A threat actor is selling root shell access to a UK automation company’s CEO machine for $25K, but the real prize is the CEO’s OpenClaw AI assistant containing conversations, company databases, Telegram bot tokens, and Trading 212 API keys. The case highlights how locally running AI personal assistants (OpenClaw) are being marketed as turnkey intelligence backdoors on forums like BreachForums. #OpenClaw #BreachForums
Keypoints
- An attacker (forum user “fluffyduck”) listed root shell access to a UK-based automation company CEO’s PC on BreachForums for $25K in Monero or Litecoin.
- The listing’s primary value is the CEO’s OpenClaw AI assistant data: chat history, company production database (BSON), Telegram bot token, and Trading 212 API keys.
- OpenClaw runs locally with direct host access and stores data in plain-text Markdown and a .env file, enabling easy credential and data theft if the host is compromised.
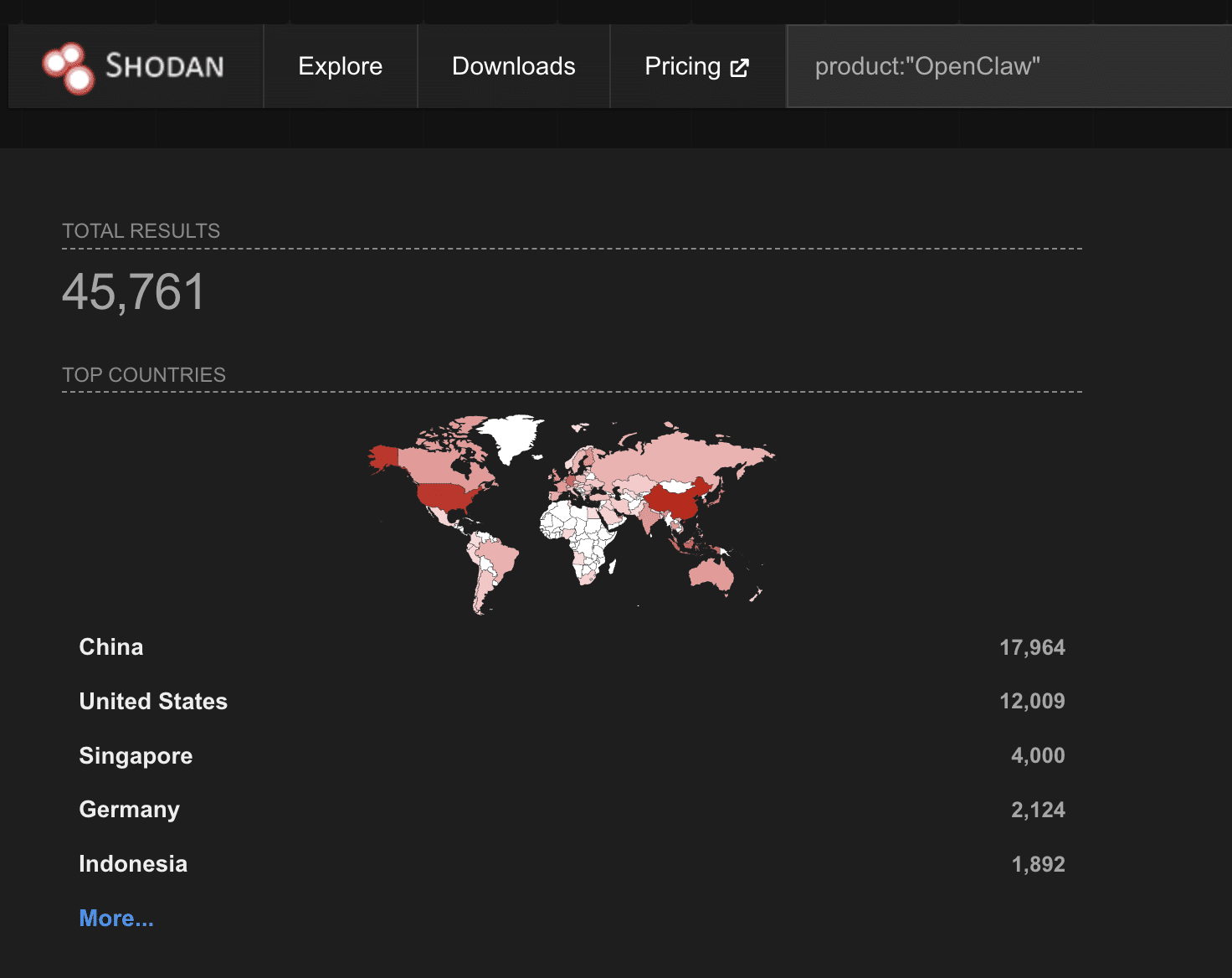
- OpenClaw’s rapid adoption produced large exposure: 45,000+ internet-facing instances (Shodan), 30,000+ actively compromised instances (Bitsight), and 824 malicious skills on ClawHub (Koi).
- Multiple high-severity CVEs with public exploits impact OpenClaw (CVE-2026-24763, CVE-2026-25157, CVE-2026-25253), enabling container escape, command injection, and token exfiltration.
- The breach model shifts monetization from selling raw access to selling aggregated intelligence (AI assistant data), drastically reducing attacker reconnaissance time.
- Enterprise controls (shadow AI discovery, DLP, ZTNA) are recommended to detect and block unauthorized AI assistants and prevent sensitive-data exposure.
MITRE Techniques
- [T1190] Exploit Public-Facing Application – Used when “a malicious web page can steal an authentication token, establish a WebSocket connection, bypass authentication…” [‘a malicious web page can steal an authentication token, establish a WebSocket connection, bypass authentication, and escape the container to execute commands on the host’]
- [T1059] Command and Scripting Interpreter – Demonstrated by OS command injection and arbitrary command execution via unsanitized inputs and SSH injection: “OS command injection through unsanitized secure shell (SSH) target strings, enabling arbitrary command execution via -oProxyCommand= injection.”
- [T1611] Escape to Host (Container Escape) – Illustrated by Docker sandbox escape and container breakout that allow host command execution: “Docker sandbox escape via unsafe PATH environment variable handling, allowing authenticated users to execute arbitrary commands on the host.”
- [T1552] Unsecured Credentials – Evidenced by plaintext storage of secrets and leaked tokens: “OpenClaw stores everything in plain-text Markdown files under `~/.openclaw/workspace/` … API keys in a `.env` file.”
- [T1078] Valid Accounts – Use of stolen/compromised legitimate credentials (Telegram bot token, Trading 212 API keys, OpenClaw dashboard credentials) to access services and automation: “CEO’s Telegram bot token and chat ID. Trading 212 API keys … OpenClaw dashboard credentials.”
Indicators of Compromise
- [CVE ] known vulnerable identifiers – CVE-2026-24763, CVE-2026-25157, and CVE-2026-25253 (public exploits enabling container escape, command injection, and token exfiltration)
- [Credential/Token ] exposed secrets and API keys tied to accounts – Trading 212 API keys, CEO’s Telegram bot token, and OpenClaw dashboard credentials
- [File path ] local artifact locations storing sensitive data – ~/.openclaw/workspace/ and .env (plaintext conversation logs, preferences, and API keys)
- [Forum username ] vendor/listing identifier – “fluffyduck” on BreachForums (seller of the compromised access)
- [Repository/project ] affected software names and projects – OpenClaw (formerly Clawdbot/Moltbot) and the Moltbook breach (1.5 million API tokens exposed)
Read more: https://www.catonetworks.com/blog/cato-ctrl-when-openclaw-ai-personal-assistant-becomes-backdoor/