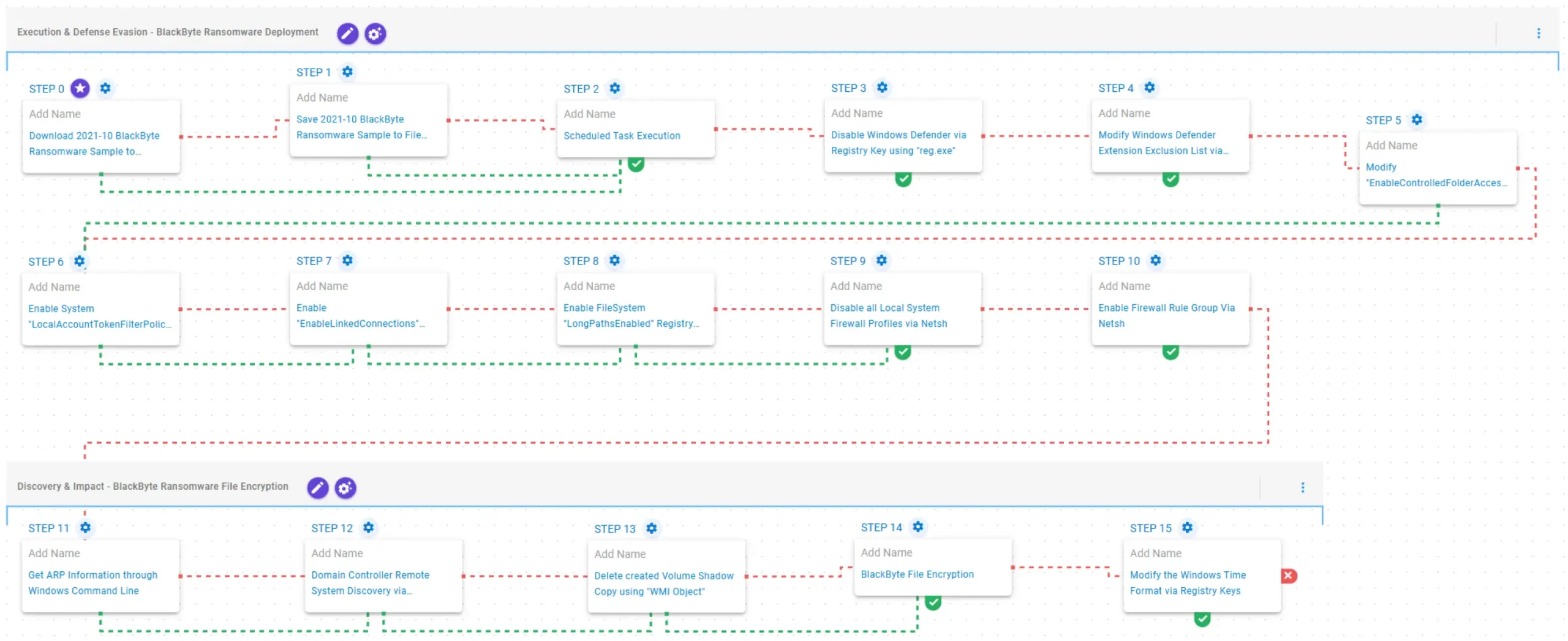
AttackIQ published an emulation of BlackByte ransomware behaviors to help organizations validate and improve their detection and prevention controls against this evolving RaaS threat. The emulation reproduces execution via scheduled tasks, disabling and excluding Windows Defender and firewall profiles, ARP discovery, shadow copy deletion, and AES/RSA file encryption to test defensive controls. #BlackByte #AttackIQ
Keypoints
- BlackByte is a Ransomware-as-a-Service (RaaS) family active since July 2021, believed to be an offshoot or rebranding related to Conti and sharing similarities with Lockbit.
- Early BlackByte builds were written in C#, later rewritten in Go with additional C++ components, and operators avoid targets with Russian/Eastern European language settings.
- Operators have exploited vulnerabilities (e.g., ProxyShell), abused vulnerable drivers, and used worm-like propagation and Living-off-the-Land binaries (LoLBins) to spread and evade detection.
- AttackIQ released an emulation (AEV Platform) that reproduces BlackByte TTPs to validate security controls, including scheduled task execution, Defender and firewall tampering, and file encryption.
- Defenders previously received a Trustwave decrypter in October 2021, prompting BlackByte operators to introduce multi-key encryption and enhanced leak infrastructure while warning against third-party decryptors.
- The emulation scenarios are based on reporting from Cisco Talos, Trend Micro, Zscaler, Palo Alto Networks, and IC3 and include tests for registry-based defense disabling, ARP discovery, VSC deletion, and AES-128/RSA-1024 encryption.
MITRE Techniques
- [T1105 ] Ingress Tool Transfer – Used to save and deliver BlackByte samples to disk for testing: (‘The BlackByte Ransomware Sample (SHA256: 8d2581e5…912) is saved to disk’)
- [T1053.005 ] Scheduled Task – Execution via creating and triggering a scheduled task with schtasks to run the ransomware: (‘creating a scheduled task using the schtasks utility and triggering it for immediate execution.’)
- [T1562.001 ] Impair Defenses: Modify Registry/Disable Security Tools – Disabling Windows Defender and modifying Defender exclusions and CFA via registry and Set-MpPreference to evade detection: (‘modifies the HKLMSOFTWAREPoliciesMicrosoftWindows DefenderDisableAntiSpyware registry key to 1’)
- [T1112 ] Modify Registry – Multiple registry modifications to enable linked connections, LocalAccountTokenFilterPolicy, and long path support to maintain access and broaden file reach: (‘modifies the EnableLinkedConnections registry key to ensure mapped drives remain accessible’)
- [T1562.004 ] Impair Defenses: Disable Firewall – Disables all local Windows Firewall profiles and enables specific firewall rule groups using netsh and PowerShell: (‘netsh advfirewall set allprofiles state off’)
- [T1016 ] System Network Configuration Discovery – Gathers ARP table information to perform local network reconnaissance: (‘executes the arp -a command to obtain the system’s Address Resolution Protocol (ARP) information.’)
- [T1490 ] Inhibit System Recovery (Delete Volume Shadow Copies) – Deletes Volume Shadow Copies via WMI to prevent recovery before encryption: (‘executes the Get-WMIObject Win32_ShadowCopy PowerShell command to delete a Volume Shadow Copy’)
- [T1486 ] Data Encrypted for Impact – Performs file discovery and encrypts files using AES-128-CBC for file encryption and RSA-1024 for key encryption: (‘Files matching an extension list are identified and encrypted in place using similar encryption algorithms as used by BlackByte ransomware.’)
Indicators of Compromise
- [File Hash ] BlackByte sample used in emulation – SHA256: 8d2581e5cc6e6fdf17558afe025ff84d9023ea636aca74dee39900d8f523e912
- [File Extension ] Defender exclusion modification – .exe (added to Windows Defender Extensions exclusion list)
- [Registry Keys/Values ] Defense and system configuration changes observed – HKLMSOFTWAREPoliciesMicrosoftWindows DefenderDisableAntiSpyware (set to 1), HKLMSYSTEMCurrentControlSetControlFileSystemLongPathsEnabled (set to 1), HKCUControl PanelInternationals1159 and s2359 (set to BLACKBYTE)
Read more: https://www.attackiq.com/2026/02/25/emulating-blackbyte-ransomware/