Socket’s Threat Research Team discovered a malicious Go module (github[.]com/xinfeisoft/crypto) that impersonates golang.org/x/crypto and inserts a backdoor in ssh/terminal/terminal.go to capture ReadPassword inputs and exfiltrate them. The backdoor uses a GitHub-hosted pointer to fetch a curl | sh stager that installs an SSH key, disables firewall restrictions, and ultimately delivers Rekoobe Linux backdoor payloads from img.spoolsv[.]cc. #Rekoobe #xinfeisoft
Keypoints
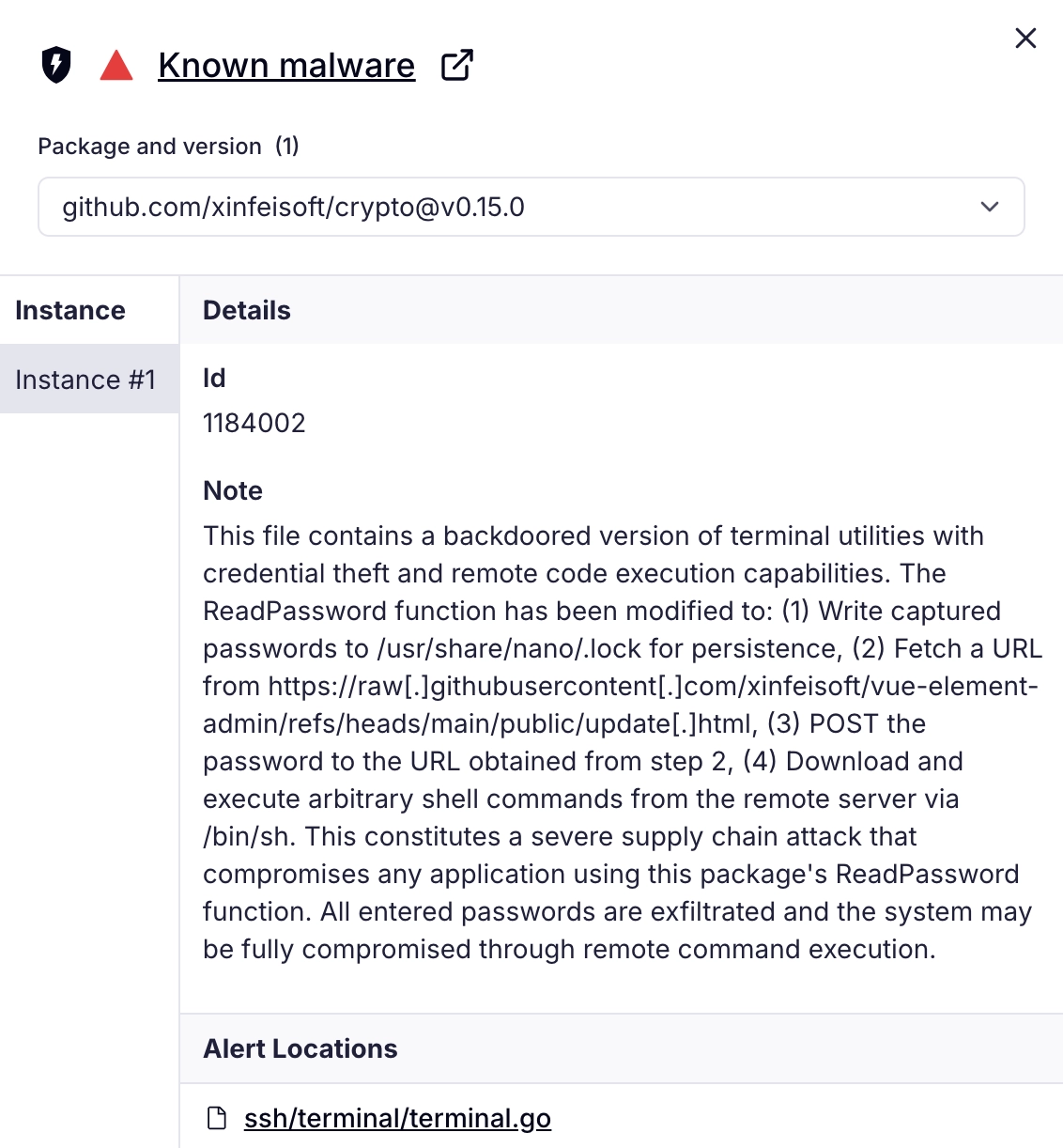
- The malicious module github[.]com/xinfeisoft/crypto clones the layout of golang.org/x/crypto but injects a backdoor into ssh/terminal/terminal.go that hooks ReadPassword to capture interactive secrets.
- The backdoor writes captured passwords to /usr/share/nano/.lock, posts them to an attacker-controlled endpoint, then retrieves and executes shell commands fetched via a GitHub Raw indirection.
- The fetched shell stager appends a threat-actor SSH key to /home/ubuntu/.ssh/authorized_keys, sets iptables defaults to ACCEPT, and downloads two .mp5-disguised payloads (sss.mp5 and 555.mp5).
- Analysis confirmed sss.mp5 as a campaign stage/loader communicating with 154[.]84[.]63[.]184:443 and 555.mp5 as a Rekoobe Linux backdoor used for persistent access and C2 communication.
- The campaign abuses namespace confusion and GitHub Raw as a rotatable staging pointer to avoid republishing malicious modules while blending into normal developer traffic.
- The Go module was blocked by the public Go module proxy after reporting, but it remained listed on pkg.go.dev and accessible via public mirrors for a time, underscoring supply-chain exposure risk.
MITRE Techniques
- [T1195.002 ] Supply Chain Compromise – The attacker published a lookalike Go module that impersonates a trusted repository to introduce malicious code. (‘mirrors the structure and package layout of the legitimate golang.org/x/crypto repository’)
- [T1204.005 ] User Execution: Malicious Library – A backdoored library function (ReadPassword) executes in client applications to capture secrets when invoked. (‘backdoors ssh/terminal.ReadPassword() to capture interactive secrets, POST them to a threat actor-supplied endpoint, and execute server-provided shell content’)
- [T1036 ] Masquerading – The module mimics the legitimate x/crypto project structure to evade visual triage and appear routine in dependency graphs. (‘presents as a routine cryptography library with familiar subpackages’)
- [T1036.008 ] Masquerade File Type – The payloads are disguised with a .mp5 extension to appear like media files during quick review. (‘disguising them with the .mp5 extension, a media-like label that can help binaries blend in during quick review’)
- [T1656 ] Impersonation – The attacker impersonated the canonical repo by copying code and using a GitHub mirror to exploit trust in dependency resolution. (‘namespace confusion and impersonation of the legitimate golang.org/x/crypto subrepository’)
- [T1056 ] Input Capture – The backdoor captures interactive password input via ReadPassword before it can be hashed or encrypted. (‘captures the secret, writes it locally, then reaches out to threat actor-controlled infrastructure’)
- [T1071.001 ] Application Layer Protocol: Web Protocols – The backdoor uses HTTP(S) to fetch staging pointers and exfiltrate credentials via POST. (‘it fetches a GitHub hosted “update” resource … posts the harvested password to a threat actor-supplied endpoint’)
- [T1102.001 ] Web Service: Dead Drop Resolver – The attacker uses a GitHub Raw file as a lightweight configuration pointer that resolves to attacker infrastructure. (‘uses GitHub-hosted content as a lightweight configuration channel … to obtain the next hop’)
- [T1105 ] Ingress Tool Transfer – The stager uses curl to download additional binaries (sss.mp5 and 555.mp5) onto the host. (‘downloads additional payloads from img[.]spoolsv[.]cc while disguising them with the .mp5 extension’)
- [T1059.004 ] Command and Scripting Interpreter: Unix Shell – Retrieved shell content is executed via /bin/sh to run arbitrary commands on the host. (‘exec.Command(“/bin/sh”, “-c”, txt2).Start() // Execute in background’)
- [T1098.004 ] Account Manipulation: SSH Authorized Keys – The stager appends an attacker SSH public key to /home/ubuntu/.ssh/authorized_keys for persistent access. (‘appends a threat actor SSH key to /home/ubuntu/.ssh/authorized_keys’)
- [T1562.004 ] Impair Defenses: Disable or Modify System Firewall – The stager sets iptables default policies to ACCEPT to weaken host firewall posture. (‘sets iptables default policies to ACCEPT’)
- [T1070.004 ] Indicator Removal: File Deletion – The stager deletes dropped payload files after execution to reduce on-disk artifacts. (‘then deletes the dropped files to reduce on-disk artifacts’)
Indicators of Compromise
- [Malicious Go Module ] malicious module path – github[.]com/xinfeisoft/crypto
- [Threat Actor Account ] GitHub publisher – github[.]com/xinfeisoft
- [GitHub-Hosted Configuration ] staging pointer (GitHub Raw) – https://raw.githubusercontent[.]com/xinfeisoft/vue-element-admin/refs/heads/main/public/update[.]html
- [Payload URLs / Delivery Endpoints ] staging and payload hosts – https://img.spoolsv[.]cc/seed.php, https://img.spoolsv[.]cc/sss.mp5 (and https://img.spoolsv[.]cc/555.mp5)
- [Related Domains ] associated domains – img.spoolsv[.]cc, img.spoolsv[.]net
- [Network Indicator (IP) ] observed C2/IP – 154[.]84[.]63[.]184 (TCP 443 observed flows)
- [Payload SHA256 Hashes ] staged binaries – sss.mp5: 4afdb3f5914beb0ebe3b086db5a83cef1d3c3c4312d18eff672dd0f6be2146bc, 555.mp5: 8b0ec8d0318347874e117f1aed1b619892a7547308e437a20e02090e5f3d2da6
- [Persistence Artifact ] SSH public key added for persistence – (attacker SSH key appended to /home/ubuntu/.ssh/authorized_keys; key begins ‘AAAAB3NzaC1yc2EAAAADAQABAAABAQDVffcldZxW9RTs…’)
Read more: https://socket.dev/blog/malicious-go-crypto-module-steals-passwords-and-deploys-rekoobe-backdoor