache Tomcat and on-premises Microsoft SharePoint servers.’)
- [T1566.001 ] Spearphishing Attachment – The group used targeted phishing with job-seeking lures and archive attachments delivering LNK or HTA payloads (‘spear-phishing…impersonating recruiters or reputable organizations…ZIP archives containing Microsoft Windows Shortcut (LNK) files or HTML Application (HTA) scripts.’)
- [T1189 ] Drive-by Compromise – Watering-hole websites were compromised to distribute malware to sector-specific visitors (‘Watering hole attacks: Websites regularly visited by targeted sectors are compromised to distribute malware to visitors.’)
- [T1059.001 ] PowerShell – Operators abused native Windows utilities such as PowerShell to execute payloads and reduce detection (‘Native Windows utilities such as PowerShell, WMI, and command-line tools are abused to reduce detection risk.’)
- [T1047 ] Windows Management Instrumentation – WMI was used as a living-off-the-land mechanism for remote execution and management (‘Native Windows utilities such as PowerShell, WMI, and command-line tools are abused to reduce detection risk.’)
- [T1003 ] Credential Dumping – Tools like Mimikatz, ProcDump, and CredentialsFileView were used to extract credentials from LSASS memory and registry stores (‘tools like Mimikatz, ProcDump, and NirSoft’s CredentialsFileView are used to extract credentials from LSASS memory and registry stores.’)
- [T1021 ] Remote Services – Harvested credentials were abused for RDP and SSH access to move laterally and reach sensitive hosts (‘Harvested credentials enable access to additional systems through RDP, SSH, and SMB, allowing movement toward sensitive servers and administrative infrastructure.’)
- [T1074 ] Data Staged – Collected information was staged locally and compressed prior to exfiltration (‘Collected data is typically staged locally, compressed, and transferred to attacker-controlled infrastructure.’)
- [T1567 ] Exfiltration Over Web Service – Operators uploaded stolen data directly to cloud storage services (e.g., MEGA) using tools like WinSCP and PuTTY (‘Operators have logged into cloud storage services such as MEGA directly from compromised networks, uploading data with tools like WinSCP and PuTTY.’)
- [T1572 ] Protocol Tunneling – C2 and data channels were tunneled over legitimate protocols using 3Proxy, PLINK, and Stunnel to mask traffic (‘Utilities such as 3Proxy, PLINK, and Stunnel tunnel command-and-control traffic over legitimate protocols, masking data transfer activity.’)
- [T1055.012 ] Process Hollowing – Newer backdoor variants employed process hollowing against legitimate processes like explorer.exe to evade detection (‘Newer variants employ process hollowing (e.g., explorer.exe).’)
- [T1574.001 ] DLL Side-Loading – DLL side-loading techniques were used to load malicious payloads (e.g., Dora RAT via WinRAR SFX) (‘Dora RAT (DLL side-loading via WinRAR SFX)’)
- [T1071.001 ] Application Layer Protocol: Web Protocols – Malware used encrypted HTTP-like communications for C2 (e.g., TigerRAT) (‘TigerRAT: … encrypted HTTP-like communications.’)
- [T1486 ] Data Encrypted for Impact – Ransomware strains such as Maui and SHATTEREDGLASS were deployed after theft to encrypt systems and increase leverage (‘Andariel deployed strains such as Maui and later SHATTEREDGLASS…once data theft is complete, Andariel deploys ransomware to encrypt systems and increase leverage.’)
- [T1036 ] Masquerading – C2 traffic and components were disguised as legitimate update traffic to avoid detection (‘Atharvan: … disguising C2 traffic as legitimate Microsoft update traffic.’)
- [T1112 ] Modify Registry – Some malware families stored configuration in the registry as part of persistence and configuration management (‘NukeSped lineage malware with registry-based configuration storage.’)
Indicators of Compromise
- [CVE ] exploited vulnerability – CVE-2021-44228 (Log4Shell) used against VMware Horizon and other public-facing services
- [Malware ] observed families and payloads – Maui, DTrack, and 6 more families including TigerRAT, EarlyRat, Atharvan, Dora RAT, DurianBeacon, NukeSped
- [File Names ] ransomware artifacts and logs – maui.key, maui.evd, maui.log
- [Mutex ] mutex/marker – SAPTARISHI-ATHARVAN-101 used by Atharvan for instance identification
- [Tools ] credential and forensic utilities used by operators – Mimikatz, ProcDump (credential dumping and extraction)
- [C2/Tunneling Tools ] proxy and tunneling utilities – 3Proxy, PLINK, Stunnel used to tunnel C2 traffic
- [Cloud Services ] exfiltration endpoints and transfer tools – MEGA, uploaded via WinSCP and PuTTY from compromised networks
- [Exploited Products ] targeted software and services – VMware Horizon, Apache Tomcat, on-premises Microsoft SharePoint
- [Delivery Artifacts ] phishing/delivery file types – ZIP archives containing LNK (Windows Shortcut) files and HTA scripts
Read more: https://socradar.io/blog/dark-web-profile-andariel/